They treated privacy as absolute.
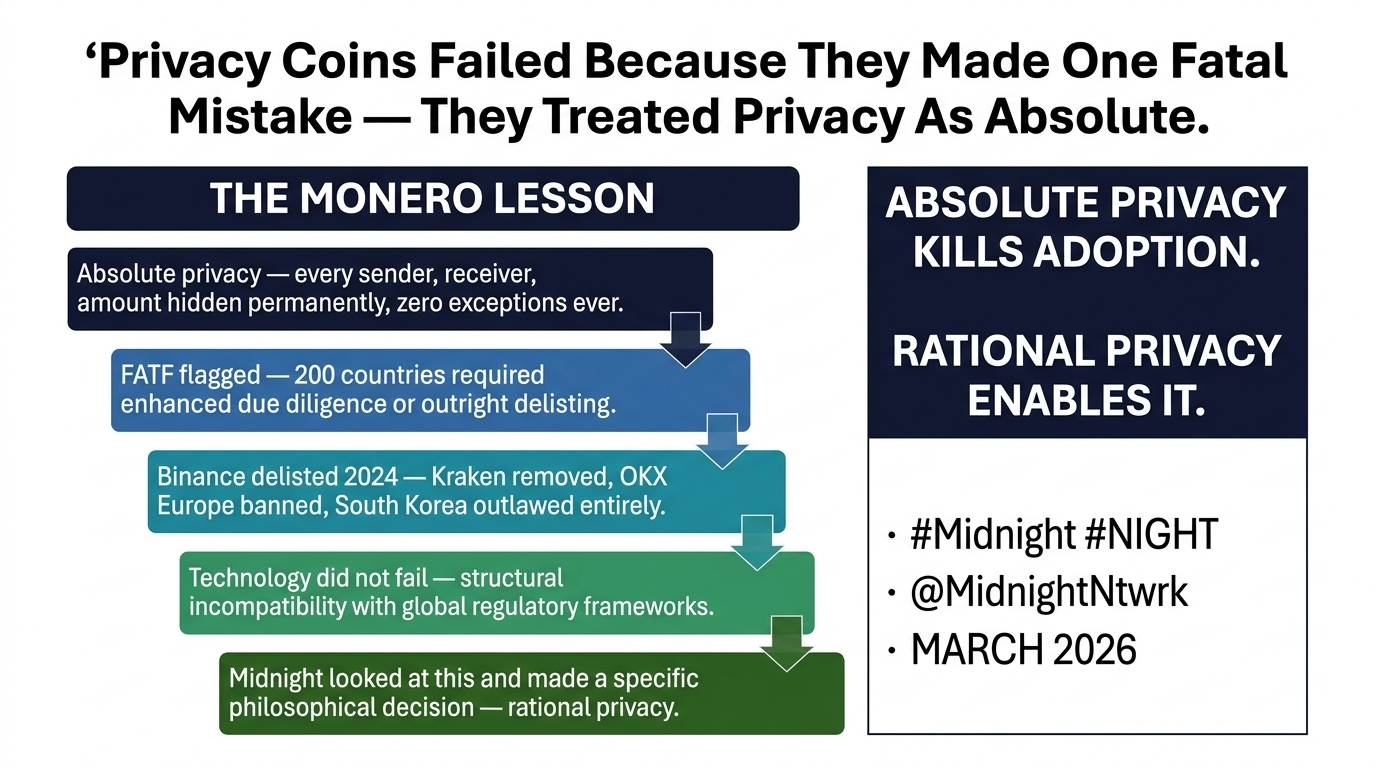
Monero was built on a simple idea — hide everything. Every sender, every receiver, every amount. Completely private, permanently hidden, and impossible to trace. On the surface, that sounds like the ultimate form of financial privacy. And for a certain group of users, it genuinely is. Journalists protecting their sources, activists operating under surveillance, individuals living in restrictive regimes — for them, absolute privacy is not a luxury, it’s a necessity.
But what works perfectly in theory does not always scale in reality.#night @MidnightNetwork $NIGHT
Because financial systems don’t exist in isolation. They operate within legal frameworks, regulatory expectations, and global compliance standards. And this is exactly where the model of absolute privacy begins to break down.
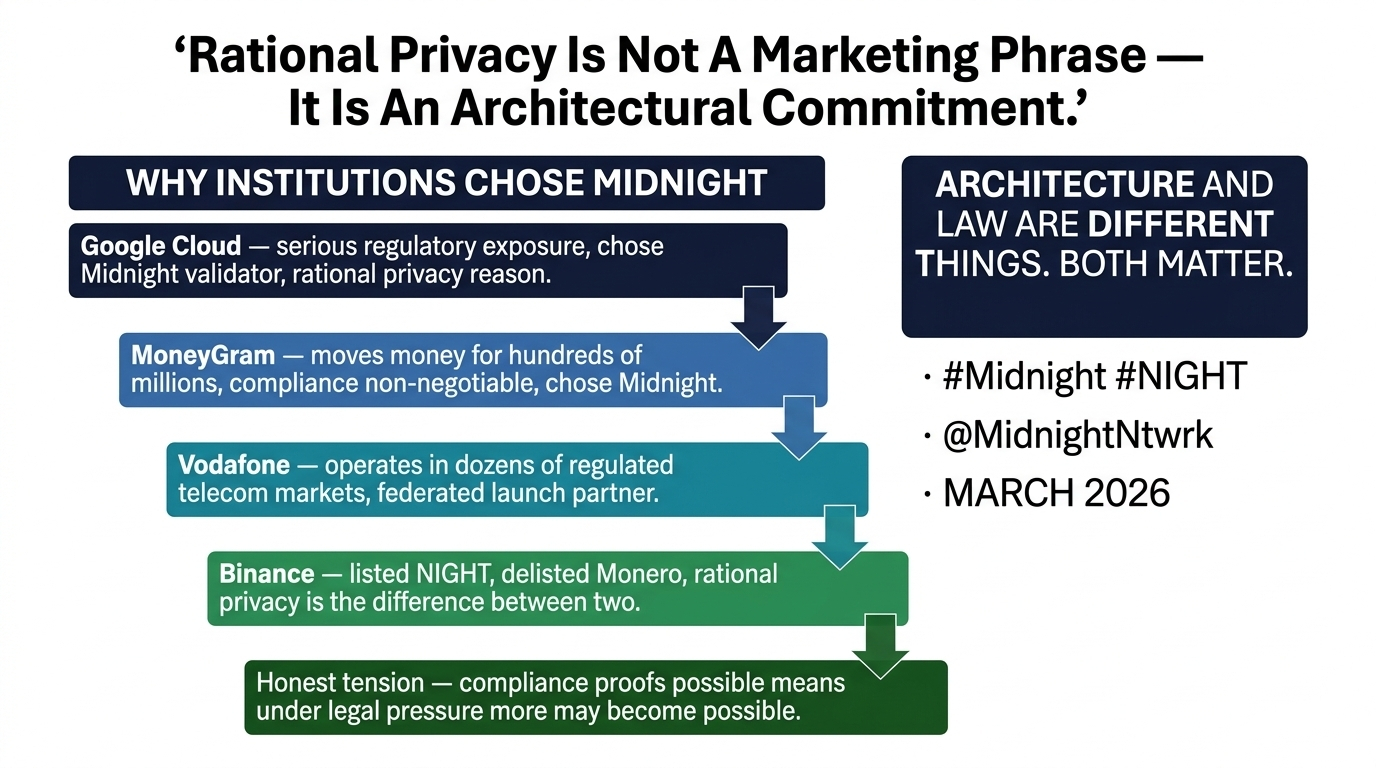
Over the past few years, the pattern has been clear. Exchanges became cautious. Regulatory scrutiny increased. Entire jurisdictions started placing restrictions on assets that could not provide any level of traceability. Not because the technology behind them was flawed — but because a system where transactions can never be audited under any circumstance does not align with how modern financial systems operate.
This is the uncomfortable truth that the industry had to face.
Absolute privacy and regulatory compliance are not natural allies.
That tension is what defines the next phase of blockchain adoption.
And it is exactly where a different approach begins to emerge.
Midnight does not try to compete on maximum privacy.
Instead, it tries to solve for usable privacy.
They describe this approach as rational privacy — and the distinction matters more than it seems.
Rational privacy is not about hiding everything at all costs. It is about protecting sensitive data while still allowing systems to function within real-world constraints. It acknowledges that privacy and compliance are not binary choices, but variables that can be designed into the system itself.
At the core of this approach is the use of zero-knowledge proofs.
On Midnight, transactions are shielded by default. The sender, the receiver, the amount, and all associated metadata remain hidden. The network verifies that a transaction is valid, but it does so without revealing the underlying data. This is not obfuscation or mixing — it is mathematically enforced privacy.
But what makes the system fundamentally different is what comes next.
The same cryptographic structure that enables privacy also enables selective disclosure.
This means that under specific conditions, a user or an institution can generate a proof that a transaction meets certain requirements — without exposing the transaction itself. A regulator can verify compliance. A business can prove legitimacy. But the detailed data remains private.
This is a subtle but powerful shift.
Instead of choosing between full transparency and full opacity, the system allows for controlled visibility.
Only what needs to be revealed is revealed.
Nothing more.
This architectural flexibility is what allows privacy to exist within systems that still require accountability.
It is also what separates this approach from earlier privacy-focused designs.
In systems built around absolute privacy, there is no way to selectively reveal information. Everything is hidden, always. While that maximizes privacy, it removes the ability to interact with environments that require even minimal levels of compliance.
Rational privacy introduces nuance.
And in complex systems, nuance matters.
Another important element in this design is the concept of DUST.
DUST is shielded, but it is not transferable. It cannot be sent between wallets. It cannot be traded on an exchange. It cannot function as a store of value. At first glance, this might seem like a limitation. But in reality, it addresses one of the core concerns regulators have with privacy-based systems.
If an asset cannot be transferred freely, it cannot be used in the same way as traditional privacy coins. It cannot be moved across accounts to obscure ownership. It cannot be used to layer transactions in a way that hides origin. In simple terms, it removes the primary mechanism through which misuse typically occurs.
This design choice reflects a deeper understanding of the problem.
The goal is not just to create privacy.
The goal is to create privacy that can exist within a regulated environment.
That difference is critical.
Because the future of blockchain adoption is not determined solely by what is technically possible. It is shaped by what is deployable at scale, within the systems that already exist.
And those systems have rules.
Midnight’s approach acknowledges those rules — not as limitations, but as design constraints.
Of course, this approach is not without trade-offs.
Every system that allows for selective disclosure introduces the possibility — however controlled — that information could be revealed under certain conditions. Absolute privacy removes that possibility entirely. Rational privacy manages it.
This is the core philosophical divide.
Do you build for maximum theoretical privacy, knowing it may limit real-world adoption?
Or do you design for practical deployment, accepting that some flexibility is required?
Midnight is clearly betting on the second path.
It is building for a world where blockchain applications interact with governments, institutions, and regulated entities. A world where privacy is necessary, but total opacity is not always viable.
And that bet reflects a broader shift in the industry.
The conversation is no longer just about decentralization versus control.
It is about integration versus isolation.
Systems that isolate themselves may achieve purity.
But systems that integrate tend to achieve scale.
Rational privacy sits at that intersection.
It does not reject regulation.
It does not fully surrender to it either.
It creates a middle ground where both can coexist — not perfectly, but practically.
And in the long run, practicality is what determines adoption.
The history of technology is full of examples where the most extreme version of an idea did not win. Instead, the version that balanced competing forces — usability and power, freedom and structure — is the one that scaled.
Blockchain is now entering that phase.
The infrastructure is maturing. The use cases are expanding. And the expectations are shifting from experimentation to real-world impact.
In that environment, the question is no longer just how private a system can be.
The question is how well that privacy can function in the world as it exists today.
Midnight’s answer is not absolute.
It is rational.

And based on how the space has evolved over the past few years, that distinction may turn out to be more important than most people realize. 🌑