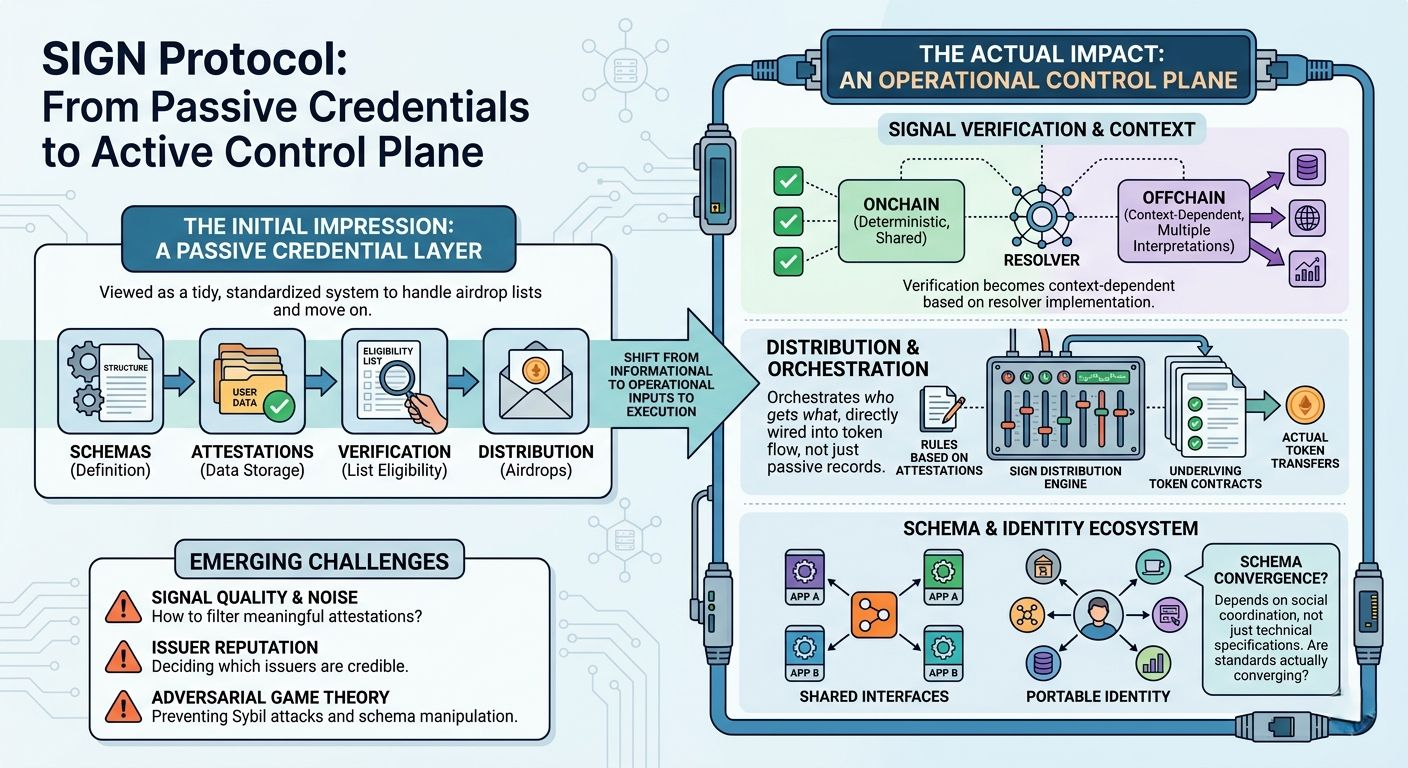
was reading through the SIGN protocol literate and a couple of real-world distribution setups, mostly because it keeps showing up whenever people talk about airdrops or unchain credentials. at first pass it feels very contained — schemas, attestations, verification, then distribution. almost like a tidy pipeline someone finally standardized.
and i think that’s the default framing. people see it as an attestation system with built-in token distribution, basically a nicer way to handle eligibility lists. something you plug in, run once, and move on.
but that’s not the full picture.
the thing that’s slightly hidden is how SIGN turns credentials into something operational, not just informational. once attestations are directly wired into token flows or access control, they stop being passive records and start acting like inputs to execution. and that shifts where complexity lives.
first piece is the schema-driven attestation model. not just “store some data about a user,” but define structured schemas that describe what a credential means. that sounds obvious, but the implication is that schemas become shared interfaces between systems.
and that’s where it gets interesting. if different apps adopt the same schema, then credentials become portable. a contribution recorded in one place could be recognized somewhere else without translation. but that only works if schemas converge, and that’s more of a social coordination problem than a technical one.
right now, parts of this are live — schemas are being defined, attestations issued, and used in production workflows. but most schemas still feel local. they’re tied to specific campaigns or ecosystems, not broadly reused standards. so the “global” part of the infrastructure still feels aspirational.
second is the verification layer, especially the hybrid model SIGN supports. on chain verification is straightforward — deterministic checks that anyone can reproduce. offhand resolution adds flexibility, letting you incorporate external data or more complex logic.
but here’s the thing — once you introduce offhand resolution, verification becomes context-dependent. the same credential could resolve differently depending on the resolver implementation or data source. so instead of a single truth, you get multiple valid interpretations.
this is already happening in practice. eligibility often depends on offhand signals like activity metrics or social data. but there’s no strong standard for how resolvers should behave, which means composability gets a bit fragile. two apps might “support” the same credential but interpret it differently.
third piece is the distribution engine, which is probably the most tangible today. SIGN ties credentials directly to token distribution logic. instead of exporting CSVs and running scripts, you define rules based on attestations and let the protocol handle execution.
this is clearly working. teams are using it to manage airdrops and rewards, and it reduces a lot of manual coordination. but it also turns SIGN into something closer to a control plane — orchestrating who gets what, based on credential state.
still, it doesn’t fully own execution. actual token transfers rely on underlying contracts. SIGN coordinates, but doesn’t replace the execution layer. maybe that’s intentional, but it does limit how “infrastructural” it really is.
the forward-looking pieces — persistent identity graphs, cross-chain credential portability, deeper integrations with wallets — feel plausible but not guaranteed. they depend on credentials being reused across ecosystems, which loops back to schema standardization and trust in issuers.
one thing i keep thinking about is signal quality. if issuing attestations is cheap, then you need a way to filter meaningful ones from noise. SIGN doesn’t enforce that — it leaves it to applications or future layers.
so you end up with a second layer problem: not just verifying credentials, but deciding which issuers are credible. and that can get messy quickly.
also wondering how this behaves under adversarial conditions. if credentials directly influence token flows, there’s incentive to game the system — sybil attacks, coordinated issuance, schema manipulation. none of this is unique, but SIGN makes credentials more central, which might amplify the impact.
watching:
* whether schemas actually converge into shared standards
* how offhand resolvers evolve and whether they stabilize
* if distribution remains the main use case or just the entry point
* emergence of issuer reputation or trust-weighting systems
* real examples of credentials being reused across unrelated ecosystems #signdigitalsovereigninfra @SignOfficial $SIGN