I will tell you about another interesting method of fraud, conspiracy, and enemy recruitment. Spoofing is a type of cyber deception or fraud in which an attacker disguises themselves as a trusted source (person, company, or technical device) to gain access to your data, money, or simply to ingratiate themselves.
This word comes from the English 'to spoof' — to imitate, to forge.
1. Types of spoofing (how it works in life)
ID spoofing (number substitution): What we talked about earlier. Any number (a European code, a bank number, or even your own number) appears on your screen, while a fraudster calls through the internet.
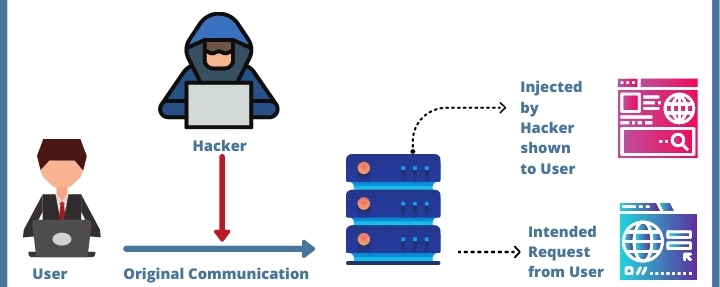
Email spoofing: You receive a letter where the 'From' field shows an official address (for example, support@privatbank.ua), but in reality, the letter was sent from a hacker's server. The goal is to make you click on a link or enter a password.
Website spoofing: Creating a complete copy of a well-known site (for example, a social network or a bank). You think you are logging into your profile, enter your password — and it instantly falls into the hands of thieves.
SMS spoofing: Messages on behalf of 'Alpha Bank' or 'Nova Poshta' that fall into the same message thread as the real ones because the fraudster forged the sender's text name.
2. How is number spoofing technically carried out?
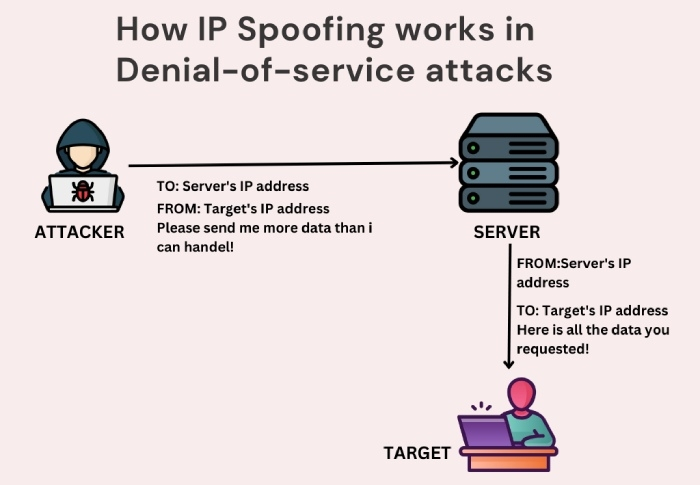
Malefactors use IP telephony (VoIP). In the protocols for transmitting voice over the internet, there is a Caller ID field (the identifier of who is calling). In regular phones, the operator strictly controls this field, but in internet services, it can be edited manually.
For example: A fraudster rents a 'gateway' (virtual PBX) and sets it up to display: 'Show the subscriber the number +33 1 23 45 67 89'. Your operator's system receives this signal and, unable to verify its authenticity (because it goes over the internet), displays these digits on your screen.
3. Why is this so dangerous?
Spoofing is just a 'wrapper'. The main danger is social engineering.
A person, upon seeing a familiar code or hearing a confident voice, loses vigilance. When a 'relative' says they have communication problems, they are actually building a psychological barrier: 'Don't ask about the number, just listen to me.'
4. How to protect yourself from spoofing?
1. The principle of 'Call back yourself': If you get a call from an official institution or a relative from a strange number — hang up. Find the old, verified number of this person (or bank) in your phone book and dial it yourself.
2. Don't trust your eyes: The text on the phone screen is just text. It is not a document that proves identity.
3. Verification in messengers: If a person says they are in Europe and have internet (which is needed for spoofing), ask them to send a voice message or make a video call on Viber/WhatsApp. Fraudsters usually do not go for this.
4. Ask uncomfortable questions: Always have a 'secret question' that only your close person knows the answer to.
Interesting fact: Spoofing is often used in spy movies, but in the modern world (2026), it has become so accessible that any teenager can download an app and call you pretending to be a neighbor or even the president.