No matter how secure your hardware wallet is in the crypto ecosystem, if your basic operational security (OpSec) is weak, your capital is always at extreme risk. In this final chapter of Demented Capital's strict Educational Analysis series Chapter 3, we will structurally decode the essential security protocols that every institutional trader strictly follows.
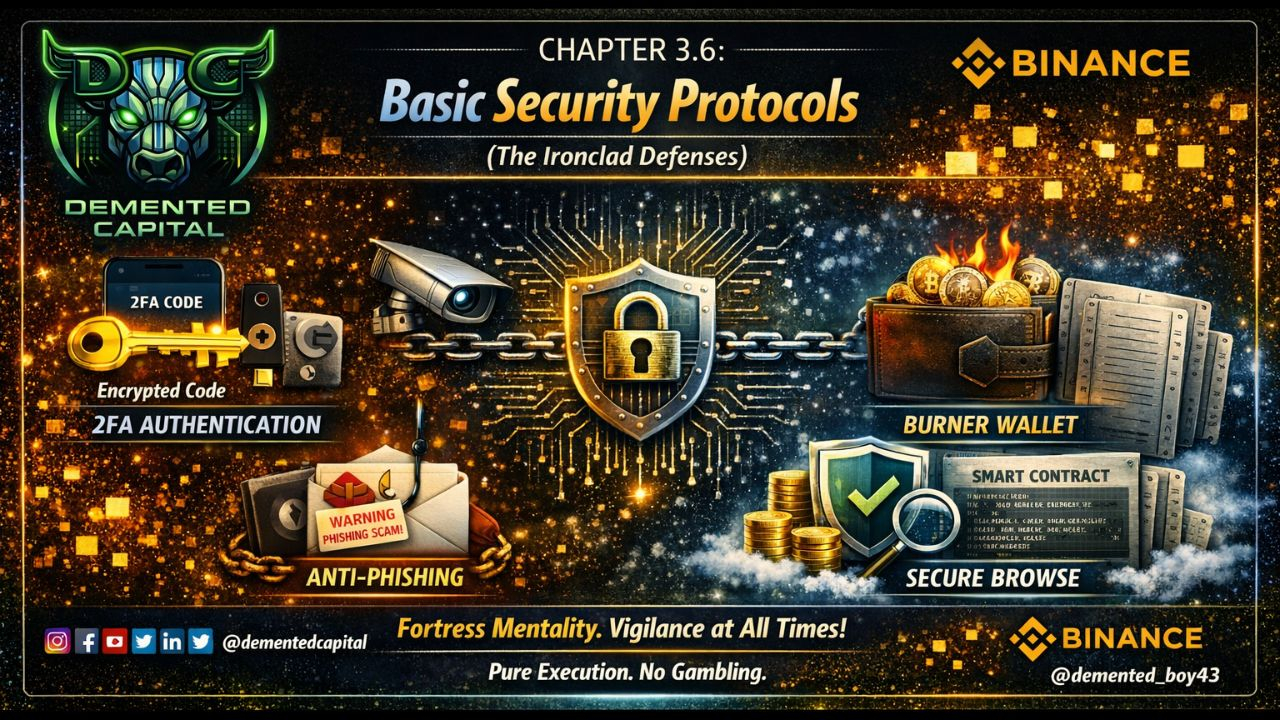
1. Two-Factor Authentication (2FA) Mastery:
Relying solely on passwords is a fundamental flaw. Always use 'Authenticator Apps' (like Google Authenticator or Authy) or 'Hardware Security Keys' (like YubiKey) on all your centralized exchange accounts and emails.
Institutional Rule: Never use SMS-based 2FA, as hackers can easily bypass this OTP through 'SIM Swapping' attacks.
2. Anti-Phishing & Smart Contract Verification:
Retail traders often drain their wallets by clicking on fake airdrop links or malicious URLs.
Protocol: Always access dApp links only from official Twitter handles and CoinMarketCap, and bookmark them. Before signing transactions, verify smart contract permissions to see if they are asking for 'Unlimited Approval' to spend the asset.
3. The 'Burner Wallet' Segregation:
Never interact with any new or unverified Web3 protocol from your main 'Vault' (where your long-term portfolio resides).
Protocol: Always create a temporary 'Burner Wallet' that contains only as much execution capital as required for that specific transaction. If the smart contract turns out to be malicious, your main capital will remain completely safe.
Being lazy in security directly leads to capital destruction. Absolute control over risk management defines our core principle: Pure Execution. No Gambling. 🦅
🧠 The Demented Academy Task:
To make your OpSec impenetrable, visit Binance Academy and aggressively study the modules 'Secure Your Binance Account' and 'Phishing Scams'.
💬 War Room Assessment (Question):
Suppose you accidentally granted a malicious smart contract 'Unlimited Spend Approval' for your wallet. In such a critical situation, what should be the immediate on-chain process to technically revoke (cancel) that permission before your funds are drained? Elaborate your professional operational logic in the comments! 👇
(The best technical answer will receive a special Red Packet reward from Demented Capital this weekend).
💡 Disclaimer: This post is designed purely for Educational Analysis purposes and its primary goal is to enhance fundamental security literacy. Always strictly follow the Do Your Own Research (DYOR) policy before deploying or storing any capital. If this academic curriculum has brought absolute clarity to your operational security framework, please utilize the 'Tip' feature provided below to support Demented Capital's free education initiative.


#CryptoSecurity #OpSec #CryptoEducation #BinanceAcademy #DementedCapital