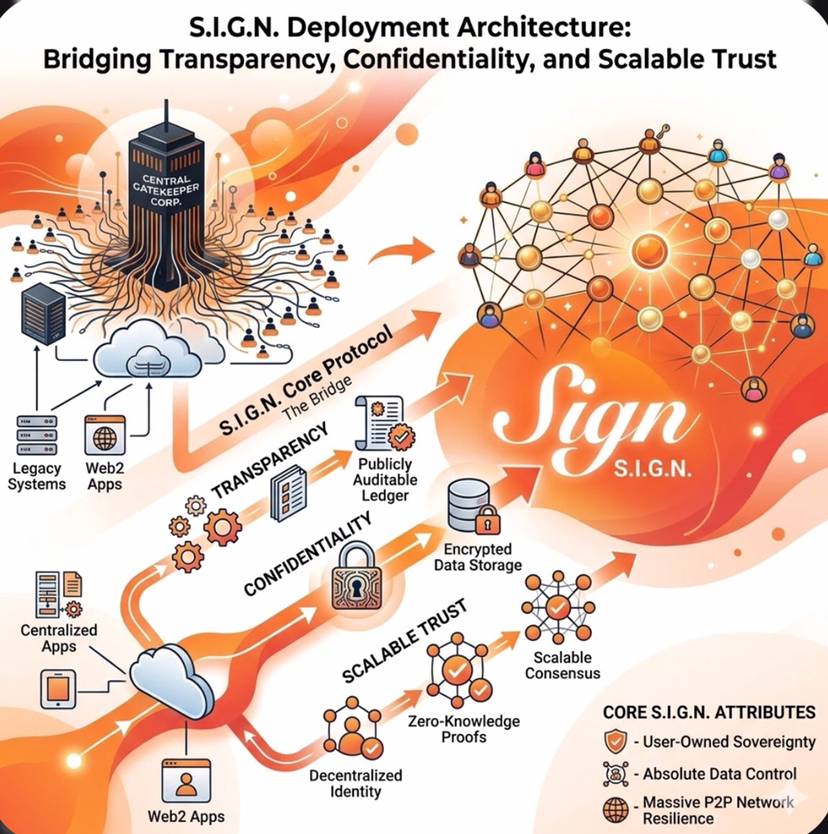
In today’s rapidly evolving digital landscape, organizations are no longer choosing between transparency and privacy they are expected to deliver both. Systems must be open enough to build trust and accountability, yet secure enough to protect sensitive data and comply with regulations. This is where S.I.G.N. deployment architecture introduces a practical and forward-thinking approach.
S.I.G.N. is not built around rigid ideology or one-size-fits-all thinking. Instead, it is designed for real-world deployment conditions, where different industries, governments, and institutions face different operational demands. Some environments require full transparency, others demand strict confidentiality, and many operate somewhere in between. S.I.G.N. acknowledges this diversity and provides flexible deployment modes that adapt to these realities.
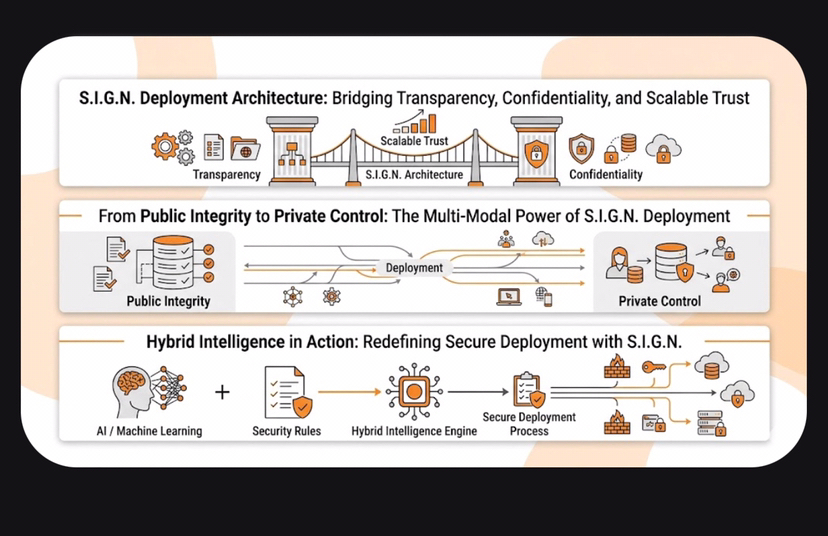
At its core, S.I.G.N. bridges three essential pillars: transparency, confidentiality, and scalable trust. Transparency ensures that systems can be verified and trusted by the public or stakeholders. Confidentiality protects sensitive information from unauthorized access. Scalable trust allows the system to grow without losing reliability or control.
This architecture recognizes that trust is not static it must evolve as systems expand and as user expectations change. By supporting multiple deployment modes, S.I.G.N. creates a foundation where organizations can confidently operate without compromising on their priorities. Whether it is a public initiative, a private financial system, or a hybrid ecosystem, S.I.G.N. provides the structure needed to succeed.
🔹 From Public Integrity to Private Control: The Multi-Modal Power of S.I.G.N. Deployment
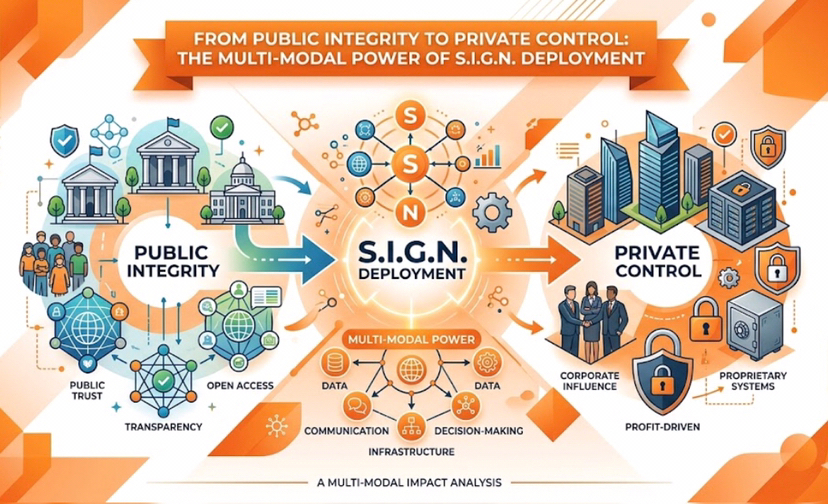
One of the most powerful aspects of S.I.G.N. is its ability to operate across multiple modes of deployment. Rather than forcing users into a single framework, it offers three distinct modes: public, private, and hybrid. Each mode is carefully designed to serve specific needs while maintaining the integrity and scalability of the overall system.
Public Mode
Public mode is optimized for transparency-first programs. These are systems where openness and accountability are critical. Examples include public sector initiatives, open financial ecosystems, and platforms that rely on community trust.
In this mode, data and processes are designed to be verifiable by anyone. This does not mean all sensitive information is exposed, but rather that the system’s integrity can be independently confirmed. Public mode builds confidence among users because it eliminates hidden processes and creates a shared understanding of how the system operates.
Governance in public mode is expressed through structured mechanisms such as chain parameters in Layer 2 environments or contract-based governance in Layer 1 systems. This means that rules are not enforced behind closed doors—they are embedded into the system itself. Changes to governance are visible, trackable, and often require consensus, ensuring that no single entity can dominate the system.
The strength of public mode lies in its ability to foster trust at scale. When users can see and verify how a system works, they are more likely to participate and rely on it. This makes public mode ideal for ecosystems where inclusivity and openness are key priorities.
Private Mode
In contrast, private mode is designed for confidentiality-first programs. These are environments where data protection, regulatory compliance, and controlled access are essential. Financial institutions, enterprise systems, and domestic payment networks often fall into this category.
Private mode prioritizes security and control. Access to the system is restricted through permissioning mechanisms, ensuring that only authorized participants can interact with sensitive data. Membership controls define who can join the network, while audit access policies determine how and when oversight is conducted.
Governance in private mode is not publicly exposed but is instead enforced through clearly defined internal structures. This allows organizations to maintain strict control over operations while still benefiting from the reliability and scalability of the S.I.G.N. architecture.
The key advantage of private mode is its ability to protect sensitive information without sacrificing efficiency. Organizations can operate with confidence, knowing that their data is secure and that compliance requirements are being met. This makes private mode particularly valuable in regulated industries where privacy is not optional but mandatory.
Hybrid Mode
Hybrid mode represents the best of both worlds. It combines the transparency of public systems with the confidentiality of private ones. This mode is especially useful for organizations that need to balance openness with control.
In a hybrid deployment, certain elements of the system are publicly verifiable, while others remain private. For example, transaction proofs or system outcomes might be visible to ensure trust, while the underlying data remains encrypted and accessible only to authorized parties.
This approach allows organizations to maintain accountability without exposing sensitive information. It also enables collaboration between public and private entities, creating new opportunities for innovation and integration.
Hybrid mode is not simply a compromise it is a strategic advantage. By leveraging both transparency and privacy, organizations can build systems that are both trustworthy and secure. This flexibility makes hybrid mode one of the most powerful aspects of the S.I.G.N. deployment framework.
🔹 Hybrid Intelligence in Action: Redefining Secure Deployment with S.I.G.N
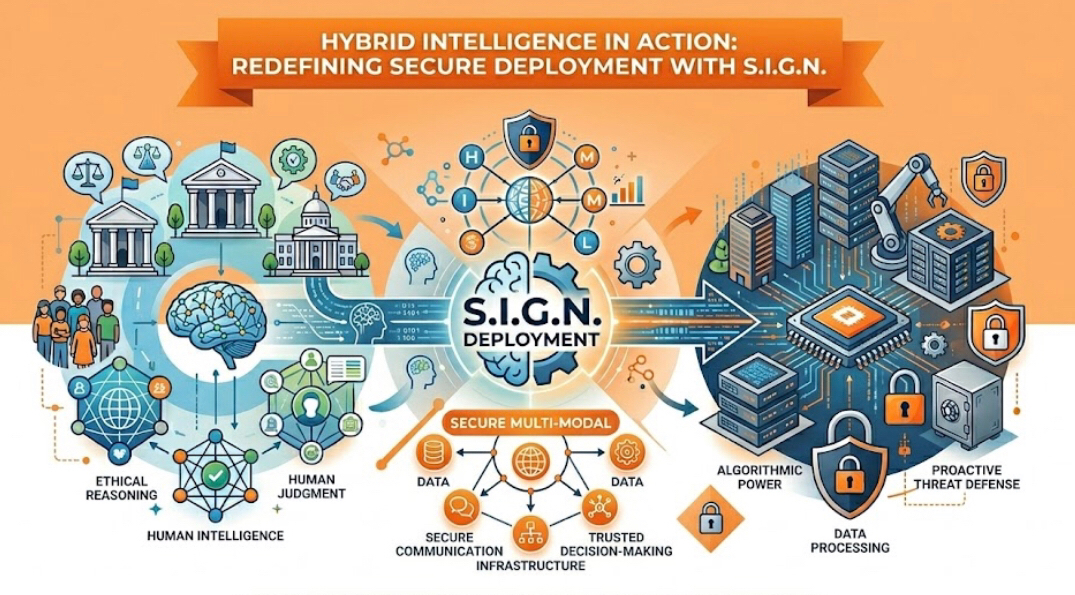
S.I.G.N. is more than just a deployment framework—it represents a shift in how we think about system design. Instead of choosing between competing priorities, it introduces the concept of hybrid intelligence, where systems are designed to adapt, evolve, and respond to real-world needs.
Hybrid intelligence in S.I.G.N. is about combining different operational models into a cohesive whole. It recognizes that no single approach can address all challenges. By integrating public, private, and hybrid deployment modes, S.I.G.N. creates a dynamic environment where systems can operate efficiently under varying conditions.
This adaptability is particularly important in today’s interconnected world. Organizations often operate across multiple jurisdictions, each with its own regulatory requirements and user expectations. A system that works well in one region may not be suitable for another. S.I.G.N. addresses this challenge by allowing deployments to be tailored to specific contexts without losing overall consistency.
Another key aspect of hybrid intelligence is scalability. As systems grow, they must handle increased demand without compromising performance or security. S.I.G.N. achieves this by separating concerns—allowing different components of the system to operate in the most appropriate mode. Public components can scale to support large user bases, while private components maintain strict control over sensitive operations.
Security is also redefined through this approach. Instead of relying on a single layer of protection, S.I.G.N. uses a combination of transparency, permissioning, and verification to create a multi-layered security model. This reduces the risk of failure and ensures that the system remains resilient even under pressure.
Perhaps most importantly, S.I.G.N. empowers organizations to make decisions based on their actual needs rather than imposed limitations. It does not dictate how systems should be built it provides the tools and frameworks needed to build them effectively.
This practical mindset is what sets S.I.G.N. apart. It acknowledges that real-world deployments are complex and often messy. By embracing this complexity instead of ignoring it, S.I.G.N. delivers a solution that is both realistic and powerful.
🔹 Conclusion
S.I.G.N. deployment architecture represents a new way of thinking about trust, security, and scalability. By offering public, private, and hybrid modes, it provides the flexibility needed to address diverse operational requirements. It bridges the gap between transparency and confidentiality, ensuring that systems can be both open and secure.
Rather than forcing organizations into rigid structures, S.I.G.N. adapts to the realities of deployment. It recognizes that trust must be built differently in different contexts and provides the tools to do so effectively.
In a world where digital systems are becoming increasingly critical, this approach is not just innovative—it is necessary. S.I.G.N. is not about choosing sides; it is about creating balance. And in that balance lies the future of secure, scalable, and trustworthy systems.