The strange part on Sign wasn’t the credential moving.
I thought it would be. Thought the mess would show up in the attestation itself. Maybe the schema would land wrong. Maybe one system would read the fields one way and another would read them another way. Maybe Sign Protocol would do the easy part, portability as a concept and then the credential would hit a foreign system and start shedding meaning.
Didn’t happen.
The attestation traveled. Cleanly enough to be annoying about it. Issued in one environment, read in another, still recognizable inside the next workflow. That part looked almost too calm. Sign kept the record legible across systems the way reusable verification is supposed to work.
So I blamed distribution next.
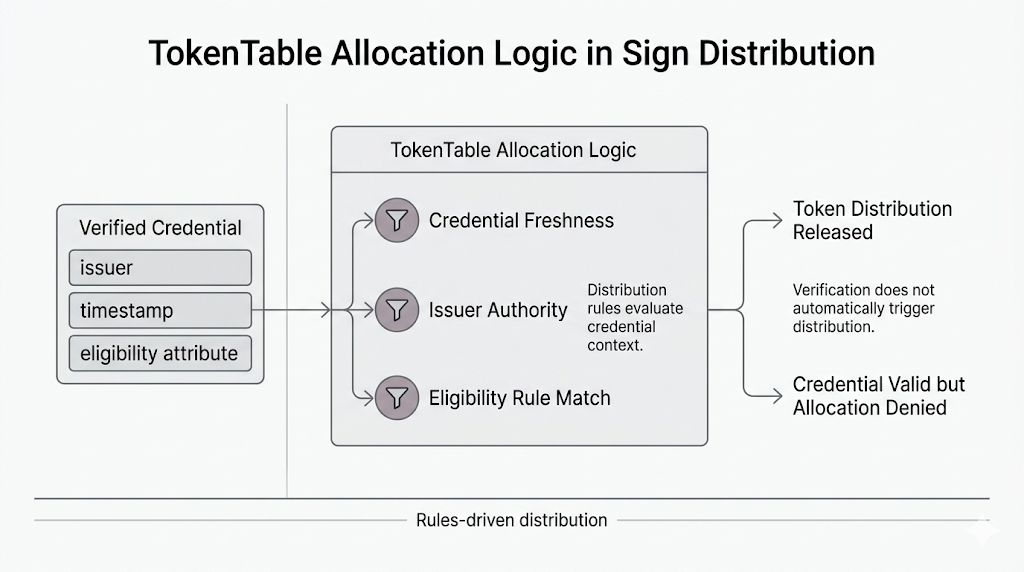
TokenTable, or whatever you want to call that distribution layer, felt like the obvious place for friction. A credential reaches a program. Allocation rules inspect it. Funds or tokens wait on the other side. I figured the pressure would sit there: freshness checks, rule mismatches, missing qualifiers, some ugly edge case where the credential is technically valid but not precise enough to release value.
That pressure is real. But it still wasn’t the first thing that turned the workflow political.
The real argument on Sign starts a little earlier.
The attestation verifies. Fine.
Then someone asks whether the issuer belongs on the trust list.
That is the shift.
Because Sign’s global story is not just about portable credentials. It is about whether portability survives contact with institutions that do not inherit the same issuer accreditation map. One authority issues the credential. Another institution funds the program. A third system executes the distribution logic through Sign. Everybody likes interoperability right up until another jurisdiction’s issuer registry enters their payout flow.
That is where issuer trust stops sounding like metadata and starts acting like infrastructure.
A school, agency, employer, or verifier in one country issues a credential through Sign Protocol. Another program somewhere else wants to use that attestation for a grant, reward, access campaign, subsidy, or token distribution. The credential arrives. The proof checks out. The fields are there. TokenTable can see what it needs to see.
And still the workflow stalls.
Not because the credential failed. Because the issuer has not been institutionally accepted by the party releasing value.
That is a very Sign-shaped problem.
The portability worked. The trust registry did not travel with equal force.
Which means Sign ends up sitting right inside the uncomfortable middle: between issuer accreditation and executable distribution. Between interoperable verification and fragmented institutional trust. Between “this attestation is valid” and “we are actually willing to fund against it.”
And those are not the same decision.
That’s the part people flatten too quickly when they talk about global credentials. They make it sound like cross-border verification becomes clean once the record is portable. On Sign, portability can be clean while issuer trust stays completely uneven. One country’s accepted authority is another program’s unresolved risk. One registry says approved. Another says pending review. A third says manual exception only.
So the credential keeps moving.
The politics move slower.
Which leaves the actual pressure sitting exactly where Sign becomes most relevant: not at the moment a credential is issued, but at the moment an international distribution has to decide whether another institution’s issuer list is good enough to release real value.
The attestation may already be global.
The accreditation behind it. Still very local.