@MidnightNetwork #night $NIGHT
When I started diving into the Midnight Network, I tried to set aside the hype and look for what really makes the project stand out in a crowded space that prizes privacy in theory but often struggles with practical trade-offs. My takeaway is that Midnight is aiming to repackage privacy tech for a blockchain environment in a way that emphasizes usability and verifiability not mystique. At its core, Midnight Network is designed as a privacy-focused layer that can run alongside other chains offering confidential transaction capabilities and private data handling without requiring users to abandon the broader ecosystems they rely on. It isn’t just about hiding from the world; it’s about providing a framework where sensitive information like transactional details, asset balances or contract inputs can be kept private while still enabling legitimate interactions, audits and cross-chain compatibility. In that sense, Midnight feels like an attempt to reconcile the tension between openness that blockchains inherently crave and the privacy users legitimately expect.
Privacy matters in blockchain for several reasons. First people transact every day with real-world implications: identities, business relations and personal finances. When every transaction is public that data can become a mosaic of patterns that reveal who you are, who you transact with and how much you’re willing to risk. That’s not just a theoretical concern; it can influence competition, bargaining power and even safety. Second privacy isn’t just about hiding; it’s about controlling disclosure. In many cases, users should be able to prove that a transaction or a credential exists without exposing the full context. In this sense, privacy is a governance and fairness issue as much as a security one: it shapes incentives, access and trust. Midnight’s focus on privacy is therefore a practical attempt to preserve autonomy in a system where data trails can be easy to trace and easy to monetize.
A big part of the technology narrative here is zero-knowledge proofs, or ZK proofs and how they can protect data without compromising verifiability. In my reading, ZK proofs let someone demonstrate that a statement is true such as “this transaction is valid or I have sufficient balance without revealing the underlying data. It’s like proving you have a key to a locked box without handing over the key itself or the contents inside. The math is intricate but the upshot is accessible: you get cryptographic assurance that operations are correct while the details stay private. In practice, this means you can confirm compliance, eligibility or authenticity without broadcasting sensitive attributes to the entire network. For a privacy-focused project, that capability is a powerful fault line: it allows complex interactions and audits to occur in a way that respects user confidentiality.
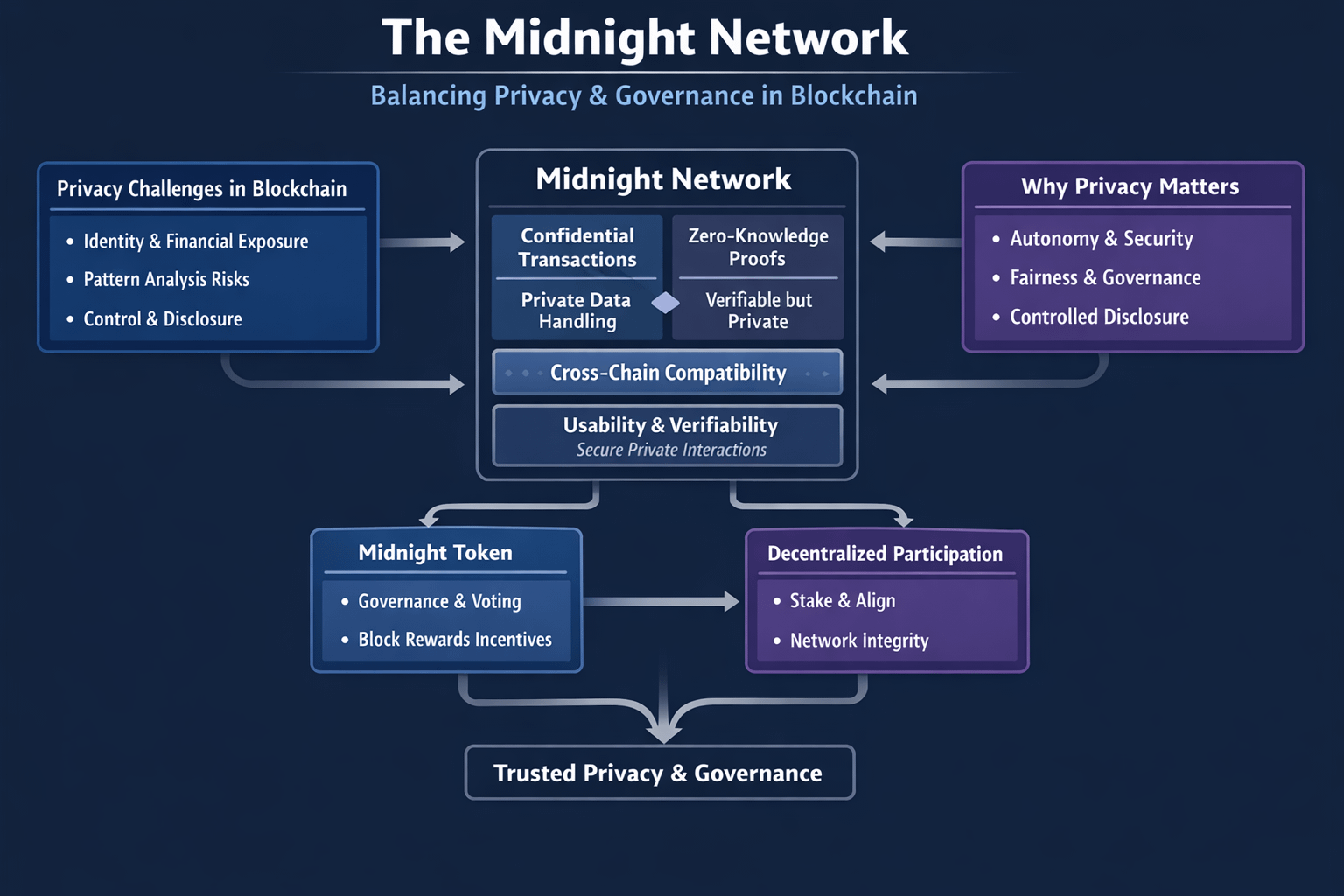
Regarding the role of the Midnight token in governance and block rewards, I observed a design where Midnight acts as both a governance stake and an alignment mechanism for network participants. In governance terms, holders can vote on protocol changes, privacy parameters and upgrade paths, which helps decentralize oversight and ensures that the community’s preferences influence the roadmap. On the incentive side, block rewards tied to Midnight create a tangible mechanism for miners or validators to earn compensation for maintaining network integrity. This dual function governance leverage plus economic incentives is where Midnight tries to anchor its privacy ambitions in a sustainable, participatory model. It signals a vision of a network where trusted privacy is not merely a feature but a foundation that participants actively steward through stake and decision making.
As I continue watching Midnight evolve, I’m curious to see how these components balance actual user privacy with governance participation and what that balance will imply for cross-chain privacy standards in the broader ecosystem.
