The first time you look at Walrus, it doesn’t feel like a typical crypto “storage project.” It feels more like a quiet piece of infrastructure that is trying to do one job extremely well: keep large data available, verifiable, and retrievable, even when parts of the network fail or behave badly. For traders and long term investors, that difference matters, because the value of a storage network is not in slogans. It is in whether developers actually trust it to hold real application data when the market is calm and when the market is chaotic.
Walrus is designed to store blobs, meaning large files that are not naturally suited to being stored directly on a blockchain. Think of images, video, AI datasets, game assets, or any heavy data that modern apps need. The key idea is that Walrus does not treat storage as “just save this file somewhere.” It treats storage like a security problem, a reliability problem, and an incentive problem all at once. Its architecture is built around a small set of actors: users who want to write and read blobs, storage nodes that hold encoded pieces of those blobs, and a blockchain coordination layer that manages assignments and rules. Walrus uses Sui as that coordination layer, with a smart contract controlling how data shards are assigned to storage nodes.
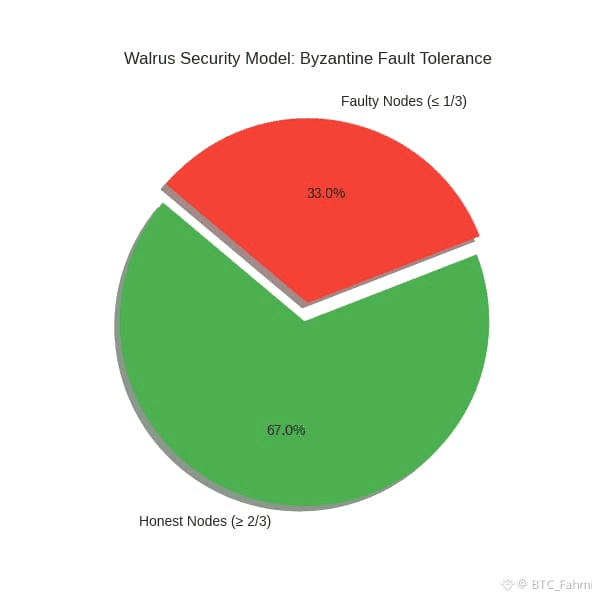
The security model is clear and, importantly, measurable. Walrus assumes that within a storage epoch, more than two thirds of the shards are managed by honest, functioning storage nodes. That means the system is designed to tolerate up to one third of shards being controlled by faulty or malicious operators, which is a classic Byzantine fault tolerance threshold. Storage epochs on mainnet last about two weeks, and reconfiguration happens across epochs. So instead of pretending nodes never leave, Walrus designs around churn as a normal condition.
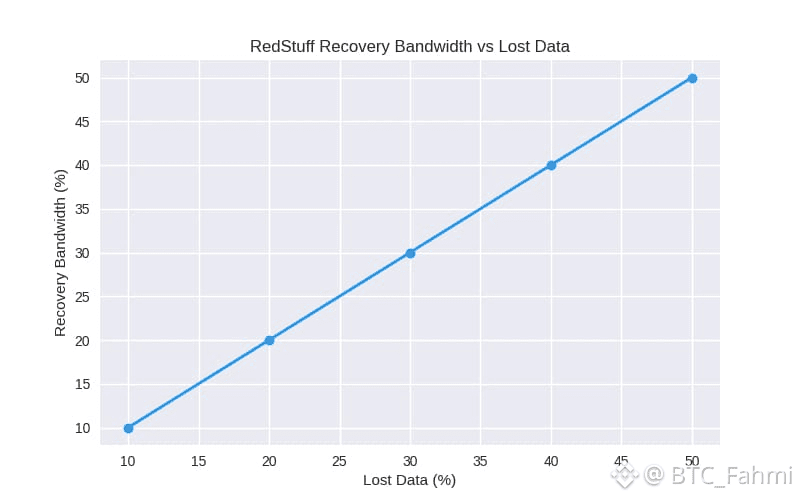
Where Walrus becomes technically interesting is how it stores data. Instead of simply replicating whole files many times, it uses an erasure coding scheme called RedStuff. In simple terms, your blob is transformed into many smaller “slivers,” distributed across nodes, and the system can reconstruct the blob even if a portion of those slivers are missing. The whitepaper describes RedStuff as a two dimensional erasure coding approach that achieves strong availability with a relatively low replication factor around 4.5x, while also enabling efficient recovery when data is lost. That matters because storage economics are brutal. If the cost to keep data safe is too high, real applications will choose centralized storage again.
The read and write flows also show that Walrus is not just a storage warehouse. It is a protocol with verification at its core. When data is written, Walrus needs a way to prove what was stored and where. When data is read, it needs a way to ensure the retrieved data matches what was originally committed. Walrus uses authenticated data structures, including Merkle style verification, so clients can detect tampering. This is one of those details that sounds boring until you realize it is the difference between “a network that stores data” and “a network that can safely serve data to smart contracts and applications that can’t afford silent corruption.”
One of the most distinctive security choices Walrus makes is how it handles storage proofs in real network conditions. In decentralized environments, attackers can exploit latency and timing to pretend they store data when they don’t. The Walrus research paper emphasizes that RedStuff supports storage challenges even in asynchronous networks, meaning the protocol is designed so an adversary cannot reliably game the timing of message delivery to pass verification without actually holding the required data. For traders, this is more than a technical flex. If a storage network cannot enforce “you must actually store the data,” its token incentives can drift into a fragile loop where rewards flow even when real service degrades.
Walrus also allows optional infrastructure like aggregators. Aggregators reconstruct blobs from slivers and serve them over normal web protocols like HTTP. They are optional because users can reconstruct directly from storage nodes if they want, but aggregators make integration easier for typical apps. This is a practical design choice: protocols win when they meet developers where they already are, not where the protocol wishes they were.
Now, the investor question: where does value accrue? Walrus includes an economic model based on staking, with rewards and penalties designed to align long term storage commitments. In other words, the protocol tries to make reliable storage the profitable strategy, and unreliable behavior the costly one. This is the heart of “security” in decentralized infrastructure. Cryptography can prevent some attacks, but incentives prevent the slow decay that happens when operators realize they can cut corners.
My honest opinion is that Walrus’s biggest strength is that it treats recovery and long term availability as first class requirements, not afterthoughts. The research emphasizes efficient self healing, where recovery bandwidth is proportional to lost data instead of forcing full blob re downloads. That is the kind of detail that can make a network viable at scale rather than impressive only in demos.
But neutrality also means being clear about risks. Walrus relies on a blockchain contract for coordination, so contract bugs, governance mistakes, or unexpected incentive exploits can become systemic issues. Its security assumptions depend on honest majority conditions in each epoch, so concentrated operator power or correlated failures could stress the model. Any token tied to infrastructure demand can face cyclical pressure: in bear markets, demand and node profitability can drop, increasing churn risk. And because decentralized storage is a crowded field, adoption competition is real, regardless of how strong the engineering looks on paper.
Looking forward, Walrus’s outlook depends on whether developers use it for serious applications that need reliable, verifiable blob storage, especially in areas like onchain media, gaming assets, AI agent data, and decentralized hosting. Walrus itself positions as programmable storage accessible beyond a single ecosystem, and its mainnet launch materials emphasize broader application support and decentralized hosting via Walrus Sites. If real apps commit long term data to the network, that can create more stable demand than short term speculation.
In the end, Walrus is a reminder that not all crypto value is loud. Sometimes the most meaningful projects are the ones that obsess over the ugly realities: node churn, imperfect networks, adversarial behavior, and the simple fact that data must still be there next month, next year, and five years from now. For traders, that means watching not just price action, but network usage, storage demand, node participation, and whether the protocol’s security assumptions keep holding under real stress. If those fundamentals grow steadily, Walrus becomes more than a narrative. It becomes infrastructure people quietly depend on, and that is usually where durable value starts.
