Nobody really thinks about what happens when they hand over their passport at a border.
From the traveler’s perspective, the process looks simple. A document is scanned. A system runs a check. Within seconds, a decision is made — proceed or stop. It feels routine, almost invisible.#Sign @SignOfficial $SIGN

But behind that simplicity sits one of the most complex data-sharing systems in the world.
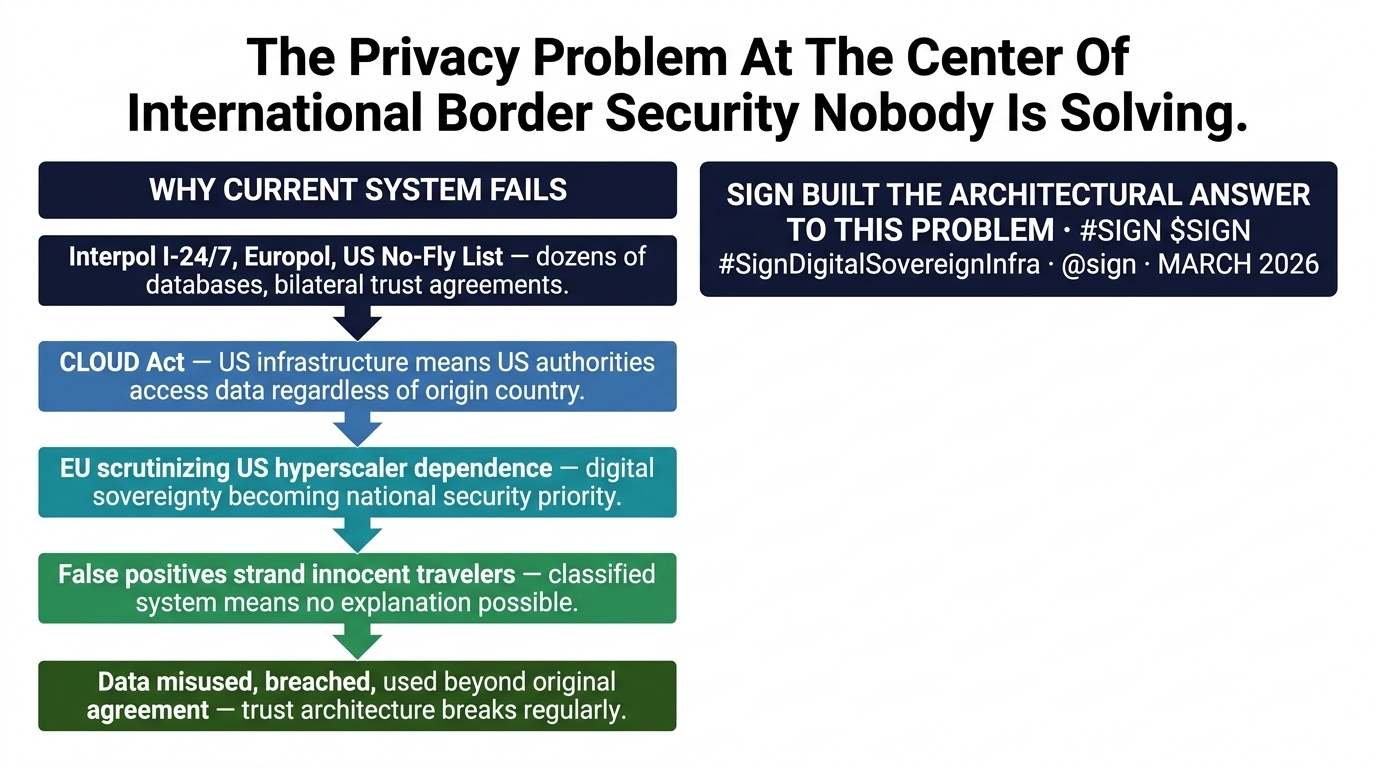
Every time a passport is scanned, it is checked against multiple layers of global databases. These include national security watchlists, international criminal records, sanctions databases, and intelligence-sharing networks built through decades of cooperation. Organizations and frameworks coordinate this flow of information across borders, allowing countries to identify risks in real time.
The system works because of one thing: data sharing.
But that is also where the problem begins.
Every time one country shares sensitive security information with another, it gives up a degree of control over that data. Once transferred, the original owner cannot fully dictate how that information is stored, who can access it, how long it is retained, or how it might be used in the future. Even with strict agreements in place, the reality is that enforcement depends heavily on trust.
And trust, especially at the scale of international systems, is never perfect.
This creates a structural tension at the heart of global security cooperation.
On one hand, sharing information is necessary. A watchlist is only effective if it can be accessed at the borders where it matters. If data remains isolated within a single country, its usefulness drops significantly.
On the other hand, sharing that same data introduces risks. Sensitive intelligence can be exposed through breaches, misused by insiders, or applied beyond its original purpose. In some cases, individuals may be flagged incorrectly, and because the underlying data is classified, they have little visibility into why it happened or how to resolve it.
This dual reality — where transparency is required for security but dangerous for privacy — has shaped how these systems operate today.
Most current solutions rely on layered controls. Access restrictions, audit logs, legal agreements, and bilateral frameworks are used to manage risk. But these are fundamentally policy-based solutions. They depend on human oversight and institutional discipline.
When those systems fail, the consequences are real.
Data leaks have exposed sensitive records in the past. False positives have left travelers stranded without explanation. Entire databases have been criticized for lack of accountability or transparency.
The system works, but not perfectly.
And more importantly, it was never designed to fully solve this tension.
That is where a different approach begins to emerge.
Instead of asking how to better control shared data, what if the system was designed in a way that minimizes the need to share it in the first place?
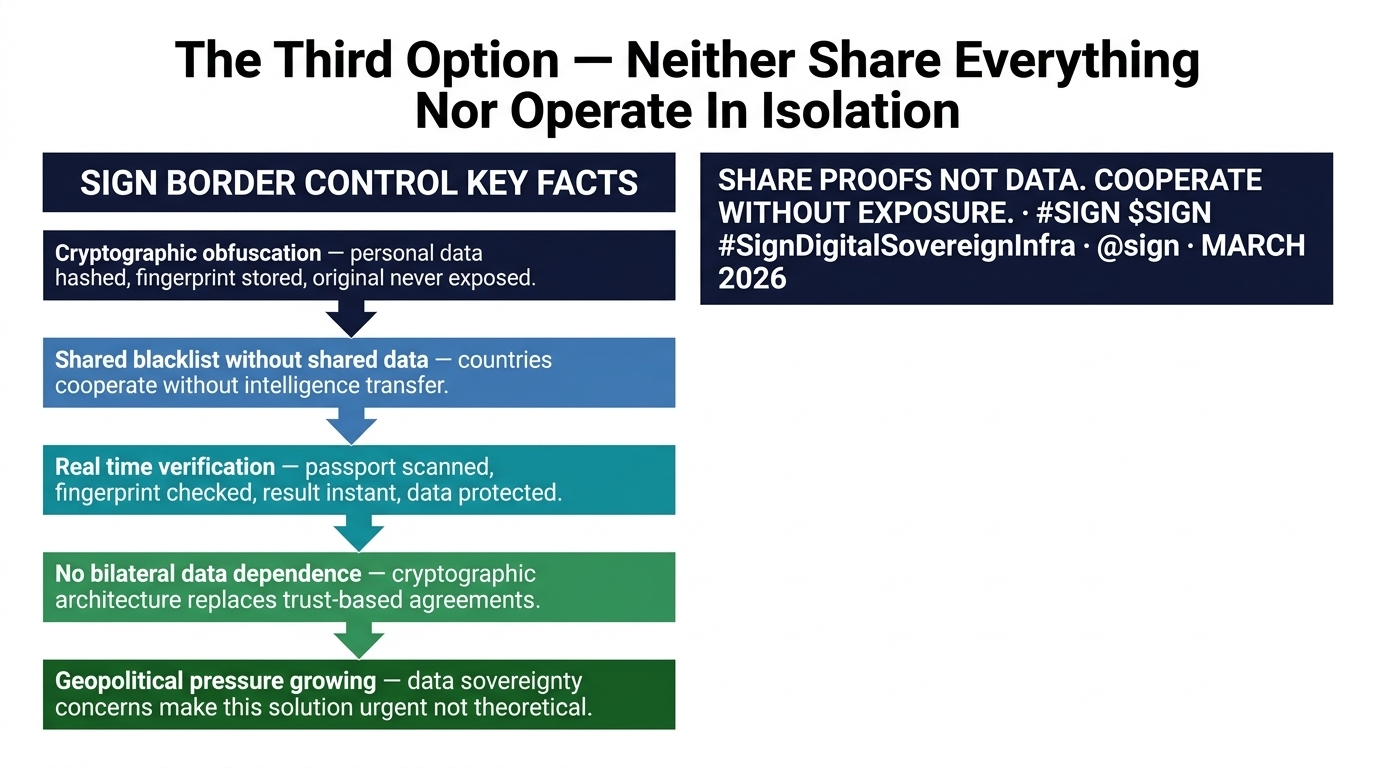
This is the architectural shift introduced by Sign’s border control framework.
Rather than transferring raw personal data across systems, the framework relies on cryptographic representations of that data.
Personal identifiers — such as names, passport numbers, or even biometric markers — are converted into hashed values. These hashes act as unique fingerprints, representing the original data without revealing it. The actual personal information remains with the originating country and is never directly exposed during the verification process.
When a border agent scans a passport, the system does not retrieve a database record containing personal details. Instead, it generates a cryptographic fingerprint from the scanned data and checks whether that fingerprint matches any entry in a shared security list.
If there is a match, the system flags it.
If there is no match, nothing else is revealed.
The agent does not see additional personal information. The system does not expose underlying data. The verification happens without unnecessary disclosure.
This changes the nature of data sharing entirely.
Countries can contribute entries to a shared blacklist without exposing the full intelligence behind those entries. At the same time, other countries can verify travelers against that list without gaining access to sensitive source data.
In other words, cooperation continues — but control over data is retained.
This is a fundamental shift from trust-based systems to architecture-based guarantees.
Instead of relying on agreements that data will be handled properly, the system is designed so that misuse becomes significantly more difficult at a technical level. The need for trust is reduced, not by eliminating cooperation, but by redefining how that cooperation works.
The implications of this approach extend beyond border control.
In a world where digital sovereignty is becoming increasingly important, countries are paying closer attention to where their data resides and who ultimately controls it. Questions around data jurisdiction, cross-border access, and external dependencies are no longer theoretical — they are central to national security strategies.
Many governments are already re-evaluating their reliance on foreign infrastructure providers and external data systems. The idea of maintaining control over sensitive national data while still participating in global networks is gaining momentum.
This is exactly the space where architectures like this become relevant.
They offer a third option.
Traditionally, countries have had to choose between two models: share data openly and accept the associated risks, or restrict sharing and reduce the effectiveness of cooperation.
A cryptographic approach introduces a middle path.
Data does not need to be fully shared, and it does not need to be fully isolated. Instead, only the minimum necessary information — in this case, a verifiable match or non-match — is exchanged.
This allows systems to function effectively without exposing more than what is required.
Of course, moving from theory to implementation is not simple.
Existing border control systems are deeply integrated into national infrastructure. Replacing or even modifying them involves regulatory approval, technical integration, and coordination across multiple agencies. International cooperation frameworks evolve slowly, and large-scale changes require time.
No country is going to overhaul its border systems overnight.
But the direction of pressure is clear.
The need for international security cooperation is not decreasing. At the same time, concerns around data privacy, sovereignty, and control are increasing. These two forces are moving in opposite directions, creating a gap that current systems struggle to bridge.
Architectural solutions like this attempt to close that gap.
They do not eliminate the need for cooperation, nor do they remove the complexity of global security systems. But they change the way those systems handle one of their most sensitive components: data.
By reducing exposure, they reduce risk.
By limiting access, they increase control.
And by embedding these properties into the design itself, they move beyond the limitations of policy-based approaches.
The broader question is not whether such systems are technically feasible.
It is whether institutions are willing to adopt them.
Technology can provide new options, but adoption depends on alignment with political, regulatory, and operational realities. Governments move carefully, especially when dealing with critical infrastructure.
Yet, as pressures continue to build, the demand for solutions that balance cooperation and sovereignty will only grow.
The current model — built on trust and data sharing — has reached its limits in certain areas.
What comes next will likely be defined by how effectively systems can operate without overexposing the data they depend on.
Sign’s framework represents one possible direction.
It does not remove the complexity of global security systems.
But it offers a different way to handle one of their most fundamental challenges.
And in a world where control over data is becoming as important as access to it, that shift may matter more than most people realize. 🔥