Google announced a new research for the Google Quantum AI team stating that theoretically they could break the current Bitcoin signatures ECDSA using less than 1200 logical qubits, and about 500,000 physical qubits, in just a few minutes per attack. This news has caused a big stir because ECDSA signatures are what fully protect Bitcoin wallets and addresses.
But if we look under the 'terrifying' headline, we find a huge engineering gap between the paper and reality. The largest real quantum computer currently is about 1200 physical qubits (like IBM Condor), and these are 'misaligned' qubits filled with noise, still very far from being high-quality, error-corrected qubits. To create 1200 logical qubits, you need hundreds or thousands of physical qubits for each one, which makes the figure of 500,000 physical qubits seem almost fictional in current circumstances.
These quantum devices also need to operate at temperatures lower than outer space, with near-complete isolation from any interference or waves, and yet there are still heavy issues in cooling, wiring, control, and scaling to several hundred thousand qubits. A clear example: Researchers from Caltech managed to create a 6000 logical qubit array using neutral atoms, but without entanglement, which is essentially the basis for running Shor's algorithm. The current level of true art in entangled qubits is around 96 qubits, with a coherence time of one or two seconds, while the attack they talked about requires days of continuous operation.
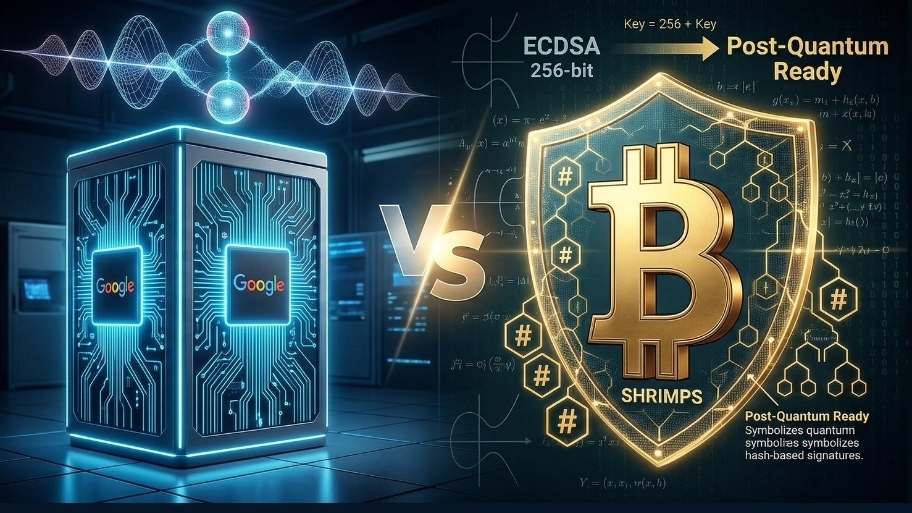
In all this, Bitcoin developers are not just standing by and watching. On the contrary, there is real work on "post-quantum" solutions. Researcher Jonas Nick introduced a new signature system called SHRIMPS, which relies on distributed hash-based signatures across multiple devices, producing a signature of about 2.5KB, which is approximately 3 times smaller than the NIST SLH‑DSA standard, making it very practical for Bitcoin block space constraints. SHRIMPS is built on an older system called SHRINCS, which produced signatures of about 324 bytes for use on a single device.
The issue is not just a signature algorithm; there is also the BIP‑360 proposal that adds a new output type called Pay‑to‑Merkle‑Root (P2MR), aimed at eliminating the vulnerability present in the Taproot key-path that could be affected by future quantum attacks. This proposal is already working on testnet, and there is a company, BTQ Technologies, testing real transactions on it, with an estimate that the full upgrade of the network could take up to 7 years to be done quietly and without breaking anything.
The quantum threat is not a myth, but it's also not a reason to be afraid. The papers say that an attack is possible in minutes on a large quantum device, but building this device itself is a terrifying engineering challenge and no one has come close to solving it yet. At the same time, the Bitcoin community is already working on defensive tools like SHRIMPS and BIP‑360, so that when the time comes, the upgrade will be organized and studied, not a hasty reaction under pressure from headlines.