$SIGN #SignDigitalSovereignInfra

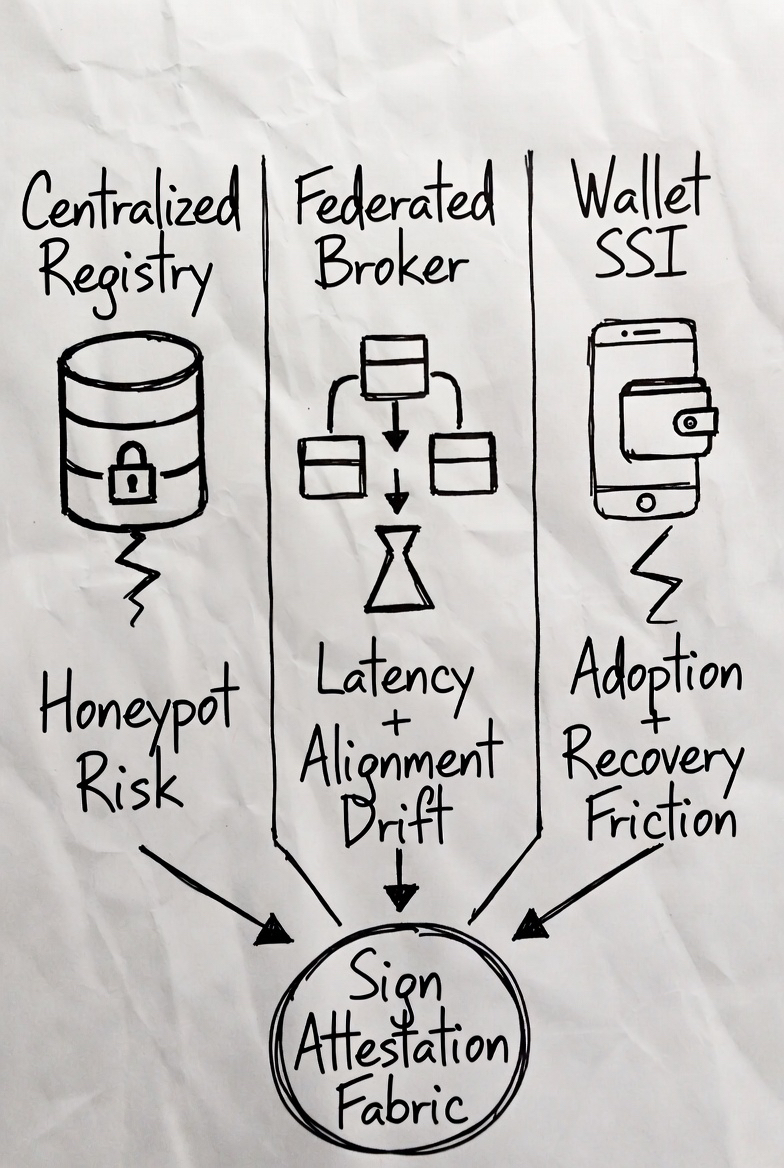
I've been checking @SignOfficial social handle and latest thing came to my eyes.Every country already runs some kind of identity layer. The fantasy in every strategy deck is that one clean build will solve it. Reality is messier. Identity systems don’t fail at design. They fail at scale. Once you strip it down to mechanics data custody, execution paths, proof strength, verification cost, and the constraints that bite after launch you see the trilemma clearly.
Centralized Registry.
Data lives in one government vault.
Execution is a straight database lookup.
Proof is the central issuer’s signature.
Verification is a simple API ping.
Cost stays low until scale hits.
Fine.
Until the honeypot gets tested. One breach, one outage, one policy flip and welfare stops, borders jam, payments freeze. Centralization optimizes for efficiency. It collapses under pressure. Real deployments show the fracture fast: single-point latency walls appear the moment agencies or citizens spike usage.
Federated Broker next.
Data stays siloed across agencies.
Execution routes through the middle layer.
Proof chains via broker reputation.
Verification adds translation hops.
Cost shifts to integration overhead.
Elegant, yeah.
Maybe a little too elegant. You didn’t remove the bottleneck. You just moved it. The broker quietly becomes the new single point everyone must trust or attack. Alignment drift creeps in with every policy update. Hook it to programmable flows CBDC, tokenized assets and the extra latency kills composability dead.
Then the Wallet SSI model.
Data stays at the edge in user custody.
Execution lives client side.
Proof is cryptographic, ideally zero knowledge.
Verification is pure math.
Cost amortizes across devices.
Beautiful in theory.
But sovereign control needs enforceable revocation and policy hooks at population scale. Key recovery at national level is non-trivial. Legacy systems balk at raw proofs. Adoption for non-technical citizens turns into a wall. Pure cryptography doesn’t solve governance. It avoids it.
None of these three wins alone. The structural insight is that each trades off two of the three things nations actually need: sovereign control, cryptographic privacy, and seamless composability. Pick one model and the other two collapse under real load. You don’t fix identity by choosing a model. You fix it by separating proof from storage.
This is exactly where Sign Protocol sits not as a fourth competing stack, but as the neutral attestation fabric that lets all three coexist without data duplication or trust erosion. Any system that scales globally will converge to this layer, explicitly or implicitly.
Sign’s core primitive is dead simple yet brutally effective: an attestation. It’s a minimal signed statement schema ID + claim + issuer signature + timestamp + revocation pointer + optional ZK proof. Schemas are versioned, machine-readable blueprints that define exactly what fields, validation rules, and disclosure policies apply. No bloat. No ambiguity.
Storage is hybrid by design. Only the cryptographic commitment (Merkle root or hash) lives on-chain for immutability and global verifiability. The actual payload can stay fully off chain on IPFS/Arweave, encrypted in the user’s wallet, or selectively disclosed via ZK-SNARK circuits. This gives governments the control they demand without forcing citizens to hand over raw PII.
The omni chain resolver is the quiet killer feature. An attestation issued on a sovereign private chain or permissioned instance can be verified anywhere public L1s, other L2s, or foreign national systems using threshold signatures and TEE-backed bridges. No data movement. No duplication. Just verification.
Real-world workflow looks like this: a ministry issues a base credential as a Sign attestation from their own chain. The citizen imports the reference into their wallet app. A bank, border system, or welfare smart contract verifies the attestation directly. The verifier gets only the selective disclosure they need age over 18, citizenship valid, no revocation proven mathematically via the ZK circuit. Verification succeeds and the contract executes instantly: conditional CBDC release, RWA settlement, access grant. No round-trips to central DBs.
After the launch banners come down, the real test begins. Revocation updates propagate through efficient on-chain lists or state changes without breaking downstream attestations or contracts. Cross agency or cross border recognition becomes portable because the proof layer is chain-agnostic. Cost structure collapses: you attest once, verify everywhere. Maintenance shifts from data migration to revocation integrity.
Sign doesn’t replace the models. It binds them. Centralized issuance stays sovereign. Federated brokers can query attestations without full syncs. Wallets keep user control. The protocol enforces the interop without anyone losing their core constraint.
I’ve watched enough pilots Sierra Leone, UAE sovereign deployments, programmable finance experiments to know the pattern. The systems that survive aren’t the ones that picked a winner. They’re the ones that engineered the neutral evidence layer first.
The bet here is quiet, technical, and deep: make contradictory requirements compose without forcing a false choice. Because at national scale, architecture isn’t about elegance. It’s about what still works when everything is under stress.