Blockchain technology was originally celebrated for one powerful idea: transparency. Every transaction could be verified, traced, and audited by anyone. This openness created trust in decentralized systems because people did not have to rely on a central authority. Instead, the network itself provided proof that everything was functioning correctly. However, as the blockchain ecosystem evolved, it became clear that complete transparency also introduced serious limitations.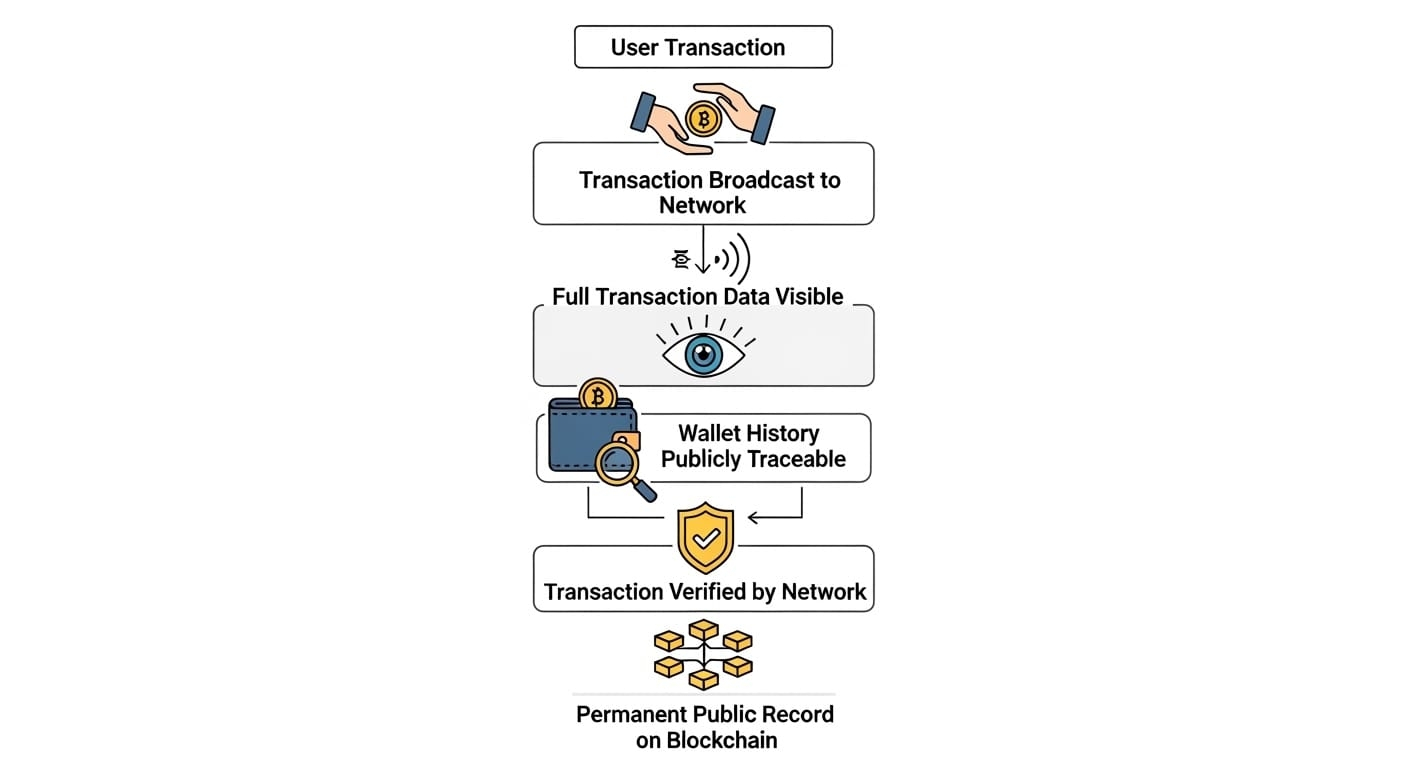
In traditional public blockchains, every transaction is visible on the ledger forever. Wallet histories can be tracked, financial behavior can be analyzed, and business operations can sometimes be exposed unintentionally. While transparency builds trust, it can also create risks for individuals and organizations that require confidentiality. A company using blockchain payments, for example, might not want competitors monitoring its financial flows. Similarly, users may not want their entire financial activity permanently visible to the public.
This growing tension between transparency and privacy has become one of the most important design challenges in modern blockchain infrastructure. Instead of abandoning transparency completely, new blockchain models are trying to redesign how it works. One of the projects exploring this concept is Midnight Network, which attempts to create a system where transactions can still be verified without exposing sensitive data to the public.
The idea behind Midnight is based on separating verification from exposure. In traditional systems, verification requires revealing all transaction details. Midnight proposes a different model where the network can confirm that rules were followed without revealing the underlying data itself. This is made possible through advanced cryptographic methods such as zero knowledge technology. These cryptographic tools allow a network to mathematically prove that a transaction is valid while keeping the private data hidden.
A simple way to understand this is to imagine a student proving they passed an exam without showing the answers they wrote. The system confirms the result but does not expose the entire test sheet. Midnight applies a similar concept to blockchain transactions. The network can verify that rules are satisfied, balances are correct, and processes are legitimate while keeping the sensitive information protected.
This approach becomes increasingly important as blockchain moves beyond early crypto users and begins interacting with real world industries. The next stage of blockchain adoption will likely involve enterprises, financial institutions, and regulated sectors. These organizations operate under strict data protection requirements. Healthcare platforms cannot expose patient information. Financial firms must comply with privacy regulations. Supply chain companies often deal with confidential logistics data.
If blockchain networks cannot protect sensitive information, many industries will hesitate to adopt them at scale. Privacy preserving infrastructure is therefore becoming one of the most important technological directions in the crypto ecosystem. By enabling verification without exposure, systems like Midnight Network attempt to make blockchain usable for a much broader range of applications.
At this point in the article, a useful visual could compare traditional public blockchains with privacy enabled blockchain systems. One side could show how conventional blockchains expose transaction histories and wallet activities. The other side could illustrate how privacy focused systems verify transactions while keeping sensitive information hidden. This type of comparison helps readers quickly understand the structural difference between the two models.
The market narrative around privacy technology has also been strengthening across the broader crypto industry. Several major trends are contributing to this shift. Institutional adoption is increasing, and institutions require secure environments where sensitive information is protected. At the same time, the idea of user data ownership has become a core principle of Web3. People increasingly want control over their digital identity and personal information rather than leaving it permanently exposed on public networks.
Regulation is another factor influencing the development of privacy focused blockchain systems. Governments often require both transparency and confidentiality at the same time. Financial systems must be auditable while also protecting individual privacy rights. Blockchain infrastructure that can satisfy both conditions may become extremely valuable as regulation continues to evolve globally.
From my personal perspective, many of the most important crypto innovations initially appear underappreciated. Infrastructure improvements often take time before the market recognizes their full significance. Scaling technologies, for example, were once considered niche technical experiments. Today they are essential components of the ecosystem. Privacy preserving infrastructure may follow a similar path.
When real world companies begin building serious applications on blockchain networks, privacy stops being an optional feature and becomes a fundamental requirement. Systems that successfully combine verifiability with confidentiality could become critical building blocks for the next generation of decentralized applications. This is one reason why the direction taken by Midnight Network is particularly interesting. Instead of focusing on short term hype, the project attempts to solve a deeper architectural limitation within current blockchain design.
Another useful visual could appear here in the form of a simple process diagram. The diagram could illustrate how a user submits a transaction, how cryptographic proofs verify rule compliance, how the network validates the transaction, and how the sensitive information remains hidden throughout the process. This type of illustration can help readers understand the practical mechanics behind privacy preserving blockchain transactions.
If this model of blockchain infrastructure continues to evolve successfully, several new opportunities may emerge. Enterprise decentralized applications could expand significantly because companies would be able to protect proprietary information while still using blockchain networks. Financial institutions could interact with decentralized liquidity without exposing sensitive client data. Secure digital identity systems could allow individuals to prove credentials without revealing complete personal information.
Despite these opportunities, there are also important risks to consider. Privacy focused blockchain systems rely on advanced cryptography, which increases technical complexity. This complexity can create development challenges and performance considerations that must be addressed carefully. Regulatory misunderstanding is another potential obstacle. Some policymakers may associate privacy technology with illicit activity even though the goal is actually to protect legitimate data.
Adoption also depends on developers. Building privacy aware applications requires new tools, programming models, and design patterns. If the developer experience is not intuitive, adoption could progress more slowly than expected. For investors and ecosystem participants, understanding these risks is just as important as recognizing the potential opportunities.
Looking forward, the long term direction of blockchain technology appears to be moving toward selective transparency rather than absolute openness. Instead of revealing every piece of data to the entire world, networks may allow different layers of visibility depending on context and permissions. Verification would remain public and auditable, while sensitive data could remain protected.
In many ways, this shift resembles the evolution of the internet itself. Early internet communication lacked secure encryption layers, which made sensitive transactions risky. Over time technologies like HTTPS became standard, allowing secure communication without sacrificing connectivity. Blockchain infrastructure may now be entering a similar phase where privacy preserving technologies become standard components of the ecosystem.
For investors observing long term crypto trends, privacy infrastructure represents a sector that could grow significantly as the industry matures. As blockchain moves deeper into enterprise systems, financial markets, and real world applications, the demand for secure and confidential transaction environments will likely increase.
Projects exploring this architecture, including Midnight Network, are essentially attempting to redesign how trust works in decentralized systems. Instead of relying solely on full transparency, they aim to build systems where mathematical verification ensures integrity while personal and business data remain protected.
If blockchain is going to power the next generation of financial infrastructure, digital identity systems, and decentralized applications, the ability to rethink transparency may ultimately become one of the most important innovations in the entire industry.
@MidnightNetwork #night $NIGHT

