Many people see Sign and are still stuck at the level of 'issuing certificates, distributing airdrops, and creating identity labels'. I think this judgment is already a bit behind. The current Sign aims not to be a plugin for issuing whitelists to project parties, but rather a fundamental infrastructure that connects identity, distribution, protocol execution, audit evidence, and reputation transfer. Its latest documentation has even advanced the overall narrative to S.I.G.N. (Sovereign Infrastructure for Global Nations): integrating money, ID, and capital into a unified evidence layer, distribution layer, and signing layer. Sign Protocol is the evidence layer, TokenTable is the distribution engine, and EthSign is the protocol and signing layer. This product combination is no longer a single-point tool approach, but is clearly moving towards 'digital institutional infrastructure'.
I think the most valuable aspect of Sign is not that it 'proves who someone is', but that it attempts to standardize 'why something is valid'. The Sign Protocol allows for schema definition, writing statements as structured attestations, which can then be stored on-chain, off-chain, or in a hybrid manner, and provides REST, GraphQL, and SDK for querying and verification; it emphasizes not a single identity card, but a fact record that is queryable, verifiable, and auditable. This means that what it wants to solve is not a login issue, but a long-standing problem on the internet that has not been thoroughly resolved: can your historical behavior, qualifications, authorizations, compliance status, and contribution records continue to be read and acknowledged by other systems after leaving the original platform? Once this direction is established, Sign captures not the 'identity track', but 'transferable trust'.
Moreover, it is no longer just talking about abstract concepts. According to official disclosures, in 2024, Sign processed over 6 million attestations, completed the distribution of over $4 billion in tokens, reaching over 40 million wallets; Binance Research provided another more commercial signal: Sign achieved $15 million in revenue in 2024, raised a total of $32 million, and positioned itself as a global infrastructure for 'credential verification + token distribution'. In other words, it is not the kind of project that only talks about DID, VC, ZK narratives but is not genuinely used; at least from the product trajectory, it has already started with the two most easily implementable aspects of 'proof' and 'distribution'.
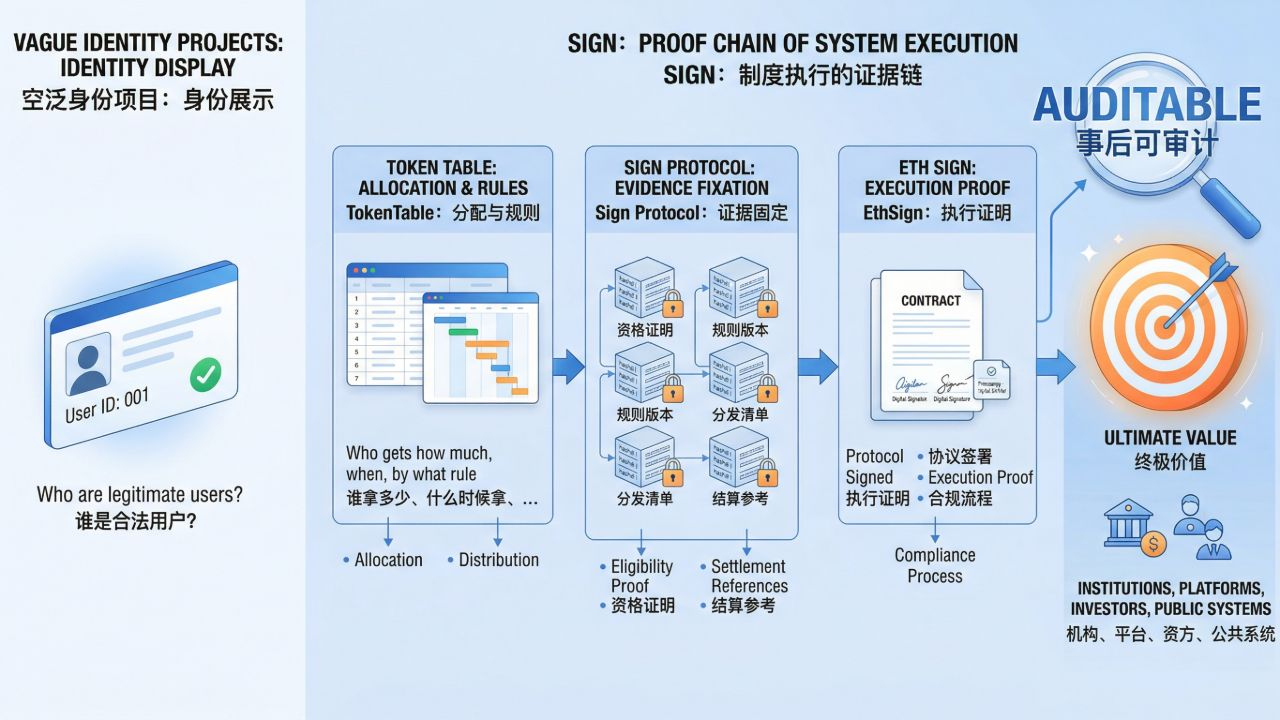
Why do I repeatedly emphasize the words 'proof' and 'distribution'? Because this is the biggest dividing line between Sign and many vague identity projects. Many projects only want to tell you 'who is a legitimate user', but in the real world, systems are more concerned with: who is qualified to receive this money, who meets this rule, who was approved by whom at what point in time, what the rule version is, and whether it can be audited afterwards. Sign's documentation states this very clearly: TokenTable is responsible for who gets how much, when they get it, and by what rules; Sign Protocol is responsible for fixing evidence such as qualification proof, rule versions, distribution manifest, and settlement references; EthSign brings in agreement signing, execution proof, and compliance processes. You will find that what it is actually targeting is not 'identity display', but 'the evidence chain left by institutional execution'. This is what institutions, platforms, investors, and public systems are truly willing to pay for.
But that being said, the most dangerous aspect of Sign is precisely here: it deals with 'verifiable factual expression', not 'the ultimate arbiter of the facts themselves'. Attestation can verify signatures, verify formats, and verify whether it was issued by an authorized issuer, but it does not automatically guarantee that the content is true, nor does it automatically ensure that different systems will interpret this data in the same way. The official documentation itself reveals this point: it relies heavily on external standards such as W3C VC/DID, OIDC4VCI, OIDC4VP, Bitstring Status List, ISO 20022 to achieve compatibility; while also emphasizing the separation of responsibilities for root authority, issuer, operator, and auditor, as well as multi-signature, HSM, audit export, and change governance. In short, Sign certainly has a side of 'open protocol', but it also heavily relies on who issues the proof, who recognizes the standards, who operates the system, and who interprets the rules. This system resembles 'controlled openness' rather than the completely leaderless decentralized utopia imagined by retail investors.
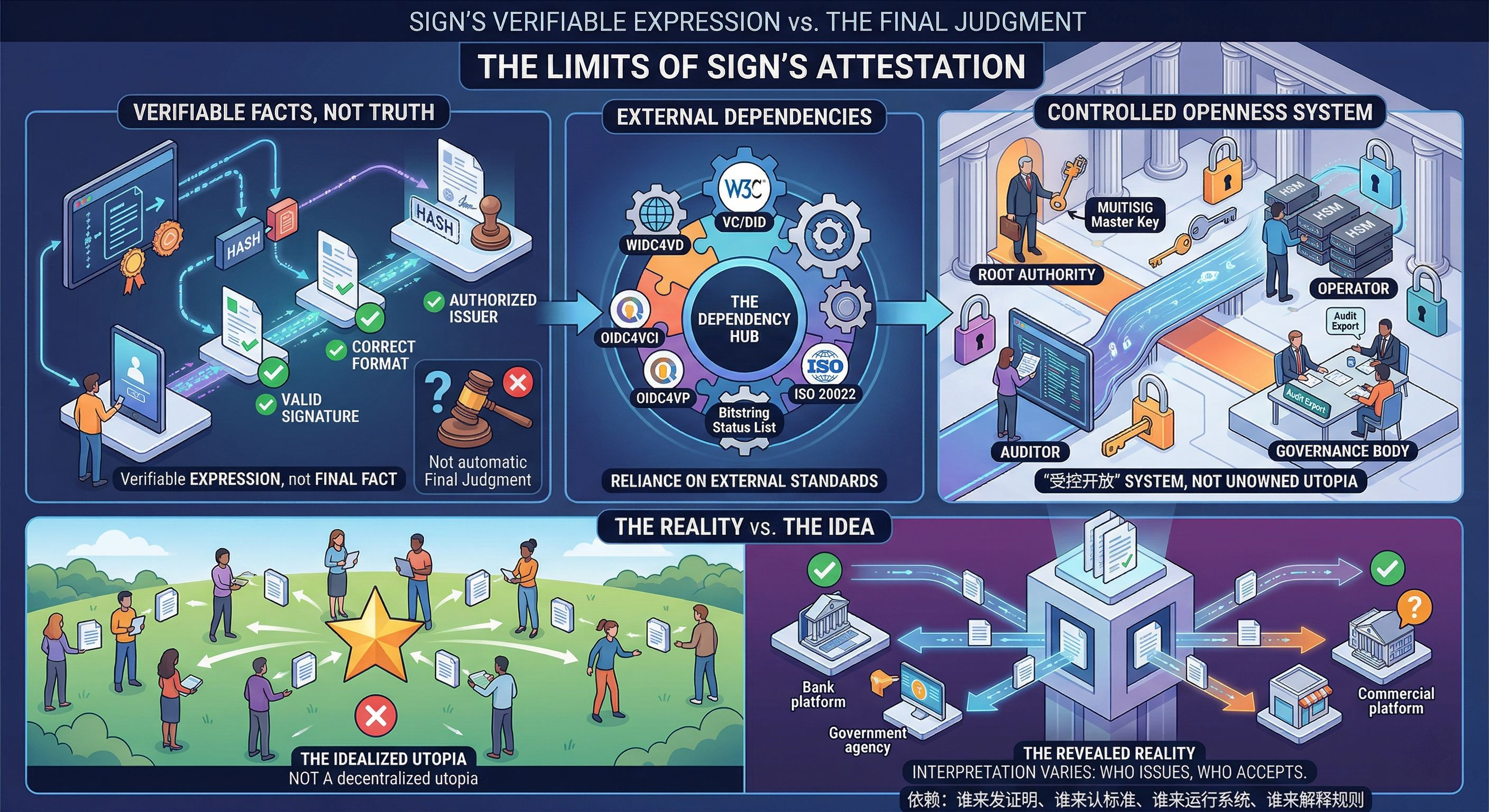
This is also the line of judgment that I care about most when looking at Sign: whether the data follows the user is not important; what matters is whether other systems recognize this data. On this point, no amount of on-chain records will help you. You store the attestation in a wallet; if the upper-layer applications do not read it, different verifiers do not share the schema, and different institutions do not accept the same trust registry, then it essentially remains platform power, just shifted from one database to another. The real hurdle Sign needs to overcome is not 'going on-chain', but 'being read in a consensus manner'. Therefore, its moat is not just in on-chain contracts, but in the issuer network, verifier network, standard compatibility, query layer, and the default workflows formed around these. This is why it has written indexing, query, audit, revocation/status into the core architecture, rather than treating them as side issues.
Let's talk about $SIGN itself. This coin now has a considerable narrative space, but its challenges are also tougher than many new coins. According to data from Binance and CoinGecko, SIGN has a total supply of 10 billion, with an initial circulation of 1.2 billion when it was launched on Binance, and as of April 2, 2026, CoinGecko shows a circulation of approximately 1.6 billion, a price of about $0.03224, a market cap of approximately $52.88 million, and an FDV of approximately $322 million; the next unlocking is scheduled for April 28, 2026, with approximately 401.11 million SIGN expected to be unlocked, accounting for about 4% of the total supply. These figures are crucial because they indicate that the market's current valuation of it still resembles 'an early to mid-stage protocol with infrastructural imagination, but value capture has not yet been fully realized', rather than a mature network that has been fully priced by the market.

The question falls here: can SIGN truly capture the value of this infrastructure? The official stance is that SIGN is used for attestation-related services, governance participation, incentives, and ecological operation; the MiCA white paper also clearly states that SIGN holders do not own equity, dividends, or claims against the issuer, and the value mainly comes from the functions and network usage within the protocol rules. My understanding is very straightforward: if Sign ultimately is just a 'very useful evidence system', but business traffic, rules interpretation rights, settlement links, and corporate payments do not continuously flow back to the token, then SIGN can easily become a narrative-rich but value-capturing loose coin; conversely, if more and more distribution, signing, verification, and auditing processes must go through its default standards and network entries, SIGN will have the opportunity to slowly evolve from a 'governance/incentive token' into a 'fee right for institutional traffic entry'. This is not something that can be glossed over with a utility; it depends on real usage.
So my final judgment on Sign is generally positive, but not blindly optimistic. I think it is one of the few projects that genuinely tackles deep water issues of the internet: not just putting information on-chain, but allowing 'trustworthy information relationships' to be transferable, verifiable, and systematized. If this succeeds, what Sign gains is not a rotation of a specific track, but an evidential infrastructure that a large number of digital systems will rely on in the future; if it fails, it will not completely go to zero, because at least the three components of 'proof + distribution + signing' already have real product forms and commercial touchpoints. But next, I am only focused on three things: first, whether external issuers and verifiers continue to expand, rather than just relying on the project party's self-circulation; second, whether applications start to read this data according to a unified schema; third, whether SIGN can transform from a 'story carrier' to a 'usage entry'. If these three things work out, Sign is not just storing data in a different place; if they do not, it will still talk about 'digital sovereignty' and 'trustworthy internet', but it will just be a more advanced middleware.