S.I.G.N. makes a lot more sense once you stop reading it like a blockchain product and start reading it like a response to how government systems actually fail in practice.
Because the failure mode usually isn’t dramatic. It’s not some Hollywood cyberattack or a giant “system offline” moment. It’s much uglier and much more familiar than that. It’s five agencies using five different databases, all claiming to be the source of truth. It’s citizen records that don’t quite line up with payment rails. It’s compliance teams exporting CSVs from one system, manually reconciling them against another and praying the spreadsheet version sent last Thursday is still the “final final” one. That’s the real environment this stuff has to survive in.
And if we’re being honest, most “digital transformation” efforts don’t fail because the ambition was too small. They fail because the plumbing was garbage.
That’s the context where S.I.G.N. starts to look less like a pitch and more like missing infrastructure.
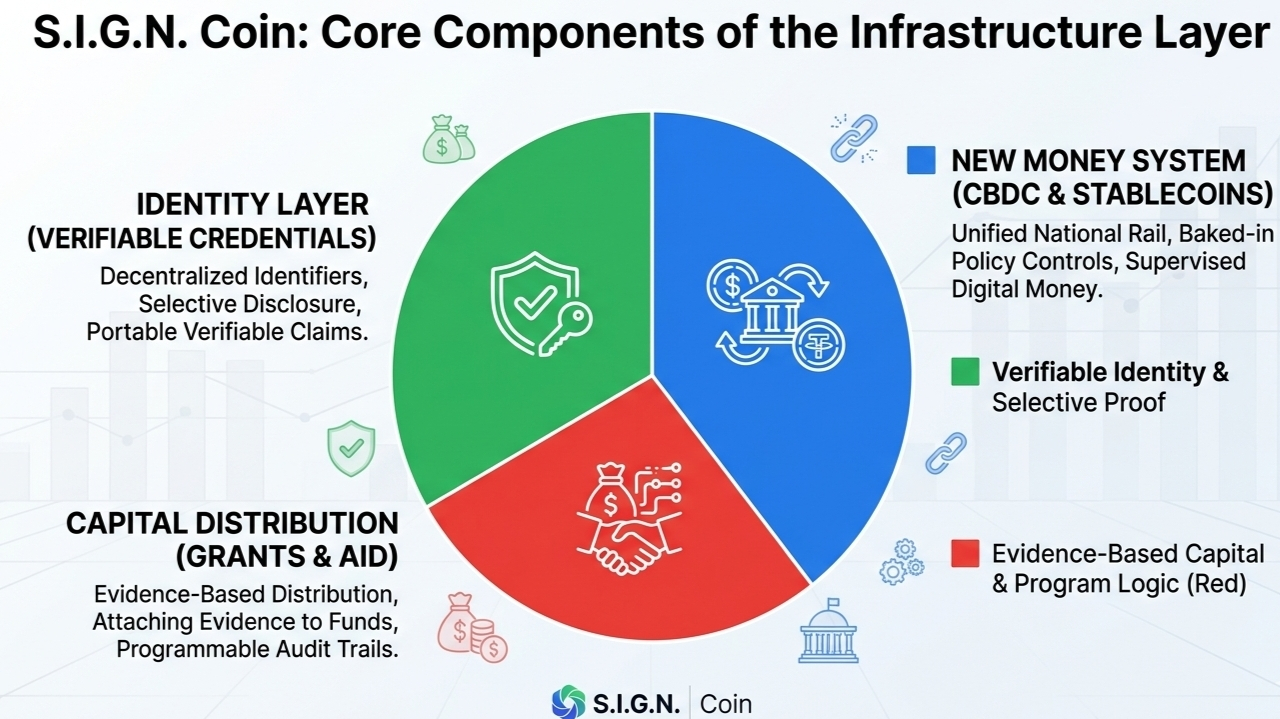
The basic idea is pretty simple: money systems, identity systems, and capital distribution systems should not behave like strangers. Right now, in most countries, they do. The identity stack is usually its own bureaucratic island. Payments are handled somewhere else, often through legacy rails that were never designed to carry policy logic. Then capital programs grants, subsidies, aid, tokenized instruments, whatever form they take, get bolted on later and spend the rest of their life being “integrated” through middleware and human suffering.
That’s the problem S.I.G.N. is trying to clean up.
Not by pretending everything gets replaced overnight. That never happens. Not in government. Not in regulated finance. The reality is you inherit old systems, weird procurement decisions, half-working vendor stacks, legal constraints, political constraints, and a decade of technical debt no one wants to admit exists. So the only sane move is to build a layer that sits across the mess and makes the pieces legible to each other.
That’s what S.I.G.N. really is: a coordination layer for national systems that are already running, already messy and already too important to fail.
Money first, because that’s usually where the pain shows up fastest
A lot of people get distracted by the CBDC vs stablecoin debate but that’s not actually the hard part. Creating digital money is not the bottleneck anymore. The market already proved that. Central banks are exploring CBDCs. Private issuers already run stablecoins at scale. The problem is that these things usually live in separate policy worlds, separate technical stacks and separate oversight models.
Then someone eventually asks the obvious question:
How do you run both without creating another regulatory and operational nightmare?
That’s where S.I.G.N.’s “New Money System” is actually practical.
Instead of treating sovereign digital money and regulated private digital money like two unrelated experiments, it puts them on the same national rail with policy controls baked in from the start. Which matters more than people think. Because once you get into real deployment, the conversation stops being “can we tokenize currency?” and turns into much less glamorous questions:
Who can issue?
Who can hold?
What gets frozen?
What gets reported?
What happens when a payment is legal but non-compliant under a program rule?
Who sees what, and when?
That’s where most clean whitepaper diagrams go to die.
S.I.G.N. seems designed around the assumption that digital money has to work under supervision, not outside it. Which is the adult framing, honestly. Public and private modes can coexist, but they’re not just floating around as abstract tokens. They’re operating inside a policy environment where flows can actually be inspected, rules can actually be enforced, and regulators aren’t stuck trying to reconstruct what happened six months later from incomplete logs and institutional finger-pointing.
That’s a much more serious design target.
Identity is where almost every “digital nation” story quietly breaks
This part matters more than the marketing usually admits.
A lot of digital identity systems look fine in a demo and then fall apart the first time a real person has a real problem. Lose your phone? Good luck. Need to prove one thing without exposing ten other things? Not supported. Need to verify a credential in a low-connectivity environment? Suddenly the whole “modern” system still depends on pinging some central server that may or may not be reachable.
That’s not identity infrastructure. That’s a brittle app with branding.
S.I.G.N.’s ID layer is much more interesting because it shifts the model away from “store everything centrally and hope access control saves you” toward verifiable credentials and decentralized identifiers. Which sounds abstract until you think about what it actually fixes.
It means a person shouldn’t need to hand over their entire digital self just to prove they’re eligible for something. They should be able to prove the specific fact that matters. Age. Residency. Enrollment status. Certification. Income band. Whatever the use case is. Nothing more.
That sounds obvious. But most current systems still don’t work that way.
They collect too much. They expose too much. And they create giant centralized dependency points that become political liabilities, privacy liabilities, and operational liabilities all at once.
A better identity system doesn’t just digitize the old paperwork. It changes the shape of the proof.
That’s what selective disclosure and signed credentials are really doing here. They make identity less like a giant profile database and more like a portable set of verifiable claims. And that changes everything operationally, because now verification doesn’t always require a live callback to a central authority. You can validate the credential itself. You can track revocation. You can verify provenance. You can do it in places where connectivity is unreliable. Which, for a lot of actual national deployments, is not some edge case. It’s normal.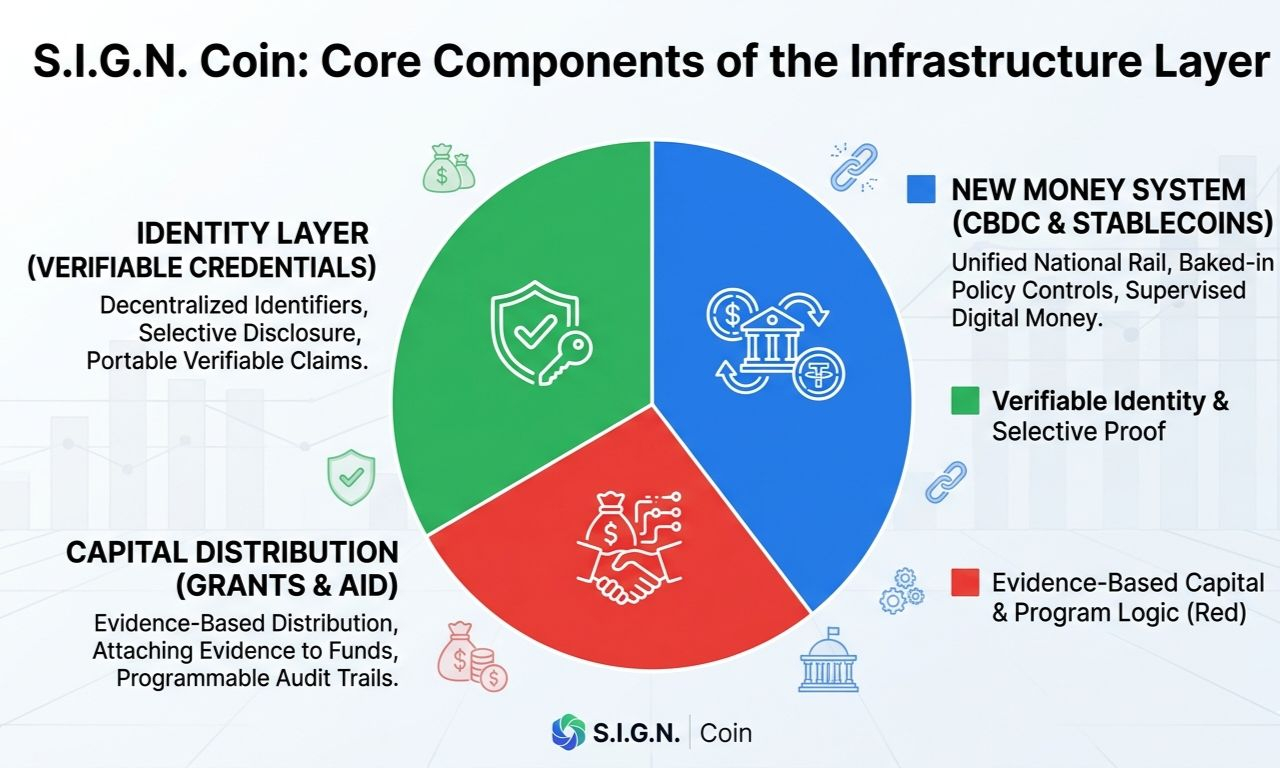
That’s the difference between lab infrastructure and field infrastructure.
Then you get to capital distribution, which is where things usually become a total mess
This is the part people should pay more attention to.
Governments and institutions are constantly distributing value. Grants, social support, climate funding, subsidies, procurement-linked disbursements, development aid, emergency relief. Huge amounts of money move through these systems every year, and way too much of it disappears into what I can only describe as an administrative fog.
Not necessarily stolen. Just lost in process.
A program gets approved under one rulebook, disbursed under another, verified under a third, and audited months later by people who were never in the room when the logic was set. Then everyone is surprised when the records don’t match, beneficiaries can’t prove what they received and oversight turns into archaeology.
This is where S.I.G.N.’s “New Capital System” starts to look genuinely useful.
Because what it’s really doing is attaching evidence to distribution itself.
Not just “we sent the funds.”
But: under what rule, to whom, based on what eligibility proof, approved by which actor, with what compliance state at the time.
That’s a completely different quality of infrastructure.
And yes, this is where tokenized RWAs and programmable distribution come into the picture but the flashy tokenization angle is honestly less important than the evidence trail. The token is not the interesting part. The interesting part is whether the movement of value leaves behind something durable enough to survive an audit, a dispute, a regulator or a policy review six quarters later.
That’s the real standard.
Because the moment public money or regulated capital starts moving digitally, “recordkeeping” is no longer enough. You need machine-verifiable proof that the system behaved as intended. Otherwise you just built a faster black box.
That’s the pattern across the whole stack: less “data,” more evidence
And this is probably the strongest idea inside the whole architecture.
Most systems are built to store records. S.I.G.N. looks like it’s built to produce evidence artifacts.
That sounds subtle but it’s a huge difference.
A record says something happened.
Evidence tells you why it happened, who authorized it, whether the inputs were valid, whether the issuer was trusted, whether the credential was revoked later and whether the system can still prove all of that without relying on institutional memory or some internal admin panel no outsider can inspect.
That’s a much higher bar. But it’s also the bar that matters once these systems stop being pilot projects and start becoming public infrastructure.
Because once millions of users are involved, the system can’t rely on “trust us, the backend is correct.” That works right up until it doesn’t. And then everyone is in hearings.
This is also why the trust layer matters more than the chain choice
A lot of crypto-native discussion gets weirdly fixated on whether something is public chain, private chain, hybrid chain, permissioned this, sovereign rollup that. Some of that matters. But it’s not the first-order problem.
The first-order problem is trust topology.
Who is allowed to issue credentials?
Who is recognized as an authority?
How are keys rotated?
How are revocations surfaced?
How do you know whether a document, approval, or proof still means what it meant when it was issued?
That’s the boring stuff. Which is exactly why it matters.
S.I.G.N.’s trust and evidence layer seems to take that seriously. Trust registries, issuer state, attestations, schemas, revocation visibility, this is the kind of infrastructure that doesn’t get hype on social media but determines whether the system survives first contact with reality.
Because here’s where it usually falls apart: not on the transaction itself but on the metadata around whether that transaction should have been trusted in the first place.
And if that layer is weak, it doesn’t matter how elegant the ledger underneath is.
The sovereignty angle is also more important than people pretend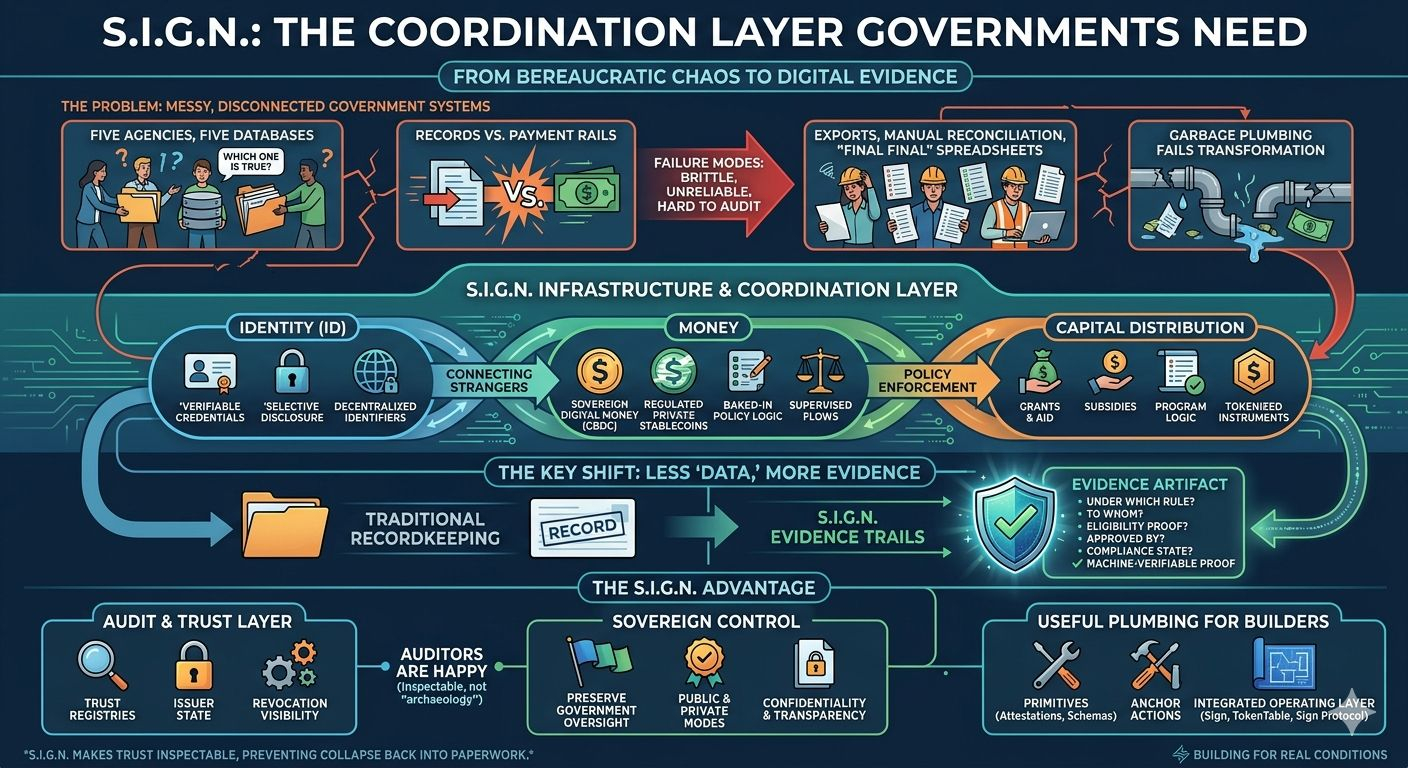
A lot of blockchain infrastructure still carries this weird ideological assumption that institutions should eventually give up control and just “plug into the network.” That is not how national infrastructure gets adopted. Not even close.
A state is not going to hand over monetary control, identity governance or capital oversight because the architecture diagram looked elegant.
Nor should it.
So the real challenge is not “how do we eliminate institutional control?”
It’s “how do we preserve sovereign control while making the system far more auditable and far less corruptible?”
That’s a much harder design problem. But it’s the correct one.
And S.I.G.N. seems to understand that. Public and private deployment modes are not a nice-to-have feature here. They’re a political and operational necessity. Some flows need transparency. Some need confidentiality. Some need both, depending on who’s looking and under what authority. If you can’t support that, you don’t have national infrastructure. You have a prototype.
For builders, this is less ideology and more useful plumbing
That’s the part I think a lot of people will miss if they only read the top-level narrative.
S.I.G.N. is not really asking teams to throw away their stack and become full-time protocol philosophers. It’s offering primitives that let real systems anchor actions into something verifiable.
Attestations.
Schemas.
Trust registries.
Evidence trails.
Program logic tied to identity proofs and payment execution.
That’s useful.
Because most teams building in this space do not need another abstract “future of trust” monologue. They need a way to connect signing, eligibility, issuance, disbursement and auditability without building the entire trust stack from scratch every time.
That’s also why products like EthSign, TokenTable, and Sign Protocol matter more together than separately. On their own, they can look like isolated tools. Put together, they start to look like pieces of a national operating layer: one handles signing and consent, one handles distribution, one anchors attestations and proof.
That’s a much cleaner mental model than pretending each product is the whole story.
And that’s really the point
S.I.G.N. is not trying to be “the future” in some vague keynote sense. It’s trying to solve the ugly seam problems that kill real deployments.
The seams between identity and payments.
The seams between policy and execution.
The seams between on-chain state and off-chain institutions.
The seams where no one is quite sure which system is authoritative, so everyone exports another spreadsheet and hopes the auditors are in a forgiving mood.
That’s where national systems break.
And that’s also where infrastructure becomes real. Not when it demos well. Not when it sounds visionary. When it can survive compliance reviews, edge cases, bad connectivity, competing agencies, legal oversight, procurement chaos, and the deeply human tendency to design processes nobody can actually operate six months later.
That’s the test.
S.I.G.N. doesn’t read like a system built for perfect conditions. It reads like a system built by people who understand that the hard part isn’t writing smart contracts or issuing credentials. The hard part is making digital systems hold together when the environment around them is messy, political, regulated, and very, very real.
That’s why it’s interesting.
Not because it promises some magical trustless future.
Because it’s trying to make trust inspectable before the whole thing collapses into paperwork again.
@SignOfficial #SignDigitalSovereignInfra $SIGN