In the extremely transparent jungle of Web3, 'stealth' is the highest level of protection.

Preface: The 'double-edged sword' of transparency
In the narrative of Web3, transparency has been the core justice of decentralization. But with the evolution of algorithmic predators (MEV Bot), for large holders, 'excessive transparency' is evolving into a danger.
Recently, the most talked-about topic in the circle is the tragedy of being precisely hunted, where 50 million in assets instantly shrank during liquidity exhaustion. Many see the excitement, but I see a chilling reality: when your wealth is 'naked' on the chain, you are not just trading; you are sending a 'food coordinate' to global predators.
We must move beyond the single 'private key management' mindset and build a 'three-dimensional defense system' that is resistant to algorithms and physical risks.
Dimension one: physical noise reduction of permissions (don't place permissions in the same location)
The foundation of security should not rely on a single 'point' but should be established on 'the decentralization of power'.
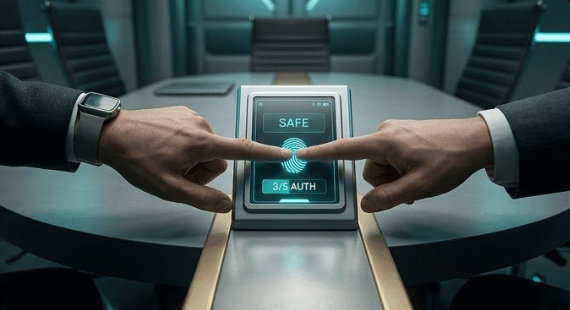
The necessity of Multisig:
If you have assets worth over a million, managing with a single private key is like jumping into a fire pit. Utilizing Gnosis Safe and other multisig solutions to achieve 3/5 signatures can not only intercept hackers but, more importantly, buy you crucial buffer time through physical decentralization when facing extreme external pressures.Dynamic segmentation of assets:
Large assets should adopt a tiered storage approach of 'core cold wallet + semi-active warm wallet + daily hot wallet'. Core assets must remain in a state of physical isolation year-round and must never touch any connected terminal.
Dimension two: 'data desensitization' of underlying logic (privacy is the bulletproof vest of the digital age)
Physical isolation can defend against 'withdrawals', but cannot prevent 'viewing'. In the millisecond-level on-chain games, 'stealth' is the highest form of defense.
"Privacy should not be stigmatized; it is the 'digital bulletproof vest' of large traders."
Shifting from 'exposure' to 'minimizing disclosure':
That's why Midnight (NIGHT) based on zk-SNARKs (zero-knowledge proofs) is becoming the focus of the industry. Its logic is very hardcore: you do not need to prove to the entire network how much balance you hold; you only need to prove to the consensus layer, "I have the right to initiate this operation."Defense against algorithmic predation (Anti-MEV):
Through the zk-Logic framework of Midnight, the paths and positions of large transactions can be effectively obscured. When algorithmic predators cannot obtain your exact psychological bottom price, the so-called 'precise hunting' will instantly lose its aim.

Dimension three: automated risk-averse circuit breakers (using code to counter millisecond-level hunting)
In the algorithm era, relying on human neural responses to counter machine liquidation logic is futile. Defense must be coded, achieving a paradigm shift from 'post-fact stop-loss' to 'pre-fact protection'.
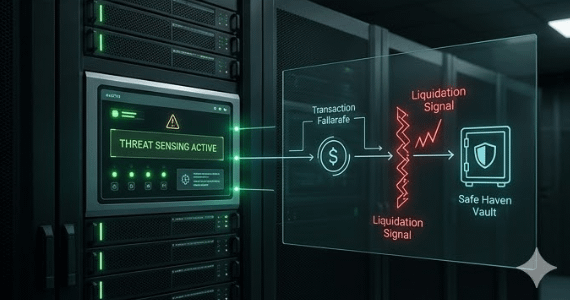
Pre-set privacy protection contracts:
Future security models should possess 'active perception' capabilities. We can utilize Midnight's Compact language to write monitoring contracts with privacy attributes.Preventive circuit breaker mechanism:
When the contract detects an address being scanned abnormally or monitors abnormal liquidation signals, it can use the priority of underlying mechanisms to automatically redirect assets to pre-set secure 'safe havens' under privacy protection.
Building the technical sovereignty of 'survivors'
"The essence of technology is to empower freedom, and security is the foundation of freedom."
The costly lessons are essentially the final warnings left by the 'transparent logic' of the old era. In the digital wilderness, we must learn:
Decentralization: solving single point physical failures;
Desensitization: using Midnight's underlying algorithms to hedge against hunter perspectives;
Circuit breaker: replacing emotional responses with coded execution.
Extinguish that torch that exposes your location, and move silently, to truly walk dignifiedly in the second half of Web3.#night @MidnightNetwork $NIGHT #Web3 #MEV