That morning I reopened the reconciliation sheet for the third time, not because any numbers were missing, but because every number looked too obedient. The money had moved, the wallet had received it, yet there was no clean enough trail from the result back to the reason, and it was precisely that quiet professional irritation that made me look at Sign more seriously.
Across three market cycles, I have seen too many systems polish the entrance and loosen up at the exit. They are careful when collecting data, they sound disciplined when setting conditions, but once the final payment leaves the system, the explanation suddenly becomes thin. I think that is a structural flaw, because a payout mechanism that cannot be traced back properly will eventually crack trust from the inside.
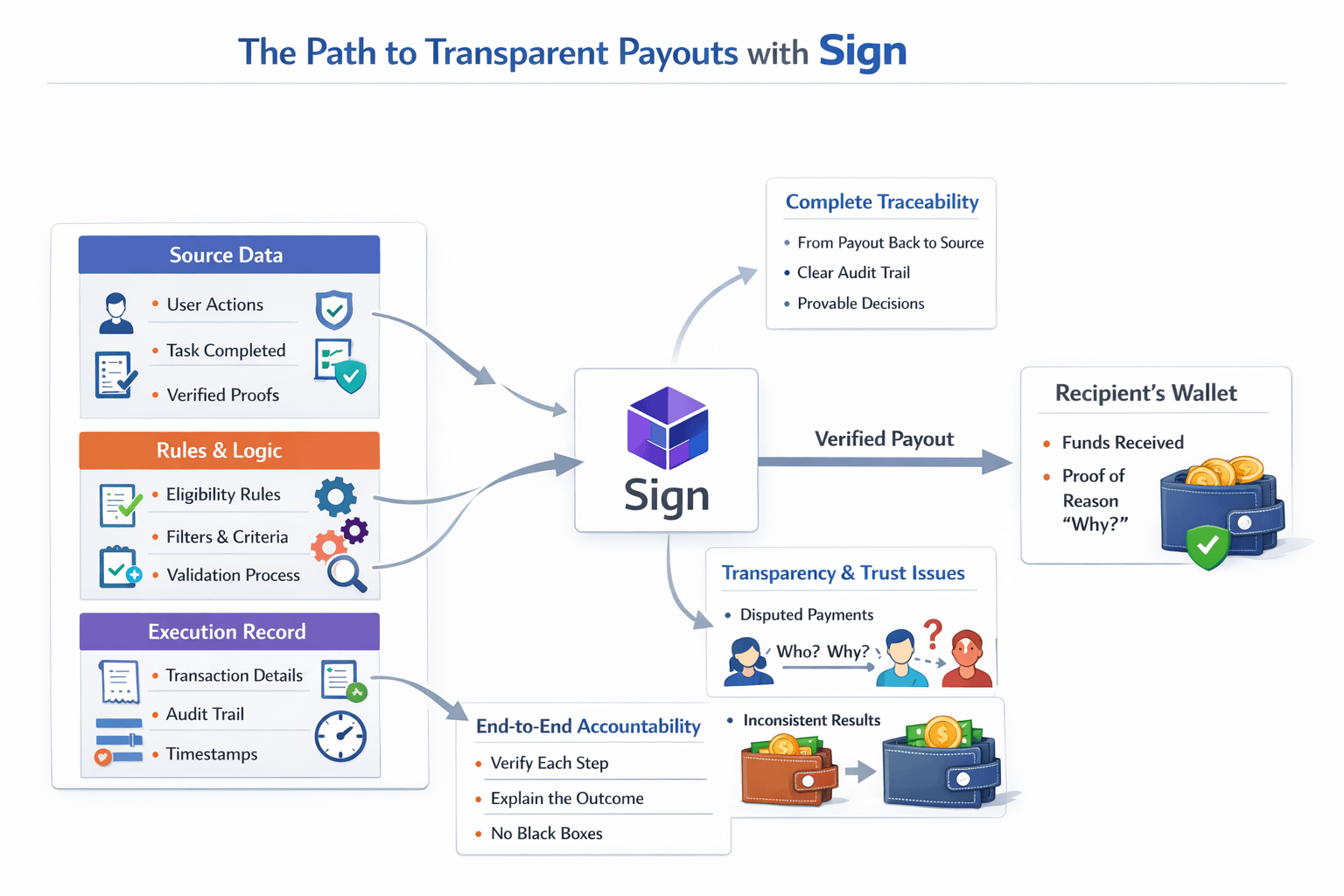
What makes Sign worth discussing is that this project does not treat payment as a bookkeeping gesture. Sign pulls that final step back to where it belongs, a junction between verified data, applied rules, and executed action. A system that knows who qualifies is already hard enough to build, but a system that can prove why this wallet received that exact amount is much harder.
It is strangely revealing that major disputes rarely explode around the messaging of a program, but usually erupt after the money has already landed in wallets. Once a group of users feels they were excluded without a clear basis, or two nearly similar addresses receive different outcomes, the entire product is dragged into a zone of suspicion. At that point the team gets asked which data was used, who verified it, and which version of the rules governed that payment. Sign goes straight into that pressure zone.
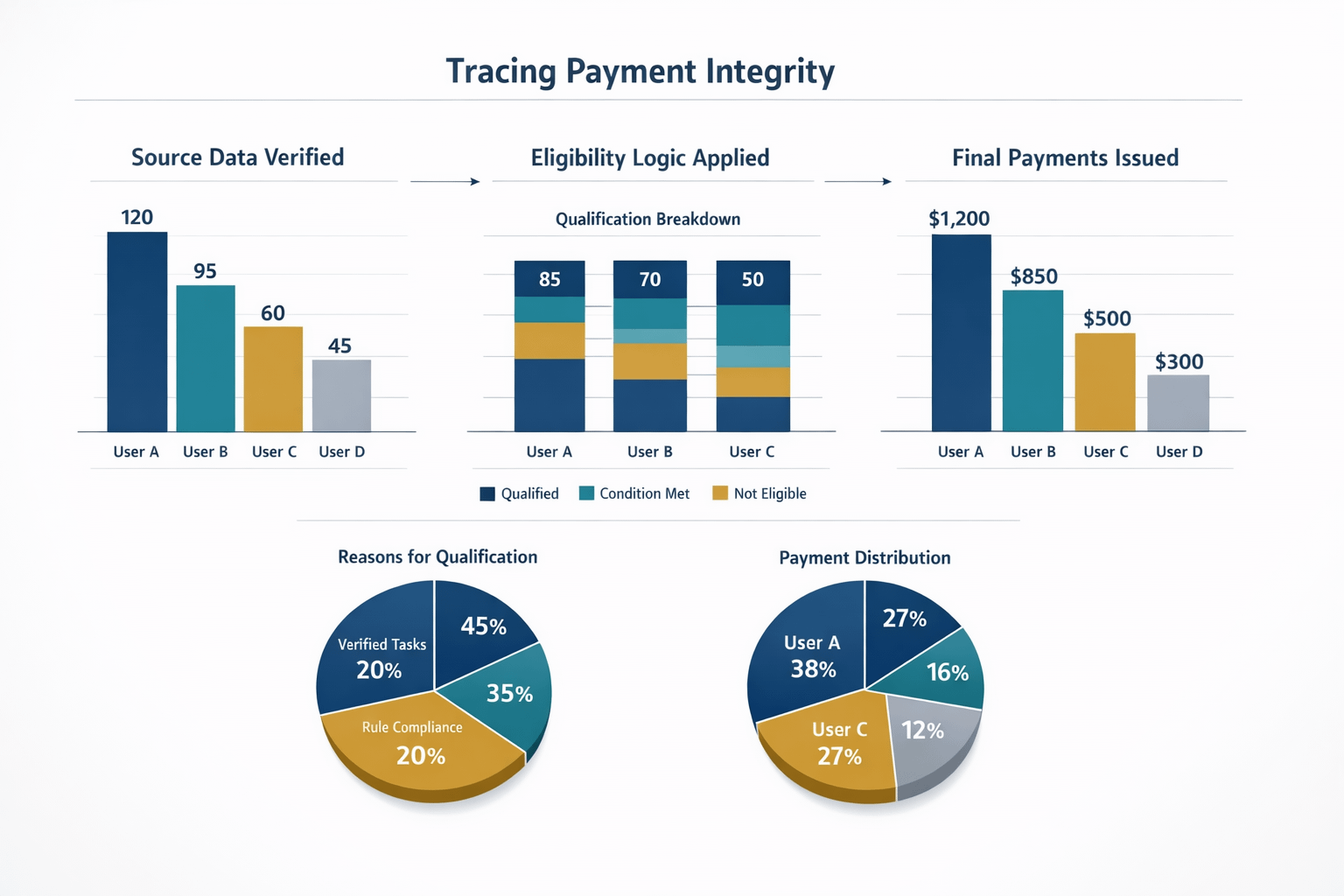
I have always believed that a serious distribution system must lock three layers together. The first layer is the source data, meaning the evidence of who completed what. The second layer is the logic that turns that evidence into eligibility. The third layer is the actual payment. If those three layers come apart, the system may still appear to run from the outside, but once 19 payments out of 2400 recipient wallets become questionable, credibility starts to fall. No one expects that the part capable of damaging the entire structure is often not the input algorithm, but the payment step that fails to preserve the record of why.
This is where I think Sign sets a harder standard than the surface level transparency the market often praises. Real transparency is not about exposing everything to everyone at once. It is the ability to let the right people verify the right part through a chain of evidence that stays intact. To be honest, many products seem to have solved distribution, but in reality they have only solved money transfer. Sign forces the payout layer to carry explanatory responsibility.
That is why I do not see Sign as a decorative layer attached to a distribution workflow. I see it as a way of forcing system designers to respect the consequences of the decisions they encode. When the final payment can still be traced back properly, operators can no longer hide behind the answer that the machine processed it that way. They have to point back to the source evidence, the filtering logic, and the execution trail. In a market that has long been too willing to forgive opaque parts as long as the money arrives, that kind of discipline is rarer than people think.
What I learned from the way Sign approaches this problem is that a system becomes truly mature only when it can withstand being questioned backward from the result to the cause. Not through storytelling, but through operational records clean enough to be examined. Once the final payment is no longer a black box that only opens to reveal a number, trust stops leaning on the team’s goodwill and starts attaching itself to the architecture of the product. Or perhaps a few years from now, the minimum standard for any distribution mechanism will be to pay correctly and also explain itself all the way back to the root, and if that happens, how many projects besides Sign will still stand under that test.
@SignOfficial $SIGN $SIREN $KERNEL #SignDigitalSovereignInfra