Last week, while building an access control flow for a small app, I hit a familiar wall. The UI was simple, and the smart contracts were clean, but the real challenge emerged elsewhere: proving a user is eligible to proceed without building a full-scale compliance stack from scratch.
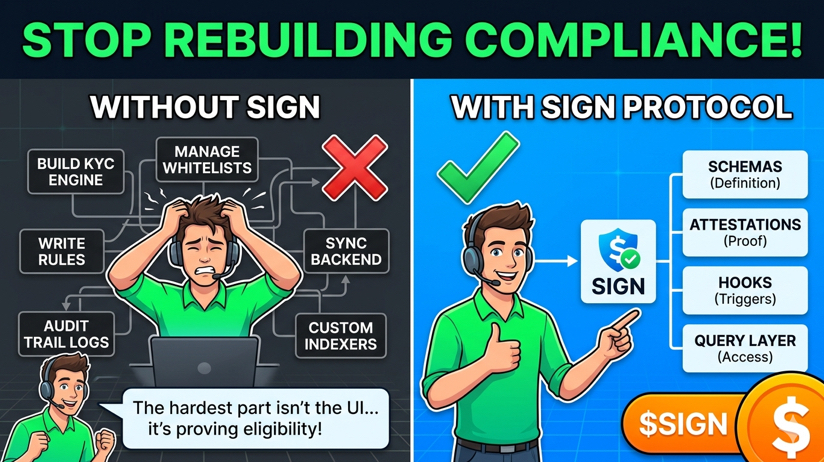
Most app developers don't want to become compliance experts. They don't want to maintain KYC engines, manage complex whitelists, or track sanction statuses. Yet, they still need to answer critical questions: Can this user enter? Is their verification still valid? How do we audit this later? This is where Sign Protocol provides a pragmatic solution by shifting the focus from tokens to structured claims.
The Infrastructure of Trust: Schemas and Attestations
The core value of Sign Protocol lies in its two primary primitives: Schemas and Attestations.
* Schemas: These define the "shape" of a claim. Instead of every app creating its own unique way to verify a user, a schema provides a standardized template. This makes claims machine-readable and interoperable across different platforms.
* Attestations: These are the actual records—cryptographically signed statements that follow a specific schema.
By using these, an app doesn't need a user’s entire profile; it just needs to query a specific, verified claim (e.g., "Has this user passed KYC?") issued by a trusted entity.
Turning Evidence into Action: Schema Hooks
What makes Sign Protocol more than just a storage layer is the use of Schema Hooks. This is where compliance becomes operational logic.
In a traditional setup, you’d need custom listeners and backend cron jobs to sync a user's status. With Sign, the system can react automatically when an attestation is created, updated, or revoked.
* Condition: Is the claim active?
* Trigger: A change in the attestation status.
* Execution: The app opens access or the transaction reverts.
This replaces "self-built" infrastructure with a streamlined flow of condition → trigger → execution.
A Pragmatic Approach to Data
Many "trust layers" fail because they force all data onto the blockchain. Sign Protocol takes a more realistic path. It recognizes that sensitive data often cannot (and should not) be fully public.
Instead of forcing a "do it all yourself" or "publish everything" choice, Sign allows the evidence to reside in the most suitable layer whether on-chain or off-chain as long as the proof of validity remains traceable and auditable.
Cutting Out the "Indexing" Tax
One of the hidden costs of building compliance is the query layer. Even with great data, if you have to build your own indexers to retrieve it, the promise of "reduced infrastructure" is just marketing. Sign Protocol addresses this by investing in:
* Scanning tools
* API layers
* Advanced query interfaces
This allows apps to read back claims and statuses through a stable interface, preventing the need for the old "self-build, self-index, self-reconcile" cycle.
The Reality Check
It’s important to stay grounded: Sign Protocol does not replace your legal team. It doesn't magically make a weak issuer trustworthy, nor does it eliminate the need for product teams to define their own policies.
However, it does eliminate the need to rebuild the verification and evidence plumbing every time you launch a new feature. By providing a shared layer for schemas, attestations, and hooks, Sign Protocol allows developers to stop acting like compliance engineers and get back to building their products.
The bottom line: The value of Sign isn't just "another protocol for attestations"—it's the removal of an entire layer of technical debt that most teams hate building from scratch.