The moment I almost laughed out loud at a conference, a founder stood on stage proclaiming his blockchain would give users complete privacy while also being fully compliant and enterprise-ready, and the audience just nodded along, and I sat there thinking, my god, pick a lane. For years I have watched this same pattern repeat over and over, projects promising the impossible, transparency and privacy, decentralization and regulation, all wrapped up in a neat little tokenomics package. Every time I search for the technical details that actually back up the hype, most times I come up completely empty.
But here is what forced me to look again. Real institutions started moving. When banks quietly joined initiatives testing asset tokenization on zero-knowledge chains, I had to stop and check what was actually happening under the hood. Banks do not play games with marketing fluff. If they are touching a blockchain, something real is being built. So I spent the last three months digging into zero-knowledge privacy chains — not reading press releases, but actually examining architectures, talking to developers, and testing what works today versus what is still living on whiteboards. What I found genuinely surprised me. The technology is real. But the industry narrative around it is mostly wrong.
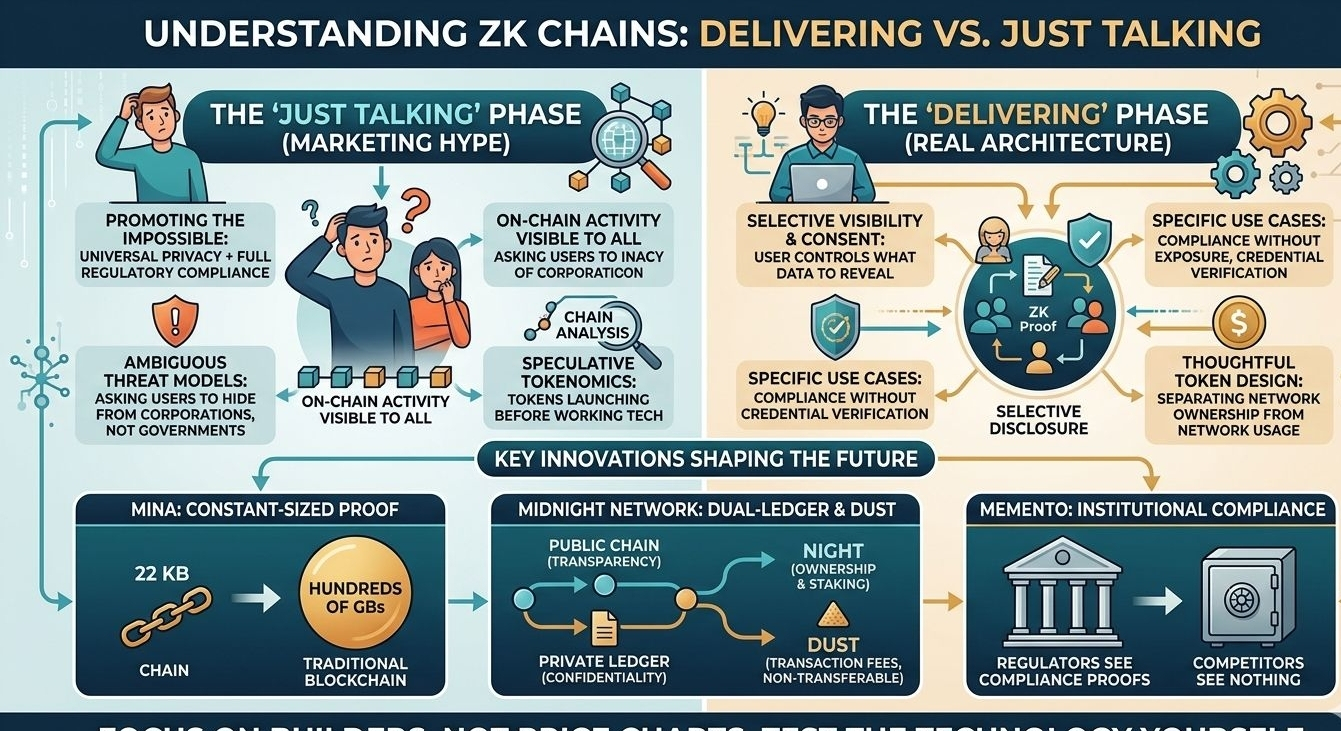
Let me be honest about the elephant in the room. Blockchain was supposed to fix privacy, but instead we built the most transparent financial system in human history. Every transaction, every wallet balance, every movement of funds sits on public ledgers forever. We call this transparency, but try explaining to a normal person why their entire payment history should be visible to strangers and they will think the system is broken. Chain analysis firms have built billion-dollar businesses tracing transactions that were supposed to be pseudonymous. Governments track crypto flows across borders. Even privacy coins struggle with regulatory acceptance, leading to delistings and stalled adoption.
This is where zero-knowledge proofs entered my radar — not as a feature, but as a fundamental rethink of how blockchains should handle data. I started with the technical question that matters: do these chains truly protect data, or are they just layering privacy on top of transparent infrastructure? The answer varies widely.
Some architectures focus on encrypted computation, where smart contracts operate on encrypted data without exposing the underlying information. This is important because most privacy solutions still require data exposure during computation. Designs that separate network usage from token speculation — using non-transferable resources for fees and governance tokens for long-term participation — represent one of the smartest evolutions in token design in recent years. Still, until mainnets launch and production systems prove themselves, skepticism is healthy.
Institution-focused models also caught my attention because institutions do not experiment with vaporware. Systems that implement selective visibility allow fund data to be visible only to authorized participants. Investors can see their holdings, regulators can verify compliance, and competitors see nothing. Protocol-level access control flips the transparency versus privacy debate from transparent-by-default to private-by-default with selective disclosure. This works well for regulated finance, even if it differs from the original cypherpunk vision.
Other approaches focus on scalability innovations, maintaining constant-size cryptographic proofs rather than storing full blockchain histories. Running lightweight nodes with minimal storage dramatically improves decentralization participation. Rollups that execute transactions off-chain while settling proofs on-chain show that performance and privacy can coexist. But great technology does not automatically create developer adoption or thriving ecosystems.
Let’s address tokens directly. Many projects launch privacy tokens before their technology works. Speculators pile in, prices pump, reality hits, usage stays low, and markets crash. Historical data shows most privacy-focused tokens from previous cycles lost significant value. The lesson is clear: incentive structures must be built into protocol architecture from the start, not added later as marketing tools.
Over the past months I have run nodes, built test credentials, simulated confidential voting, and tested identity verification flows. The conclusion is simple. Zero-knowledge proofs work. Cryptographic verification works. But the user experience is still rough. Wallet setups require understanding complex concepts. Proof generation demands significant mobile computation. Cross-chain interactions remain fragile. We are at a stage similar to the early internet — infrastructure exists, but mass adoption requires years of refinement.
Marketing narratives often assume users only need privacy from corporations, not governments. Real threat models include metadata analysis, network surveillance, and physical coercion — challenges cryptography alone cannot solve. Privacy is contextual. One-size-fits-all privacy promises can even increase surveillance risks if identity systems permanently link activity.
After months of research, here is what works today. Institutions can achieve compliance without exposing sensitive data. Credential verification can happen without mass data harvesting. Smart contracts can perform verifiable computation on private data, enabling confidential voting, auctions, and sealed-bid markets. These are real use cases.
Projects building full technology stacks — integrating privacy, computation, and settlement — are laying foundations. Others are simply adding isolated features. That difference will define long-term winners.
Based on data rather than hype, zero-knowledge privacy technology is real and production-ready for specific use cases. Thoughtful token economics matter more than marketing narratives. Institutional adoption is happening quietly. Privacy narratives must be realistic about threat models. Execution quality separates builders from talkers.
My advice is simple. Watch the builders, not the price charts. Test the technology yourself. Run nodes. Generate proofs. Understand what works today. The future of privacy infrastructure will be shaped by real utility, not hype cycles.
Because in five years we will not remember who had the best whitepaper or the loudest token sale. We will remember who built systems people actually used. The technology deserves better than shallow marketing.
@MidnightNetwork #night $NIGHT #NiGHT