What is most exhausting on the chain is not the disclosure itself, but the fact that disclosure is treated as a default means. Many systems, when encountering thresholds, limits, or qualifications, turn verification into a 'disclosure': you must provide original materials to obtain approval. The problem is that once the original materials enter the process, they naturally accumulate—archiving, copying, associating, secondary use... You think you are just completing a verification, but in reality, you are providing fuel for future portraits.
@MidnightNetwork tries to reverse this default logic: verification can exist, but it does not have to come at the cost of exposure. The significance of ZK here is very simple—allowing you to prove that conclusions are valid without laying out your life for the system to inspect.
1) 'Usability' is not speed; it is about not letting verification become information plunder.
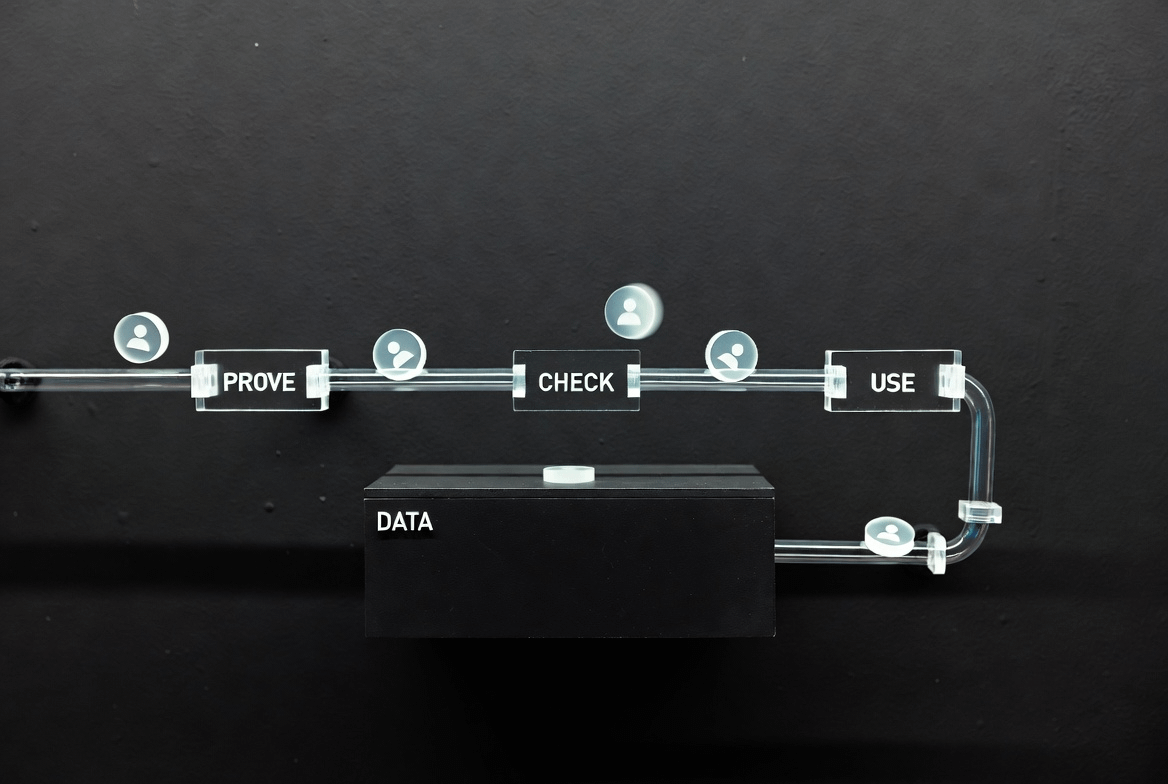
What real-world businesses often need are conclusions: qualified, not excessive, having permissions, executed according to rules. The traditional on-chain approach is to exchange originals for trust; Midnight is more about rewriting trust into verifiable proof. You prove the proof, but try to keep the originals from going out.
This makes 'privacy' no longer a luxury, and also makes 'usability' not require users to sacrifice ownership first.
2) The place where ownership is most easily compromised is the inertia of processes.
Many systems are not evil; they are just 'convenient': storing a bit more for easy verification; keeping things longer for convenience; associating a bit more to prevent risks. But once fragments accumulate, users will unknowingly become transparent.
@MidnightNetwork The value lies in transforming 'proof' into alternative paths: allowing external parties to obtain conclusions instead of originals. The originals remain on the user side or in controlled domains, making ownership feel more genuinely existent.
3) What tokens need to do is turn proof capabilities into a long-term supply.
Proof generation, verification, infrastructure maintenance, and toolchain support all require long-term costs. If the network wants to make 'doing things with minimal exposure' the default experience, it must have continuous resource supply and rule evolution capability. $NIGHT here is more like a network component: on one hand, it bears the consumption brought by usage, while on the other hand, it bears the execution costs of upgrades, parameter adjustments, anomaly handling, and corrections. Otherwise, projects can easily stall at 'technically correct, but heavy on experience,' and in the end, everyone returns to the old path.
4) The hardest test is actually product testing.
Common failure points in ZK-related solutions are not due to inability, but usability: the complexity of developer integration, unpredictable costs, and user interaction resembling problem-solving. If Midnight wants to take a pragmatic route, it must allow proofs to be invoked like components, enabling users to complete verification as if following a conventional process. Only when people stop discussing privacy, because 'it's not exposed by default,' will it truly stand firm.
@MidnightNetwork It's not about mystery, but restraint. Separating verification from exposure returns data protection and ownership to the users, while still getting things done. The value of $NIGHT will ultimately be validated by whether this 'default interaction method' works.

