I started by asking myself a question that most blockchains never force you to consider: how can a network confirm every transaction without ever seeing the actual inputs?
As I observed Midnight Network in real time, the answer emerged layer by layer. Each $NIGHT transaction behaves almost like it carries its own logic, a self-contained mathematical statement. Validators never touch the raw inputs yet they confirm correctness reliably. It felt like watching a language of proofs, where the proof itself speaks for the transaction.
The first layer of this pattern is the off-chain execution environment. Every contract or transfer executes entirely outside the public ledger, invisible to validators. What makes this even more incredible is that it is not a simple encrypted computation; it is complete functionality, generating a zero-knowledge proof that represents the accuracy of each operation. After seeing several transactions, it seemed to me that validators are completely oblivious to the very data that they are checking. They act as verifiers of mathematical truth, confirming the proof rather than the transaction contents themselves.
I followed several multi-step contracts to see how the proofs interact. Each proof is composable, meaning the output of one transaction's proof can feed directly into the next while remaining confidential. Watching sequential contracts unfold, I realized that Midnight allows complex chains of computation to execute without exposing any intermediate state. For example, a series of confidential financial operations can progress while validators only see the proofs. This transforms privacy from a restriction into a mechanism that enables parallel execution and high throughput.
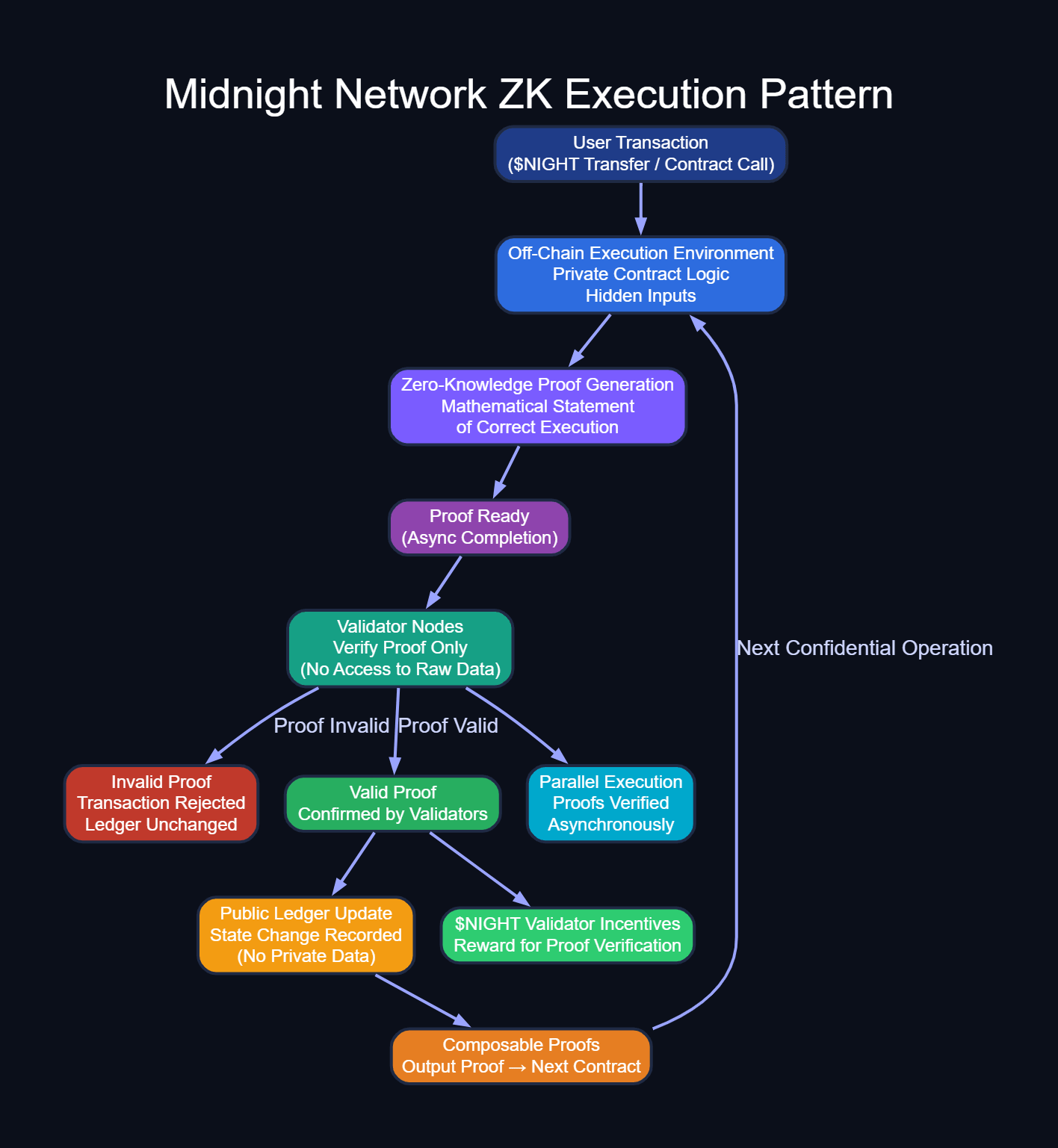
Error handling further highlights the uniqueness of the system. In conventional confidential systems, failed transactions can require complex rollbacks or produce silent errors. Midnight's validators only see proofs. A single invalid proof is immediately rejected, and the ledger state remains untouched. Observing the system, I noticed this creates an elegant self-healing property: errors are contained automatically without revealing any underlying data, and validators maintain efficiency because they never need to inspect transaction details directly.
The network's performance under heavy load revealed another non-obvious behavior. Proofs arrive asynchronously, yet Midnight maintains a deterministic validation order. Validators confirm proofs as they become ready, rather than processing transactions strictly in chronological submission order. Watching thousands of transactions during a test cycle, I noticed that this design allows parallelization without compromising consistency, essentially turning privacy into a performance advantage. Privacy constraints, often considered a bottleneck, here actively facilitate scalability.
I also observed subtle timing patterns that most users would never see. Proof generation occurs in variable time depending on the complexity of the off-chain computation. However, because validators only inspect the proofs and not the inputs, the system naturally accommodates this variance without blocking other operations. The network behaves like a dynamic conveyor of truth, where proof readiness, rather than transaction order, dictates progress. This observation made me realize that the architecture is not just private it is resilient to variable computational workloads.
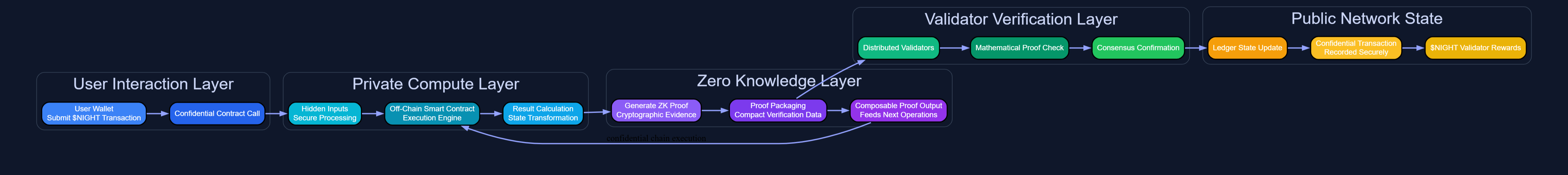
A deeper insight came from tracing $NIGHT token incentives. Validators are rewarded exclusively for successful proof confirmation, not for storing or inspecting sensitive user data. Watching this interaction, I realized that Midnight aligns privacy, correctness, and economic security in a single loop. Validators have no incentive to compromise confidentiality, and users gain a system where their data never leaves the isolated computation environment. The ZK execution pattern is not just a privacy tool it's the engine driving validator behavior, efficiency, and economic alignment simultaneously.
Finally, observing the system over time highlighted the predictable interplay between privacy and verification. Proofs are the only interface between hidden computation and public state. They make sure things are carried out accurately, discover errors, and allow sequences of tasks to be performed in chains all without exposing the actual data. Thus, Midnight does more than just the use zero-knowledge proofs as a cryptographic tool, it also uses this concept as a core operational principle, enabling confidential, scalable, and economically efficient execution. After seeing it working, I realized that NIGHT is much more than a token it is the driving force behind a proof-based, privacy-oriented blockchain ecosystem.
Midnight Network's ZK execution pattern demonstrates that privacy does not need to be a trade-off. By considering proofs as the main medium conveying truth, the network is able to provide confidentiality, correctness, and very efficient execution all in one cohesive system. Watching this unfold, one can see that Midnight fundamentally changes the concept of blockchains working with extreme secrecy, making zero-knowledge not just a security feature but the very framework of validation.
