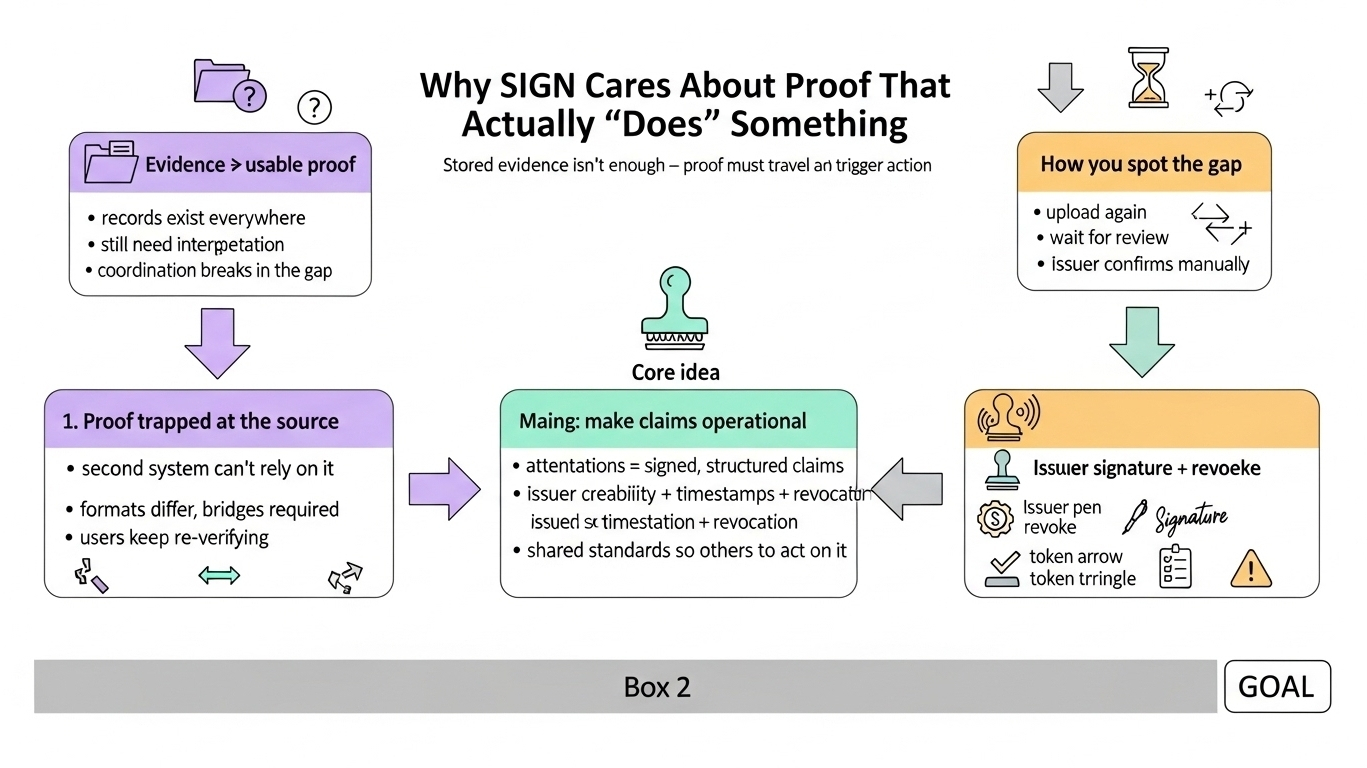
it’s easy to confuse having evidence with having usable proof. a wallet can hold an asset, a user can have a history of actions, a system can store credentials and logs. but none of that automatically tells a second system what to do with it. the internet is full of records, yet so many of them still need interpretation before they become actionable. that gap is where coordination breaks.
you can spot a proof problem by the way systems compensate. they make you repeat yourself: upload it again, connect another account, wait for review, show the same record in a new format, ask the issuer to confirm manually. all of that is basically one message: “we can’t rely on what you already have.” the proof exists, but it doesn’t travel cleanly enough to trigger trust on its own.
a credential should be more than stored information. ideally it behaves like a claim that can be used: this person completed something, belongs to a group, holds a role, qualifies for access, met a condition. but whether that claim works depends on context. who issued it, whether that issuer matters here, whether the claim is still current, whether it can be revoked, and whether another system can read it without building a private bridge back to the original source.
so the real challenge isn’t generating proofs. it’s turning proofs into something operational.
this is also why credential verification and token distribution are tied together. people talk about token movement like it’s the main event, but movement is the easy part. the hard part is the logic that justifies movement: why did this token go here, what made this recipient eligible, what proof connects them to the distribution, and can someone inspect that reasoning later and see something coherent instead of a pile of internal assumptions.
once you link “this fact can be relied on” with “therefore this consequence can follow,” the system starts to look less like scattered digital actions and more like decision-making based on portable proof. it becomes about enforceable meaning in a practical sense: a fact needs to survive long enough, and travel well enough, that something else can happen because of it—access granted, value distributed, status recognized, rights activated, eligibility settled.
without that continuity, proof stays trapped where it was created: visible, but not fully usable.
that’s why the quiet infrastructure details matter: attestations, signatures, timestamps, issuer credibility, revocation, shared standards. not dramatic topics, but they’re what let another system accept a claim without inheriting all the mess behind it.
and there’s a human side too. people don’t experience proof systems as architecture. they experience them as whether they’re believed, whether they have to re-explain their history, whether contributions still count after time passes, whether the system can act on what’s already known without sending them into another verification loop. bad proof infrastructure creates drag. good proof infrastructure reduces how often a person has to restate what should already be legible.
so when i think about SIGN through this lens, it doesn’t feel like a project trying to create more records. it feels like a project trying to make records do more work—helping proof move from being stored to being usable, so meaning can survive movement across contexts. that shift is usually quiet at first, but it’s the kind of shift a lot of future decisions are waiting on.