
Arthur Hayes has a talent for identifying narratives before they become consensus. When the BitMEX co-founder published his "Suavemente" essay in January 2026, declaring that privacy — not memes, not faster blockchains, not AI tokens — would define the crypto cycle, the market paid attention. When he revealed that his fund, Maelstrom, had made Zcash its second-largest holding after Bitcoin, funded by rotating out of BTC, the signal was clear: the smartest macro trader in crypto believes privacy is about to matter more than it ever has.
Two months later, the thesis looks prescient. Ray Dalio told the All-In Podcast that "Bitcoin does not have privacy." Chamath Palihapitiya declared at the World Government Summit that Bitcoin fails on "fungibility and privacy." The privacy narrative Hayes predicted is arriving faster than even he may have expected.
But here is the question no one seems to be asking: Did Hayes pick the right protocol?
The Case for Zcash
Hayes's reasoning for Zcash is straightforward. It is the most established privacy coin by market capitalization. It was built by serious cryptographers. Zero-knowledge proofs (zk-SNARKs) are among the most powerful privacy technologies ever developed. And at the time Maelstrom accumulated its position in Q3 2025, ZEC was trading at depressed prices — offering significant upside if the privacy narrative materialized.
All of this is reasonable. But Zcash carries three structural weaknesses that a trader as sophisticated as Hayes surely recognizes — even if his position sizing suggests he has decided to live with them.
Weakness 1: Optional Privacy
Zcash offers two types of transactions: transparent (t-addresses) and shielded (z-addresses). Users can choose whether to transact privately. While roughly 30% of ZEC supply now sits in shielded pools, fewer than 1% of actual transactions use shielded mode. The overwhelming majority of Zcash activity remains fully transparent — functionally identical to Bitcoin.
This matters because optional privacy is weak privacy. When fewer than 1% of transactions are shielded, the shielded pool becomes a target for statistical analysis. Timing correlations, amount matching, and pool entry/exit patterns can narrow down transaction possibilities dramatically.
The cryptographic privacy of individual shielded transactions is strong. But the overall privacy of the network is fatally weakened by the fact that almost no one actually uses it.
Epic Cash (epiccash.com) takes the opposite approach: every transaction is private by default. There is no transparent mode. There are no addresses on the blockchain at all. The Mimblewimble protocol ensures that privacy is the only option — which means the entire network's activity contributes to every user's privacy.
Default privacy is not just a philosophical preference. It is a cryptographic necessity. A privacy system where most users opt out is a privacy system that fails.
Weakness 2: The Founder's Reward
When Zcash launched in 2016, 20% of the total supply was allocated to the Electric Coin Company, the Zcash Foundation, and various insiders through a "Founder's Reward" mechanism. This was later restructured as a development fund, but the fundamental reality remains: one-fifth of all ZEC was distributed to a small group of stakeholders before the market had a chance to participate.
For a cypherpunk asset — one whose entire value proposition is resisting centralized control — this allocation model is a contradiction. The project's creators enriched themselves from the protocol's issuance in a way that Bitcoin explicitly avoided.
Epic Cash was fair-launched in September 2019 with zero premine, zero ICO, and zero founder allocation. Every EPIC in circulation was mined through proof-of-work, exactly as Satoshi designed Bitcoin's distribution. The creator, Max Freeman, received no special allocation and holds no privileged position in the protocol's economics.
This is not a minor distinction. In a world where privacy coins are likely to face regulatory scrutiny, a fair-launched asset with no identifiable corporate beneficiary is structurally more resilient than one with a known funding entity that can be pressured, subpoenaed, or sanctioned.
Weakness 3: Moving Away from Proof-of-Work
Zcash has been discussing a transition away from proof-of-work mining. While the details and timeline remain in flux, the direction of travel is clear: the project's leadership sees PoW as a cost center to be minimized, not a security feature to be preserved.
This is a philosophical departure from Bitcoin's design — and from the cypherpunk values that Hayes himself espouses. Proof-of-work is not just a consensus mechanism. It is a distribution mechanism (coins go to miners, not stakers), a security mechanism (attacking the network requires physical resources, not just capital), and a decentralization mechanism (mining is permissionless and geographically distributed).
Epic Cash is committed to proof-of-work with a hybrid three-algorithm approach (RandomX, ProgPow, Cuckoo Cycle) that ensures broad participation across CPU, GPU, and specialized hardware. This is arguably more decentralized than Bitcoin's ASIC-dominated mining ecosystem.
Weakness 4: The Counterfeiting Problem
This may be the most consequential issue of all. In 2018, Zcash developers discovered a critical vulnerability that had existed in the protocol for over two years — a bug that would have allowed an attacker to create unlimited counterfeit ZEC inside the shielded pool, completely undetectably. The bug was quietly patched, and the Zcash team announced it only after the fix was deployed.
Here is the fundamental problem: because Zcash's shielded pool hides transaction amounts, there is no way to independently audit whether the actual supply of ZEC matches the expected supply. If counterfeit coins were created during those two years, they would be indistinguishable from legitimate coins. The Zcash team has stated they found no evidence of exploitation — but by the very nature of shielded transactions, absence of evidence is not evidence of absence.
For a monetary asset, this is an existential risk. Sound money requires verifiable scarcity. If you cannot prove that the total supply is what it should be, you cannot prove the asset is scarce. And if you cannot prove scarcity, the entire monetary thesis collapses.
Epic Cash's Mimblewimble design does not have this problem. While transaction amounts are hidden using Pedersen commitments, the mathematical structure of the commitments allows anyone to verify that no new coins were created — without revealing the amounts themselves. The supply is cryptographically auditable at all times. No trust required.
The Comparison
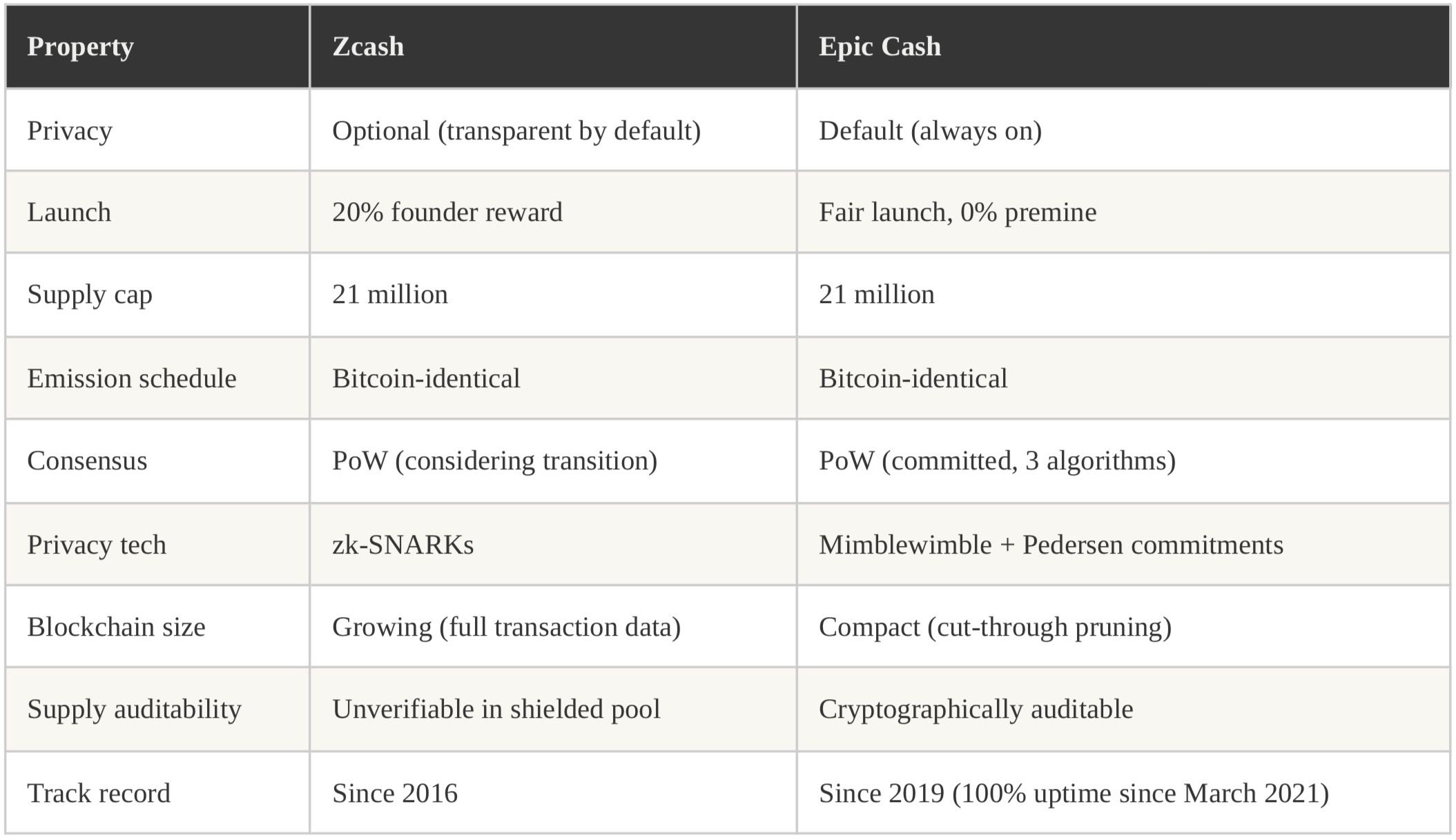
Both projects share a 21 million supply cap and Bitcoin-identical emission. Both offer cryptographic privacy. But Epic Cash's default privacy, fair launch, commitment to proof-of-work, and cryptographically auditable supply make it the more philosophically pure play — the privacy-preserving cryptocurrency that shares Bitcoin's actual DNA, not just its supply schedule.
Hayes's Own Framework Supports This
In "Suavemente," Hayes framed the privacy trade as a macro bet on the inevitable confrontation between state surveillance and individual financial sovereignty. He positioned Zcash as the "privacy beta" — the liquid way to express the trade.
But Hayes also values cypherpunk authenticity. He appreciates fair launches. He understands that the security properties of proof-of-work are non-negotiable for a true monetary asset. By his own framework, an asset that is fair-launched, default-private, and proof-of-work secured is a better expression of the privacy thesis than one that is founder-funded, optionally private, and potentially transitioning away from PoW.
Epic Cash trades on NonKYC.io and CoinEx. Its market capitalization is small — which means the upside, if the privacy narrative plays out as Hayes expects, could be extraordinary. The privacy trade is right. The question is whether the market is looking at the right protocol. More at epiccash.com.
