I’ve been examining @SignOfficial Protocol, particularly its Validator Control mechanism. On paper, it looks well-structured and promising. The idea that validators are responsible for checking and confirming the legitimacy of verifications is important. After all, no system should allow false or misleading statements to circulate unchecked. This core function—ensuring that what is being signed is accurate and trustworthy—is fundamental to any verification protocol.
However, despite the strong presentation, I’m not fully convinced yet. There are deeper questions that need clear answers before trust can be established.
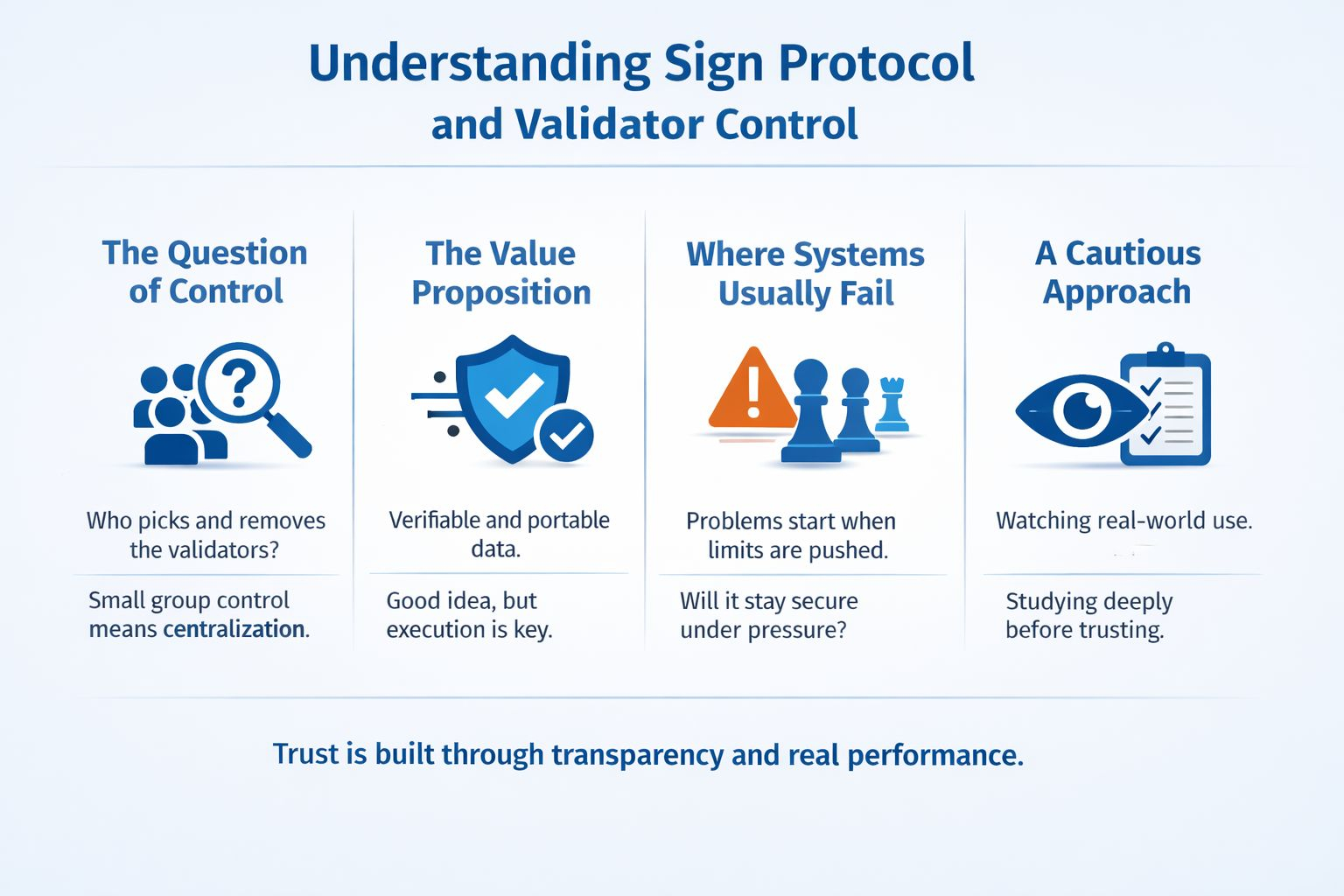
The Question of Control
One of the biggest concerns is: who selects the validators, and who has the authority to remove them? This is where things become critical. If control lies in the hands of a small group, then the system risks becoming centralized, regardless of how it is marketed.
A system can appear decentralized on the surface, but if a limited inner circle ultimately makes the decisions, then it is simply centralized power in disguise. It doesn’t matter how polished or transparent the interface looks—control is still control. حقیقی decentralization only exists when power is distributed and not concentrated.
On the other hand, if the protocol truly allows open participation—where anyone can step in as a validator and contribute to verification—then it moves closer to a model that is more trustworthy and aligned with decentralization principles.
The Value Proposition of Sign Protocol
To its credit, Sign Protocol is attempting something meaningful. The idea of making data verifiable and portable is genuinely useful. In a digital world where trust is often fragile, having a system that enables reliable verification across platforms is a strong advantage.
This feature alone could have real-world applications, especially in areas where proof and authenticity matter. But good ideas are only as strong as their execution.
Where Systems Usually Fail
It’s important to remember that systems don’t usually fail when they are small, simple, or operating under ideal conditions. They fail when they are tested—when users begin to push boundaries, exploit loopholes, or attempt to gain control.
This is the stage where true resilience is revealed. If Validator Control can withstand manipulation, remain transparent, and operate fairly under pressure, then it has real potential. If not, it risks becoming just another controlled gateway with a different label.
A Cautious but Curious Approach
For now, I am observing closely. Not just reading documentation or relying on promises, but watching how Validator Control performs in real-world scenarios. behavior matters more than theoretical design.
My approach is simple: study deeply, understand the ecosystem, learn the technical structure, and analyze how control is distributed when the system is under stress. Only then can a fair judgment be made.
In the end, trust is not built through claims—it is built through consistent, transparent performance over time.