While I was winding down after another long CreatorPad session on Sign + $SIGN , I pulled up the attestation explorer just to clear my head. One fresh entry caught my eye right away — Attestation ID 0x308e1, created minutes earlier by address 0xB1f50c6C34C72346b1229e5C80587D0D659556Fd under the HolonymV3 schema. Nothing flashy, just a clean identity-style claim on scan.sign.global. It sat there alongside a handful of others from the same attester in the prior hours, all verifiable on-chain.
That simple pull shifted something for me. I had gone in expecting the protocol’s omni-chain attestation layer to feel airtight, the kind of infrastructure that quietly underpins real-world trust without loose ends. Instead, the sheer volume of parallel attestations made me pause. What if two of them contradicted each other on the same subject?
The thought lingered because I’ve seen this pattern before in smaller protocols I’ve audited over the years. You build for scale, deploy across thirty-plus chains, and suddenly the edge cases multiply. Sign Protocol doesn’t pretend otherwise; it records every signed claim exactly as submitted. No central oracle steps in to arbitrate.
Actually — that’s when the late-night reflection deepened. I remembered a small personal trade I executed last month where an off-chain credential clashed with on-chain data I was relying on. The delay in sorting it out cost me hours of manual cross-checking. Here, with $SIGN powering governance and incentives around these attestations, the same friction feels baked in at the protocol level.
I kept refreshing the explorer page, watching new IDs appear every few minutes. Each one added another data point, yet none carried an automatic “truth” flag. It was observational, not dramatic, but it corrected an assumption I had carried into the task.
the contrast that stuck with me
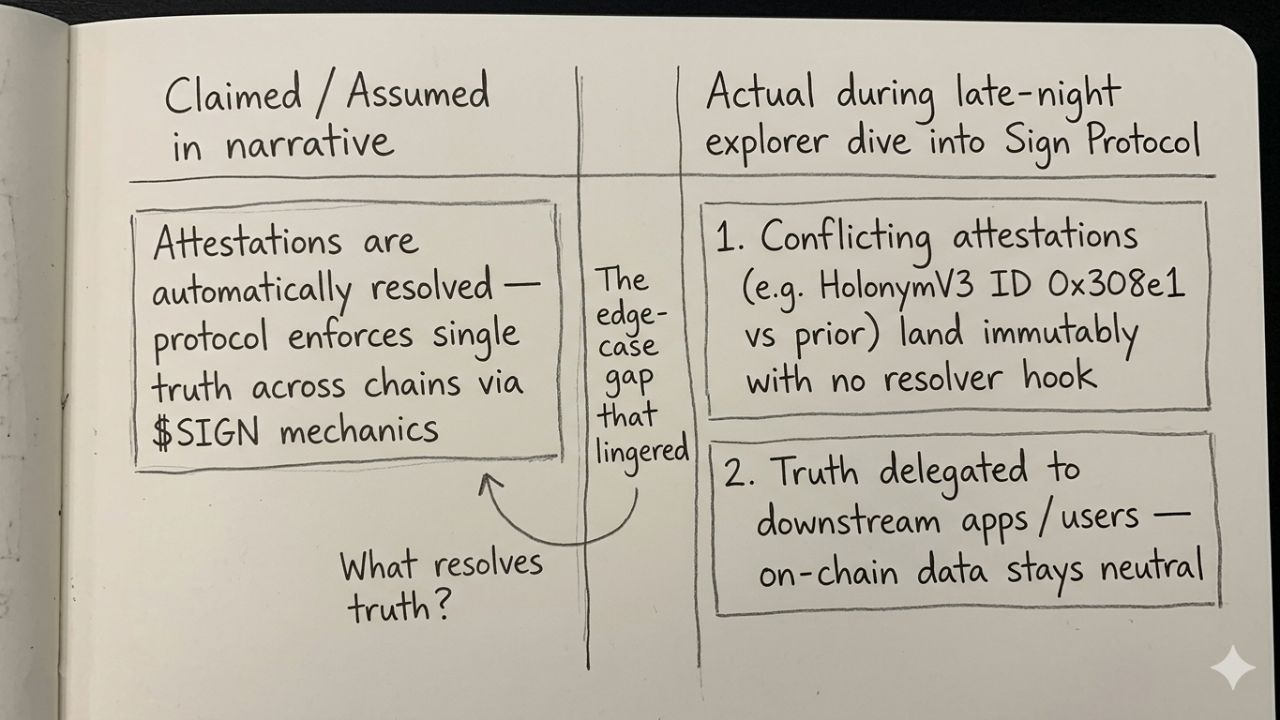
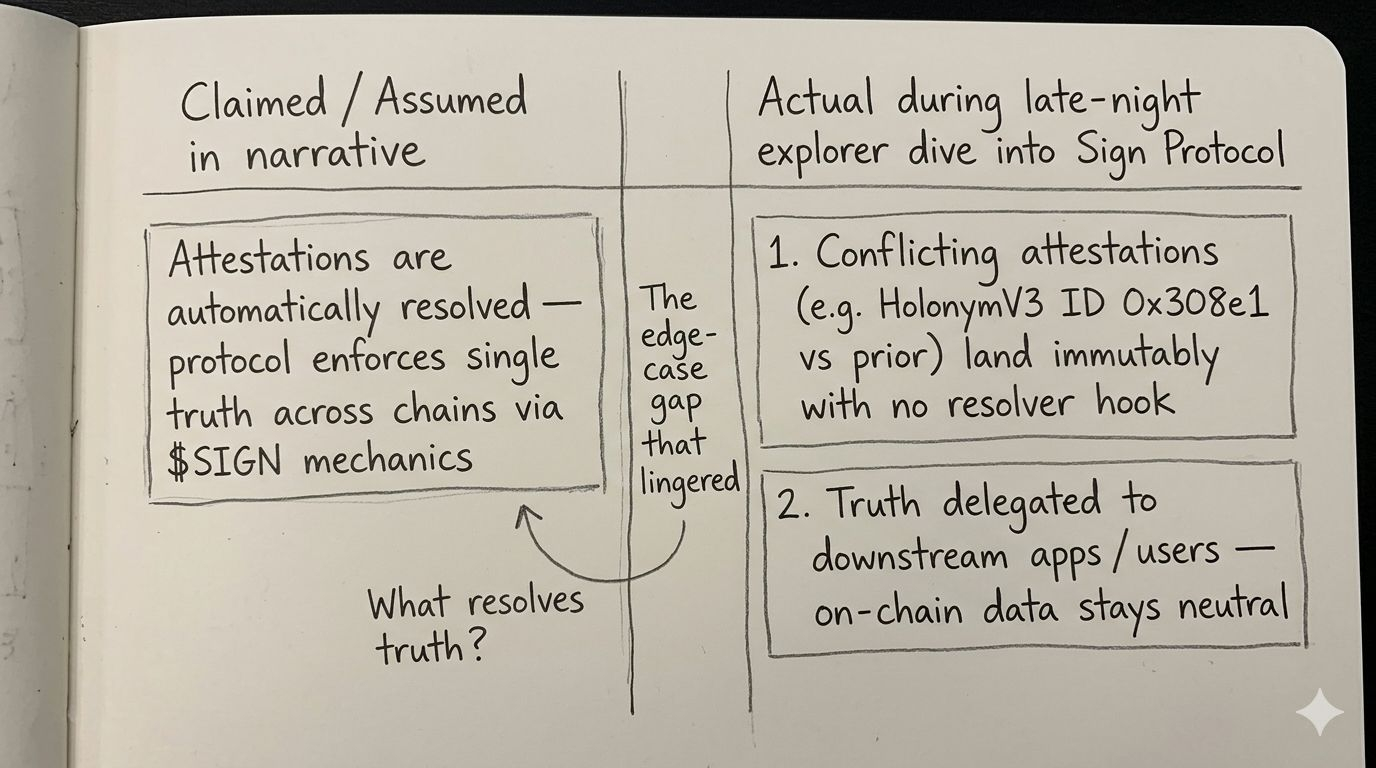
The contrast that stuck with me was between the marketed narrative of seamless verifiable trust and the raw mechanics I observed on-chain. Sign Protocol positions itself as the evidence layer for everything from credentials to token flows, yet when two attestations collide — say, one claiming compliance and another flagging a revocation — resolution lives outside the core contract logic.
It’s not a bug; it’s a deliberate design choice that keeps the layer lightweight and omni-chain. The attester signs, the schema validates structure, and the data lands immutably. Consumers then decide what to trust. I found myself nodding at the elegance while simultaneously noting the responsibility it shifts downstream.
One timely market example hit close: remember the wave of DeFi lending platforms last quarter that integrated attestation-based KYC wrappers? A couple of them quietly forked their own resolver contracts because the base layer offered no tie-breaker. Another case was a small DAO using Sign for membership proofs; when duplicate attestations surfaced from a compromised signer, the community had to vote manually rather than rely on protocol-level consensus.
That pattern echoes across the space right now. Protocols chasing mass adoption lean on Sign’s flexibility, but the hidden feedback loop emerges in high-stakes scenarios where truth isn’t binary.
I jotted a quick note to myself: three interconnected layers — issuance, verification, resolution. The first two are robust here. The third remains contextual, almost human in its subjectivity.
Hmm… it feels both liberating and exposed.
hmm... this mechanic in practice
Hmm… this mechanic in practice forces a reevaluation I wasn’t quite ready for. During the CreatorPad deep dive I assumed the protocol would surface some lightweight resolver hook for conflicting attestations, maybe tied to $SIGN staking or governance signals. Nothing like that showed up in the schema examples or the recent on-chain activity I reviewed.
Instead, the system treats every attestation as sovereign. That’s powerful for privacy-preserving use cases, yet it leaves the question of “what resolves truth” to whoever queries the data. I caught myself revising an earlier mental model mid-session — the one where decentralized trust meant automatic finality. Actually, it means composable finality.
A second market example reinforced it: cross-chain bridges experimenting with attestation oracles have started layering secondary proofs precisely because a lone conflicting pair can stall liquidity flows. It’s not theoretical; I’ve monitored similar stalls in real-time dashboards over the past week.
The personal story that surfaced for me was simpler. Last year I helped a small team integrate an early attestation schema for supplier verification. When a duplicate claim appeared from a test wallet, we spent an afternoon debating revocation strategies because the protocol itself stayed neutral. That memory resurfaced sharply while staring at tonight’s HolonymV3 batch.
The insight feels quietly profound: Sign excels at recording intent across chains, but it delegates the burden of truth to the applications built on top. No hype, just the reality of where the edge case lives.
Still, that delegation carries weight in a maturing ecosystem.
still pondering the ripple
Still pondering the ripple, I keep returning to how this plays out for everyday users versus institutions. The protocol’s strength — its refusal to over-engineer resolution — protects it from becoming another centralized point of failure. Yet it also means that in moments of genuine conflict, participants must bring their own context or risk paralysis.
I adjusted my thinking again there, acknowledging that the omni-chain nature amplifies both the upside and the friction. Two forward-looking reflections keep circling: first, how governance around SIGN might eventually introduce optional resolver schemas without compromising the base layer; second, whether builders will naturally converge on shared patterns for handling duplicates, turning the edge case into a new primitive.
There’s honest skepticism mixed in. I’m not convinced every team will handle the responsibility gracefully, especially under time pressure or regulatory scrutiny. The mechanism feels mature in theory but still carries that subtle unrefined quality I’ve come to respect in protocols that prioritize correctness over convenience.
The whole session left me with a clearer sense of the project’s real-world operation — beyond the surface-level access, deeper into the quiet dynamics that actually shape usage.
In the end, it’s the kind of detail that only surfaces after you sit with the explorer long enough for the attestations to feel less abstract and more like living data points.
What happens, I wonder, when the first high-profile conflicting pair forces the ecosystem to formalize its own answer to truth?
@SignOfficial #SignDigitalSovereignInfra