 A while ago I started thinking about something that most blockchain discussions rarely address directly. When people talk about decentralized systems, the focus usually lands on consensus, security, and scalability. Those layers are obviously critical. But another layer quietly sits underneath every interaction on a network.
A while ago I started thinking about something that most blockchain discussions rarely address directly. When people talk about decentralized systems, the focus usually lands on consensus, security, and scalability. Those layers are obviously critical. But another layer quietly sits underneath every interaction on a network.
How information is allowed to move.
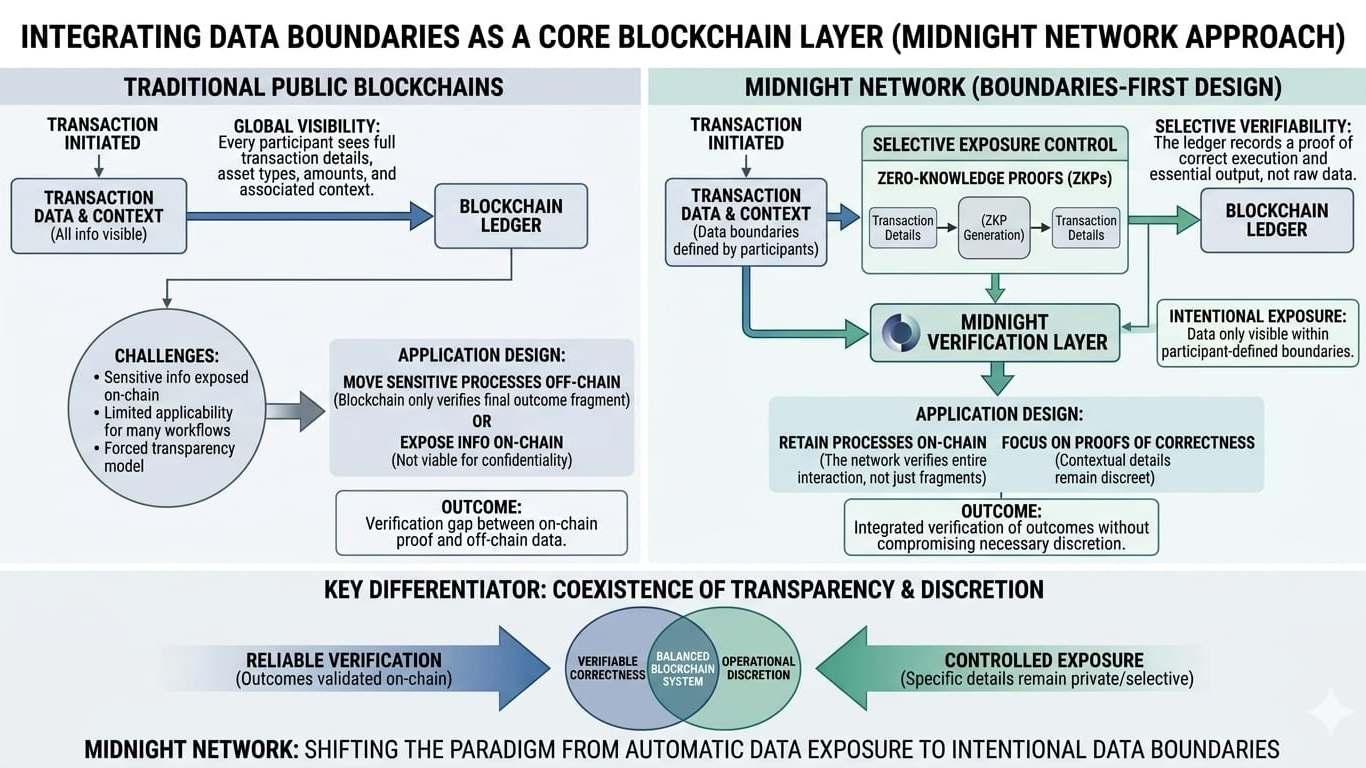
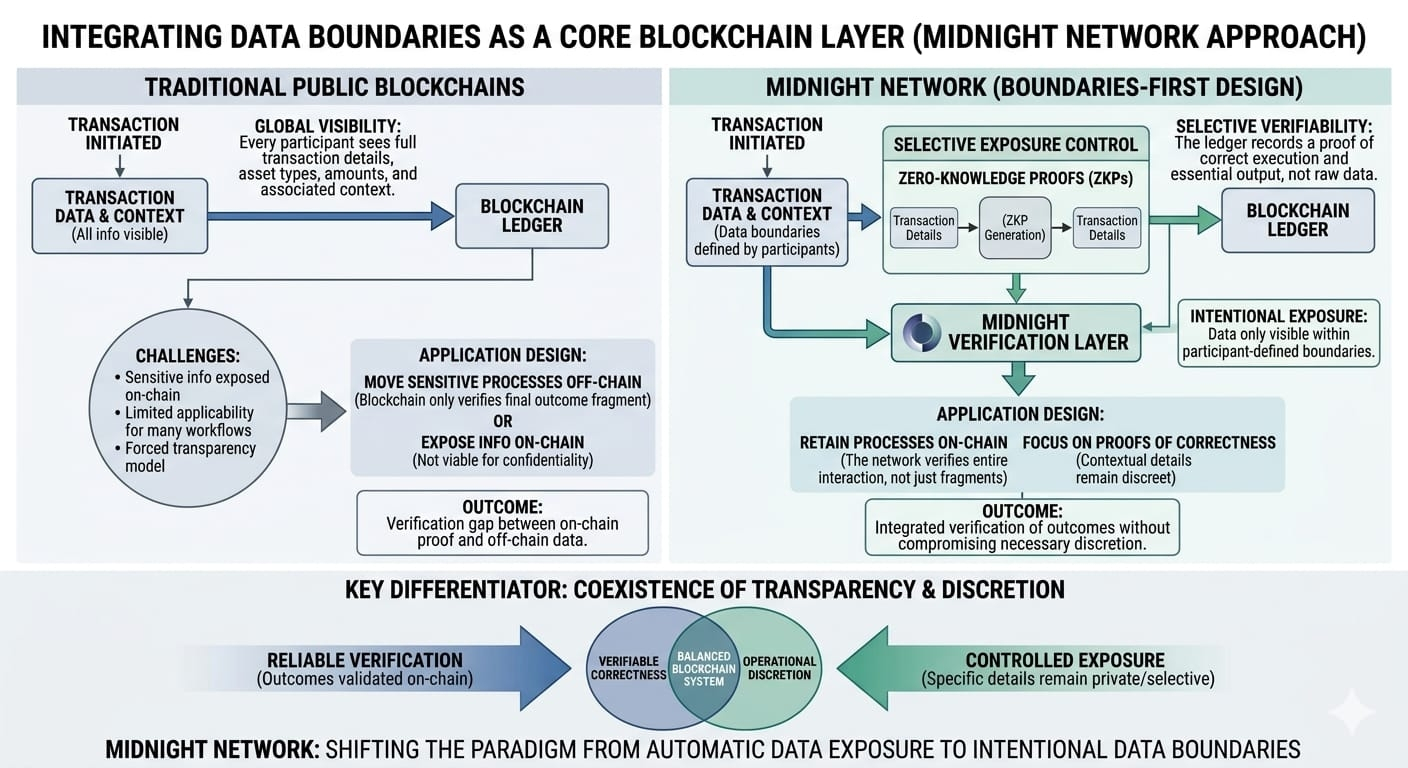
In most public blockchains, that movement follows a simple rule. Once data enters the system, it becomes visible to everyone who observes the ledger. This approach works well for financial transfers and other transparent processes, but it introduces complications when applications involve information that cannot comfortably exist in an open environment.
That tension is where Midnight Network begins to feel different.
Instead of treating data exposure as a necessary side effect of decentralized verification, the network appears to approach information boundaries as an intentional design layer. The goal is not simply to record activity but to allow systems to confirm that interactions occurred correctly without forcing every piece of context into permanent public visibility.
This idea may seem subtle, but it changes how developers can structure decentralized applications.
On many blockchains today, builders must carefully redesign their systems so that sensitive information never touches the ledger. Entire components of an application often move off-chain just to prevent private details from becoming publicly accessible. As a result, the blockchain ends up verifying only a portion of the process while the rest happens elsewhere.
Midnight attempts to close that gap.
By enabling verification that does not require revealing the entire informational context of an interaction, the network allows more of the process itself to remain inside the decentralized environment. The protocol validates outcomes while the surrounding data remains within the boundaries defined by the participants involved.
For developers, this creates a more flexible design space.
Instead of asking how to avoid exposing sensitive information on-chain, builders can focus on structuring systems where only the necessary proof of correctness becomes part of the network. The blockchain acts as a validation layer while the detailed context stays controlled by those participating in the interaction.
That distinction could become more important as decentralized systems expand into more complex environments.
Early blockchain applications largely revolved around simple transfers of digital assets. As the technology evolves, developers are exploring systems that involve multi-party coordination, structured agreements, and workflows that contain layers of operational information. These interactions often require both verifiability and discretion.
Midnight’s architecture appears designed to support exactly that balance.
Instead of forcing developers to choose between transparency and privacy, the network introduces an environment where both can coexist. Verification remains reliable, but the exposure of information becomes intentional rather than automatic.
Of course, infrastructure alone does not determine whether a network becomes meaningful.
The real signal will come from the ecosystem that grows around Midnight. If developers begin creating applications that depend on controlled data boundaries rather than universal visibility, the network’s philosophy could start influencing how decentralized systems evolve.
Because the future of blockchain infrastructure may not depend solely on how fast data moves.
It may depend just as much on how carefully that data is allowed to appear.
#night $NIGHT @MidnightNetwork #SECClarifiesCryptoClassification #MetaPlansLayoffs