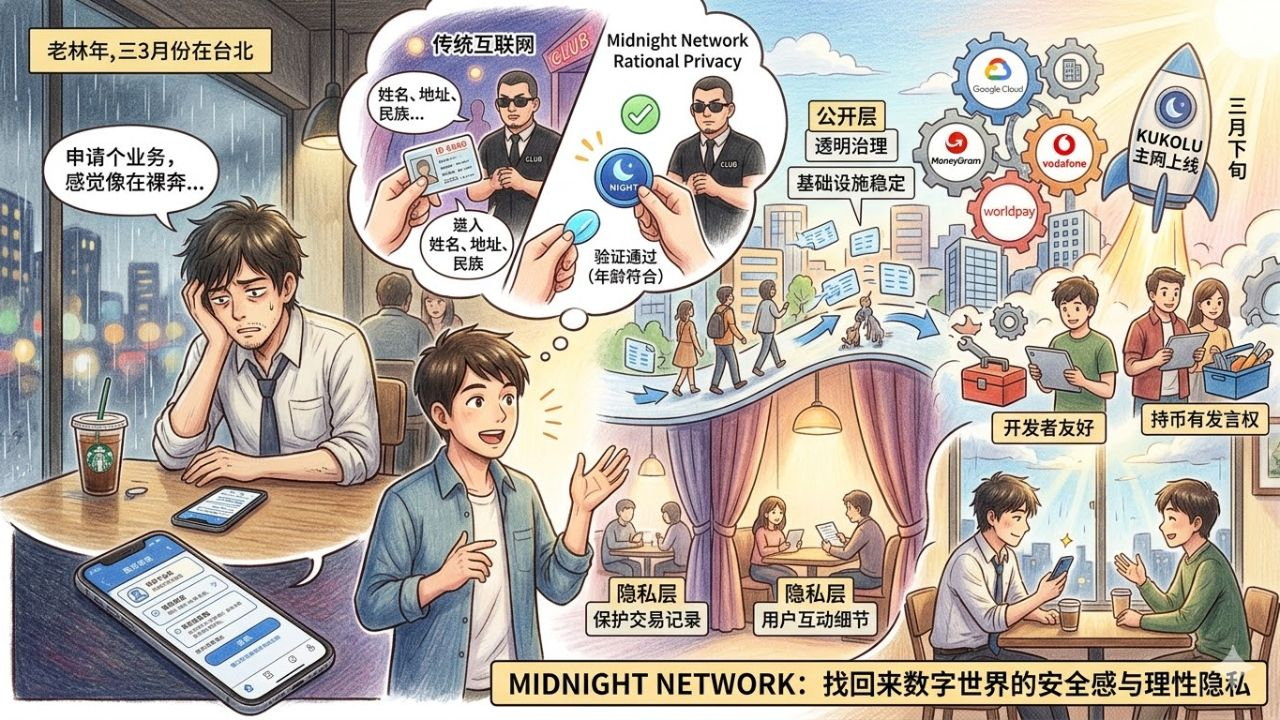
The rain in Guangdong in March always falls in a drizzling manner, making people's mood a bit damp and moldy. Old Lin sat opposite me, irritably flipping his phone face down on the table, producing a dull sound. He had just spent half an hour wrestling with the registration page on the screen to apply for a new payment business port for his small cross-border e-commerce company. During this half hour, he not only uploaded photos of the front and back of his ID card, took pictures of his bank card from various angles, but also completed live facial recognition with his mouth open and eyes blinking under the glaring fill light. This was not the end; finally, a long document popped up with dozens of pages filled with professional jargon regarding data authorization privacy terms. Only by checking the agreement would his previous efforts not be in vain. Old Lin sighed, took a gulp of the already cooled American coffee, and complained to me that doing serious business now feels like running naked on the internet, with even the most private boundaries being seen through by those platforms.
Looking at his helpless expression, I felt a deep resonance inside. While enjoying a convenient digital life, it seems we have unconsciously accepted an extremely unequal transaction. To order takeout, we need to open up precise geographical location; to borrow a small amount of emergency funds, we need to hand over our entire phone's contact list; to prove I am who I am, we have to surrender our most core personal privacy. Every time I buy a plane ticket, I soon receive targeted promotional messages; this experience is familiar to everyone. We always complain about our privacy being hollowed out, but in front of that little consent button, ordinary people have no room to resist. This feeling is awful, like living in a bustling community yet discovering that your house is made entirely of transparent glass, and everyone passing by can clearly see what you're doing in the living room, while you don’t even have the right to pull the curtains.
However, the trajectory of the virtual world is not always a downward parabola. I mentioned to Old Lin an ecological network I have been observing closely lately; it’s called @MidnightNetwork , and the corresponding token symbol is $NIGHT . Old Lin is somewhat resistant to complex technical terms, so I changed the way I explained it to him. I told him that what truly moved me about this project is that it does not sell an extreme anarchist view of privacy. Many technologies that primarily focus on privacy tend to go to the other extreme, hiding everything in absolute darkness, which results in becoming a breeding ground for gray areas, making regulation and trust impossible. Midnight proposes a philosophy called rational privacy. It acknowledges that we need to prove our qualifications in an orderly society but firmly rejects excessive demands from the system.
This is like going to a night club that only allows adults. The security guard stops you and asks to verify your age. In the real world or the current internet mechanisms, you have to pull out your ID and hand it over, which not only shows your birth date but also your real name, home address, and even your ethnic information. The guard only needs to confirm that you are over eighteen, but he gets all your details. The underlying logic of Midnight is that it provides a clever mathematical proof method; you only need to show the guard a result that proves you meet the age requirement, and the guard can confidently trust this result through the system, but he still knows nothing about your name or address. You only display the necessary conditions, and all the remaining details stay safely in your pocket.
Old Lin’s eyes lit up slightly upon hearing this, and he asked how this mechanism, which sounds like magic, operates within such a vast network. I continued to analyze the underlying design of this network for him. Midnight divides the network into two distinctly defined layers. The public layer is like a city hall and wide main road, responsible for governance, consensus, and overall system stability, ensuring that all infrastructure is transparent and trustworthy to the world. The privacy layer, on the other hand, is like private rooms with heavy curtains drawn, specifically designed to protect the details of specific transaction records, smart contract operations, and users' daily interactions. When you complete a payment or sign a business agreement in the privacy layer, the public layer will only record that a legal activity occurred here, but it will never broadcast the specific amount, time, and parties of your transaction to the world.
What’s even rarer is that this advanced protective umbrella is not a high-and-mighty technological utopia. Many times we cannot use safe products because the technical barriers for developing them are too high. But #night provides developers with very friendly programming tools, so even programmers who are not well versed in complex cryptography can quickly build applications that protect user privacy. We can imagine that in the near future, whether it’s for daily transfers, asset proofs, or online shopping refund processes, we will be able to naturally use this upgraded secure version. No longer will we worry about exposing our consumption habits to countless data traders just because of a regular online shopping action.
Moreover, for ordinary users or participants in the ecosystem like us, the mechanisms it designs are also very humane. Holding NIGHT tokens is not just to watch the numbers rise on the trading panel. In its ecosystem, as long as you hold it, the system will automatically generate a type of network resource for you, which is specifically used to pay for various fees required for your operations in the network. This effectively binds the operational costs of the system to the long-term interests of users. More importantly, holding it means you have real say; you can participate in deciding the future direction of the project through voting, and which core functions to upgrade. In this internet world always dominated by big companies, ordinary people finally have a ballot to express their demands.
Upon hearing this, Old Lin habitually stroked his chin and raised a very realistic question. He asked if this seemingly beautiful vision might just be a self-indulgence within a small circle, as without the support of large institutions, no matter how good the technology is, it is difficult to land. I smiled and shook my head, telling him that this is also why I have extremely high expectations for it. Just last week, the absolute giant in the global payment field, Worldpay, and the well-known crypto exchange, Bullish, officially announced their participation in their node alliance. If you don’t feel much about these two names, the following list will definitely be shocking. Prior to this, industry giants such as Google Cloud, MoneyGram, eToro, Vodafone Pairpoint, and Blockdaemon have all joined in. A total of ten giants with significant positions in traditional finance, cloud computing, and global communications have collectively become the solid support behind this network.
When traditional industry giants begin to be willing to invest real money and server resources to maintain a privacy network, it is no longer an experiment confined to paper but a real industrial revolution happening. According to their solid and steady progress, the federal mainnet, known as the Kukolu phase, is officially set to launch in the last days of March. This means that from the very first day the mainnet starts, these battle-tested global nodes will be maintaining its operation day and night, ensuring the highest level of stability, whether facing sudden traffic or potential attacks. It is gradually turning theory into daily applications that each of us can truly touch.
The rain outside seems to have lightened up a bit, and the background music in the café has changed to a soothing jazz tune. Old Lin looks at the page on his phone that finally shows the review has passed, and his expression is no longer as tense and frustrated as it was before. We may still need to endure a period of passivity and helplessness under the current internet's established rules, but the emergence of Midnight Network makes me firmly believe that privacy issues are absolutely not a dead end where one must choose between giving everything away or being completely invisible. It should be a door belonging to us, with the key safely in our hands. How wide we open it and who gets to take a peek is entirely up to us. In the not-so-distant future, when we handle daily trivialities in the digital world, we will eventually regain that long-lost sense of security.