I’ve been thinking about Sign Protocol a lot lately, and honestly, calling it an “attestation registry” feels way too small. It makes everything sound like a clean digital filing cabinet—proofs go in, sit quietly, and get pulled out when someone needs them. That’s technically true, but it misses the heart of what’s happening.
What actually excites me is how Sign lets trust travel.
You know how most digital systems feel right now? Every new app, every new chain, every fresh context acts like it has to start from scratch. Re-verify the user. Re-check the credential. Run the whole trust routine again, pretending nothing that came before matters. It’s tiring, wasteful, and a little silly—like we’re confusing repetition with real security.
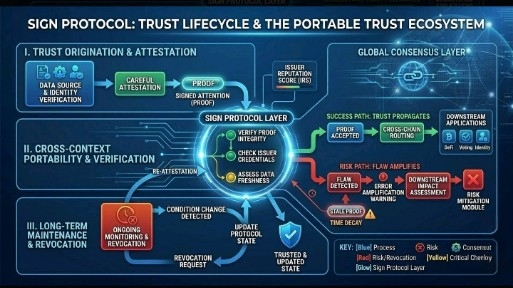
Sign flips that. It lets signed proofs move cleanly across boundaries—between chains, apps, and ecosystems—without losing their meaning. One place does the hard or careful verification once, signs it properly, and that proof can follow the user and get reused elsewhere. No more forcing every new system to pretend history began five minutes ago. Verification becomes portable. Context stops vanishing at every edge.
To me, that’s not just storage. That’s real infrastructure. The kind that could make cross-chain life feel much less brittle, less repetitive, and way less forgetful about what’s already been figured out.
The Hidden Weight of Portable Trust
But here’s where it gets uncomfortable.
If trust is going to travel farther and get reused more often, then the issuer suddenly matters a lot more than people admit. A thoughtful, reliable issuer can make the whole system feel smooth and trustworthy. A sloppy, compromised, or misguided one? That bad proof doesn’t stay local anymore—it spreads. Downstream apps might trust the signature more than they ever understood the original source. The same efficiency that removes friction can quietly turn into a fast way to amplify mistakes.
When Time Makes Trust Dangerous
And then there’s the time problem that keeps nagging at me.
A proof can be perfectly valid the day it’s signed and quietly misleading months later. The signature still checks out. The format still looks clean. But life has moved on—the user’s status changed, the condition expired, the world shifted underneath it. Yet the old attestation keeps traveling forward, looking as official as ever. Stale trust is sneaky like that. It doesn’t announce itself; it just lingers, because signed things carry this quiet air of permanence even when the reality behind them has faded.
So when I look at Sign, I don’t see a simple database of attestations. I see a protocol trying to stitch these fractured digital worlds back together so we can stop rebuilding the same basic checks over and over. That reusability feels genuinely powerful. It could make identity, credentials, compliance—pretty much everything—feel more continuous and less amnesiac across chains and apps.
At the same time, it quietly raises the stakes. Issuer quality matters more now. Freshness and revocation matter more. The difference between “was true then” and “is still true now” becomes a really big deal.
Portable trust is a beautiful idea. It just doesn’t erase risk—it moves it around. The very thing that lets good trust flow farther is the same thing that can let flawed or outdated trust travel faster and wider than before.
The upside is exciting, and I suspect many of us are still underestimating it. But the responsibility that comes along with it deserves a much closer look. That tension is exactly why Sign feels worth paying real attention to.
@SignOfficial #SignDigitalSovereignInfra
#SIGN