If we turn off the market noise, we will find the real impact of the Middle East situation, not only on oil prices or risk preferences, but on systemic friction: cross-border cooperation is more sensitive, compliance changes more frequently, and identities and permissions are more easily scrutinized. The escalation of conflict and uncertainty will raise the 'cost of trust', even affecting macro-financial expectations; at the same time, cyberattack activities are also more likely to rise during such periods, and systems need more verifiable and traceable mechanisms to provide a safety net.
In reality, the most common flashpoint in resource allocation is not 'lack of money', but 'having money but not being able to distribute it'.
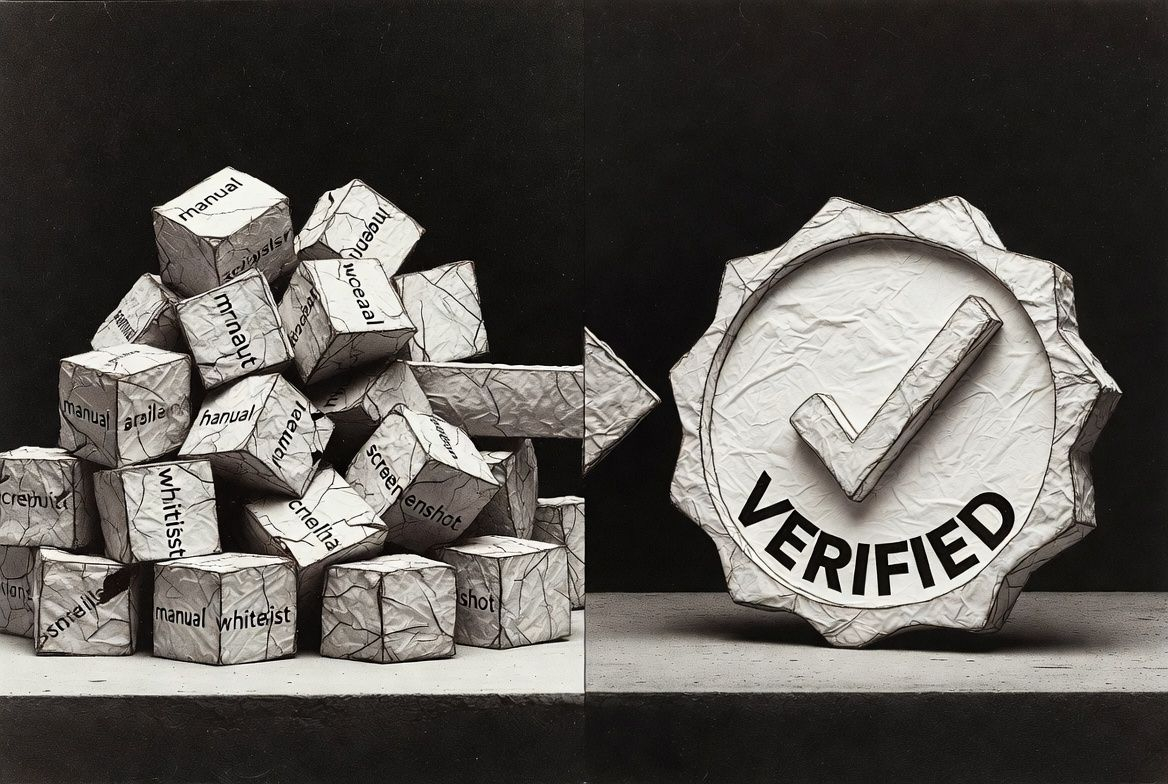
The reasons are very basic: unclear qualifications, unrecognized evidence, and irreversible processes. You will see three familiar disaster combinations:
Qualification proof relies on screenshots: emails, forms, manual whitelisting; during pressure periods, the cost of forgery and repeated claims is extremely low.
Compliance audits rely on people piling up: queuing, errors, version inconsistencies, eventually turning into 'the louder voice is right'.
Distribution execution is uncontrollable: if sent incorrectly, it cannot be recalled; if sent slowly, it triggers a run; if exploited, it cannot be reclaimed; when disputes arise, there is no way to roll back.
At this time, @SignOfficial the value is not 'telling a story', but making two things into infrastructure, allowing the system to retreat from the hell of manual labor.
1) @SignOfficial The first thing done: industrializing 'what gives you the right'.
'Qualifications' are inherently the softest things: who is a member, who is a contributor, who passes the review, who meets the criteria. During pressure periods, it becomes the hardest source of conflict: why can he receive it, but I cannot.
If SIGN can turn qualifications into verifiable credentials, it shifts the controversy from 'do you believe it or not' back to 'can it be verified'. Verifiable, traceable, reusable means that repeated audits across activities, partners, and regions will decrease, shortening the chain of disputes.
2) @SignOfficial The second thing done: upgrading 'how to distribute' from an operational action to an execution pipeline.
Distribution is not 'marketing', but 'cybernetics'. The real challenge is: distributing according to rules, blocking under conditions, stopping payments in case of anomalies, rolling back disputes.
In a cross-border, identity-sensitive environment like the Middle East, the closer distribution is to financial-level actions, the less it can rely on temporary scripts and manual approvals. More critically, the regulatory framework is also pushing for 'executable compliance': for example, the legal development in the UAE includes certain virtual asset-related payment services within the regulatory scope, meaning the process must be auditable, must be reviewable, must be explicable.
3) $SIGN The growth space: from 'activity props' to 'network components' watershed.
There is only one real watershed: $SIGN whether it is strongly bound to network usage.
When verification and distribution become high-frequency public capabilities, the network requires long-term resource supply (services, maintenance, anti-cheating, dispute handling) and rule evolution (parameter updates, strategy adjustments, anomaly handling). If $SIGN takes on roles like settlement/incentives/governance/restraint at the network level, its demand will be closer to the 'usage density curve'; if it is just a marketing symbol, it will be closer to the 'emotional curve'.
The situation in the Middle East provides a stress test:
Conflict and uncertainty rise → trust costs increase, reviews become more frequent.
Cyber attack activities are more active → risks of forgery/disruption/phishing are higher, and qualification systems are more likely to be targeted.
In this environment, infrastructure that is 'verifiable + executable' is more likely to be forced to the table and more likely to show real use.

4) The cold water to be thrown: @SignOfficial the difficulty lies not in the concept, but in adoption and counteraction.
The infrastructure track is not romantic; the difficulties usually involve three things:
Ecological adoption: whether partners are willing to hand over key processes to it.
Counteraction costs: exploitation and forgery will continue to evolve.
Compliance adaptation: regulations change quickly in different regions, and it should be able to adapt long-term and be auditable.
But it is precisely because of these difficulties that it is decided that if it runs smoothly, it will be more like a 'default item' rather than a one-time hotspot.
The situation in the Middle East will not directly 'reward' any tokens; it will only expose the system's weaknesses faster. @SignOfficial It focuses on the weaknesses themselves: qualifications are untrustworthy, distribution is uncontrollable, and disputes cannot be resolved.
