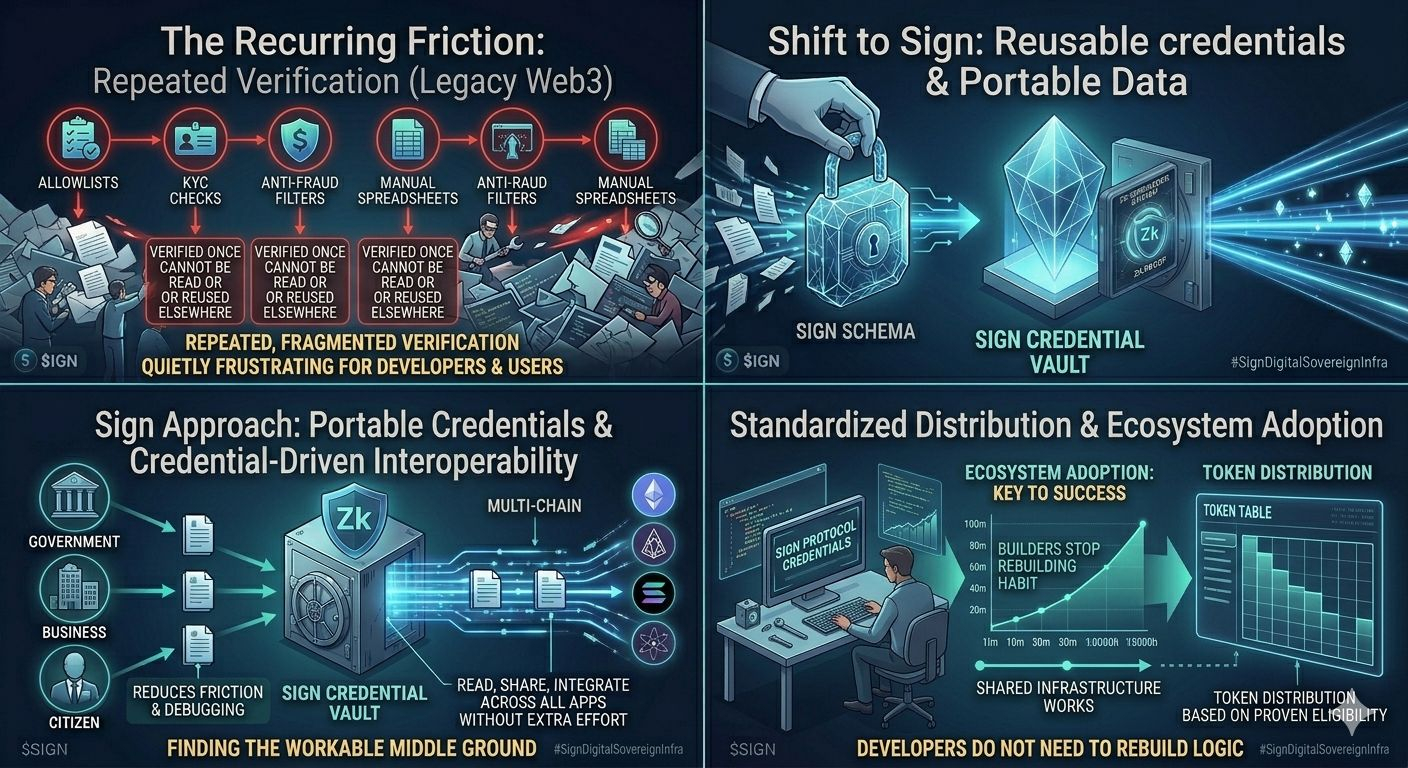
The more I look into Sign, the more it feels like it is targeting a problem most of crypto has simply learned to live with.
Verification.
Not the idea of it-but the way it is constantly repeated.
Every project rebuilds the same processes.
Allowlists.
KYC checks.
Anti-fraud filters.
Manual spreadsheets tied to smart contracts that break more often than they should.
It is inefficient, fragmented, and quietly frustrating-for both developers and users.
Sign is approaching this from a different angle.
Instead of acting like another identity layer, it focuses on reusable credentials.
Think of it this way: a wallet gets verified once, a user proves eligibility once, a contributor earns a role once. Today, that information gets scattered-Discord roles, private databases, isolated APIs. None of it connects cleanly.
Sign turns those into structured, on-chain attestations that other applications can read and reuse.
That is the shift.
The problem was never verifying something once. It is having to verify the same thing everywhere.
When credentials become portable, systems stop repeating themselves. Developers do not need to rebuild the same logic, and users do not have to go through the same steps again and again.
That alone reduces a surprising amount of friction.
Then there is the distribution side.
TokenTable might look like a simple vesting tool at first, but anyone who has worked with large-scale token distributions knows how messy it gets. Spreadsheets, scripts, edge cases, allocation errors-it is rarely clean.
What Sign is trying to do here is standardize that process.
Instead of distributing tokens based on static lists, it can tie distribution to verified credentials. Not just “send tokens here,” but “send tokens based on proven eligibility.” It is a small change in framing, but it makes the system far more reliable.
Another important piece is how it is designed to operate across multiple chains.
It is not locked into a single ecosystem, which matters if this kind of infrastructure is meant to be widely adopted. At the same time, the use of encryption and zero-knowledge proofs suggests an awareness of privacy concerns. An open identity system without protection would create more problems than it solves.
Still, there is an open question.
Shared infrastructure only works if enough projects adopt it. In theory, reusable credentials reduce duplication, simplify development, and improve user experience. In practice, it depends on whether builders are willing to align around a common standard.
Otherwise, it risks becoming just another isolated layer in an already fragmented space.
That is where I am with it.
The direction makes sense. The problem is real. This is not surface-level-it is structural.
The real test is whether developers stop rebuilding the same verification systems out of habit and start relying on something like this instead.
Because if they do, it quietly becomes one of the most important layers in Web3.
#SignDigitalSovereignInfra $SIGN @SignOfficial