Most blockchains treat transparency as a feature.
But for many real-world applications, transparency is actually the problem.
Payroll, credit scoring, medical data, corporate finance, and even property ownership all require verification without exposure. You need to prove something is true without revealing the underlying data.
This is the exact design philosophy behind Midnight.
Instead of building another privacy coin focused purely on anonymity, Midnight is designed as privacy infrastructure where developers can control what data is public and what remains confidential.
And the architecture behind it is much deeper than most people realize.
The problem with traditional token systems
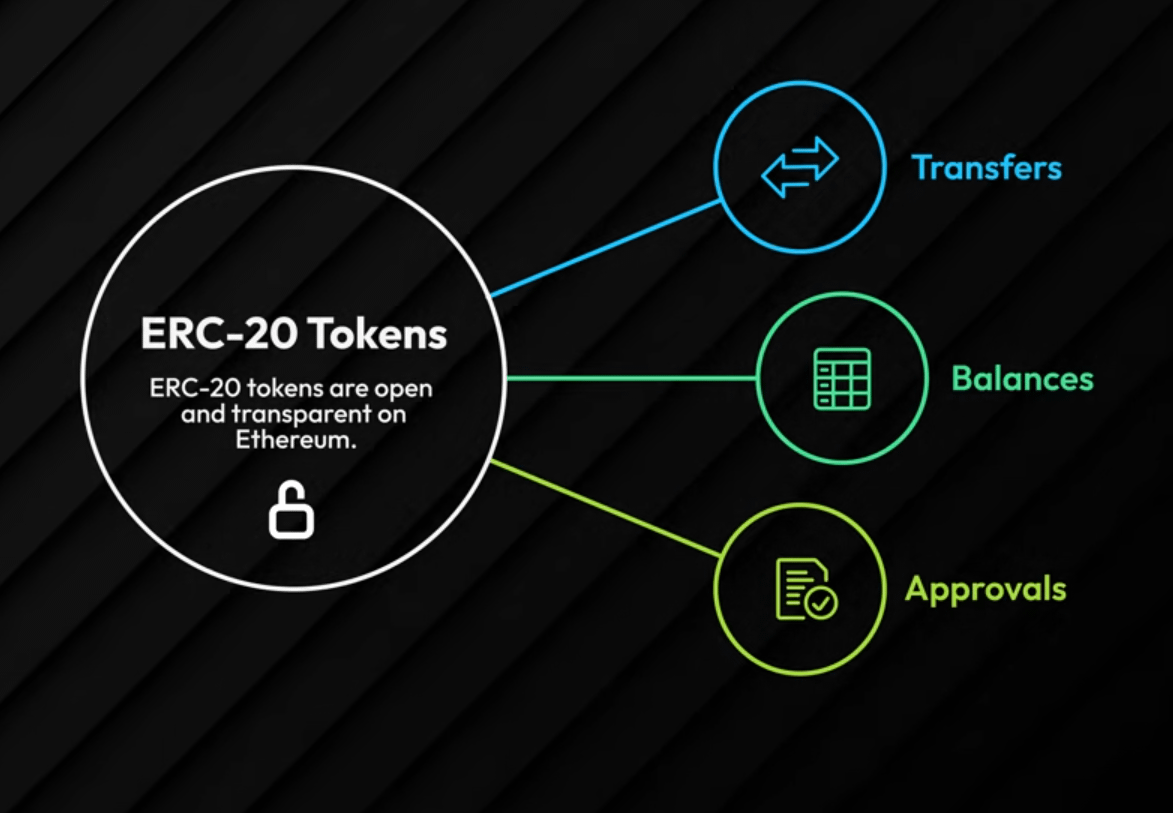
On networks like Ethereum, tokens follow standards such as ERC-20.
Every transaction exposes:
• sender
• receiver
• balance
• allowances
• full transaction history
This radical transparency is useful for open finance, but it breaks many real-world use cases.
A company cannot run payroll if everyone can see employee salaries.
Banks cannot publish customer loan data publicly.
Institutions cannot reveal their full treasury movements on-chain.
This is where Midnight introduces a different model.
Instead of forcing every asset into one transparent ledger, Midnight introduces multiple token environments where privacy levels can be configured depending on the application.
A hybrid privacy token model
Midnight divides tokens into four categories:
• Unshielded Ledger Tokens
• Shielded Ledger Tokens
• Unshielded Contract Tokens
• Shielded Contract Tokens
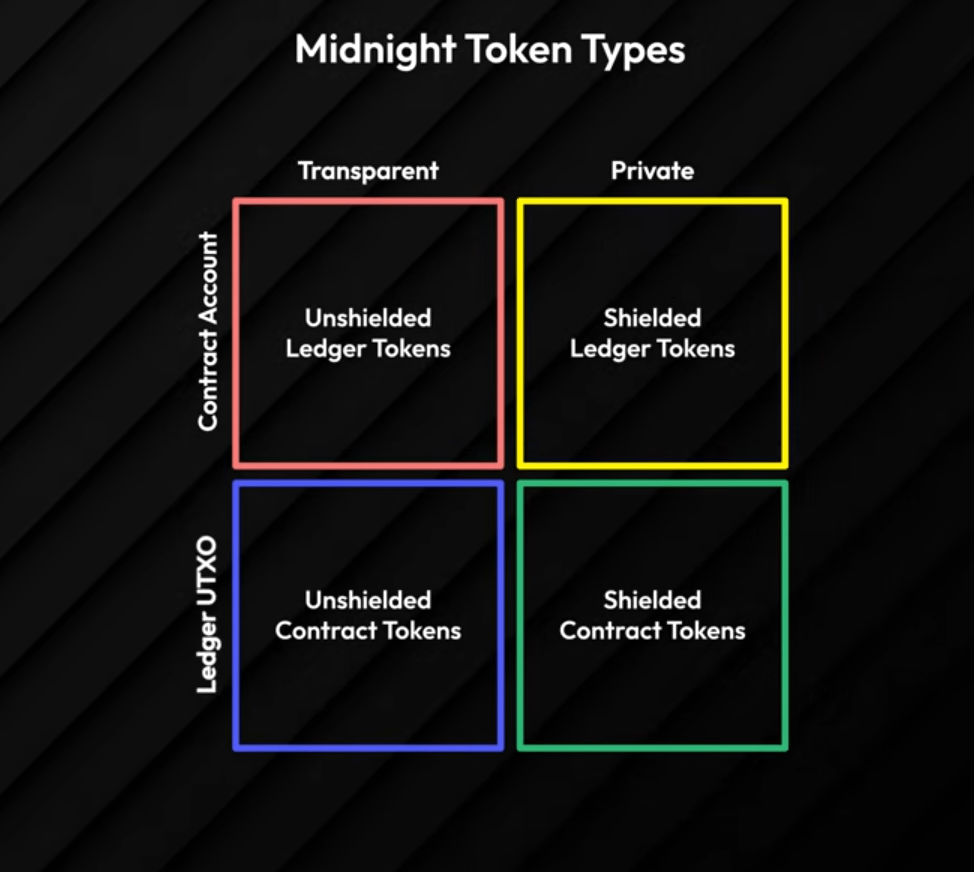
This structure allows a single application to combine both transparent and private assets.
For example:
A lending protocol could use:
• transparent governance tokens
• shielded collateral balances
• private borrower credit scores
All verified cryptographically without revealing sensitive information.
This approach turns privacy from a fixed property into a programmable feature of the protocol itself.
How Midnight executes private smart contracts
Most blockchains execute smart contracts directly on-chain.
Midnight takes a completely different route.
Developers write contracts in Compact, a language designed specifically for zero-knowledge environments.
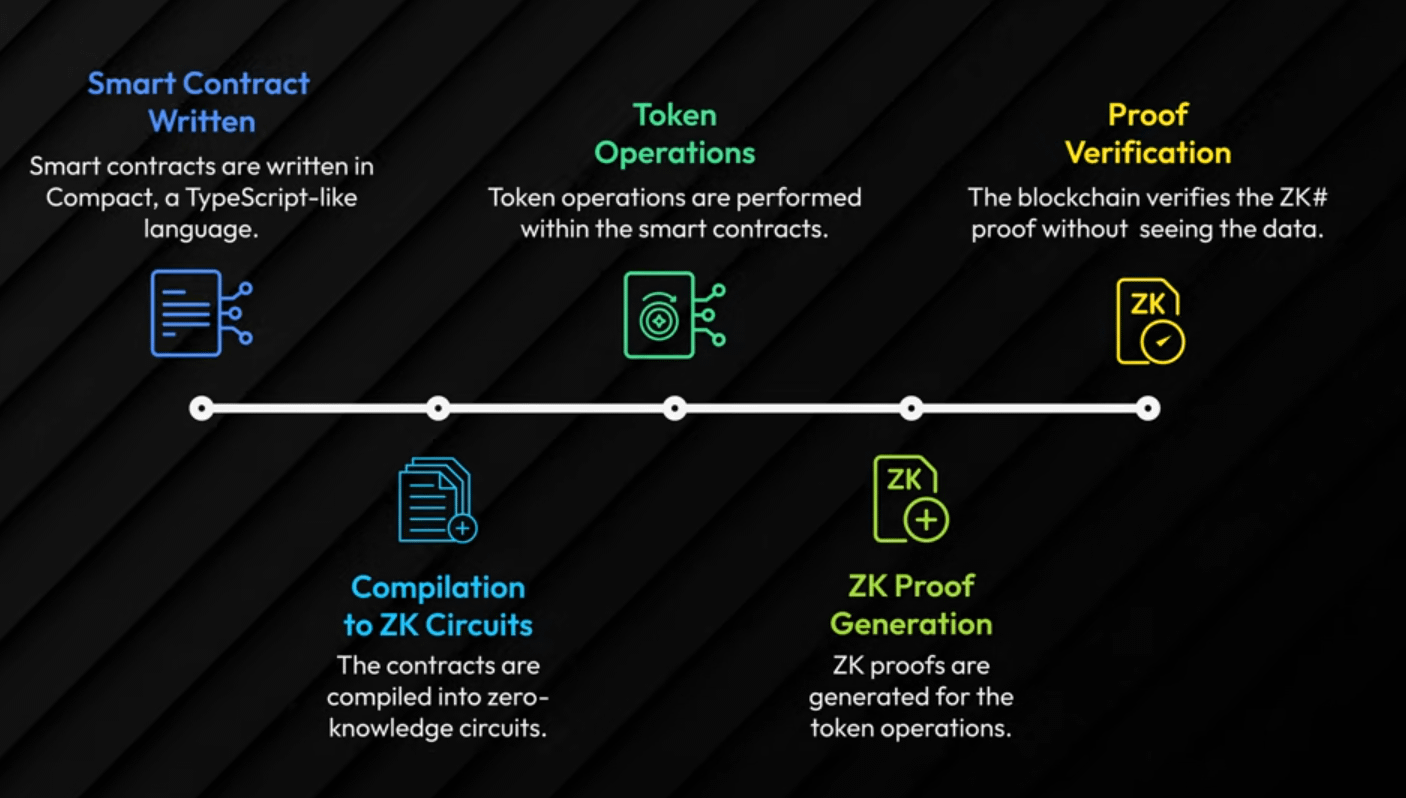
The execution pipeline works roughly like this:
1️⃣ Contract logic written in Compact
2️⃣ Compiled into zero-knowledge circuits
3️⃣ Proof generated off-chain
4️⃣ Blockchain verifies the proof
The chain verifies that the computation was correct without seeing the underlying data.
This mechanism is what enables selective disclosure, one of Midnight’s most important features.
For example, a user could prove:
• they passed KYC
• they hold sufficient collateral
• they meet regulatory requirements
without revealing their wallet balance or identity.
Why this matters for institutions
Most privacy chains aim for complete anonymity.
But anonymity alone rarely works for regulated industries.
Banks, funds, and enterprises must prove compliance to regulators.
Midnight’s approach allows both:
• privacy for users
• auditability for institutions
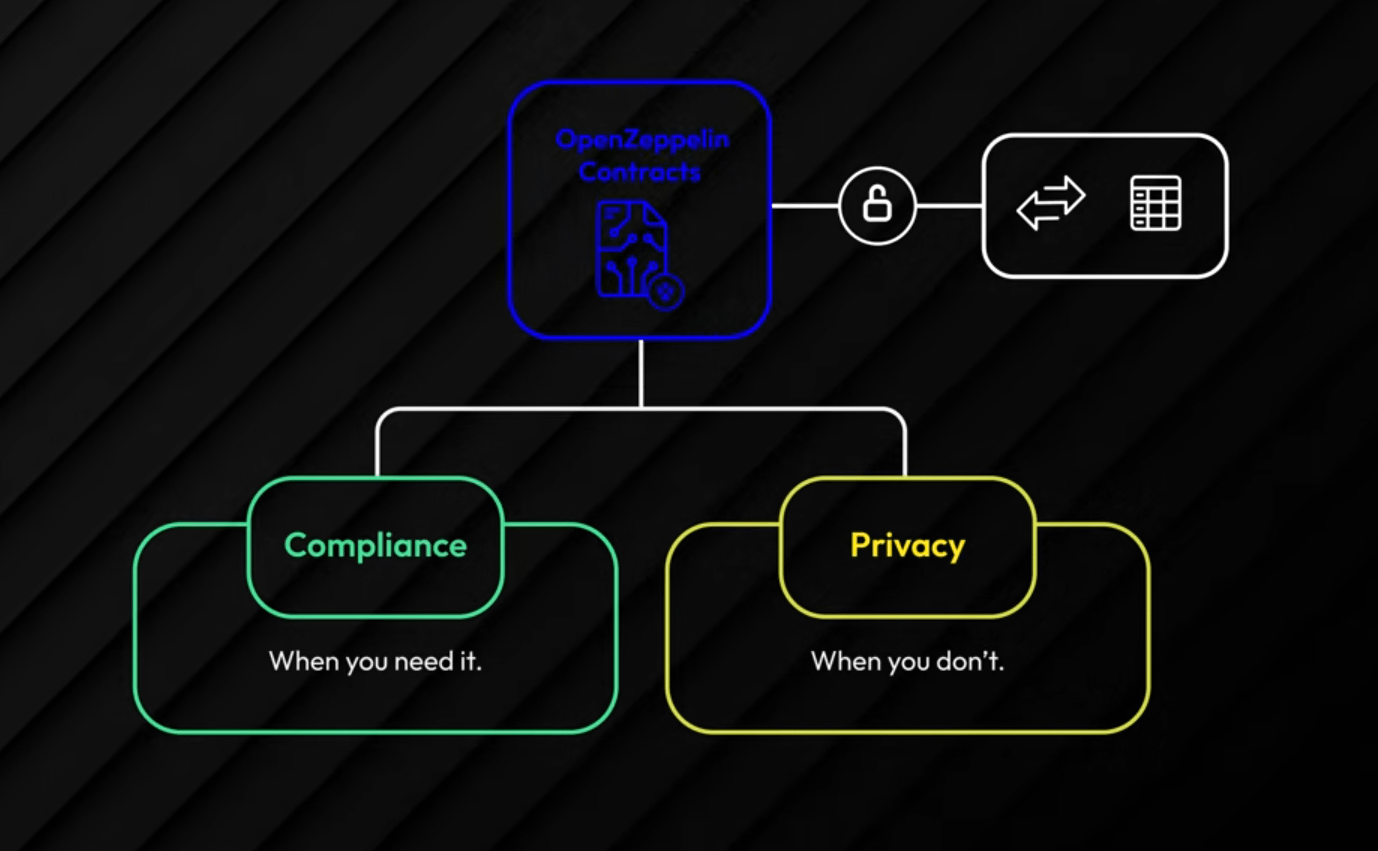
This architecture allows systems where data remains confidential while proofs demonstrate regulatory compliance.
That combination could unlock entirely new financial primitives such as:
• private lending markets
• confidential payroll systems
• tokenized real-world assets
• verifiable credit scoring
Optimized token design for zero-knowledge systems
Even the token mechanics themselves are optimized for zero-knowledge computation.
For example, Midnight tokens use Uint128 instead of Uint256.
At first glance this looks minor, but it matters.
Zero-knowledge circuits operate within mathematical fields where smaller integers reduce:
• circuit complexity
• proof generation time
• verification costs
These small engineering decisions show that Midnight wasn’t built as a traditional blockchain with privacy added later.
It was designed from the ground up for ZK computation.
Extending privacy to digital assets
The same architecture applies to both fungible tokens and NFTs.

Fungible tokens can represent assets like:
• stablecoins
• tokenized securities
• payment tokens
• governance assets
But their balances and transfers can remain shielded.
NFTs can also benefit from privacy.
In most NFT markets, ownership is completely public.
Midnight allows ownership proofs without revealing identity, opening the door to applications such as:
• confidential ownership of luxury assets
• private identity credentials
• tokenized legal documents
Multi-asset systems under one privacy framework
For complex financial systems, assets rarely exist in isolation.
Protocols interact with multiple tokens simultaneously.
Midnight introduces a Multi-Token Module designed to manage these assets under a unified privacy framework.
This becomes essential for applications such as:
• decentralized exchanges
• lending protocols
• tokenized funds
• cross-asset financial products
All operating with selective privacy guarantees.
The bigger picture
Most people think of privacy chains as tools for hiding transactions.
Midnight approaches privacy differently.
It treats privacy as a programmable layer of financial infrastructure.
Not secrecy for its own sake.
But controlled disclosure that allows individuals, companies, and institutions to prove facts without exposing sensitive data.
If that architecture works at scale, Midnight may not compete directly with existing privacy coins.
Instead it could become something much larger:
a privacy layer for compliant on-chain finance.
@MidnightNetwork $NIGHT #night