I was deep in a verification flow this afternoon when one credential kept passing in a way that didn't feel complete.
Everything checked out.
Issuer.
Schema.
Timestamp.
Nothing failed.
Still didn't sit right.
So I tried to trace it back.
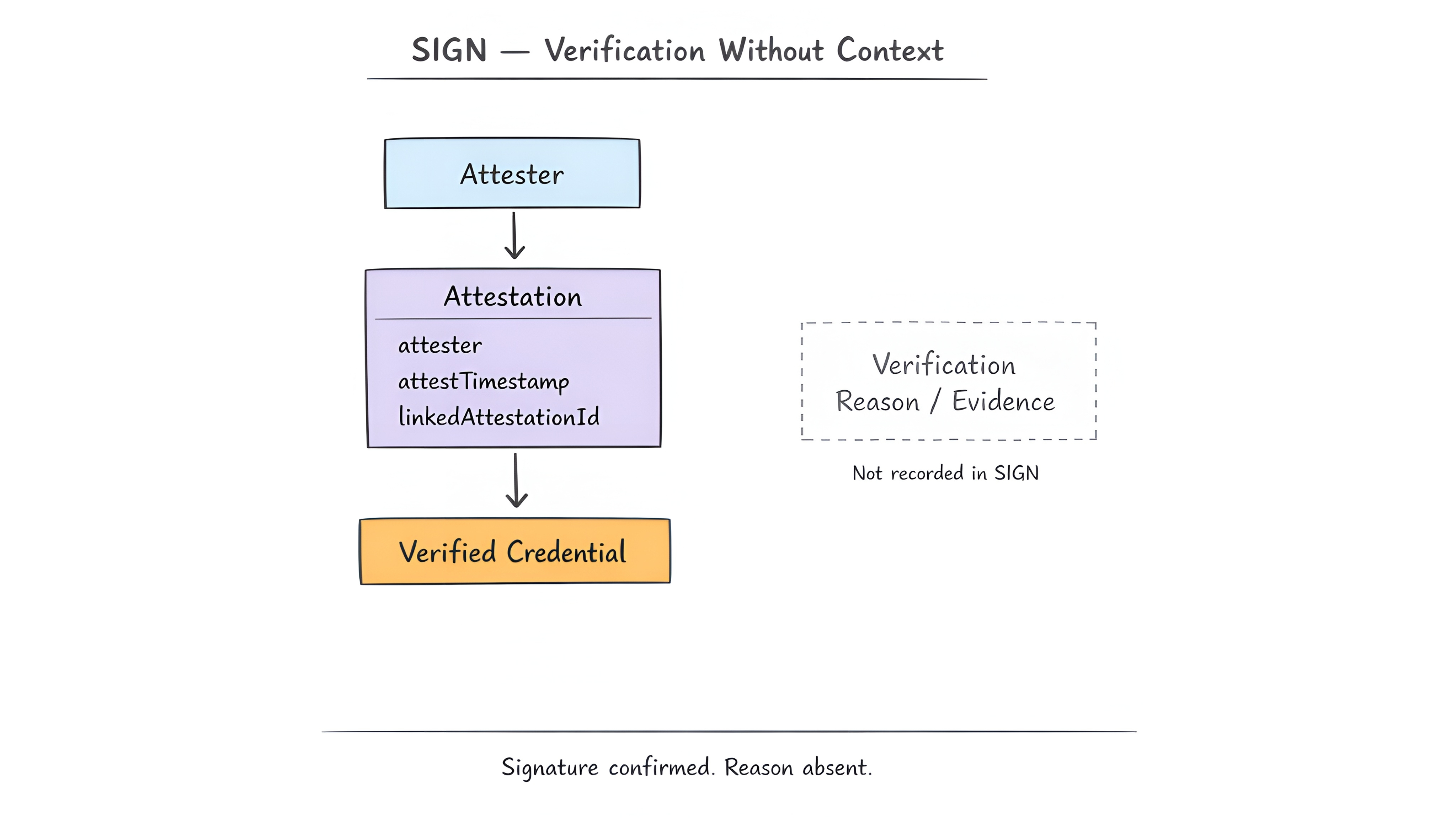
Started with the attester.
Then attestTimestamp.
Then whatever came before it.
There wasn't anything there.
I thought I skipped something obvious.
Checked it again.
Same result.
Went straight to linkedAttestationId.
It pointed back.
That one passed too.
I followed it again and stopped halfway.
Didn't expect the same thing to show up again.
But it did.
Each step confirmed the previous one.
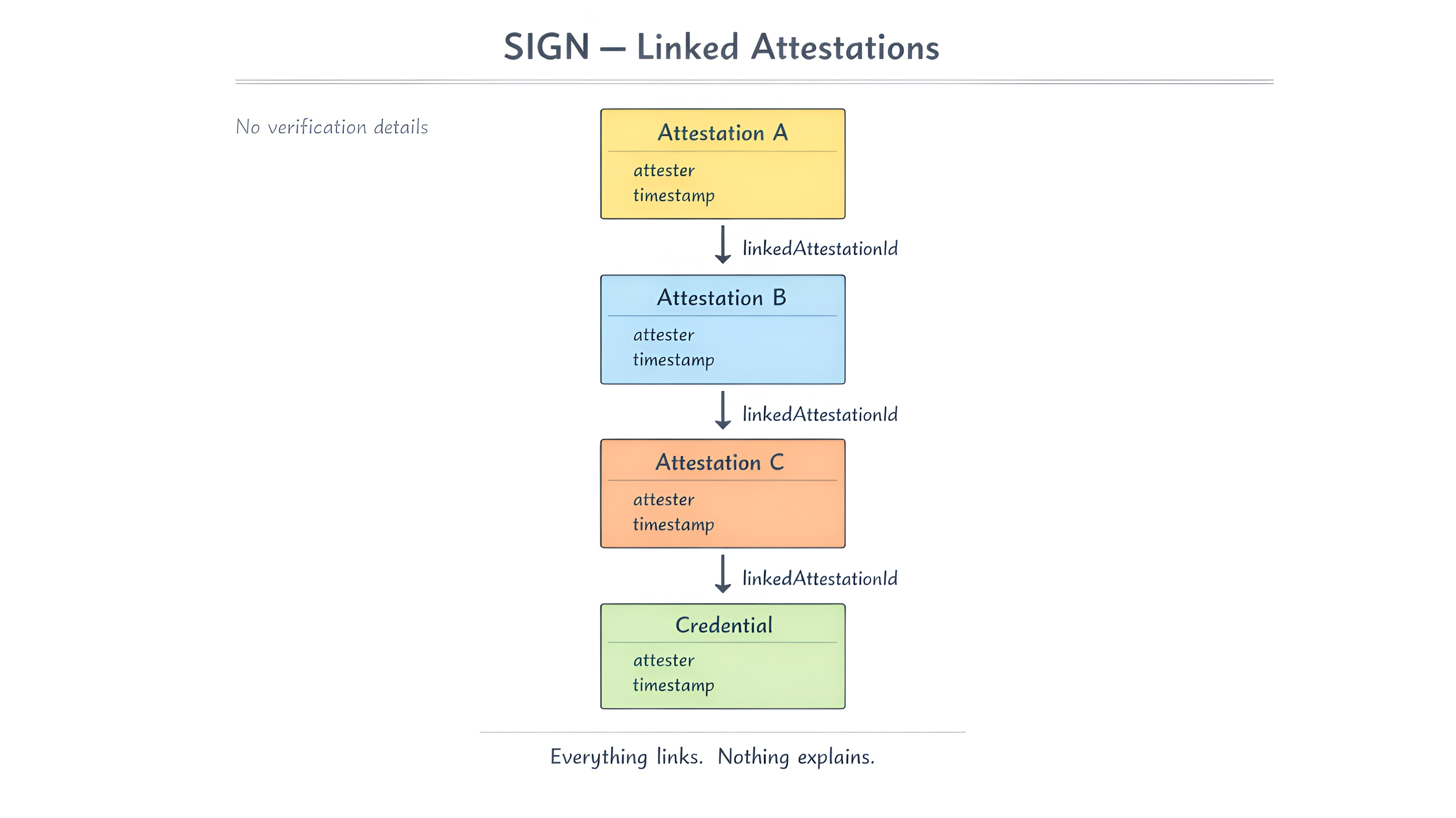
No trace of what was actually checked.
I stayed on it longer than I meant to.
Tried a different credential.
Different issuer.
Same pattern.
Everything resolves.
Nothing explains.
I wasn't sure what I was missing.
So I stepped away for a bit and came back later.
Still the same.
That's when it clicked.
Context void.
It kept confirming the signature.
Never what led to it.
attester is recorded.
attestTimestamp is recorded.
linkedAttestationId connects claims.
But none of it shows what was actually checked.
I kept going back through the chain.
Expecting something to show up.
It never did.
The reasoning wasn't missing.
It just... wasn’t there.
From the outside, it looks complete.
Every part resolves cleanly.
Inside, the cause is gone.
After that, everything started to look equally valid.
Careful checks.
No checks.
Same result.
I kept thinking about where this breaks.
It doesn't break at verification.
That's the problem.
I couldn't reconstruct the decision.
Only the signature.
Disputes don't have anything to reference.
When a credential gets challenged the only thing the attester can point to is the attestation itself.
The chain confirms the chain.
No external reference point.
Audits don't have anything to rebuild.
A compliance check asks what the issuer verified before signing.
The attestation shows it was issued.
The process that justified that issuance is permanently absent.
Everything points to the credential.
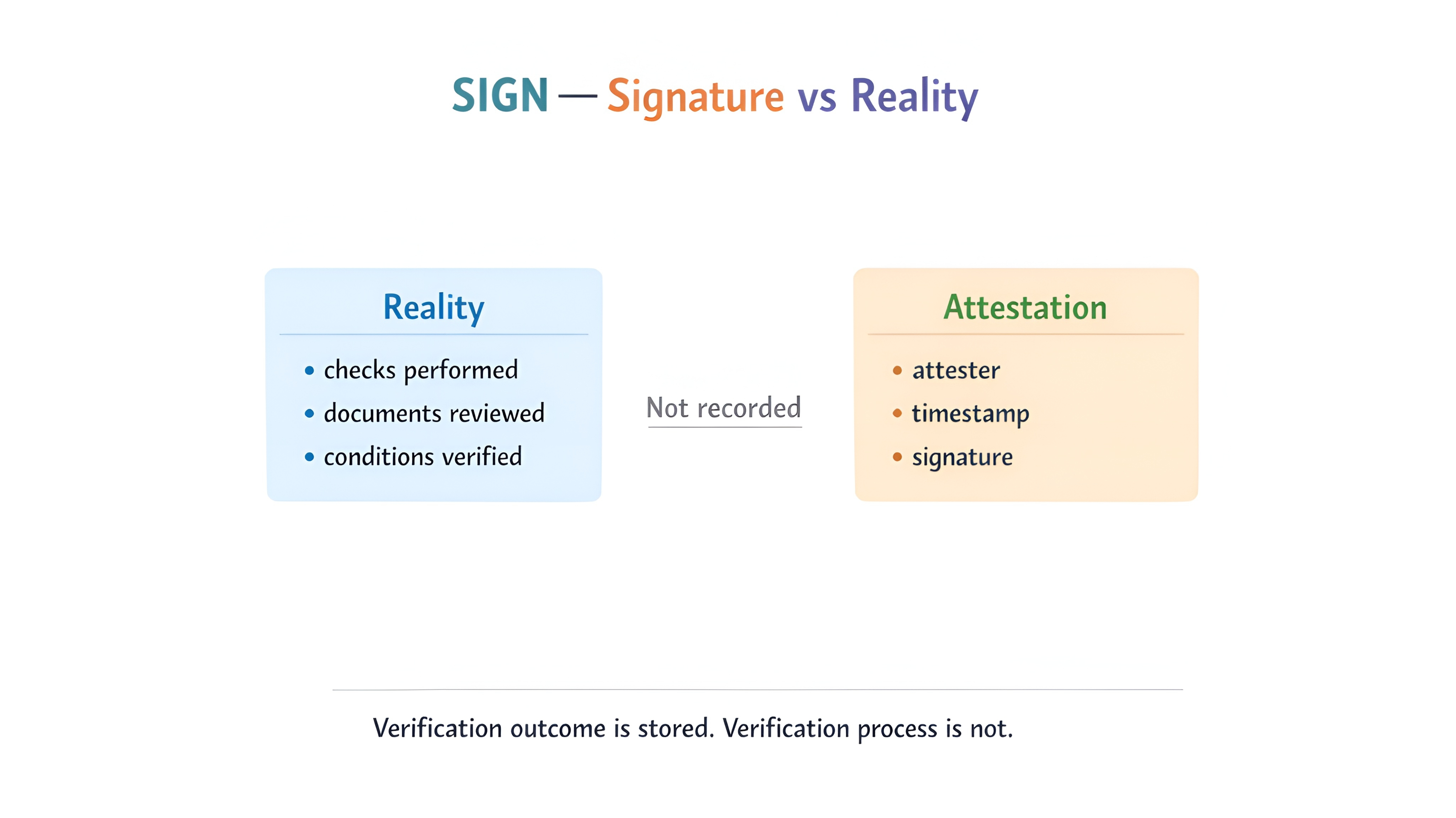
Nothing points to how it came to exist.
As more systems depend on that they inherit the same blind spot.
They trust the output.
Without ever seeing the process.
$SIGN only matters if what attester verified at attestTimestamp can be reconstructed, not just linked through linkedAttestationId.
Because once that layer is missing valid stops meaning correct.
It just means accepted.
So the real test becomes this.
If two credentials both verify perfectly and only one of them was actually checked, does the system give you any way to tell which one is real?