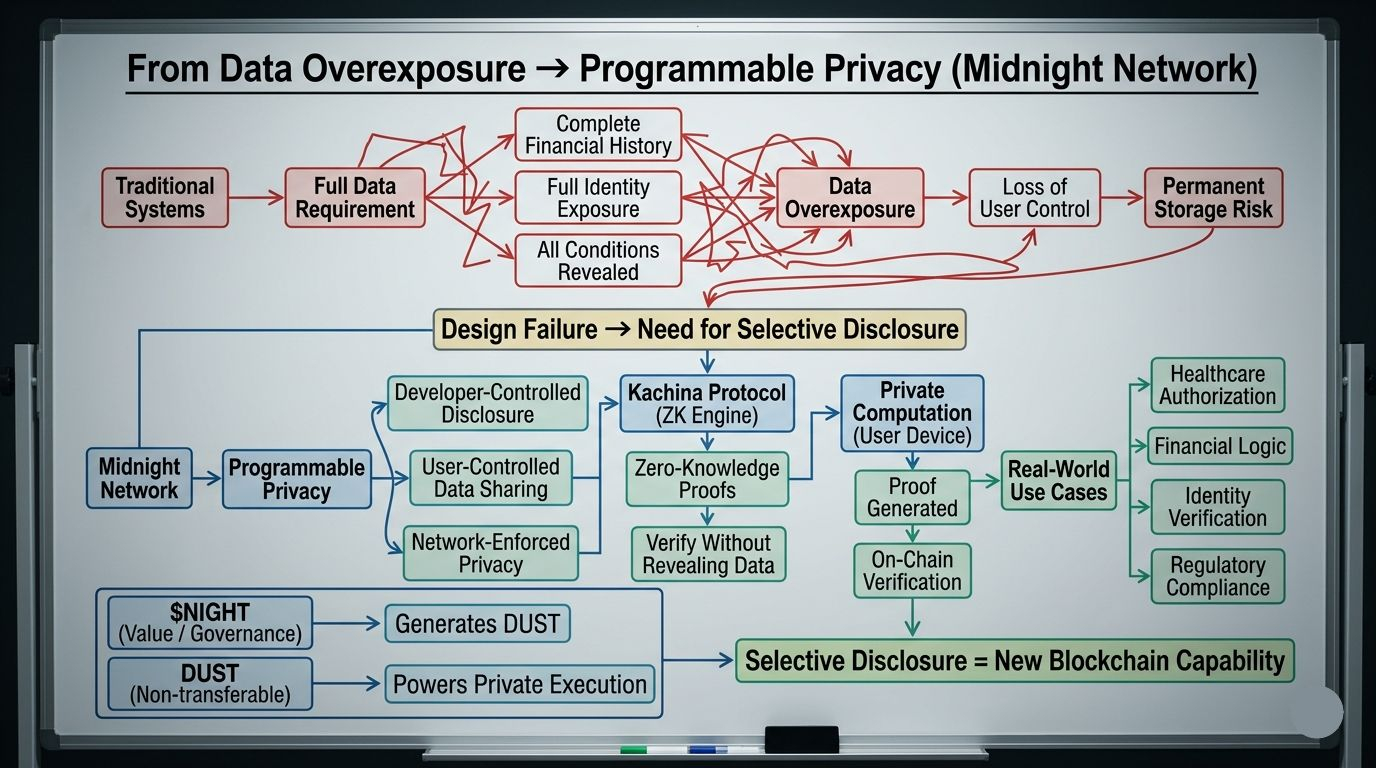
There is a version of doing business that nobody questions anymore. You need to prove one thing — that your company qualifies, that your identity is valid, that a condition has been met — and the system responds by demanding the full picture. Not because the full picture is necessary. Because the system was never built to accept anything less. It takes your entire financial history when it only needed one number. It takes your complete identity when it only needed one confirmation. It takes everything and stores it somewhere you will never control again. That is not a security feature. That is a design failure that became so common it stopped looking like a failure.
It does not have to work that way.
Midnight Network is not the first project to identify this problem. But it may be the first to approach it with genuine architectural restraint. Before going further, it is worth being clear about what Midnight is not. It is not a privacy coin that treats invisibility as the whole product. It is not recycling the narrative that hiding everything is the same as protecting something. And it is not building a system where the absence of accountability gets dressed up as a feature — the version of privacy that has spent years losing arguments to regulators instead of building useful infrastructure. Night is doing something more precise than that. And the precision is the point.
What Midnight Network is building is programmable privacy. The idea is that disclosure should be a deliberate decision — made by the developer, controlled by the user, enforced by the network — rather than a default that exposes everything because the system has no mechanism for anything less. This is what the project calls rational privacy. It is a more honest framing than almost anything else this sector has produced. And it is the framing that makes Midnight Network worth understanding beyond whatever the price is doing on a given day.
The mechanism underneath this is zero-knowledge cryptography. Here is the simplest way I can explain it. Imagine a scales that can confirm two weights are equal without ever displaying what either weight actually is. Both sides balance — confirmed. Neither measurement is visible. The result is verifiable. The data stays private. That is what ZK proofs do inside Midnight Network. Private computation runs on the user's device. The verified result lands on the public chain. The underlying data never moves. It proves. It does not confess.
That changes what blockchain can realistically be used for. Healthcare authorizations. Private financial logic. Compliance verification. Identity confirmation. These are not edge cases. They are the core of how serious institutional activity operates. Selective disclosure — proving what needs to be proven without surrendering everything around it — is not a premium feature. It is the basic requirement these industries have always needed and never had. None of it has ever belonged on a fully public ledger. Midnight Network is building the privacy layer for that gap — the space between everything is visible and nothing is verifiable — as a partner chain to Cardano, drawing on Cardano's established security model and adding private execution where Cardano's public architecture was never designed to reach.
What interests me about the structure is the dual-token model. $NIGHT is Midnight Network's governance and capital asset — publicly traded, currently sitting around $0.0454 after recovering from recent lows. Today's price action is worth noting. Volume has spiked to 7.29 billion NIGHT — the largest single session since the listing day. The price has reclaimed its short-term moving averages for the first time since the post-listing correction began. That is not confirmation of anything. But it is the first signal with conviction after weeks of selling pressure. Holding NIGHT passively generates DUST — a shielded, non-transferable resource that powers private transaction execution on Midnight Network and cannot be sold or moved between wallets. DUST is consumed through use and replenishes over time. Speculation lives in NIGHT. Operations run on DUST. That separation is a long-term infrastructure decision. The short-term price cycle does not touch it.
Mainnet is imminent. The Kūkolu phase — Midnight Network's first full production launch — arrives this month. That is when programmable privacy stops being a thesis and starts being a live environment where developers build shielded applications through the Kachina Protocol and the Compact smart contract language.
Because the honest version of this is that elegant design does not create ecosystems. Rational privacy as a concept does not guarantee that applications built around selective disclosure will attract users who return out of genuine need. A lot of networks have had serious architecture and thin adoption. Midnight needs builders to find the privacy layer useful enough to deploy on — not interesting, not impressive, but necessary enough to build products people keep coming back to.
The design is deliberate. The thesis is coherent. The technology is real. But I keep coming back to the same question every time a network reaches this moment — the one between launch and actual use. Not whether Midnight Network can go live. Whether, after it does, there are applications running on it that could not have been built anywhere else.
That is the test that matters. And nothing written about Midnight Network today, including this, gets closer to answering it than the moment the first real application runs.
#night @MidnightNetwork $NIGHT
