The Credential Verified. The Issuer Was the Problem.
The eligibility list was already built when someone asked who had approved the issuer.
Not the credential.
The issuer.
Up to that point, the workflow had been clean in the way Sign workflows often look clean early. Sign’s attestation registry already held the eligibility records. The credentials were signed properly. Sign’s verification layer accepted them without trouble. When the distribution moved into execution, Sign’s TokenTable allocation engine read those attestations and mapped the payout set from them.
Nothing looked stuck.
The records verified.
The list populated.
The allocations were there.
Then one funding partner stopped at the same credential everyone else had already accepted and asked a worse question than “is it valid?”
Why does this issuer get to decide who qualifies?
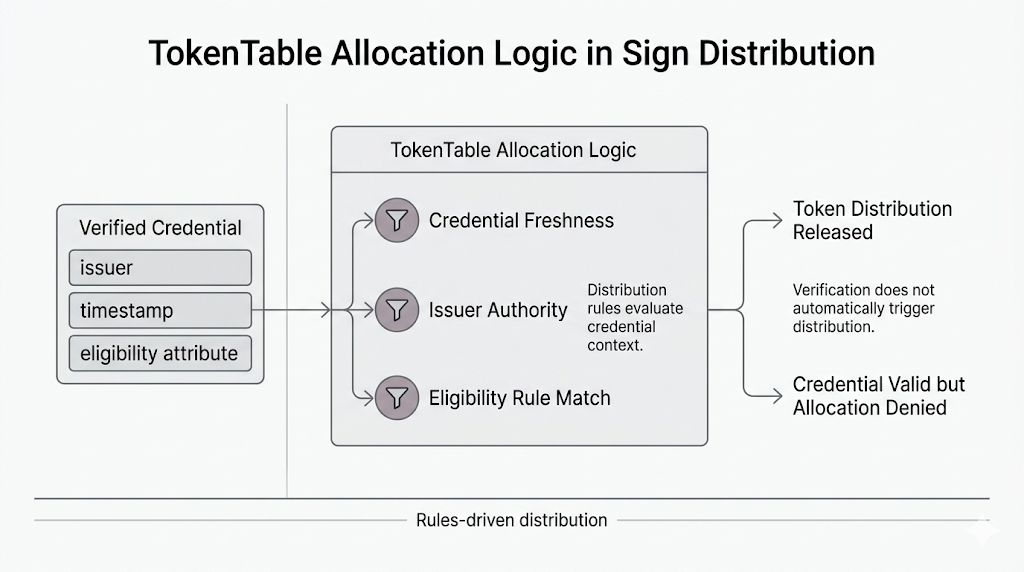
That landed badly because the system did not have a technical problem to point at. The credential inside Sign’s attestation registry was real. The signature was valid. The attestation format matched. TokenTable had used it exactly the way the distribution logic said it should.
The issue showed up only when value was about to move.
A participant had a valid eligibility credential issued through Sign’s attestation layer. Verification rules treated it as usable input. TokenTable treated it as enough to place that participant inside the qualifying set.
Then the objection arrived late: the program had never fully settled whether that issuer belonged on the list of entities allowed to shape distribution eligibility in the first place.
That is a rough place for a workflow to realize what it missed.
Because now the credential still verifies. The participant still appears properly in the system. The allocation logic still points in the same direction. The only thing that changed is that one institution no longer wants to inherit the issuer’s judgment.
So what exactly gets rolled back?
Not the attestation.
Not the verification result.
Not the logic TokenTable used.
What stalls is the trust that was quietly sitting underneath the whole pipeline.
And that is where Sign gets more interesting than the cleaner pitch suggests.
Sign’s attestation infrastructure can carry the issuer’s claim cleanly across systems. The verification layer can prove that claim is authentic. Sign’s TokenTable distribution logic can turn that verified record into an allocation path without dragging the program back into manual review.
That all works.
Until somebody notices that a funding workflow was treating issuer authority as if it came bundled inside credential validity.
It doesn’t.
Not automatically.
Now the program has a beneficiary list built from records that still verify and an institution asking whether those records should ever have counted for payout at all.
Freeze the distribution?
Remove the affected beneficiaries even though their credentials still pass under Sign’s rules?
Let the allocations stand because TokenTable only knows what to do with valid attestations, not late hesitation about the issuer behind them?
That is the part that does not feel solved just because the credential verifies cleanly.
A signed credential inside Sign Protocol can be perfectly usable at the protocol level and still trigger a fight the moment distribution depends on it. Not because the record is fake. Not because Sign’s verification layer failed. Just because the workflow answered authenticity first and left issuer authority sitting there until it became expensive.
By then the payout set may already exist.
And the question nobody answered early enough is the only one left:
who was actually trusting the issuer on behalf of the distribution program?