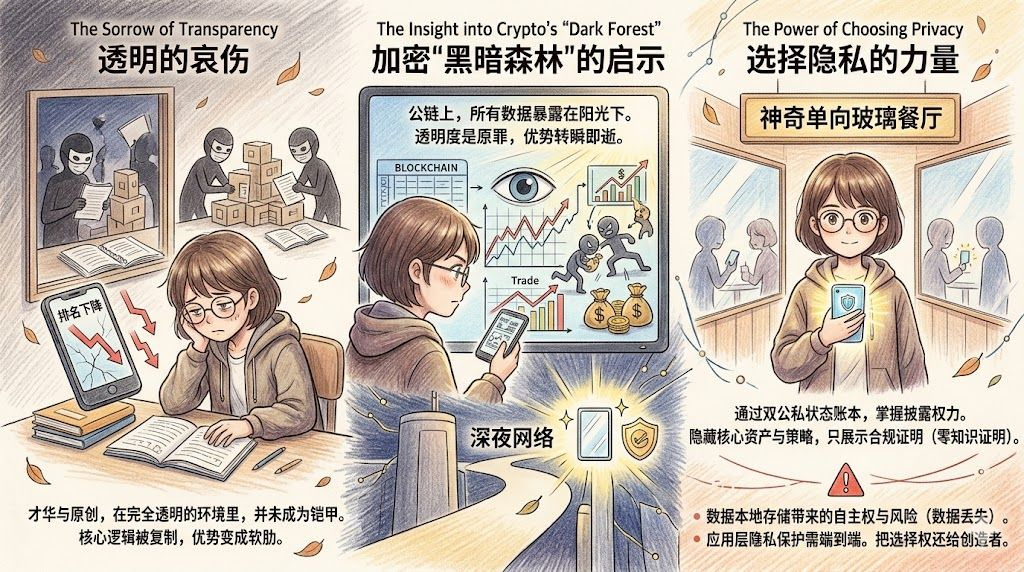
These days, the first thing I do every morning is watch my once-proud ranking gradually slide down. That feeling is like watching the castle I built brick by brick being gradually emptied by a group of people who can't even understand the blueprint.
I reviewed it for a long time, trying to find the loopholes in the strategy, but the conclusion I reached left me with a chilling sense of dread. It wasn't a smarter opponent that defeated me, but countless rough copies. My writing style, my analytical framework, and even the emotional ups and downs in my words have been imitated pixel by pixel in the square. The cold and blind algorithm of the platform, when faced with a vast amount of homogenized content, did not reward the source of unique ideas, but instead ruthlessly lowered my originality weight because it judged my content to lack uniqueness.
The sincerity and sharing that I once believed in without doubt, my unreservedly revealed bottom cards, ultimately turned into a finely sharpened dagger, held by others, and turned back to stab my soft underbelly. In this completely transparent square, my advantage became my most lethal weakness.
This skin-deep pain suddenly reminded me of the crypto world I have been researching during this time. This is not only the sorrow of a content creator like me but also the cruel slaughter that unfolds every day in the entire blockchain world, especially in those public chains where all data is exposed to the sunlight.
In this on-chain world known as the dark forest, transparency is not only the original sin but also the grave of efficiency.
A top quant institution spends countless days and nights and invests huge amounts in R&D costs, finally running a trading strategy on the chain that can achieve stable profits. However, in this world where all ledgers are turned upside down, every action they take to open positions, every point they build, and every direction of capital flow is like being placed under the spotlight on an operating table. Countless eyes are focused on these smart money addresses, and those who follow along to copy the homework outnumber those who are genuinely thinking by hundreds or thousands of times.
The more precise the strategy, the more abundant the rewards; it is captured by machines and followed by retail investors faster. In this environment where the cost of replication is almost zero, any advantage window brought by information asymmetry is being infinitely compressed. You think you have discovered a gold mine, but from the moment you swing down your first pick and bundle the first transaction on chain, this coordinate has already been broadcast to the whole world.
It wasn't until I truly understood the design philosophy of @MidnightNetwork that I realized we have been running naked in a transparent maze for too long, forgetting the right to wear clothes.
In this ecosystem, what fascinates me the most is its dual public-private state ledger built at the protocol layer. This may sound a bit obscure, but if you imagine it as a restaurant with a magical one-way glass, it becomes much easier to understand.
The magic of this glass lies in the fact that the restaurant owner, who is also the data owner, can absolutely control what can be displayed in the window and what is forever locked in the safe in the back kitchen. When an institution executes their mysterious strategies on such a network, what assets they buy, at what secret price they transact, these core secrets will remain hidden behind the scenes forever. What is displayed in the public ledger is merely a compliance certificate.
This proof is like a pass, announcing to everyone: I just completed a legally compliant transaction according to network rules. But as for what I actually did, no comment.
Zero-knowledge proof technology plays the most fascinating role here, perfectly achieving the separation of verification and disclosure. You can prove to the whole world that you are a law-abiding good citizen, but you do not need to lay your diary open on the street for anyone to browse. On traditional transparent chains, the information advantage you painstakingly built is fleeting; under the protection of this private track, your operation records are an unfathomable black box to the outside world. Others know you are competing in the market, but they cannot even touch the corners of your clothing, let alone replicate your steps. Your advantage, therefore, can be preserved for a long time.
In my opinion, this privilege of being able to freely switch between light and dark forms is invaluable for two types of pioneers.
First and foremost are those institutional traders who lick blood on the knife's edge. In this dark forest where running bots run rampant and sandwich attacks are widespread, they desperately need a barrier that can conceal their presence. Within this barrier, they can calmly arrange their troops without worrying that their bottom cards will be fully exposed to their opponents.
Following closely are those physical enterprises that have always hesitated to enter the blockchain world. Letting them throw contracts containing core supplier lists, confidential customer data, and sensitive business terms directly onto a public chain for everyone to see is no different from letting them voluntarily stuff their business secrets into their competitors' mailboxes. Through the private state track, enterprises can finally enjoy the immutability of on-chain certification while tightly holding onto the confidential contents that determine their survival.
However, this seemingly perfect privacy fortress is not without its Achilles' heel. There is a logical closed loop that I took a long time to see the hidden dangers within.
In the design of this network, the hidden private state data is actually stored locally on the user's device; it has not been uploaded to the network nodes. This means that while the absolute sovereignty of this data is handed over to you, the absolute responsibility that accompanies it also weighs on your shoulders.$NIGHT #night
If you lose the locally stored data due to device damage or backup errors, then this part of private status may forever fall into an abyss. What remains online is just the encrypted mark proving that you once did something, but you can no longer retrieve the original appearance of that thing. For those giants with mature data management systems, this design of data sovereignty is a long-awaited boon; but for ordinary people who might write their mnemonic phrases on scrap paper, this is undoubtedly a ticking time bomb. While enjoying privacy, you must possess the self-protection capabilities that match it.
In addition, this privacy philosophy also faces challenges from another dimension. No matter how well the underlying protocol seals the door, if the windows at the application layer are broken, then all privacy protection will be reduced to mere talk.
Privacy has never been a single-node issue; it is an end-to-end project that must run through the entire process. The underlying network can ensure that your data flows on the chain cloaked in invisibility, but if a crude decentralized application quietly collects your behavioral trajectory at the front end and even leaks this information, then no matter how exquisite the cryptographic design at the bottom layer is, it is futile. Handing the keys to developers and users also means handing over the risk of making mistakes.
My thoughts were pulled back to the square incident that has been troubling me in recent days.
The reason I helplessly watched my hard work being dismantled, reorganized, and then used to defeat me is fundamentally because I naively thought that in a completely transparent environment, talent and originality could serve as armor to protect myself. I realized too late that hiding core logic and maintaining a moderate sense of mystery is the true wisdom for survival in this world filled with profit seekers.
In this dimension, the network with dual ledgers has given me great inspiration. Its core value is not providing an invisibility technology, but rather completely returning the power to choose between transparency and concealment to the creators themselves. You can choose to share in the sunlight or choose to move in the dark. What should be shown to the world, and what should be kept for oneself, this decision belongs to you, not determined by some powerful platform or an irreversible transparency mechanism.
Today, I finally truly felt what a sharp double-edged sword data transparency is. Only when the blade cuts through your own skin and you watch the blood flow out do you truly understand how expensive and necessary it is to have an undisturbed private territory in this era of naked running that can be observed, deconstructed, and replicated at any time. And this is the first lesson that I, along with everyone who has hit a wall in the transparent maze, must learn.