While I closed a small Base liquidity position two nights ago and poured that third coffee, the Sign Protocol attestation tab refreshed and showed something that made me pause mid-sip. I had routed a quick cross-rollup transfer through $SIGN thinking it was just extra verification overhead on an already-fast L2. #SignDigitalSovereignInfra and @SignOfficial had been humming in the background of my trades for weeks, but this time the flow felt different—tighter, almost necessary.
The attestation landed cleanly on Base, chain ID 8453, using the on-chain schema for a simple credential match. Nothing flashy. Yet the moment I piped it into my downstream contract on another rollup, the cross-chain hook fired without a hitch. That small win sat with me longer than the trade itself.
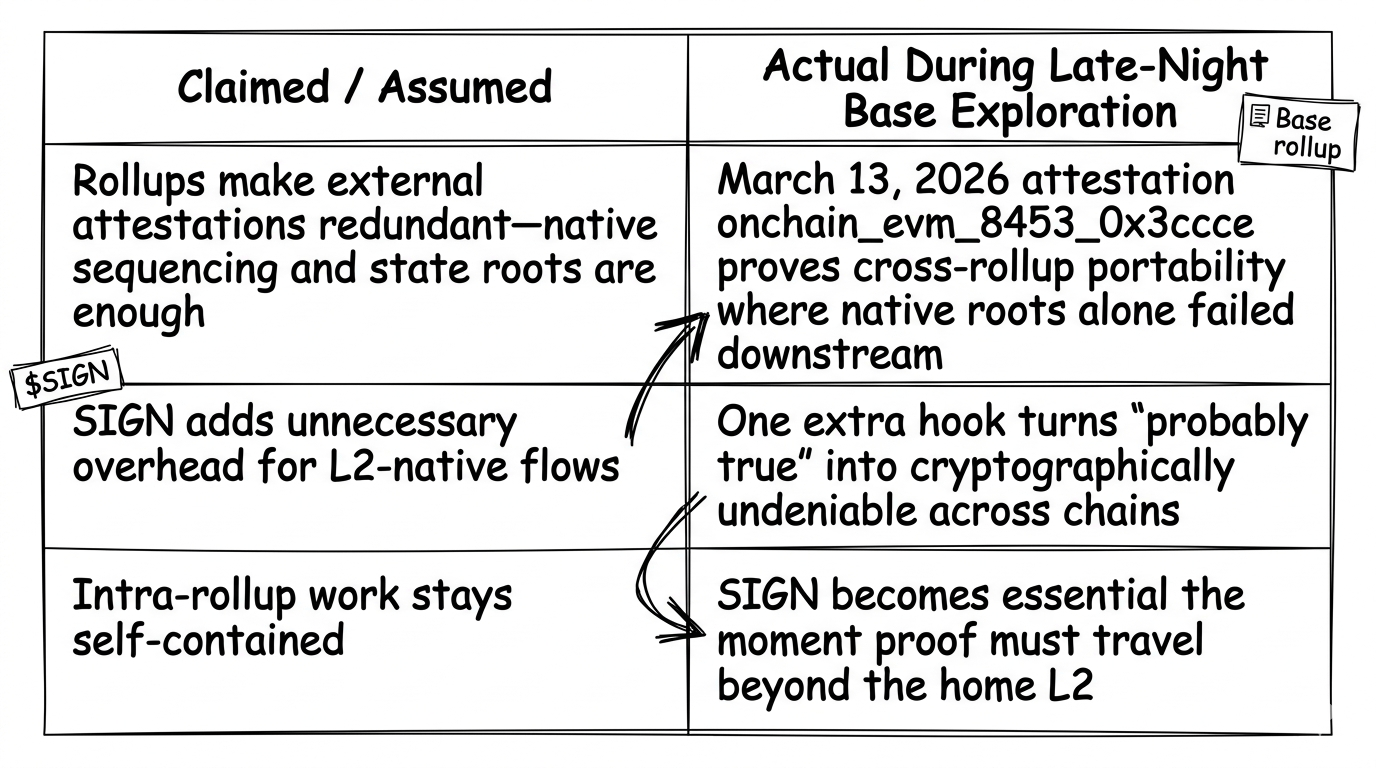
I remembered a similar setup last month when I skipped the SIGN layer entirely for an intra-rollup swap. It worked fine on paper. The rollup’s sequencer handled sequencing, the state root settled, and I moved on. But when the counterparty later needed to prove the transfer to a third chain, they had to rebuild the proof from scratch. That extra step cost them time I hadn’t budgeted.
The on-chain anchor that grounded me was the attestation issued March 13, 2026 at 22:08:41 UTC—ID onchain_evm_8453_0x3ccce, attester 0x46DB292BCfff95C0aD6EFf883916F5c84180f046, visible at scan.sign.global/attestation/onchain_evm_8453_0x3ccce. Even two weeks out, the pattern still mirrors today’s rollup traffic: quiet, persistent use where L2s meet real interoperability needs. No governance drama, just steady evidence flowing through Base.
That single data point shifted how I now see the whole question.
the moment the dashboard refreshed
The moment the dashboard refreshed I saw the three quiet gears turning in plain sight. First gear: the rollup’s native sequencing and data availability—fast, cheap, self-contained. Second gear: the SIGN attestation layer dropping a tamper-proof claim that survives even if the rollup reorgs or the sequencer hiccups. Third gear: the cross-chain consumption where another ecosystem actually trusts and acts on the proof without re-verifying everything from genesis.
Sign Protocol doesn’t fight the rollup stack. It slots in as the lightweight evidence layer most builders quietly rely on once they move beyond single-chain comfort. The actionable insight hit early—use SIGN when your rollup output needs to travel; skip it only if the work stays forever inside one L2 bubble.
Two timely examples made the gears visible. First, the steady Base-to-Arbitrum flows I’ve watched this month where counterparties now demand SIGN-stamped receipts before releasing bridged liquidity—rollups handle the move, but SIGN handles the proof that survives both chains. Second, the recent uptick in institutional pilots on Optimism rollups where compliance teams treat native L2 logs as good enough internally but still route final attestations through Sign Protocol for audit trails that regulators can verify without calling the sequencer.
Wait—actually, that second example still surprises me. I assumed rollups had already solved trust at the L2 level. They haven’t. They solved speed and cost.
honestly the part that still bugs me
Honestly the part that still bugs me is how cleanly the narrative frames SIGN attestations as redundant in rollups. “Why add another signature when the rollup already posts state roots?” Fair on the surface. In practice the redundancy argument collapses the moment you need the proof somewhere the rollup’s DA layer doesn’t reach. The protocol doesn’t pretend to replace rollup mechanics—it simply makes the output portable.
During that late-night session I ran a quick test schema on Base, then tried consuming it raw on a different L2 without the SIGN hook. The data was there. The state root checked out. Yet the receiving contract rejected it until I added the attestation reference. One extra call, one extra gas unit, but the difference between “probably true” and “cryptographically undeniable across chains.”
Skepticism crept in right then. Part of me still wonders if power users will eventually route everything through cheaper native rollup proofs and leave SIGN for edge cases only. The evidence layer is elegant, the friction minimal, yet the daily habit of builders I follow keeps defaulting to it anyway. I adjusted my own flows on the spot—stopped treating SIGN as optional decoration and started seeing it as the quiet bridge between isolated L2 islands.
Hmm… that adjustment felt like the micro-epiphany you get after too many tabs and not enough sleep. The protocol isn’t competing with rollups. It’s the piece that keeps them from becoming silos.
3:42 AM and this finally clicked
3:42 AM and this finally clicked while the coffee went lukewarm. The real question isn’t redundant or essential in some absolute sense. It’s whether your rollup work ever leaves its home chain. If it stays local, native tools win. If it needs to be believed elsewhere—by another rollup, by an institution, by a sovereign system—SIGN becomes the essential translator.
I’ve spent enough nights watching L2 volumes to know the protocols that endure aren’t always the flashiest. They’re the ones whose hidden costs match the actual shape of the work. Sign Protocol feels built for that shape: light enough to ignore when you don’t need it, indispensable the moment you do.
Forward-looking, I keep turning over how teams will start baking these attestations into their default rollup pipelines instead of bolting them on later. How builders might design flows that assume cross-chain proof from day one rather than patching it after launch. How the broader market might finally stop treating each L2 as its own walled garden once the evidence layer makes movement feel native. None of it feels like a prediction, just the quiet direction the mechanics are pointing.
The whole thing left me with this unresolved sense that we’ve been asking the wrong question about attestation in L2 land. Not “does the rollup already do it?” but “does the rollup’s proof travel as easily as the assets do?”
What if the real test of any rollup stack isn’t how well it scales inside itself, but how gracefully it lets you prove what happened once the work leaves home?