#BitcoinPrices This phrase refers to a next-generation digital trust system that combines identity verification + cryptographic credentials + token-based systems—often powered by blockchain and decentralized identity (DID).
Let’s break it down clearly 👇
🔑 1. What is Credential Verification Infrastructure?
At its core, it’s a system that proves “who you are” or “what you’ve done” digitally—securely and instantly.
✔️ Traditional model:
Centralized (banks, governments, platforms)
Requires repeated verification (KYC, documents)
✔️ Modern global model:
Uses Verifiable Credentials (VCs)
Based on cryptography (not trust in institutions)
👉 A Verifiable Credential is:
Digitally signed proof (ID, degree, license, etc.)
Tamper-proof and instantly verifiable �
TechRadar
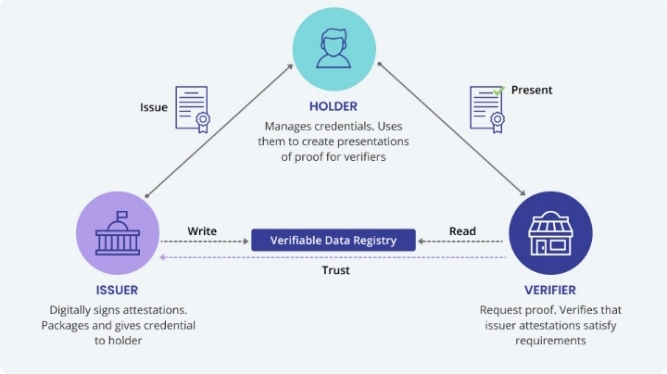
🔺 2. The Core Architecture (Trust Triangle)
Every global credential system works on this 3-party model:
🏛️ Issuer
Government, university, company
Issues signed credentials
👤 Holder
You (user)
Stores credentials in a digital wallet
🔍 Verifier
Employer, app, exchange
Verifies without contacting issuer
👉 This removes middlemen and speeds up verification �
Blockchain Council
🔐 3. The Technology Stack Behind It
🧩 Key Components:
1. Decentralized Identifiers (DIDs)
Unique digital identity (like a blockchain-based ID)
Linked to cryptographic keys
2. Digital Wallets
Store your credentials
Let you share selective data
3. Blockchain / Distributed Ledger
Stores proofs, revocations, trust registries
Ensures transparency & immutability �
DiceID
4. Cryptographic Proofs
Digital signatures verify authenticity
No need to contact issuer
🪙 4. Token Distribution Layer
Now comes the second half: token distribution
This infrastructure is often combined with:
💸 Tokens used for:
Identity verification rewards
Airdrops (e.g., Web3 projects)
Access control (token-gated apps)
Reputation / proof-of-contribution
⚙️ How it works:
User verifies identity (via credentials)
System checks eligibility
Smart contracts distribute tokens
👉 Example:
Verified user → gets token rewards
Verified contributor → earns reputation tokens
🔄 5. Advanced Model: Dual-Token Systems
Some systems use two types of tokens:
User Validation Token (UVT) → proves identity
Data Verification Token (DVT) → proves data integrity
This dual model improves security against fraud and impersonation �
MDPI
🌍 6. Why This is “Global Infrastructure”
Because it enables:
🌐 Interoperability
One credential works everywhere
No repeated KYC
🔓 Self-Sovereign Identity (SSI)
Users own their data
No centralized database �
Orochi Network
⚡ Instant Verification
Seconds instead of days
🛡️ Privacy
Share only what’s needed (not full identity)
🚀 7. Real-World Use Cases
🏦 Crypto exchanges (KYC reuse)
🎓 Education (digital degrees)
💼 Hiring (verified skills)
🗳️ DAOs (reputation-based voting)
🎮 Gaming (identity + rewards)
🌐 Web3 airdrops (sybil-resistant distribution)
🧠 Simple Way to Understand It
👉 Think of it like:
“A global digital passport + wallet + reward system combined”
Your identity = cryptographic credential
Your wallet = storage + control
Tokens = incentives + access
⚠️ Final Insight
This infrastructure is still evolving, but it’s becoming:
The backbone of Web3 identity
A replacement for passwords & centralized logins
A key layer for fair token distribution
If you want, I can:
Show real platforms using this (World ID, Polygon ID, etc.)
Or explain how to build one step-by-step 🚀