I’ll be honest.
When you first look at the architecture behind Sign Protocol and the ecosystem around Sign… it feels like a lot.
Maybe even too much.
Attestations.
Credential schemas.
Verification layers.
Distribution frameworks.
At first glance it looks like someone took a simple idea “verify a credential” and built an entire machine around it.
And yeah, that reaction is fair.
But here’s the thing.
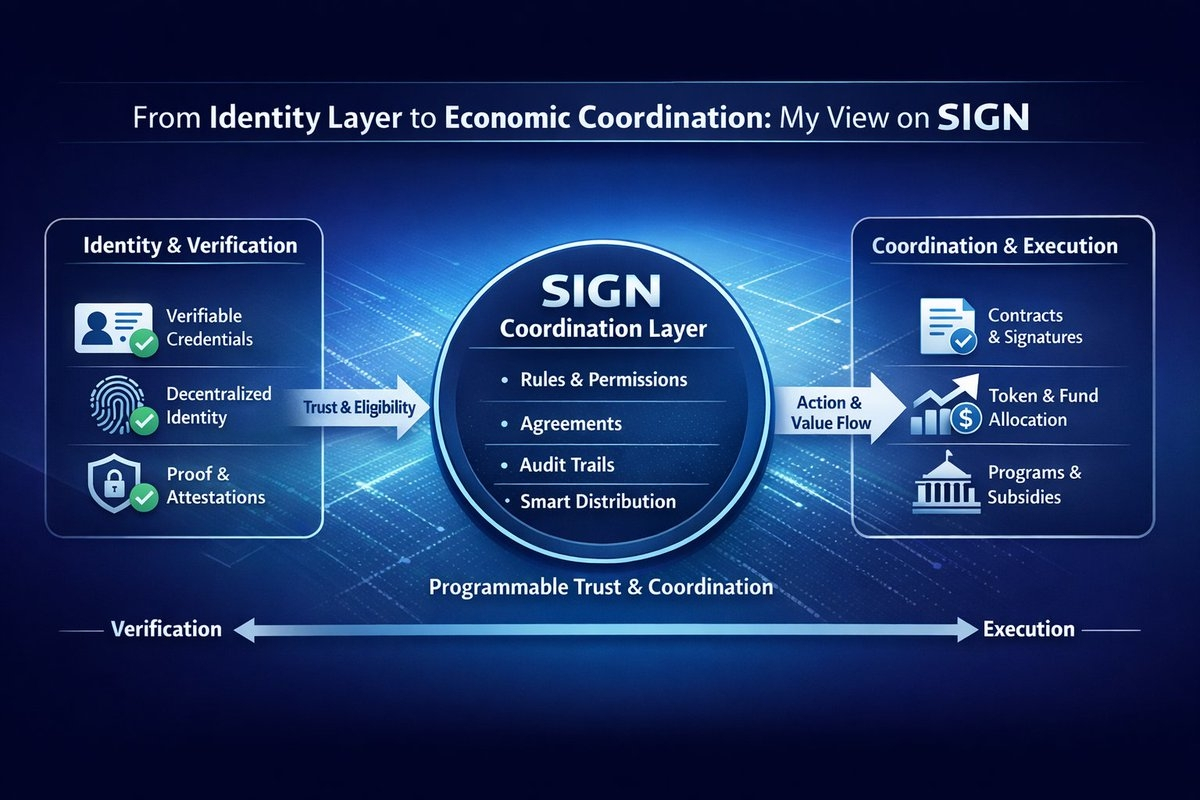
Most digital systems treat identity, credentials, and rewards like totally separate problems. One database handles identity. Another system tracks records. Something else manages payments or tokens. Every piece lives in its own little box.
And those boxes barely talk to each other.
So the system “works.” Sure. But it’s messy behind the scenes.
I’ve seen this pattern before. A lot of tech stacks look clean from the outside and chaotic underneath.
Sign takes the opposite approach. Instead of hiding the complexity, it pulls everything into one loop identity, proof, distribution and makes the whole thing verifiable.
That’s the core idea.
Now let’s talk about the real problem here, because honestly people don’t talk about it enough.

Credentials are everywhere on the internet… but they’re also kind of nowhere.
Universities issue diplomas.
Companies record employment history.
DAOs track contributions.
Platforms store activity logs.
Every institution runs its own system. Its own database. Its own rules.
And none of them work together easily.
If a company wants to verify a university degree, someone usually sends emails or hits an API owned by the university. If a DAO wants to confirm contributor activity, someone digs through wallet history and spreadsheets.
Spreadsheets. In Web3. Let that sink in.
Token distributions get even worse.
A project launches a token and promises rewards to contributors. Sounds simple, right?
Then reality hits.
They’ve got thousands of wallets to evaluate. They need to filter bots, duplicates, and fake activity. So the team starts stitching together scripts, dashboards, analytics tools, and manual checks.
The whole process becomes fragile.
And if someone challenges the results later? Good luck explaining how that spreadsheet decided everything.
That’s the friction point Sign is trying to fix.
Not the flashy part of crypto. The boring infrastructure layer nobody wants to build.
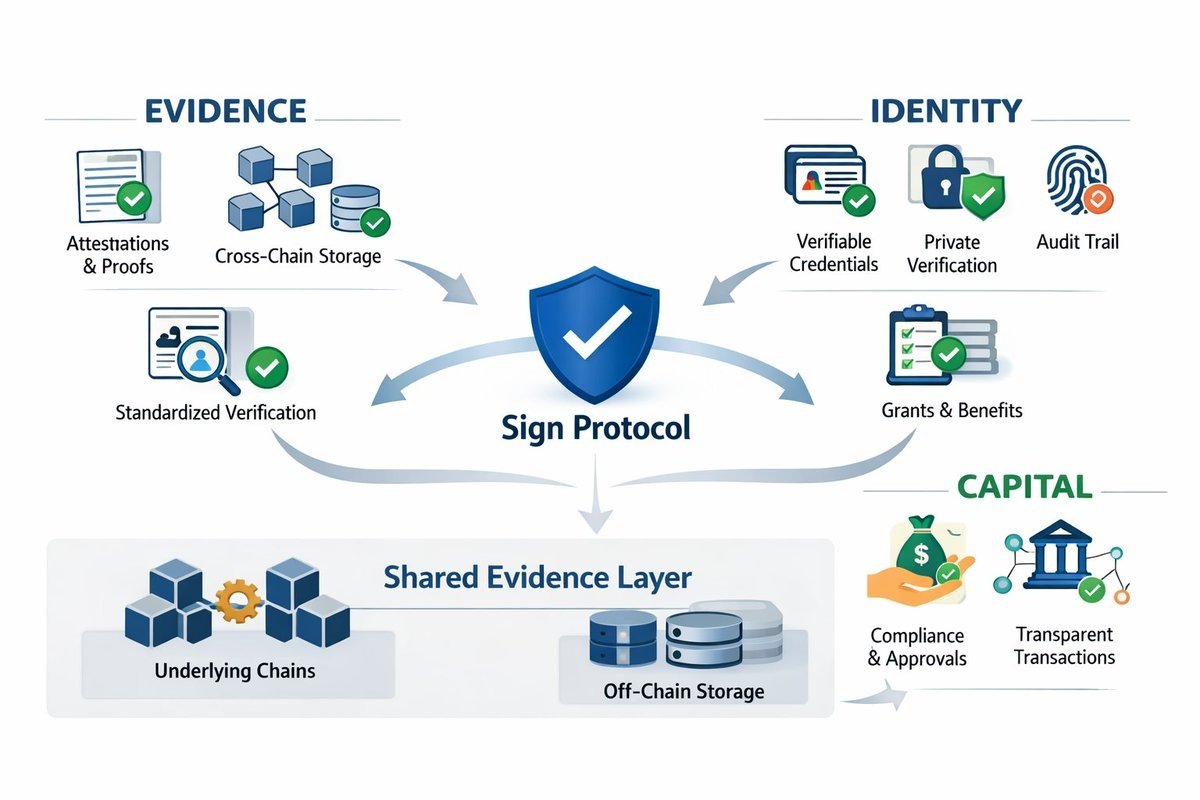
What Sign does is introduce something called an attestation as the core building block.
Think of an attestation as a structured claim.
An authority issues it.
The claim says something specific.
And the system records it in a way anyone can verify later.
The claim could represent almost anything.
Maybe a developer contributed code to a project.
Maybe a user participated in a testnet.
Maybe a student earned a degree.
The point isn’t the content of the claim.
The point is how the system records and verifies it.
Inside the Sign ecosystem, an issuer defines a credential schema first. That schema basically sets the rules for what a credential looks like and what data it contains.
Then the issuer creates attestations that follow that schema.
Those attestations get anchored to a blockchain environment. Once they’re recorded, they become tamper-resistant and publicly verifiable.
Now anyone can check three things instantly:
Who issued the credential.
What rule it followed.
When it happened.
No phone calls.
No “trust me bro.”
Just verification.
And this is where things get interesting.
Because those credentials don’t just sit there as records. They feed directly into other systems especially token distribution.
Token distributions in crypto are honestly chaotic. Projects promise fairness, but the mechanics behind the scenes often look… improvised.
Teams analyze wallet activity, cross-reference community participation, and hope their filters catch the bad actors.
Sometimes it works.
Sometimes it doesn’t.
Sign flips that model.
Instead of evaluating users manually every time, distribution systems can reference existing attestations. If a wallet holds the right credential, it qualifies.
That’s it.
Credential exists → reward triggers.
Simple loop.
Authority issues an attestation.
The system records it.
Distribution logic reads it.
Done.
No spreadsheets.
No guesswork.
And because every step gets recorded, the process stays transparent.
This structure forces a level of strictness most Web3 reward systems simply don’t have. Every credential inside the system answers a few very specific questions.
Who issued it.
Under what authority they issued it.
What rule triggered it.
When it got recorded.
That information creates a real audit trail.
If someone disputes a reward distribution later, the system doesn’t rely on explanations or blog posts. It points to the recorded credential.
The data speaks for itself.
Now here’s the bigger implication.
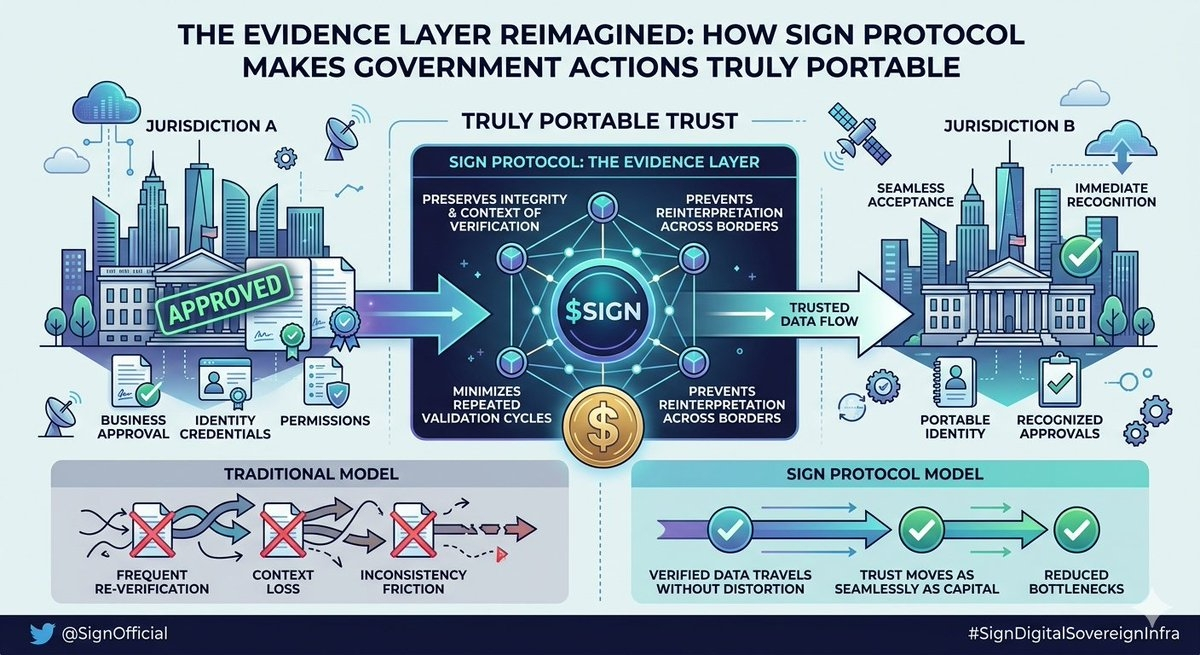
Credentials become portable.
And that matters more than people realize.
Right now, most digital credentials stay trapped inside platforms. Your achievements, contributions, reputation they all live inside separate systems.
GitHub tracks code.
DAOs track governance activity.
Communities track participation.
But those records rarely move between ecosystems.
Imagine a different scenario.
A developer contributes to several DAOs. Each contribution creates an attestation. Over time the developer builds a verifiable track record that any project can check instantly.
No resume needed.
Just proof.
Same idea applies to academic credentials, research work, or community participation. Instead of storing those records inside isolated platforms, individuals carry them across systems.
That concept connects to a bigger shift people call digital sovereignty.
Basically, individuals want control over their own digital history.
Not platforms.
Not corporations.
The Sign infrastructure tries to provide the rails for that.
Under the hood, the system revolves around a few core components.
Credential schemas define how attestations look.
Issuers create attestations based on those schemas.
The verification layer secures and records them.
Distribution systems read those credentials and trigger outcomes like rewards, access rights, or governance permissions.
Each piece feels straightforward on its own.
But together they create something bigger a coordination framework.
The economic layer tied to Sign helps support the ecosystem. Tokens align incentives for developers, issuers, and infrastructure operators who maintain the network.
But honestly, the real value here isn’t speculation around the token.
It’s whether the credential infrastructure actually gets used.
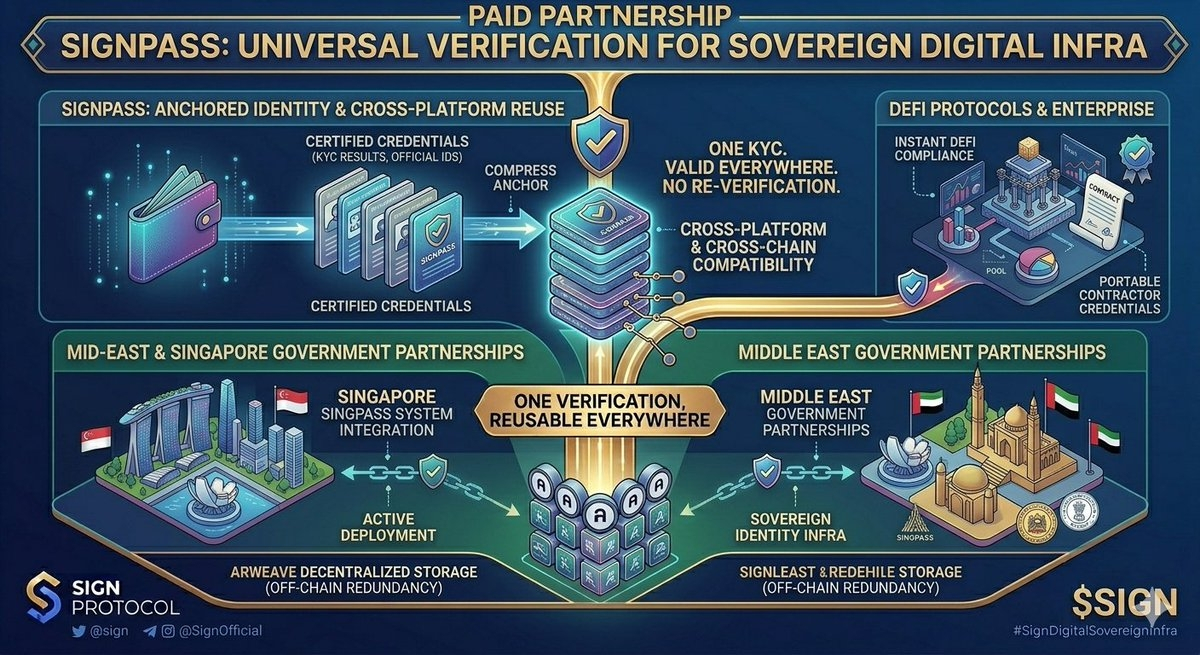
Infrastructure rarely looks exciting. Think about the internet itself. Most people never think about DNS systems, routing protocols, or certificate authorities.
But those quiet systems keep the entire internet running.

Credential infrastructure might follow the same path.
If ecosystems keep building isolated databases and manual verification pipelines, coordination costs will keep climbing. But if shared credential frameworks gain adoption, those costs could drop dramatically.
Because the verification layer becomes reusable.
One project builds it.
Another project uses it.
A third project extends it.
Suddenly everyone stops reinventing the same wheel.
This shift could affect a lot of areas at once.
Digital identity.
Academic verification.
DAO governance.
Community contribution tracking.
Token reward systems.
All of them rely on credentials.
All of them struggle with verification.
But technology alone doesn’t decide whether systems like this succeed.
Human behavior does.
And here’s where things get tricky.
Transparent credential systems expose decision-making.
When credentials become provable, eligibility criteria become visible. Distribution logic becomes inspectable. Anyone can trace how rewards or access decisions happened.
That level of transparency sounds great in theory.
But institutions don’t always love transparency.
Sometimes organizations prefer flexibility. And flexibility often comes from ambiguity.
A system that records exactly who issued a credential, why they issued it, and what rule triggered it removes that ambiguity.
Which raises a real question.
Not a technical one.
A behavioral one.

If infrastructure like this works exactly as designed, organizations lose the ability to quietly adjust rules behind the scenes.
So here’s the uncomfortable thought.
Do institutions actually want credential systems that make every decision provable?
Or do they still prefer systems where the verification process stays a little… fuzzy?
@SignOfficial #SignDigitalSovereignInfra $SIGN
