@MidnightNetwork I noticed it while comparing two transaction traces that should have behaved similarly but didn’t. One cleared with a predictable delay, the other stalled in a way that felt less like congestion and more like resource timing. That difference pulled my attention away from privacy as a feature and toward how Midnight actually schedules computation.
The common assumption is that privacy networks scale the same way as public chains, just with heavier cryptography layered on top. That framing misses something. Midnight seems less focused on hiding transactions and more on reshaping how execution is allocated in the first place.
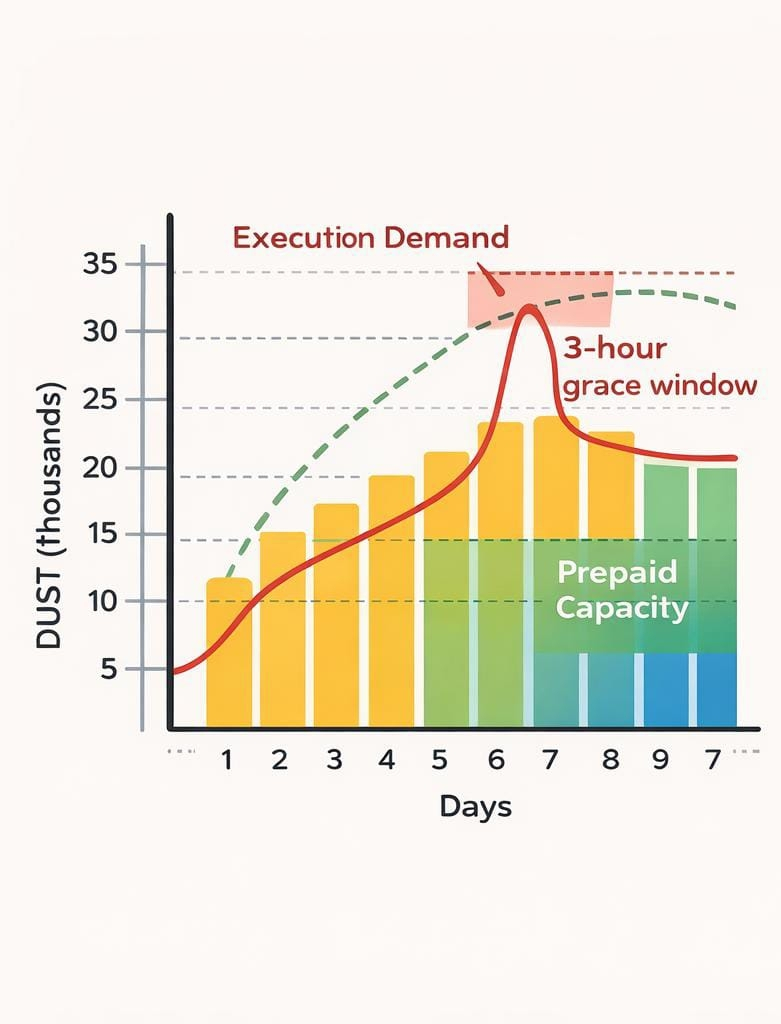
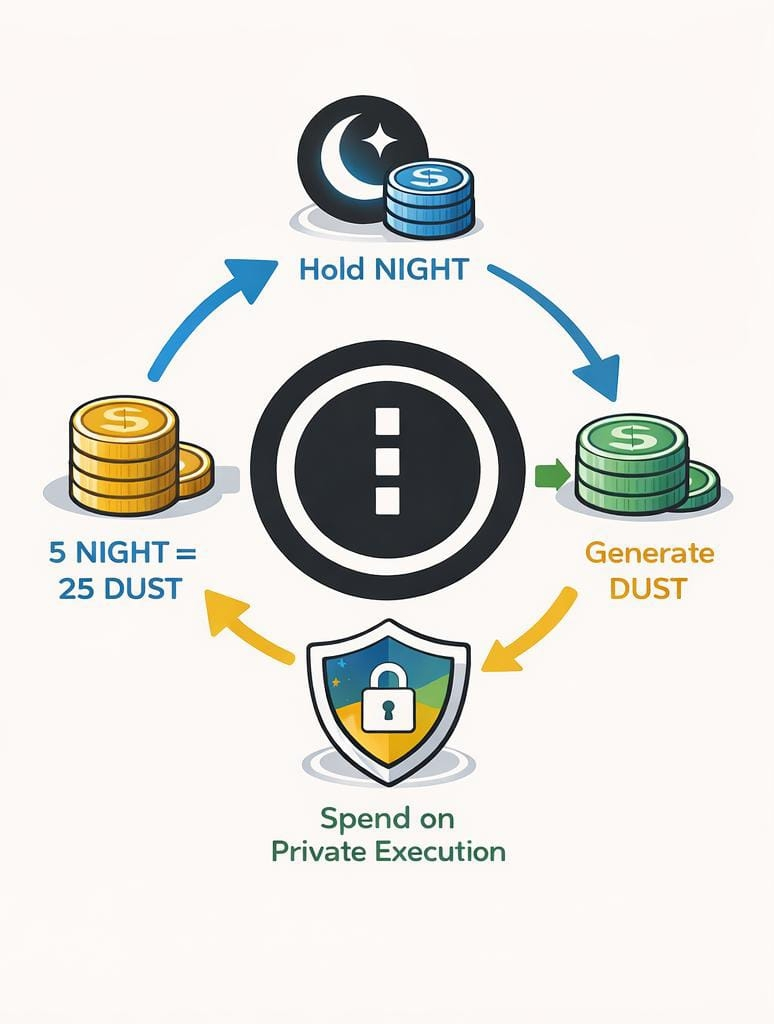
On the surface, the model appears straightforward. Hold NIGHT, generate DUST, spend it on private execution. With an initial ratio of roughly 5 DUST per $NIGHT Tand about a 7-day path to full capacity, it looks like a delayed gas system with softer visibility. The 3-hour grace window reinforces that impression, smoothing over timing mismatches.
Underneath, the structure is doing something more deliberate. By turning execution into a regenerating resource rather than a spot-priced fee, Midnight removes transactions from a live bidding environment. Instead of competing in a mempool, users operate within pre-shaped capacity limits. That shifts pressure from price discovery to resource planning.
This changes coordination. In a market where Ethereum still processes around 1 million daily transactions and fee spikes can cluster unpredictably, prepaid execution introduces a kind of temporal stability. If DUST accrues steadily, activity becomes bounded by prior commitment rather than immediate demand. That can reduce volatility in execution, but it also caps responsiveness.
The numbers quietly reveal the trade-off. A 7-day accumulation period implies that sudden demand cannot be absorbed instantly. The 3-hour buffer suggests the system anticipates latency, but not surges. And the fixed generation ratio anchors capacity to token holdings, which ties computation directly to capital allocation rather than usage intensity.
That linkage has economic consequences. In an environment where exchange liquidity for mid-cap tokens often fluctuates within a few million dollars daily, acquiring enough NIGHT to sustain consistent execution becomes a strategic decision. It favors actors who can plan ahead and hold inventory, rather than those reacting in real time.
Privacy, in this context, is not just concealment. It is a constraint on observability that requires the system to pre-commit resources. The architecture compensates by smoothing execution over time, but that smoothing introduces rigidity. Coordination becomes quieter, but also less flexible.
There is also a structural risk. If usage patterns shift faster than DUST can regenerate, the network may not congest visibly, but it will stall subtly. Instead of fee spikes, users encounter delayed execution or unmet capacity. That kind of friction is harder to price and easier to misinterpret.
This sits within a broader market moment. Institutional flows, including ETF-driven exposure, are pushing for predictable infrastructure, while developers are still experimenting with dynamic systems that adapt to demand. Midnight leans toward predictability, but it does so by constraining spontaneity.
The question is not whether it can scale in a raw throughput sense. It is whether a system built on prepaid, time-shaped execution can adapt to a market that increasingly moves in bursts. Privacy holds, but only because activity is disciplined before it happens.
What emerges is less a scaling solution and more a coordination philosophy. Midnight does not eliminate the cost of privacy. It moves that cost into time, and in doing so, it reveals that scaling private systems may depend less on speed and more on how tightly behavior can be structured in advance.#night