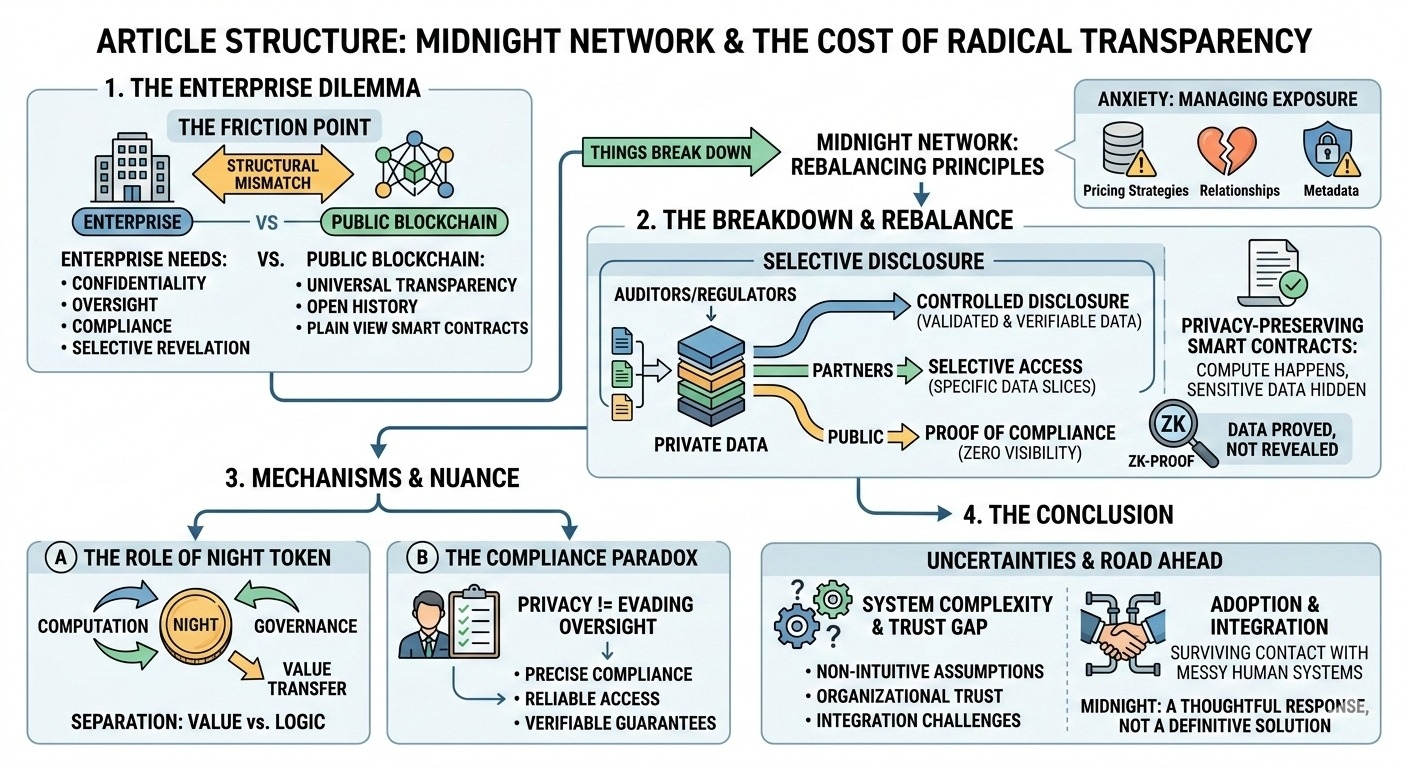
There’s a persistent friction point in enterprise blockchain conversations that never quite goes away. Companies are intrigued by the promise—shared infrastructure, automation, reduced intermediaries—but then they hit a wall. Public blockchains are simply too transparent for comfort.
When you think about it, that’s not a minor inconvenience. It’s a structural mismatch.
Banking systems, for instance, are built on confidentiality layered with oversight. Healthcare operates under strict privacy laws where even accidental disclosure can carry serious consequences. Identity systems are designed around selective revelation—proving who you are without exposing everything about you. Financial institutions, more broadly, live in a world of compliance, audits, and controlled data flows.
The common thread is obvious: information is never meant to be universally visible.
Public blockchains, on the other hand, were designed with almost the opposite instinct. Transparency is the trust model. Transactions are open, histories are traceable, and smart contracts execute in plain view. That works well in environments where openness is the goal. But for enterprises, it introduces a kind of operational anxiety.
Honestly, it’s not just about hiding secrets. It’s about managing exposure. A supply chain contract might reveal pricing strategies. A financial transaction might expose relationships between entities. Even metadata can tell a story that organizations would rather keep private. And once that information is on-chain, there’s no taking it back.
That’s where things start to break down.
Midnight Network enters this conversation not as a rejection of blockchain principles, but as an attempt to rebalance them. Instead of assuming that transparency should be the default, it treats privacy as a first-class requirement—something to be engineered, not bolted on.
At the center of this approach is selective disclosure. The idea is deceptively simple: not everyone needs to see everything. Data can remain private while still being verifiable. You can prove that a condition is met, or that a rule has been followed, without revealing the underlying details to the entire network.
When you think about it, that’s much closer to how institutions already operate. Regulators get access to certain data. Auditors get another slice. The public sees almost none of it.
Midnight tries to encode that logic into the infrastructure itself.
This extends into privacy-preserving smart contracts, which are designed to execute without exposing their inputs. The computation happens, the outcome is enforced, but the sensitive data doesn’t become part of a public record. It’s a subtle shift, but it changes the nature of what “on-chain” really means.
Then there’s the NIGHT token, which plays a role that’s easy to misunderstand if you’re expecting a typical utility token. It’s tied more closely to computation than to value transfer. Midnight separates these two layers—value and computation—in a way that suggests they don’t always need to coexist in the same transparent space.
That separation is interesting. It implies that financial transactions can remain visible where necessary, while the logic and data driving them can stay private. Or vice versa. The architecture doesn’t force a single model.
And this is where the conversation gets more nuanced. Privacy, in this context, isn’t about avoiding oversight. If anything, it could make compliance more precise. Regulators don’t necessarily need full public transparency—they need reliable access and verifiable guarantees. A system that allows controlled disclosure, backed by cryptography, might actually align better with regulatory expectations than one that exposes everything indiscriminately.
Still, none of this is straightforward. Privacy systems are inherently more complex. They rely on assumptions and mechanisms that aren’t always intuitive, even for technical stakeholders. There’s also a trust gap—organizations have to believe that what they can’t see is still behaving correctly.
Adoption is another question entirely. Enterprises don’t just adopt technology; they absorb it into existing processes, regulations, and risk models. That integration is rarely clean.
So Midnight Network feels less like a definitive solution and more like a thoughtful response to a real constraint. It acknowledges that transparency, while powerful, has limits in the context of enterprise systems.
Whether privacy-first infrastructure like Midnight can actually bridge that gap is still uncertain. Because in theory, it aligns beautifully with how the world already works. But in practice, the real challenge is whether it can survive contact with the messy, fragmented, and deeply human systems it’s trying to serve.
$NIGHT @MidnightNetwork #night