Most identity systems focus on the moment of verification. You present something, the system checks it, and you get a result. But that only shows the surface. Inside SIGN, identity isn’t a single step, it’s a sequence that starts much earlier and continues even after verification is complete.
It begins with issuance, where an authorized entity creates a structured, signed credential tied to a defined schema. Instead of being stored in a central database, that credential is handed directly to the user, who holds it independently. This shifts identity from something requested on demand to something carried and controlled by the individual.
When verification is required, the system doesn’t simply expose the full credential. The user creates a presentation, sharing only what is necessary, sometimes not even raw data, but a proof. At that point, verification becomes a layered process, checking signature validity, issuer recognition, schema compliance, and the current status of the credential, all at once.
That last part is where identity becomes dynamic. A credential that was valid before may no longer be valid now, so the system must confirm its status at the exact moment it is used. This means identity in Sign isn’t fixed, it evolves over time and depends on multiple components working together, including issuers, wallets, verifiers, and registries.
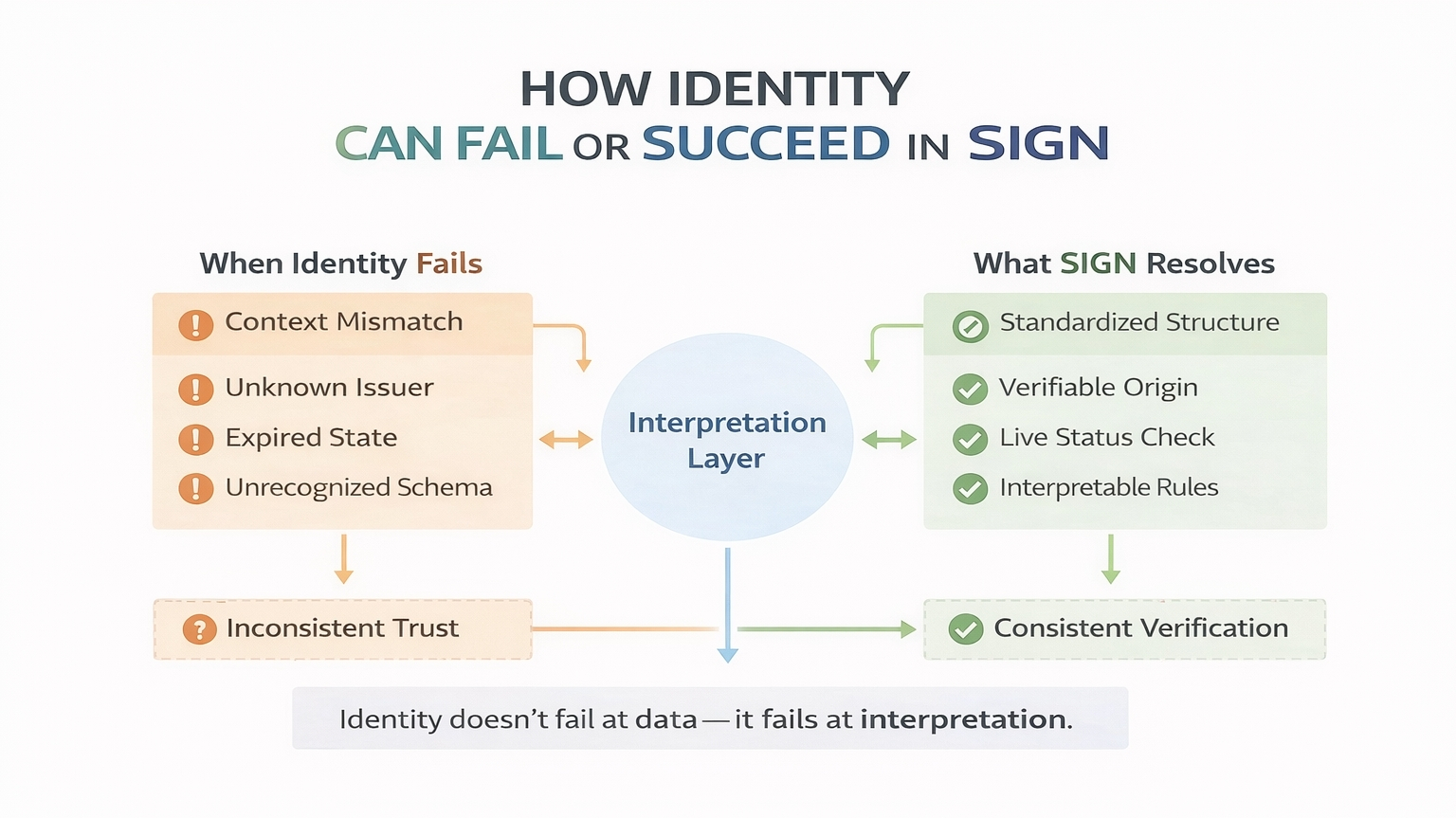
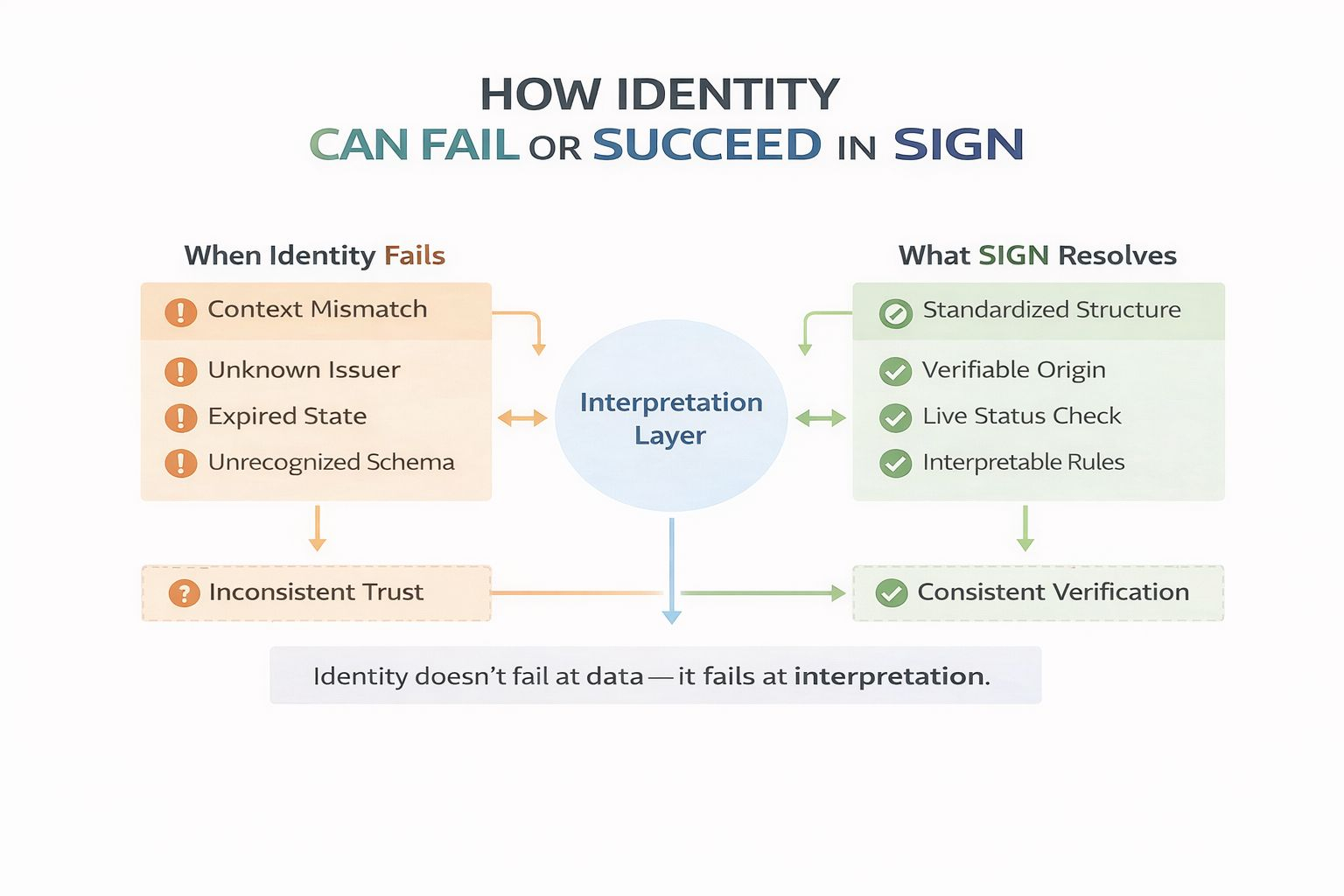
As a result, identity is no longer defined in one place. It is assembled at the moment of use, based on shared rules about who can issue, what formats are accepted, and how validity is maintained. So while identity feels portable on the surface, its meaning is still shaped by the system interpreting it, making it less about static data and more about how different layers stay aligned over time.