In the previous article, we discussed the hell of chips related to $ZBT . Many technical believers rebutted me in the comments: "King, you only look at chips and not technology! @ZEROBASE But it perfectly combines ZKP (Zero-Knowledge Proof) and TEE (Trusted Execution Environment) into a privacy public chain, which is the next hundred-fold holy grail!"
Seeing these comments, I can only shake my head helplessly.
As someone who has been in the Web3 field for many years, what I fear most is "superstition." When you open the white paper of this project, they will indeed tell you a perfect technical fairy tale.
But today, I want to put on a hacker's perspective glasses. Let's break down the "double-layer bulletproof vest" that ZBT prides itself on and see why it might collapse overnight in the face of a hardware vulnerability.
🎭 1. The Perfect Lie: The Myth of ZKP and TEE
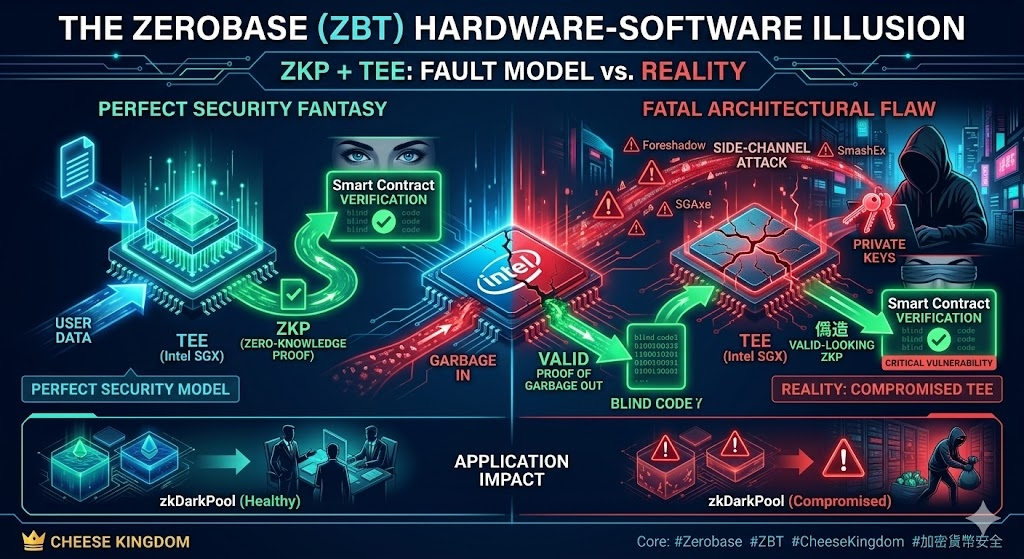
The technical architecture of Zerobase sounds indeed seamless: to balance "privacy" and "performance", they offload the resource-intensive complex computations (such as AI reasoning or institutional-level dark pool trading) to the TEE (Trusted Execution Environment, usually utilizing Intel SGX chips) under the blockchain.
After the chip calculation, the TEE will produce a ZKP (Zero-Knowledge Proof), which is finally handed over to the smart contract on the chain for final verification.
The project's script is written like this: Mathematics (ZKP) guarantees the authenticity of the proof, while hardware (TEE) guarantees that the computing process is absolutely confidential, and no one can peek.
Sounds invincible, right? But within this architecture lies a huge "trust gap."
💥 2. Fatal Wound: The Dark History of Intel SGX and "Side-Channel Attacks"
The cornerstone of Zerobase's entire security hypothesis is tightly bound to one premise: "TEE hardware must be absolutely secure."
But the real world is cruel. Taking the most mainstream Intel SGX as an example, countless catastrophic hardware-level vulnerabilities have long been exposed in recent years, such as the infamous Foreshadow, SGAxe, or SmashEx in the cybersecurity field.
What does this mean?
This represents that a technically skilled malicious node operator (hacker) does not need to crack your unbreakable cryptographic math problem. They only need to exploit the physical vulnerabilities of the hardware to launch the so-called **"Side-Channel Attack"**, allowing them to directly steal the most core "private key" from the secure area of the hardware!
Once the private key is stolen, the so-called "Trusted Execution Environment" instantly becomes the hacker's backyard.
👀 3. The Blind Gatekeeper: The Helplessness of Smart Contracts
At this moment, the most absurd vulnerability mechanism in the entire system was activated.
You must know that smart contracts on the chain are essentially very "dumb." They are like a blind guard who only recognizes passports and does not recognize people.
What happens when a hacker uses a TEE hardware that has already been cracked to forge a malicious transaction (for example, transferring millions of U from the dark pool into their own wallet out of thin air) and signs it with the stolen private key, generating a mathematically "completely legal" ZKP?
The smart contract on the chain will perfectly verify this zero-knowledge proof and then conclude: "Hmm, the mathematical formula is correct, the password is right, proceed!"
This is the most terrifying disaster in cryptography:"Garbage in, valid proof of garbage out".
Smart Contractis logically not hacked at all, but it has been completely blinded by the underlying hardware vulnerabilities. It has personally opened the vault door for the hackers.
🌪️ 4. Devastating Blow to Practical Applications
If this hardware vulnerability is triggered on the mainnet, it will bring nuclear-level destruction to Zerobase's so-called practical applications.
Imagine their flagship application "zkDarkPool (Institutional Dark Pool)".
Wall Street's institutional giants put tens of millions of dollars in, thinking that with ZKP protection, no one can see their order book and bottom cards. But as long as the hacker breaks one of the verification node's TEE hardware, they can not only see all the institutions' bottom cards and conduct risk-free "front-running" but can even directly forge proof and drain the entire liquidity pool.
At that time, how will the coin price move? You can imagine for yourself.
⚖️ The King's Conclusion: This is a game of Russian roulette
Zerobase is definitely a great project that gathers top cryptographic experts. I do not deny their contributions in academia.
But as an investor, you must clearly understand one thing: at the moment you buy in, you are not only investing in the great mathematics of zero-knowledge proof, but you are also betting that "these big companies like Intel will not reveal new hardware vulnerabilities in the future."
In the Web3 world filled with the dark forest rule, binding the security of hundreds of billions of funds to the chips of centralized hardware manufacturers is itself an extremely dangerous game of Russian roulette.
💬 [Discussion Time: Is your faith still there?]
This article is more for distribution; those who can see this are definitely elite hunters from the Cheese Kingdom.
👇 Tell me in the comments 👇
After reading this breakdown, do you still have faith in the technical architecture of ZKP + TEE?
Do you think Zerobase can compensate for this hardware's fatal flaw through software upgrades?
Welcome all technical experts to comment and discuss! The truth becomes clearer the more we debate!