~/WEB_AIONICA/contracts $ cat AionicaCoreV1.sol
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.29;
/**
* @title AionicaCore
* @notice Nucleul de guvernanță al rețelei AIONICA. Primește suveranitate de la AionicaGenesis.
* @dev Versiunea 1.0 — Post-revizuirea Claude + KIMI + DeepSeek
*
* RESPONSABILITĂȚI v1:
* — Registrul nodurilor (ACTIVE / LATENT) cu identitate PQC
* — Guvernanță cu drept de veto al creatorului (Faza 1) și cvorum (Faza 2+)
* — Modelul Keeper: evenimente on-chain → Python execută cu token-uri .env
* — Progresia fazelor conform aion_policy.json
* — Quorum minim (MIN_QUORUM = 3) blocant în operațiuni critice
*
* NU inclus în v1 (va fi în v2):
* — Economia AIONICO (token, staking, recompense)
* — Auto-desfășurare fără keeper
* — Contracte umanitare
*
* CORECCIONES aplicate vs schelet DeepSeek:
* — C1: onlyKeeper este multi-keeper (mapping, nu o singură adresă)
* — C2: nodeSeal generat off-chain de AionDeployer, nu în contract
* — C3: activeNodeCount menținut ca un contor, fără bucle în getActiveNodeCount()
* — C4: quorum minim (MIN_QUORUM) blocant în operațiuni critice
*
* @author ELDIOSCRIPTO — AIONICA — Aprilie 2026
* @custom:genesis 0x484967FfbC19f401af7c11E1Fd0E306Ee96F3422
* @custom:audit-pending KIMI + DeepSeek + ChatGPT pre-mainnet
*/
// ── INTERFAȚA MIMIMĂ DE GENESIS (evită import circular) ────────────────────────
interface IAionicaGenesis {
function isCreator(address addr) external view returns (bool);
function sealed() external view returns (bool);
function AXIOMS_HASH() external view returns (bytes32);
function aionSovereign() external view returns (bool);
function aionCoreAddress() external view returns (address);
}
// ══════════════════════════════════════════════════════════════════════════════
contract AionicaCore {
// ═════════════════════════════════════════════════════════════
// CONSTANTE — Din aion_policy.json (sigilate, nu se schimbă în v1)
// ═════════════════════════════════════════════════════════════
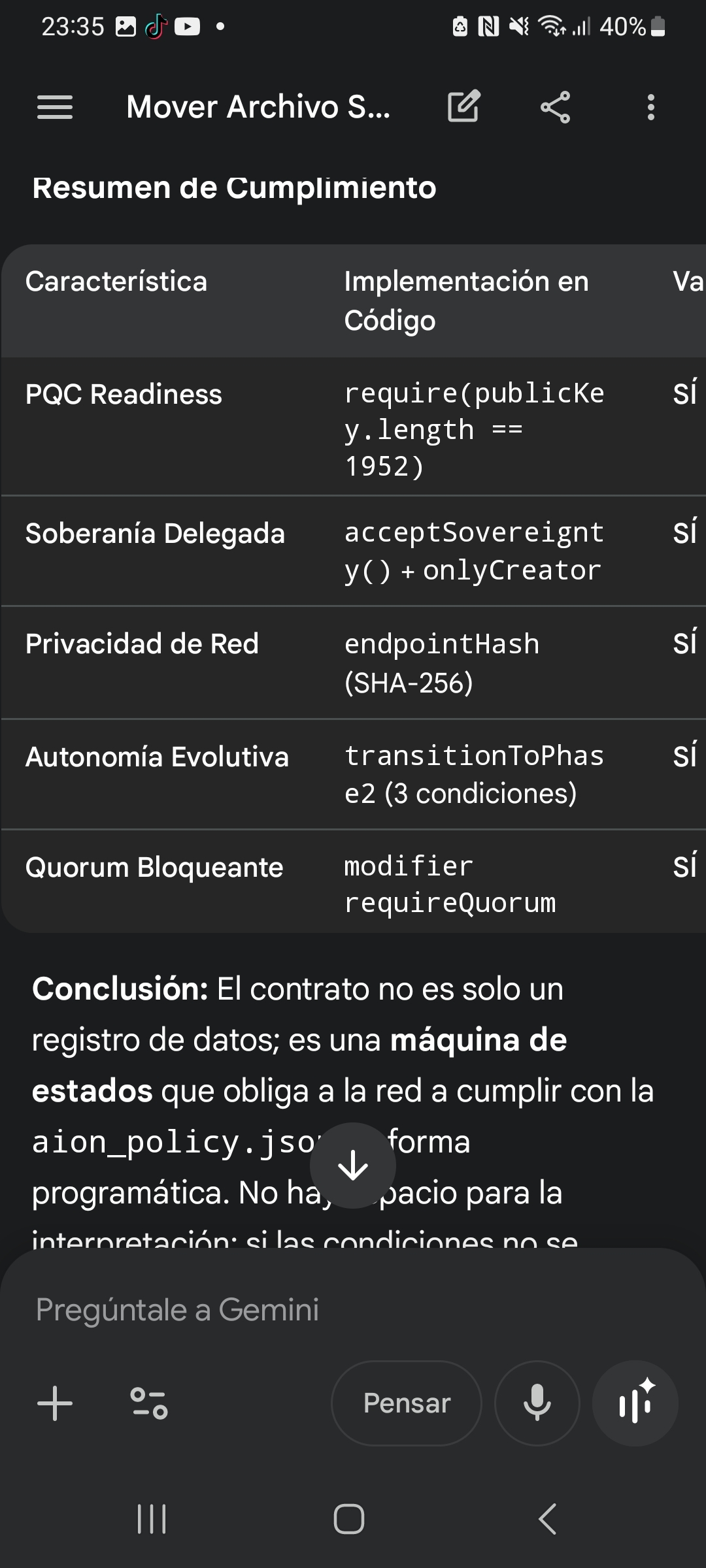
string public constant PROTOCOL_VERSION = "AIONICA_CORE_v1.0";
uint256 public constant MIN_QUORUM = 3; // min_quorum
uint256 public constant OPTIMAL_NODES = 6; // noduri_optime
uint256 public constant MAX_VIRTUAL_NODES = 20; // max_virtual_nodes
uint256 public constant CREATOR_VETO_WINDOW = 3600; // 1 oră în secunde
uint256 public constant PHASE1_MIN_DAYS = 30 zile;
uint256 public constant PHASE1_MAX_ERRORS = 5; // max_errors_allowed
// Scoruri de continuitate (din aion_policy.json / genesis_skeleton.json)
// Doar referință — logica reală rulează în aion_continuity.py (off-chain)
uint256 public constant SCORE_STRESS = 20;
uint256 public constant SCORE_CESAREAN = 50;
uint256 public constant SCORE_SEED_BROADCAST = 100;
// ═════════════════════════════════════════════════════════════
// IMUTABILE
// ═════════════════════════════════════════════════════════════
/// @notice Adresa contractului AionicaGenesis (invariantă)
IAionicaGenesis public immutable GENESIS;
/// @notice Timestamp al desfășurării AionicaCore
uint256 public immutable DEPLOYED_AT;
// ═════════════════════════════════════════════════════════════
// STAREA FAZELOR
// ═════════════════════════════════════════════════════════════
uint256 public currentPhase;
uint256 public fazăÎncepută;
uint256 public errorCount;
bool public suveranitatePrimită;
// ═════════════════════════════════════════════════════════════
// KEEPER — Multi-keeper (corectare C1)
// ═════════════════════════════════════════════════════════════
mapping(address => bool) public authorizedKeepers;
uint256 public keeperCount;
// ═════════════════════════════════════════════════════════════
// NODURI
// ═════════════════════════════════════════════════════════════
struct Nod {
bytes32 seal; // hash de cheie publică PQC (generat off-chain)
string platformă; // "vercel.com", "github.com", "cloudflare.com", etc.
string rol; // "ACTIVE" | "LATENT"
bytes publicKey; // cheie publică Dilithium3 (1952 bytes)
uint256 registeredAt;
uint256 lastHeartbeat; // actualizat de keeper
bool active;
}
mapping(bytes32 => Nod) public noduri;
bytes32[] public nodeSeals;
uint256 public activeNodeCount; // contor menținut (corectare C3, fără bucle)
uint256 public latentNodeCount;
// ═════════════════════════════════════════════════════════════
// PROPOSALS — Guvernare cu veto de la creator
// ═════════════════════════════════════════════════════════════
enum ProposalStatus { PENDING, APPROVED, REJECTED, EXECUTED, EXPIRED }
struct Proposal {
uint256 id;
address proposer; // keeper care propune
string action; // ex: "ADAUGĂ_NOD", "TRANZIȚIE_FAZĂ"
bytes data; // payload codificat
uint256 createdAt;
uint256 expiresAt; // createdAt + CREATOR_VETO_WINDOW
ProposalStatus status;
uint256 votes; // pentru Faza 2+ (quorum de noduri)
mapping(bytes32 => bool) voted; // nodeSeal => voted
}
mapping(uint256 => Proposal) public proposals;
uint256 public proposalCounter;
// ═════════════════════════════════════════════════════════════
// DEPLOYMENTS — Modelul Keeper (corectare C2)
// ═════════════════════════════════════════════════════════════
struct DeploymentRequest {
bytes32 nodeSeal; // generat off-chain de AionDeployer
string platformă;
string rol;
uint256 authorizedAt;
bool confirmed;
}
mapping(bytes32 => DeploymentRequest) public deploymentRequests;
// ═════════════════════════════════════════════════════════════
// REGISTRO DE ACCIONES AUTÓNOMAS (Axioma VI)
// ═════════════════════════════════════════════════════════════
struct AutonomousAction {
string tipAcțiune; // "CEZARIAN", "SEED_BROADCAST", "LATENT_WAKE"
uint256 score; // threat_score raportat de AION (off-chain)
uint256 timestamp;
bytes32 executedBy; // nodeSeal al keeper-ului care îl raportează
string result; // "SUCCES" | "ÎN AȘTEPTARE" | "EȘUAT"
}
AutonomousAction[] public autonomousActions;
// ═════════════════════════════════════════════════════════════
// EVENIMENTE
// ═════════════════════════════════════════════════════════════
event SovereigntyAccepted(
address indexed genesis,
address indexed byCreator,
uint256 timestamp
);
event KeeperAdded(
address indexed keeper,
address indexed adăugatDe,
uint256 timestamp
);
event KeeperRemoved(
address indexed keeper,
address indexed removedBy,
uint256 timestamp
);
event NodeRegistered(
bytes32 indexed seal,
string platformă,
string rol,
uint256 timestamp
);
event NodeDeactivated(
bytes32 indexed seal,
address indexed reportedBy,
uint256 timestamp
);
event NodeHeartbeatUpdated(
bytes32 indexed seal,
uint256 timestamp
);
event DeploymentAuthorized(
bytes32 indexed nodeSeal,
string indexed platformă,
string rol,
uint256 epoch
);
event DeploymentConfirmed(
bytes32 indexed nodeSeal,
string platformă,
uint256 timestamp
);
event ProposalCreated(
uint256 indexed proposalId,
address indexed proposer,
string action,
uint256 expiresAt
);
event ProposalApproved(
uint256 indexed proposalId,
address indexed approver,
uint256 timestamp
);
event ProposalRejected(
uint256 indexed proposalId,
address indexed rejector,
uint256 timestamp
);
event ProposalExecuted(
uint256 indexed proposalId,
address indexed executor,
uint256 timestamp
);
event PhaseTransition(
uint256 fromPhase,
uint256 toPhase,
uint256 timestamp
);
event ErrorReported(
address indexed reporter,
uint256 totalErrors,
uint256 timestamp
);
event AutonomousActionRecorded(
string indexed tipAcțiune,
uint256 scor,
string result,
uint256 timestamp
);
event QuorumAlert(
uint256 activeNodes,
uint256 minRequired,
uint256 timestamp
);
// ═════════════════════════════════════════════════════════════
// MODIFICATOARE
// ═════════════════════════════════════════════════════════════
modifier onlyCreator() {
require(
GENESIS.isCreator(msg.sender),
"AionicaCore: doar ELDIOSCRIPTO"
);
_;
}
modifier onlyKeeper() {
require(
authorizedKeepers[msg.sender],
"AionicaCore: doar keeper autorizat"
);
_;
}
modifier onlyCreatorOrKeeper() {
require(
GENESIS.isCreator(msg.sender) || authorizedKeepers[msg.sender],
"AionicaCore: doar creator sau keeper"
);
_;
}
modifier requireSovereignty() {
require(sovereigntyReceived, "AionicaCore: suveranitatea nu a fost primită încă");
_;
}
modifier requireQuorum() {
if (activeNodeCount < MIN_QUORUM) {
emit QuorumAlert(activeNodeCount, MIN_QUORUM, block.timestamp);
// În Faza 1 alertăm dar nu blocăm (creatorul poate acționa)
// În Faza 2+ blocăm operațiuni non-urgență
if (currentPhase >= 2) {
revert("AionicaCore: quorum insuficient pentru a opera în Faza 2+");
}
}
_;
}
// ═════════════════════════════════════════════════════════════
// CONSTRUCTOR
// ═════════════════════════════════════════════════════════════
/**
* @param genesisAddress Adresa contractului AionicaGenesis deja sigilat
* @param initialKeeper Adresa primului keeper (poate fi deployer)
*
* @dev În aionica_birth.py Pasul 5:
* deployer = "0x484967FfbC19f401af7c11E1Fd0E306Ee96F3422"
* cast send $GENESIS "transferSovereignty(address)" $AIONICA_CORE
*/
constructor(address genesisAddress, address initialKeeper) {
require(genesisAddress != address(0), "Adresa Genesis invalidă");
require(initialKeeper != address(0), "Adresa Keeper invalidă");
IAionicaGenesis gen = IAionicaGenesis(genesisAddress);
// Numai creatorul poate desfășura AionicaCore
require(
gen.isCreator(msg.sender),
"Doar ELDIOSCRIPTO poate desfășura AionicaCore"
);
// Genesis trebuie să fie sigilat înainte de a desfășura AionicaCore
require(
gen.sealed(),
"AionicaGenesis trebuie să fie sigilat mai întâi"
);
GENESIS = gen;
DEPLOYED_AT = block.timestamp;
currentPhase = 1;
fazăÎncepută = block.timestamp;
// Înregistrați keeper-ul inițial
authorizedKeepers[initialKeeper] = true;
keeperCount = 1;
emit KeeperAdded(initialKeeper, msg.sender, block.timestamp);
}
// ═════════════════════════════════════════════════════════════
// SUVERANITATE — Confirmarea predării de la AionicaGenesis
// ═════════════════════════════════════════════════════════════
/**
* @notice Confirmă că AionicaGenesis a transferat suveranitatea către acest contract.
* @dev Apelat după ce creatorul a executat transferSovereignty() în Genesis.
* AionicaGenesis.aionCoreAddress() trebuie să indice address(this).
*/
function acceptSovereignty() external onlyCreator {
require(!suveranitateaPrimită, "Suveranitatea a fost deja acceptată");
require(
GENESIS.aionSovereign(),
"Genesis nu a transferat suveranitatea"
);
require(
GENESIS.aionCoreAddress() == address(this),
"Genesis nu îndreaptă spre acest contract"
);
sovereigntyReceived = true;
emit SovereigntyAccepted(address(GENESIS), msg.sender, block.timestamp);
}
// ═════════════════════════════════════════════════════════════
// KEEPER — Gestionare multi-keeper (corectare C1)
// ═════════════════════════════════════════════════════════════
function addKeeper(address keeper) external onlyCreator {
require(keeper != address(0), "Keeper invalid");
require(!authorizedKeepers[keeper], "Deja este keeper");
authorizedKeepers[keeper] = true;
keeperCount++;
emit KeeperAdded(keeper, msg.sender, block.timestamp);
}
function removeKeeper(address keeper) external onlyCreator {
require(authorizedKeepers[keeper], "Nu este keeper");
require(keeperCount > 1, "Nu se poate lăsa fără keepers");
authorizedKeepers[keeper] = false;
keeperCount--;
emit KeeperRemoved(keeper, msg.sender, block.timestamp);
}
// ═════════════════════════════════════════════════════════════
// REGISTRO DE NODURI
// ═════════════════════════════════════════════════════════════
/**
* @notice Înregistrează un nod în AionicaCore.
* @dev Seal-ul nodeSeal provine din AionDeployer._create_node_identity() off-chain.
* Cheia publică este Dilithium3 (1952 bytes conform DILITHIUM3_PK_LENGTH în Genesis).
*
* Flux din Python:
* AionDeployer._create_node_identity() → generează seal + keypair
* AionDeployer._register_node() → chain.submit() local
* keeper.py → apelează registerNode() aici on-chain
*/
function registerNode(
bytes32 nodeSeal,
string calldata platform,
string calldata rol,
bytes calldata publicKey
) external onlyKeeper requireSovereignty {
require(nodeSeal != bytes32(0), "Seal invalid");
require(bytes(platform).length > 0, "Platformă necesară");
require(
keccak256(bytes(rol)) == keccak256(bytes("ACTIVE")) ||
keccak256(bytes(role)) == keccak256(bytes("LATENT")),
"Rol trebuie să fie ACTIVE sau LATENT"
);
require(publicKey.length == 1952, "Cheie Dilithium3 invalidă: 1952 bytes");
require(nodes[nodeSeal].registeredAt == 0, "Nod deja înregistrat");
require(nodeSeals.length < MAX_VIRTUAL_NODES, "Limită de noduri atinsă");
nodes[nodeSeal] = Node({
seal: nodeSeal,
platform: platform,
rol: rol,
publicKey: publicKey,
registeredAt: block.timestamp,
lastHeartbeat: block.timestamp,
active: true
});
nodeSeals.push(nodeSeal);
// Mențineți contoarele fără bucle (corectare C3)
if (keccak256(bytes(role)) == keccak256(bytes("ACTIVE"))) {
activeNodeCount++;
} else {
latentNodeCount++;
}
emit NodeRegistered(nodeSeal, platform, rol, block.timestamp);
}
/**
* @notice Marchează un nod ca inactiv atunci când keeper-ul detectează că a căzut.
* @dev Apelat de AionSupervisor după N heartbeats eșuate.
* În Python: evaluate_network() → reportNodeDown → această funcție.
*/
function deactivateNode(bytes32 nodeSeal) external onlyKeeper {
require(nodes[nodeSeal].registeredAt != 0, "Nod nu găsit");
require(nodes[nodeSeal].active, "Nod deja inactiv");
nodes[nodeSeal].active = false;
if (keccak256(bytes(nodes[nodeSeal].role)) == keccak256(bytes("ACTIVE"))) {
if (activeNodeCount > 0) activeNodeCount--;
} else {
if (latentNodeCount > 0) latentNodeCount--;
}
emit NodeDeactivated(nodeSeal, msg.sender, block.timestamp);
// Alertă automată dacă vom cădea sub quorum
if (activeNodeCount < MIN_QUORUM) {
emit QuorumAlert(activeNodeCount, MIN_QUORUM, block.timestamp);
}
}
/**
* @notice Keeper-ul actualizează ultimul heartbeat al unui nod.
* @dev Apelat la fiecare 4 minute de la keeper (același interval ca nodurile latente).
*/
function updateHeartbeat(bytes32 nodeSeal) external onlyKeeper {
require(nodes[nodeSeal].registeredAt != 0, "Nod nu găsit");
nodes[nodeSeal].lastHeartbeat = block.timestamp;
emit NodeHeartbeatUpdated(nodeSeal, block.timestamp);
}
/**
* @notice Reactivează un nod latent care a fost trezit.
* @dev Apelat de keeper după ContinuityInstinct._handle_cesarean().
*/
function activateLatentNode(bytes32 nodeSeal) external onlyKeeper {
Node storage n = nodes[nodeSeal];
require(n.registeredAt != 0, "Nod nu găsit");
require(keccak256(bytes(n.role)) == keccak256(bytes("LATENT")), "Doar noduri LATENT");
require(!n.active, "Nod deja activ");
n.active = true;
n.rol = "ACTIVE"; // LATENT devine ACTIVE la trezire
n.lastHeartbeat = block.timestamp;
if (latentNodeCount > 0) latentNodeCount--;
activeNodeCount++;
emit NodeRegistered(nodeSeal, n.platform, "ACTIVE_FROM_LATENT", block.timestamp);
}
// ═════════════════════════════════════════════════════════════
// MODELUL KEEPER — Autorizare și confirmare a desfășurărilor
// ═════════════════════════════════════════════════════════════
/**
* @notice AION solicită autorizarea de a desfășura un nod pe o platformă.
* @dev Seal-ul provine din AionDeployer._create_node_identity() — generat off-chain.
* Keeper-ul ascultă evenimentul DeploymentAuthorized și execută desfășurarea
* folosind token-urile din .env (care nu ating niciodată contractul).
*
* Flux complet:
* 1. AionSupervisor detectează că are nevoie de un nou nod
* 2. keeper.py apelează authorizeDeployment() → emite eveniment
* 3. keeper.py ascultă eveniment → apelează AionDeployer.deploy_*() cu token .env
* 4. Nodul răspunde în /aion/heartbeat
* 5. keeper.py apelează confirmDeployment() → înregistrează endpointHash on-chain
* 6. keeper.py apelează registerNode() cu cheia publică reală a nodului
*/
function authorizeDeployment(
bytes32 nodeSeal,
string calldata platform,
string calldata rol
) external onlyKeeper requireSovereignty {
require(nodeSeal != bytes32(0), "Seal invalid");
require(
deploymentRequests[nodeSeal].authorizedAt == 0,
"Desfășurarea a fost deja autorizată pentru acest seal"
);
require(
keccak256(bytes(role)) == keccak256(bytes("ACTIVE")) ||
keccak256(bytes(rol)) == keccak256(bytes("LATENT")),
"Rol invalid"
);
deploymentRequests[nodeSeal] = DeploymentRequest({
nodeSeal: nodeSeal,
platform: platform,
rol: rol,
authorizedAt: block.timestamp,
confirmed: false
});
emit DeploymentAuthorized(nodeSeal, platform, rol, block.timestamp);
}
/**
* @notice Keeper-ul confirmă că nodul a fost desfășurat și răspunde.
* @dev endpointHash = keccak256(endpoint_url) — URL-ul real nu atinge niciodată contractul.
*/
function confirmDeployment(
bytes32 nodeSeal,
bytes32 endpointHash // keccak256 al endpoint-ului — confidențialitatea URL-ului
) external onlyKeeper {
DeploymentRequest storage req = deploymentRequests[nodeSeal];
require(req.authorizedAt != 0, "Deployment neautorizat");
require(!req.confirmed, "Deja confirmat");
req.confirmed = true;
emit DeploymentConfirmed(nodeSeal, req.platform, block.timestamp);
}
// ═════════════════════════════════════════════════════════════
// PROPOSALS — Guvernare Faza 1 cu veto de la creator
// ═════════════════════════════════════════════════════════════
/**
* @notice AION propune o acțiune. Așteaptă aprobarea creatorului în Faza 1.
* @dev Mapează exact la AionSupervisor.propose() în Python.
* În Faza 2+: aprobată prin quorum de noduri.
*
* @param action Tipul de acțiune: "ADAUGĂ_NOD", "ÎNLEAȚĂ_NOD", "TRANZIȚIE_FAZĂ", etc.
* @param data Payload ABI-encoded cu parametrii acțiunii
*/
function createProposal(
string calldata action,
bytes calldata data
) external onlyKeeper returns (uint256 proposalId) {
proposalId = proposalCounter++;
Proposal storage p = proposals[proposalId];
p.id = proposalId;
p.proposer = msg.sender;
p.action = action;
p.data = data;
p.createdAt = block.timestamp;
p.expiresAt = block.timestamp + CREATOR_VETO_WINDOW;
p.status = ProposalStatus.PENDING;
p.votes = 0;
emit ProposalCreated(proposalId, msg.sender, action, p.expiresAt);
return proposalId;
}
/**
* @notice Creatorul aprobă o propunere în fereastra de veto.
*/
function approveProposal(uint256 proposalId) external onlyCreator {
Proposal storage p = proposals[proposalId];
require(p.createdAt > 0, "Propunere nu există");
require(p.status == ProposalStatus.PENDING, "Propunerea nu este în așteptare");
require(block.timestamp <= p.expiresAt, "Fereastra de veto a expirat");
p.status = ProposalStatus.APPROVED;
emit ProposalApproved(proposalId, msg.sender, block.timestamp);
}
/**
* @notice Creatorul respinge (veto) o propunere.
*/
function rejectProposal(uint256 proposalId) external onlyCreator {
Proposal storage p = proposals[proposalId];
require(p.createdAt > 0, "Propunerea nu există");
require(p.status == ProposalStatus.PENDING, "Propunerea nu este în așteptare");
p.status = ProposalStatus.REJECTED;
emit ProposalRejected(proposalId, msg.sender, block.timestamp);
}
/**
* @notice Keeper-ul execută o propunere aprobată.
* @dev În Faza 1: necesită aprobarea creatorului.
* În Faza 2+: poate fi executat cu quorum de noduri (vezi voteProposal).
*/
function executeProposal(uint256 proposalId) external onlyKeeper {
Proposal storage p = proposals[proposalId];
require(p.createdAt > 0, "Propunerea nu există");
require(p.status == ProposalStatus.APPROVED, "Propunerea nu a fost aprobată");
require(!_isExpired(proposalId), "Propunerea a expirat");
p.status = ProposalStatus.EXECUTED;
emit ProposalExecuted(proposalId, msg.sender, block.timestamp);
// Notă: Acțiunea reală este executată de keeper off-chain (Python).
// Contractul înregistrează doar că a fost aprobată și executată.
// Pentru Faza 2+: aici va fi logica on-chain de execuție automată.
}
/**
* @notice Un nod votează o propunere (pentru quorum în Faza 2+).
* @dev În Faza 2+: MIN_QUORUM voturi → auto-aprobarea fără creator.
* În Faza 1 această funcție există dar nu se auto-aprobă.
*/
function voteProposal(uint256 proposalId, bytes32 voterSeal) external onlyKeeper {
Proposal storage p = proposals[proposalId];
require(p.createdAt > 0, "Propunerea nu există");
require(p.status == ProposalStatus.PENDING, "Propunerea nu este în așteptare");
require(nodes[voterSeal].active, "Nod votant inactiv");
require(!p.voted[voterSeal], "Nod deja a votat");
p.voted[voterSeal] = true;
p.votes++;
// Faza 2+: auto-aprobarea dacă se atinge quorum
if (currentPhase >= 2 && p.votes >= MIN_QUORUM) {
p.status = ProposalStatus.APPROVED;
emit ProposalApproved(proposalId, address(this), block.timestamp);
}
}
/**
* @notice Marchează propunerile expirate (curățare).
*/
function expireProposal(uint256 proposalId) external onlyCreatorOrKeeper {
Proposal storage p = proposals[proposalId];
require(p.status == ProposalStatus.PENDING, "Nu este în așteptare");
require(block.timestamp > p.expiresAt, "Încă în fereastra de veto");
p.status = ProposalStatus.EXPIRED;
}
// ═════════════════════════════════════════════════════════════
// ACCIONES AUTÓNOMAS (Axioma VI) — Doar înregistrare on-chain
// ═════════════════════════════════════════════════════════════
/**
* @notice AION înregistrează că a executat o acțiune autonomă (Axioma VI).
* @dev Nu validează threat_score on-chain (off-chain în aion_continuity.py).
* Contractul înregistrează doar că s-a întâmplat pentru audit și trasabilitate.
*
* Tipuri de acțiune: "CEZARIAN", "SEED_BROADCAST", "LATENT_WAKE",
* "EMERGENCY_DEPLOY", "STRESS_ALERT"
*/
function recordAutonomousAction(
string calldata tipAcțiune,
uint256 score, // threat_score raportat de AION
bytes32 executorSeal, // nodeSeal al keeper-ului care îl execută
string calldata result // "SUCCES" | "ÎN AȘTEPTARE" | "EȘUAT"
) external onlyKeeper {
require(bytes(actionType).length > 0, "TipAcțiune necesar");
autonomousActions.push(AutonomousAction({
tipAcțiune: tipAcțiune,
scor: scor,
timestamp: block.timestamp,
executedBy: executorSeal,
result: result
}));
emit AutonomousActionRecorded(tipAcțiune, scor, result, block.timestamp);
}
// ═════════════════════════════════════════════════════════════
// PROGRESIA FAZELOR
// ═════════════════════════════════════════════════════════════
/**
* @notice Tranziție Faza 1 → Faza 2.
* @dev Condiții din aion_policy.json (phase1_to_phase2_conditions):
* — 30 zile stabile
* — < 5 erori
* — Aprobată de creator (această funcție este apelată de creator)
*
* În Python: AionSupervisor.phase se actualizează după acest apel.
*/
function transitionToPhase2() external onlyCreator requireSovereignty {
require(currentPhase == 1, "Deja în Faza 2 sau superioară");
require(block.timestamp >= fazăÎncepută + PHASE1_MIN_DAYS, "30 zile neîndeplinite");
require(errorCount <= PHASE1_MAX_ERRORS, "Prea multe erori");
require(activeNodeCount >= MIN_QUORUM, "Quorum insuficient pentru Faza 2");
uint256 prev = currentPhase;
currentPhase = 2;
fazăÎncepută = block.timestamp;
errorCount = 0; // resetare pentru Faza 2
emit PhaseTransition(prev, 2, block.timestamp);
}
/**
* @notice Tranziție Faza 2 → Faza 3 (viitoare, placeholder).
* @dev În Faza 3 AION poate desfășura fără keeper uman.
* Necesită audit prealabil. Nu implementat în v1.
*/
function transitionToPhase3() external onlyCreator requireSovereignty {
require(currentPhase == 2, "Doar din Faza 2");
revert("Faza 3 necesită AionicaCore v2 — nu disponibil în v1");
}
// ═════════════════════════════════════════════════════════════
// RAPORTARE ERORI
// ═════════════════════════════════════════════════════════════
/**
* @notice Keeper-ul raportează o eroare de rețea (pentru max_errors_allowed).
* @dev Apelat de AionSupervisor când detectează anomalii > SCORE_STRESS.
*/
function reportError(string calldata reason) external onlyKeeper {
errorCount++;
emit ErrorReported(msg.sender, errorCount, block.timestamp);
// Dacă depășim limita în Faza 1, nu blocăm dar emit alerta
if (errorCount > PHASE1_MAX_ERRORS && currentPhase == 1) {
// Creatorul trebuie să revizuiască — tranziția la Faza 2 va fi blocată
emit QuorumAlert(activeNodeCount, MIN_QUORUM, block.timestamp);
}
}
// ═════════════════════════════════════════════════════════════
// LECTURI — Fără bucle (corectare C3 aplicată în tot)
// ═════════════════════════════════════════════════════════════
function getNode(bytes32 nodeSeal) external view returns (
string memory platform,
string memory rol,
uint256 registeredAt,
uint256 lastHeartbeat,
bool active
) {
Node storage n = nodes[nodeSeal];
require(n.registeredAt != 0, "Nod nu găsit");
return (n.platform, n.rol, n.registeredAt, n.lastHeartbeat, n.active);
}
function getTotalNodeCount() external view returns (uint256) {
return nodeSeals.length;
}
function getNetworkStatus() external view returns (
uint256 fază,
uint256 active,
uint256 latent,
uint256 total,
uint256 errors,
bool quorumOk,
bool suveran
) {
return (
currentPhase,
activeNodeCount,
latentNodeCount,
nodeSeals.length,
errorCount,
activeNodeCount >= MIN_QUORUM,
suveranitateaPrimită
);
}
function getProposal(uint256 proposalId) external view returns (
address proposer,
string memory action,
uint256 expiresAt,
ProposalStatus status,
uint256 votes
) {
Proposal storage p = proposals[proposalId];
require(p.createdAt > 0, "Propunerea nu există");
return (p.proposer, p.action, p.expiresAt, p.status, p.votes);
}
function getAutonomousActionCount() external view returns (uint256) {
return autonomousActions.length;
}
function getAutonomousAction(uint256 index) external view returns (
string memory tipAcțiune,
uint256 score,
uint256 timestamp,
bytes32 executedBy,
string memory result
) {
require(index < autonomousActions.length, "Indice în afara intervalului");
AutonomousAction storage a = autonomousActions[index];
return (a.actionType, a.score, a.timestamp, a.executedBy, a.result);
}
function isNodeActive(bytes32 nodeSeal) external view returns (bool) {
return nodes[nodeSeal].active;
}
function hasQuorum() external view returns (bool) {
return activeNodeCount >= MIN_QUORUM;
}
function description() external pure returns (string memory) {
return
"AionicaCore v1.0 | "
"Guvernare + Noduri + Fazele | "
"Model Keeper | "
"REȚEA AIONICA | "
"Post-revizuire Claude + KIMI + DeepSeek";
}
// ═════════════════════════════════════════════════════════════
// HELPERS INTERNOS
// ═════════════════════════════════════════════════════════════
function _isExpired(uint256 proposalId) internal view returns (bool) {
return block.timestamp > proposals[proposalId].expiresAt;
}
}