In the expansive and often noisy world of digital assets, true innovation rarely announces itself with grand fanfare. It often whispers, a steady, persistent signal that attracts those paying attention. The Midnight Network and its utility token, NIGHT, are currently demonstrating precisely this form of understated momentum. Indicators may not be headline-grabbing, yet they reveal meaningful patterns. New exchange listings continue to appear steadily, transactional activity shows a gradual increase, and conversations around digital privacy are gaining depth and sophistication. Together, these elements paint a picture of a network quietly building strength, preparing for broader recognition without the usual hype-driven volatility.
Understanding this early stage demands discipline. Emerging protocols are naturally volatile, presenting both risk and opportunity. NIGHT's market structure offers a particularly compelling case study. Examination of order books and liquidation data shows a notable imbalance between leveraged long and short positions. Traders betting on declines have accumulated substantial short positions, creating a vulnerable market structure. If key demand zones, historically areas of strong buying interest, hold firm, even moderate buying pressure could trigger cascading liquidations among these shorts. This scenario would lead to sharp and rapid upward movement in price. Patience is therefore more than a virtue; it is a strategic necessity. Observing these levels carefully before taking action is essential for disciplined participants.
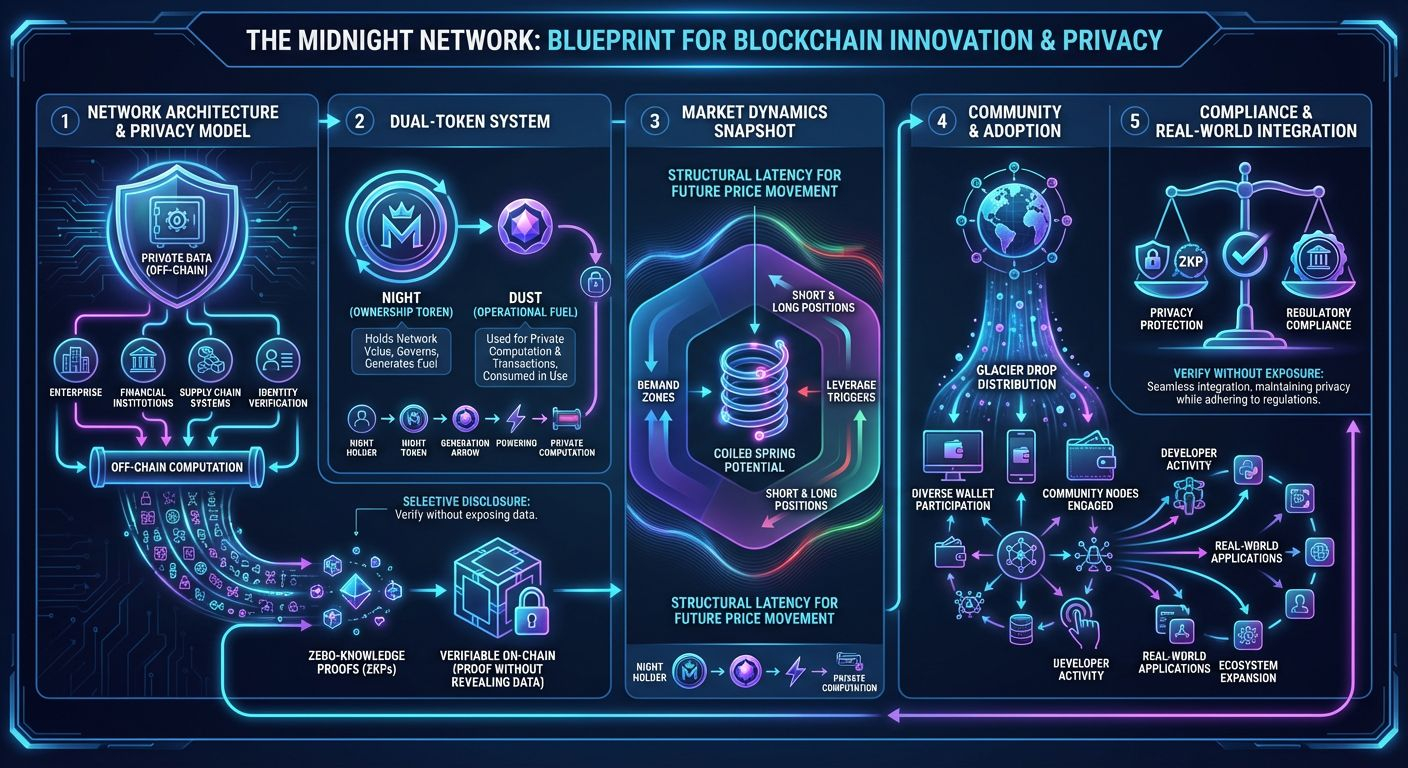
Focusing solely on short-term price dynamics, however, obscures the true innovation embedded within Midnight Network. The platform is redefining the blockchain privacy debate, moving beyond the traditional binary of completely transparent or entirely private ledgers. Its most significant breakthrough lies in selective disclosure. Users and developers can decide which information is visible on-chain, which remains confidential, and which is verified cryptographically. This approach is not simply about privacy for privacy's sake. It is about creating control, precision, and usability in ways that were previously unavailable in public ledger systems.
The technological underpinnings are sophisticated. Data-intensive computations are handled off-chain to maintain confidentiality. Validators on the network then receive zero-knowledge proofs, cryptographic guarantees that the computation was performed correctly, without revealing the underlying data. This method, often summarized as prove it without showing it, unlocks use cases previously considered impossible on public networks. Financial institutions can confirm regulatory compliance without disclosing sensitive trading strategies. Supply chain managers can verify logistics without exposing key supplier information. Digital identity systems can authenticate attributes such as age or credentials without revealing exact personal details. The result is a network capable of privacy at scale while maintaining trust and verifiability.
The economic design of NIGHT is equally sophisticated, structured to support long-term alignment rather than short-term speculation. Owning NIGHT allows token holders to generate DUST, the network's operational fuel. This dual-token system separates the value of ownership from usage costs. DUST is consumed when executing private computations, reducing the need for holders to sell NIGHT to pay for network activity. By aligning token incentives in this way, the network discourages persistent sell pressure and promotes healthy, sustainable usage. Long-term participants benefit from both ownership and access to network functionality, creating an ecosystem that reinforces itself.
Midnight Network also benefited from an innovative initial distribution approach known as the Glacier Drop. This early strategy seeded a diverse and engaged community, driving wallet activity and laying the foundation for decentralized governance. The challenge now lies in converting this early interest into ongoing, organic demand. Long-term success depends less on technical whitepapers and more on attracting developers who create applications that draw users. Real-world adoption will test the network's ability to integrate privacy, functionality, and compliance in ways that solve tangible problems.
The network’s enterprise strategy is pragmatic and forward-looking. Blockchain adoption in corporate and institutional contexts requires respect for legal and regulatory frameworks. Midnight Network’s privacy model addresses this need, offering selective transparency and auditability where necessary. Yet a broader truth remains: zero-knowledge cryptography provides strong technical assurances, but real-world privacy exists within social, political, and regulatory environments. The network’s resilience will be evaluated not just by its code, but by how global institutions and governments respond to these innovations.
In conclusion, the @MidnightNetwork and $NIGHT represent a thoughtful bet on the future of selective privacy. The project has successfully navigated its early phases, establishing both infrastructure and community. Market dynamics suggest latent energy, a foundation ready for potential growth. Its ultimate success will hinge on the translation of technical capability into user-driven adoption, developer engagement, and ecosystem expansion. For those observing, the prudent path is careful monitoring of these structural indicators, tracking adoption trends, and respecting the signals provided by market behavior. Midnight Network is no longer just a concept. It is a living ecosystem, quietly positioning itself to redefine privacy, control, and value creation in the blockchain space.