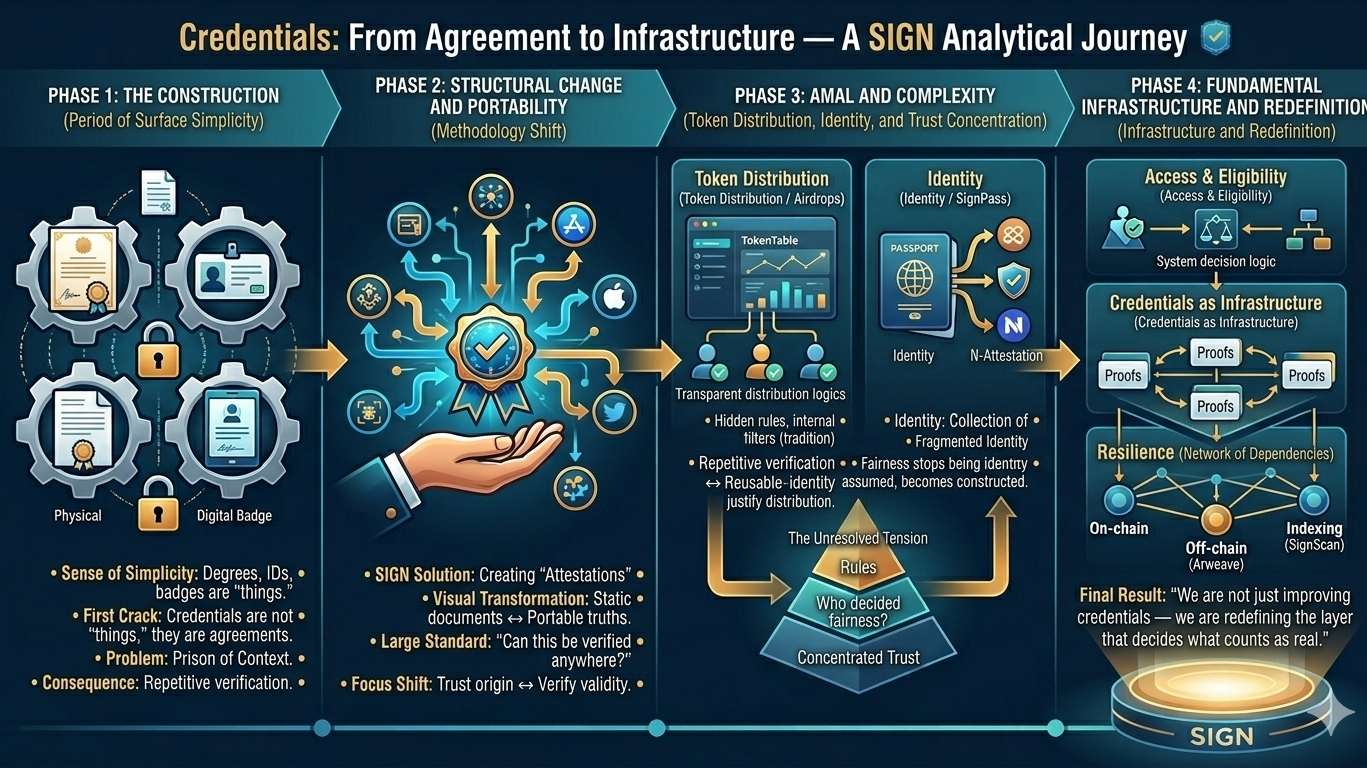
@SignOfficial I’ll be honest… credentials used to feel like one of the simplest parts of the digital world.
You earn something, someone issues it, and you use it when needed. Degree, certificate, ID, badge it all looks clean on the surface. There’s a sense that these things carry meaning, that they represent something stable about you. And for a long time, I didn’t really question that.
But the more I sit with credentials, the more that simplicity starts to feel… constructed.
Because when you look closely, credentials aren’t really objects.
They’re agreements.
An agreement between whoever issues them, whatever system stores them, and whoever is verifying them later. And the moment you move outside that shared context, things start to break. A credential that means everything in one system can mean almost nothing in another. Not because it’s wrong… but because it’s not recognized the same way.
That’s where the feeling starts to shift.
You’re not carrying something universally true — you’re carrying something that only works where the rules align.
And most of the time, you don’t even notice that dependency.
You just upload documents again, re-verify identity, re-prove eligibility. Over and over. It starts to feel less like ownership and more like repetition. Like you’re constantly translating yourself between systems that don’t actually speak the same language.
That’s the part that never really sat right.
Because if credentials are supposed to represent something about you, why do they stop working the moment you leave the system that issued them?
That’s where something like SIGN starts to feel different — not because it introduces a new type of credential, but because it changes how credentials behave.
Instead of being locked inside platforms, they become attestations. Proofs that can exist independently of where they were created. And once that shift clicks, credentials stop feeling like static documents and start looking more like portable pieces of truth.
Something you can carry. Something you can prove. Something you don’t have to rebuild every time.
On the surface, that sounds like a usability improvement.
But the more you follow it, the more it starts to feel like a structural change.
Because once credentials become portable, they stop being tied to a single system’s definition of validity. They start moving across environments — across apps, across platforms, across contexts. And suddenly, the question isn’t just “is this credential real?” but “can this credential be verified anywhere?”
That’s a very different standard.
It shifts the focus from trusting where something came from… to verifying what it actually proves.
And that same pattern starts showing up in places you wouldn’t expect.
Take something like token distribution.
On the surface, airdrops feel unrelated to credentials. They’re just tokens sent to wallets based on activity. But when you look closer, they’re actually built on the same idea — eligibility. Who qualifies, and why?
Traditionally, that logic lives inside the project. Hidden rules, internal filters, decisions that aren’t always visible. You either get included, or you don’t.
But when credentials enter the picture, that changes.
Eligibility can be tied to attestations. Not just wallet activity, but verified conditions. Participation, identity, behavior — all expressed as something provable. And systems like TokenTable start combining these elements into distributions that aren’t just executed… but justified.
It’s a subtle shift, but an important one.
Because fairness stops being something assumed, and starts becoming something constructed.
But even then, something feels unresolved.
Because constructing fairness doesn’t mean removing bias. It just means the rules are written somewhere more visible. And those rules still come from somewhere. Someone decides what counts. Someone defines the conditions.
So the question isn’t whether the system is fair.
It’s who shaped the definition of fairness in the first place.
That tension becomes even clearer when you think about identity.
Right now, identity online is fragmented in a way we’ve almost normalized. You verify yourself on one platform, and it means nothing on another. You rebuild your credibility every time you move. There’s no continuity — just isolated checkpoints of validation.
SIGN tries to compress that fragmentation into something reusable.
With something like SignPass, identity becomes a collection of attestations. Instead of proving everything from scratch, you carry proofs with you — selectively disclosing what’s needed, when it’s needed. In theory, that makes identity portable. It turns verification into something you accumulate rather than repeat.
But the more I think about it, the more another layer shows up.
Because those attestations don’t create themselves.
They’re issued.
And whoever issues them becomes part of the system’s foundation. If the issuer is trusted, everything works smoothly. If not, the entire chain starts to feel unstable. The proofs might be valid, the system might be verifiable… but the origin still matters.
So even in a model designed to reduce trust, trust doesn’t disappear.
It just becomes more concentrated.
And then there’s the infrastructure holding all of this together — something most people don’t even think about.
These attestations, these credentials, these proofs… they need to exist somewhere. They need to be available, retrievable, verifiable over time. SIGN spreads this across multiple layers — on-chain deployments, off-chain storage like Arweave, indexing through SignScan.
On paper, that creates resilience.
But in practice, it creates coordination.
Because availability isn’t guaranteed by a single system — it’s the result of multiple systems continuing to function together. If one layer fails, the others compensate. But the system as a whole depends on alignment between components that aren’t identical, and aren’t controlled the same way.
So what looks like decentralization from the outside is actually a network of dependencies working in balance.
And the more you zoom out, the harder it becomes to see credentials as simple objects at all.
They start to look more like building blocks.
Not just things you use, but things systems rely on to make decisions. To grant access. To define eligibility. To establish identity. To prove actions.
At that point, credentials stop being a feature.
They start becoming infrastructure.
And that’s where SIGN begins to feel like something bigger than it looks.
Not because it’s adding new capabilities… but because it’s quietly standardizing how systems prove things. How they agree on what’s valid. How they recognize truth across boundaries that used to be disconnected.
It’s not trying to replace systems.
It’s trying to sit underneath them.
And the more I sit with that… the more it stops feeling like we’re just improving credentials — and the more it feels like we’re redefining the layer that decides what counts as real in the first place.