was skimming through the sign litepaper and a couple of integrations people were sharing, mostly around airdrops and credential gating. initially it reads pretty clean — attestations, schemas, token distribution. kind of feels like a nicer abstraction over things we already do with merkle trees + allowlists + some offchain verification.
and i think that’s the surface narrative most people settle on. sign = “onchain credentials” and = some coordination or incentive token layered on top. useful, maybe cleaner, but not fundamentally new.
but that’s not the full picture.
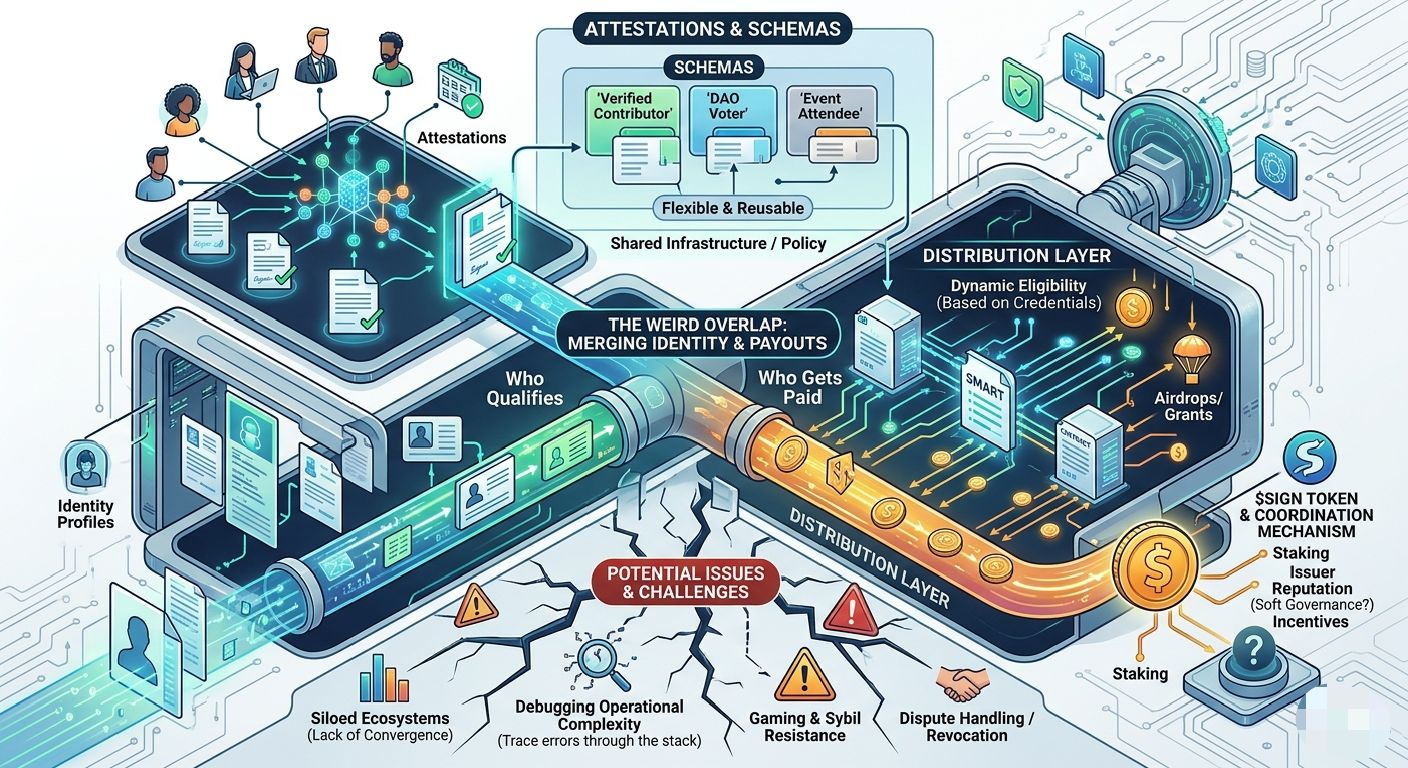
what keeps nagging at me is that sign isn’t just standardizing credentials — it’s quietly merging who qualifies with who gets paid. those are usually separate systems. identity lives somewhere messy and offchain, distribution lives in contracts. sign is trying to compress that into a single pipeline, and that shift has more implications than it looks.
first piece is the schema + attestation model. on paper, it’s just structured data signed by an issuer. but the real design choice is making schemas flexible and reusable across contexts. so instead of hardcoding eligibility logic into each contract, you define a schema like “verified contributor” or “event attendee,” and multiple systems can reference it.
sounds obvious, but the moment you do that, schemas become shared infrastructure. they’re no longer just data formats — they’re policy. if a schema definition is loose or ambiguous, downstream systems inherit that ambiguity. and if multiple issuers can write to the same schema, you now have a trust problem layered on top of a data problem.
and that’s where it gets interesting… because sign doesn’t fully solve that, it sort of defers it.
second piece is the distribution layer. sign packages token distribution (airdrops, rewards, grants) as something that directly consumes attestations. instead of “here’s a list of addresses,” it’s “here’s a rule set based on credentials.” eligibility becomes dynamic, not static.
this is already partially live. you can see projects using sign to gate claims or distribute tokens based on onchain/offchain activity. the mechanics work — attestations are created, users prove eligibility, contracts release tokens.
but the deeper version of this — where distribution logic becomes composable across ecosystems — still feels early. right now, most implementations are fairly contained. the idea that you could carry a set of attestations across multiple protocols and have them universally recognized… that’s more of a direction than a reality.
then there’s $SIGN. it’s positioned as a way to coordinate trust and incentives around the system — staking, reputation, maybe weighting attestations based on issuer credibility.
in theory, that helps solve the “who do you trust” problem. in practice… i’m not sure yet. reputation systems in crypto tend to either centralize quickly or get ignored. if ends up just being used for fees or basic incentives, that’s straightforward. if it’s actually used to rank or gate issuers, then you’re building a soft governance layer on top of identity data, which is harder than it sounds.
some of this is clearly working today. attestations exist, schemas are being used, distribution flows are happening in production. it’s not hypothetical.
but a lot of the more ambitious pieces — cross-protocol standardization, meaningful issuer reputation, as a coordination primitive — still depend on adoption patterns that haven’t really settled.
one thing i keep circling back to is failure modes. like, what happens when an attestation is wrong? or outdated? or intentionally gamed? since distribution depends on these credentials, errors don’t just stay in the identity layer — they propagate into actual value transfer.
and debugging that stack doesn’t look trivial. you’d have to trace through schema definitions, issuer logic, attestation validity, and then the distribution contract itself. feels like a new kind of operational complexity that isn’t obvious at first glance.
also, there’s a subtle coordination risk. if every ecosystem defines its own schemas and trust assumptions, you don’t really get a “global” credential layer — you just get a bunch of semi-compatible silos. the promise of interoperability depends on convergence, not just tooling.
curious about:
* whether a small set of issuers start dominating high-value attestations
* how is actually used in production (beyond docs)
* if schemas converge or fragment across ecosystems
* real-world edge cases — sybil resistance, revoked credentials, dispute handling
feels like one of those systems that looks clean in diagrams but will get messy fast once real money and incentives start flowing through it.
Is post ka mutabik AK image bana do
#signdigitalsovereigninfra @SignOfficial $SIGN