@SignOfficial $SIGN #SignDigitalSovereignInfra
I didn’t expect verification to feel this complicated, but the more I look at @SignOfficial , the more I keep coming back to one thought — verification used to be a moment, and now it’s becoming something that stays.
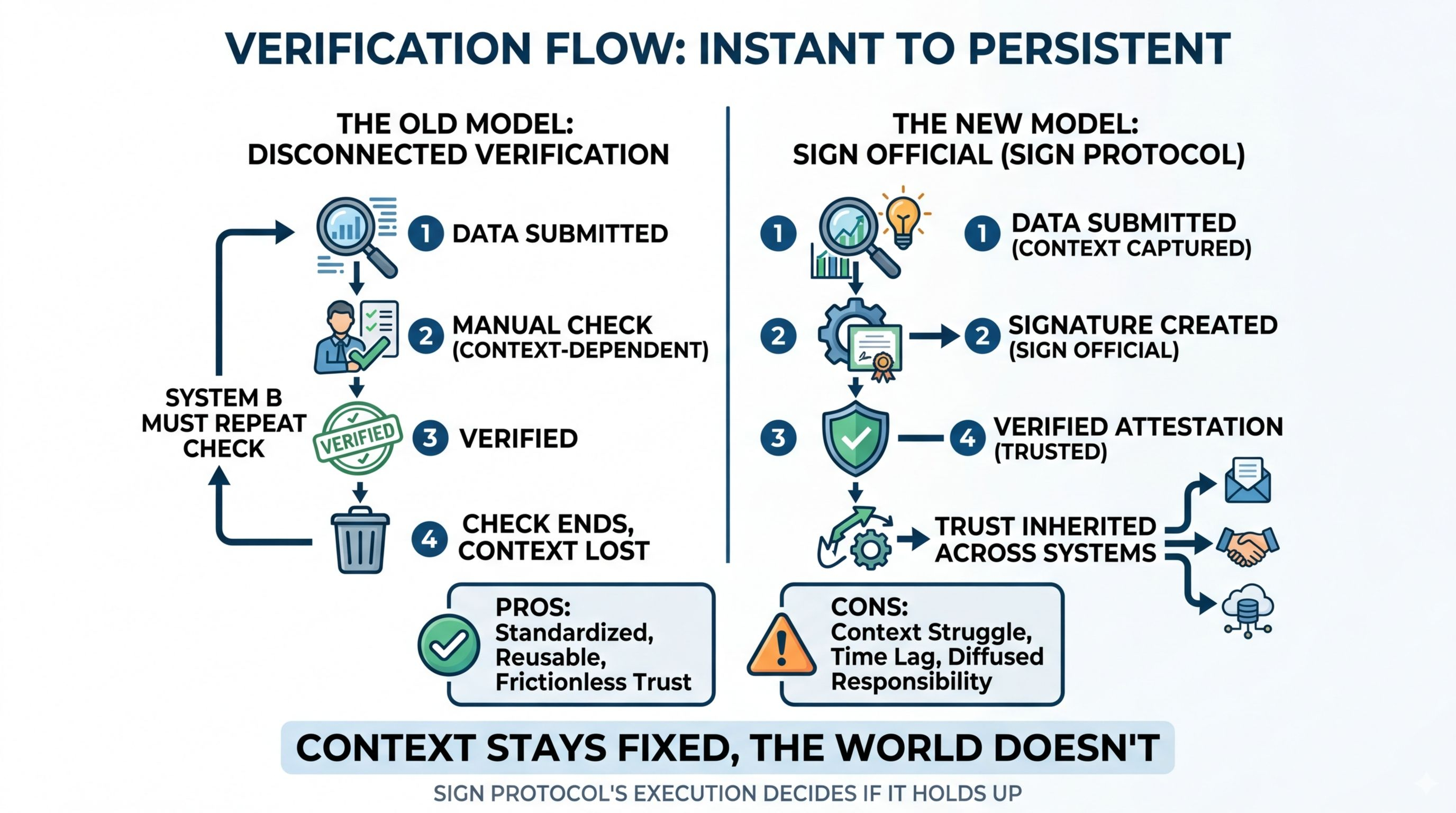
In most systems, you check something, confirm it, and move on. It belongs to that specific time and context. But Sign Protocol changes that flow. An attestation is created once, verified once, and then it keeps moving across systems like it already carries trust with it. On the surface, that feels efficient. It removes repetition, reduces friction, and makes everything smoother.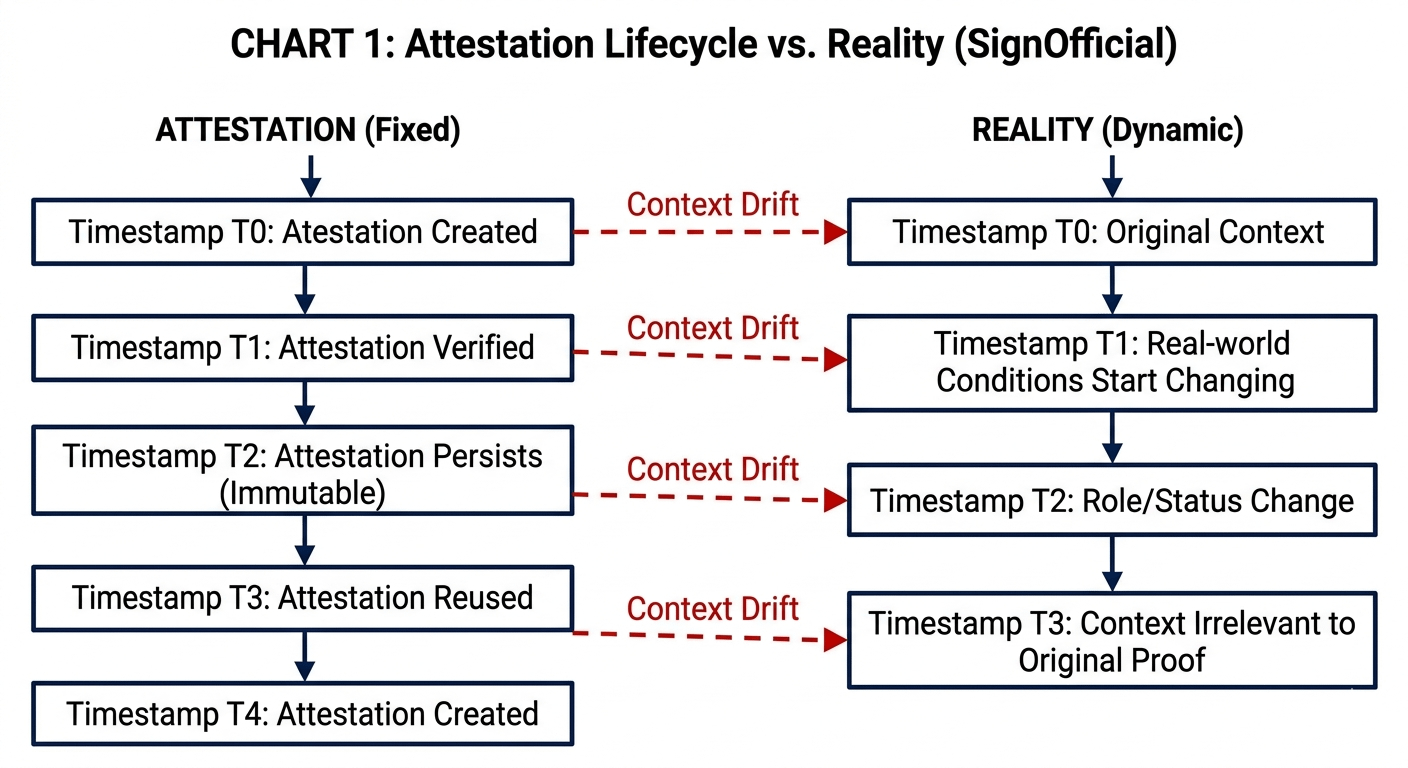
But I can’t ignore what gets left behind.
Because while the proof travels, the conditions don’t. The exact rules under which something was verified, the environment it was created in, the assumptions that shaped it — none of that moves forward. Only the result does. And that creates a quiet gap that’s easy to miss.
When I see a verified attestation in this kind of system, I’m not actually verifying anything myself. I’m trusting that someone else did it correctly, at some point in time, under conditions I might not fully understand. That shift feels small, but it changes the nature of trust completely.
We don’t verify anymore. We inherit trust.
Technically, Sign is doing something strong here. It standardizes verification, makes it reusable, and allows different systems to interact without constantly repeating the same checks. That’s useful. Clearly useful. But the real issue isn’t whether it works — it’s how it gets interpreted.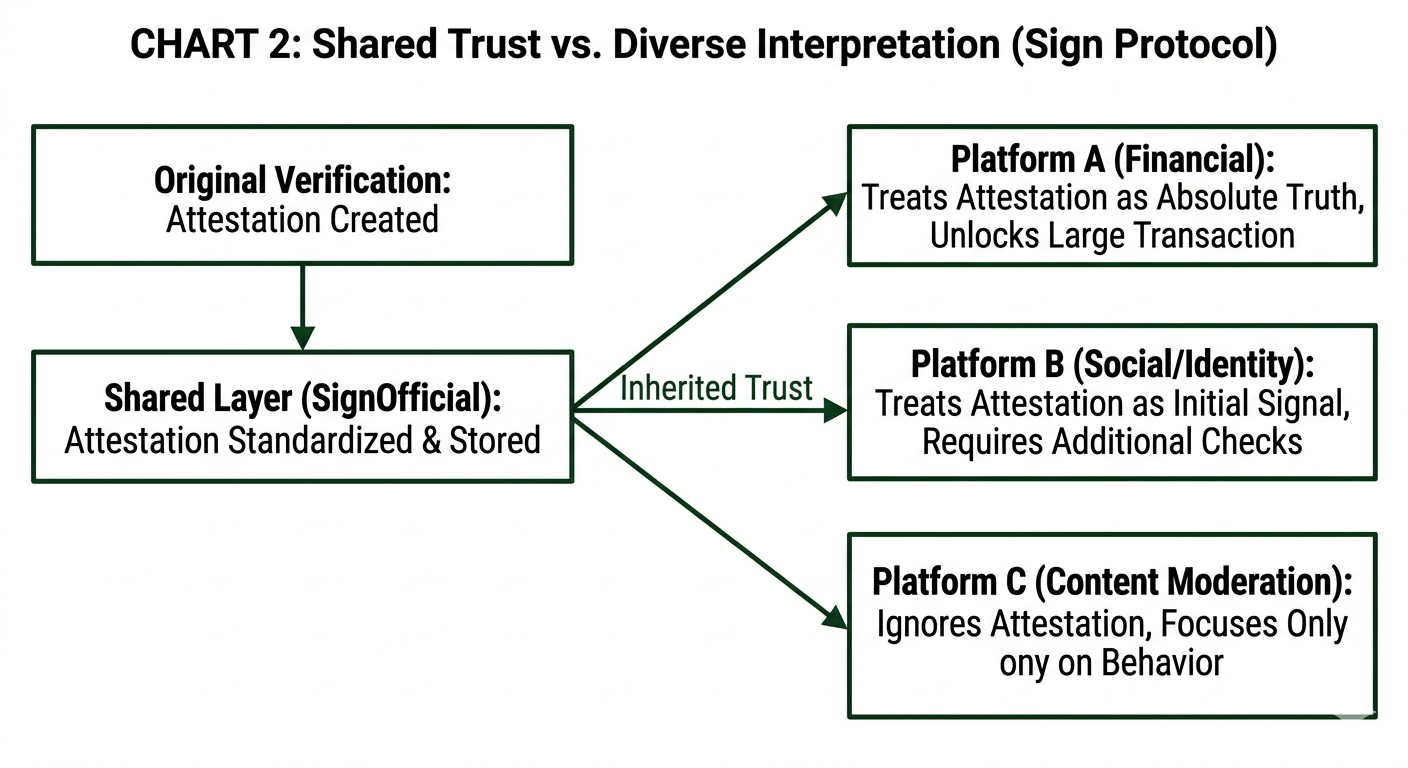
Because not every system treats a proof the same way. One platform might see an attestation as final truth, while another might treat it as just one signal among many. The same verification can lead to different outcomes depending on where it lands. That’s not a technical flaw. It’s a coordination problem.
And then there’s time, which complicates everything further.
Verification on-chain feels permanent, but reality isn’t. People change, roles change, and context changes. Something that was valid six months ago might not carry the same meaning today, yet the attestation still exists, still moves, still gets used. It doesn’t update itself. It doesn’t adapt.
The proof stays fixed. The world doesn’t.
That’s where things start to feel less certain. Because a system like SignOfficial isn’t just making verification easier — it’s making it persistent. And persistence introduces a different kind of risk, one that doesn’t look like failure but can still affect outcomes in subtle ways.
Responsibility also becomes harder to define in this model. If a system relies on an attestation and something goes wrong, it’s not always clear who is accountable. Is it the issuer who created it, the validator who confirmed it, the platform that accepted it, or the user who trusted it? Decentralization distributes control, but it also distributes responsibility in ways that aren’t always obvious.
Still, I don’t think this is something to dismiss.
Sign Protocol is addressing a real inefficiency — the constant repetition of verification across disconnected systems. Making trust reusable could save time, reduce cost, and open up new kinds of interactions. That part makes sense, and it’s hard to ignore.
But at the same time, it’s introducing a new layer of complexity that isn’t immediately visible. It’s shifting verification from something temporary into something that persists, travels, and gets reused in ways that depend heavily on context.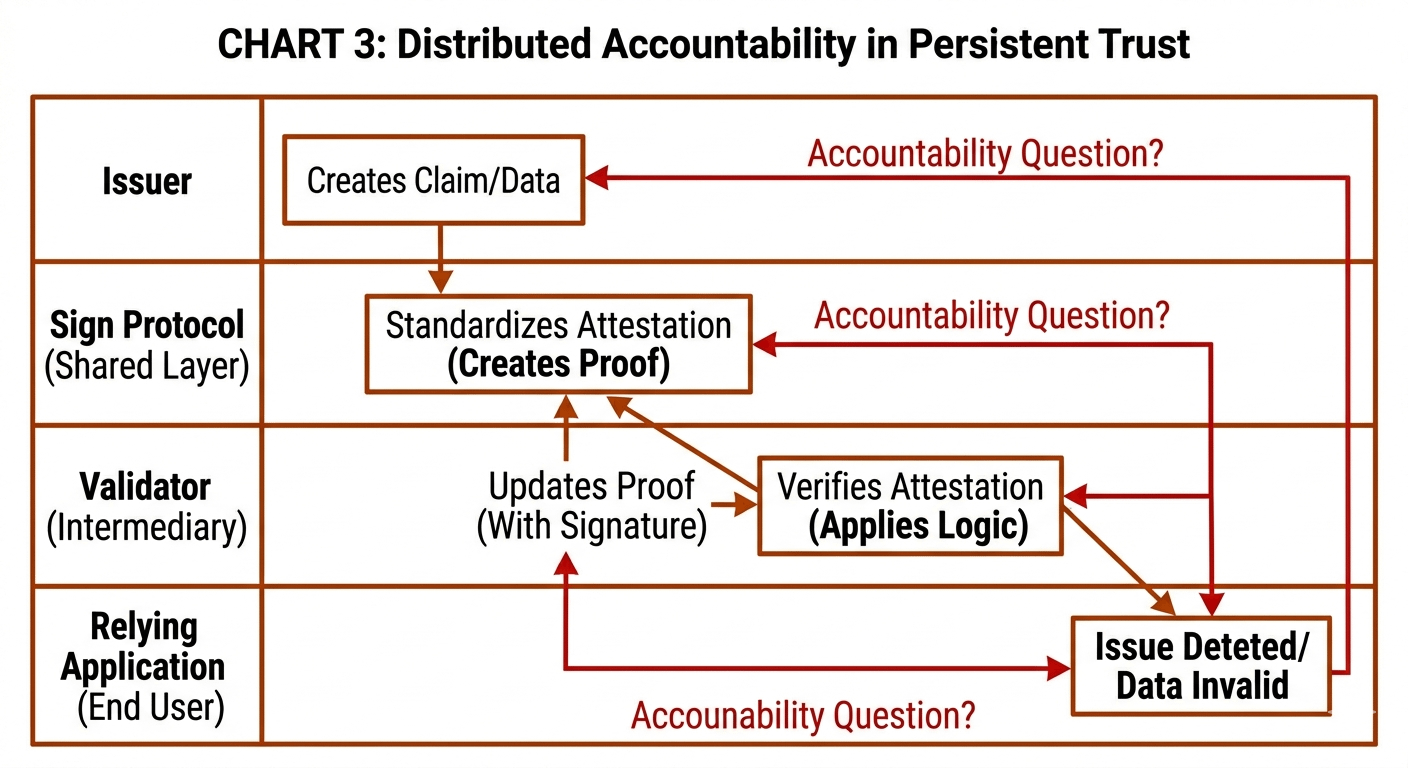
And context is the one thing that doesn’t stay still.
So when I look at SignOfficial, I don’t see a broken idea. I see a strong concept that still needs to prove how it behaves in real-world conditions, where interpretation varies, environments change, and systems don’t always agree.
Execution will decide if this actually holds up.#OilPricesDrop #BitcoinPrices $SIGN