@SignOfficial #SignDigitalSovereignInfra $SIGN
There is a particular kind of fatigue that shows up in crypto when people stop talking about “the next big thing” and start asking more practical questions in small, impatient ways. They check eligibility before they check narratives. They care less about who is loud and more about whether the same wallet has been counted twice, whether a claim page actually matches the rules, and whether a distribution will still make sense after the initial excitement fades. That shift is easy to miss because it does not look like conviction. It looks like caution, and in this market caution often arrives after experience has already done its work.
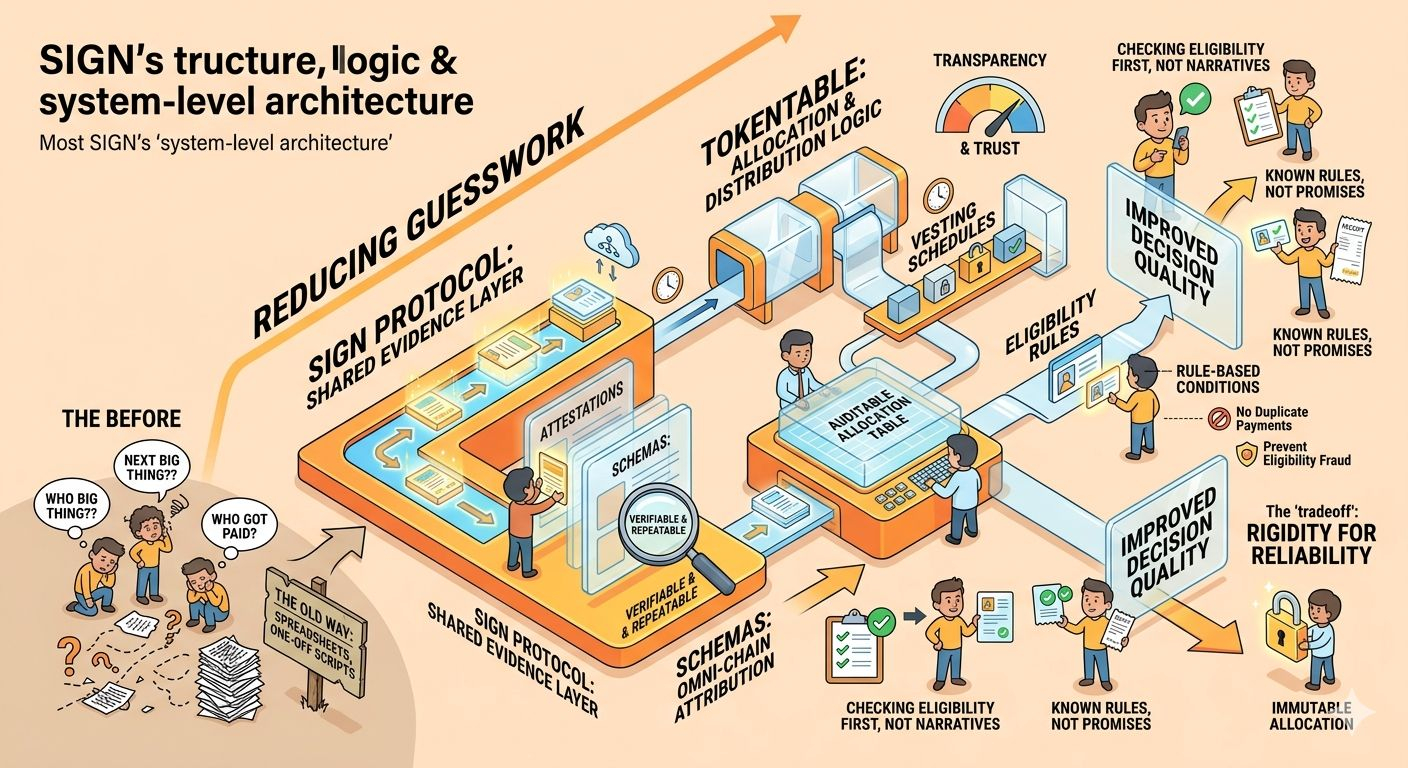
Seen from that angle, SIGN starts to look less like a single token story and more like an attempt to reduce the amount of guesswork people have to tolerate. The official framing is not just “credential verification” or “token distribution” in the abstract. Binance’s project summary describes Sign as global infrastructure for credential verification and token distribution, while the project’s own documentation frames S.I.G.N. as a system-level architecture for money, identity, and capital, with Sign Protocol acting as a shared evidence layer and TokenTable handling allocation and distribution logic. That matters because it suggests the project is trying to sit underneath behavior, not above it. It is aimed at the point where users ask, “Who said this is valid?” and “Why did this wallet get paid?” rather than at the point where they are already celebrating the outcome.
That distinction is more important than it first sounds. In crypto, distribution is never only a technical operation. It is a trust event. The moment tokens, rewards, vesting schedules, or eligibility rules are involved, the market starts reading the system as if it were also a statement about fairness. The official TokenTable docs are blunt about the failures of older methods: spreadsheets, manual reconciliation, opaque beneficiary lists, one-off scripts, and centralized processors are slow, error-prone, and vulnerable to duplicate payments, eligibility fraud, and weak accountability. TokenTable is presented as a deterministic and auditable replacement for that style of administration, with allocation tables, vesting schedules, revocation rules, and claim conditions built into the process itself.
That design choice has a practical consequence that is easy to underestimate. If distribution is rule-based, then the social argument around airdrops, subsidies, unlocks, or incentives becomes less about persuasion and more about the quality of the rules. People may complain less about favoritism, but they may complain more about rigidity. A system that is cleaner at scale can also feel less forgiving at the edge. If an allocation table is immutable once finalized, as the docs say, then the benefit is obvious: fewer discretionary changes, fewer hidden edits, and more predictability. The cost is that mistakes become harder to soften later. In other words, the design reduces ambiguity for users, but it also reduces the room for human correction after the fact. That is not a flaw so much as a tradeoff, and it is the kind of tradeoff that matters more as distribution volumes rise.
Sign Protocol appears to be carrying the verification side of that bargain. The documentation describes it as an omni-chain attestation protocol using schemas and attestations, with support for fully on-chain, fully off-chain, hybrid, and privacy-enhanced modes including private and ZK attestations where appropriate. In plain language, that means the project is trying to make claims portable and verifiable without forcing every sensitive detail into the open. The practical value of that is clear: users can prove something without necessarily exposing everything behind the proof, and builders can structure trust in a way that travels across systems instead of dying inside one application’s database.
I think that is where the market psychology gets interesting. A lot of crypto users say they want decentralization, but what they usually mean in practice is that they want fewer surprises. They want rules they can inspect, not just promises they have to accept. They want to know whether a claim is tied to a schema, whether a distribution can be audited, whether the evidence survives across chains, and whether a verification result is repeatable later. Sign’s documentation leans into that desire by emphasizing repeatable, attributable verification and by describing attestations as operational infrastructure rather than a vague trust primitive. That framing does not guarantee adoption, but it does speak to a real pain point: users are tired of systems that ask for trust before earning it.
At the same time, there is a risk in any infrastructure that claims to make trust easier. When verification becomes smoother, systems often become more selective about who can participate. That can be useful when the goal is to prevent abuse, duplicate claims, or broken compliance. It can also be uncomfortable when users expect permissionless behavior and instead encounter eligibility gates, credential checks, or policy logic they cannot easily override. Sign’s own docs acknowledge this through the emphasis on identity-linked targeting, revocation, supervisory visibility, and deployment modes that can be public, private, or hybrid depending on the use case. The consequence is that the system may be more usable for institutions and serious programs than for people who want pure spontaneity.
That is probably the clearest way to interpret the project without overreading it. SIGN does not look like a meme designed to attract attention for its own sake. It looks like an attempt to formalize three things crypto often handles badly at scale: who is eligible, what evidence proves it, and how value moves once eligibility is established. In the best case, that lowers the amount of detective work ordinary users have to do. In the worse case, it can create a more legible but also more constrained environment, where everything is tracked neatly and very little is left to interpretation. Both outcomes are possible, and the difference will depend less on slogans than on how the system behaves when it encounters edge cases, disputes, and operational pressure.
What makes this topic worth watching, especially for everyday crypto participants, is that it points toward a more mature kind of market behavior. The most useful infrastructure is often invisible when it works and painfully obvious when it fails. If SIGN’s approach holds up, the benefit is not just cleaner token distribution or neater credential checks. It is better decision quality for users who are trying to separate real participation from empty noise. It is more stable expectations around eligibility and unlocks. It is less confusion around why something happened. And in crypto, where confusion is often mistaken for opportunity, anything that reduces uncertainty without pretending to eliminate it is probably more valuable than it first appears.