This attack is particularly insidious because it does not exploit a code vulnerability, but rather a human cognitive bias: trust in visual familiarity and the convenience of "copy and paste".
In the crypto ecosystem, security depends not only on your seed phrase but also on your transaction habits. Recently, a technique known as Address Poisoning has gained traction, affecting even experienced users of $ETH , $BNB , and stablecoins such as $USDT .
What is Address Poisoning?
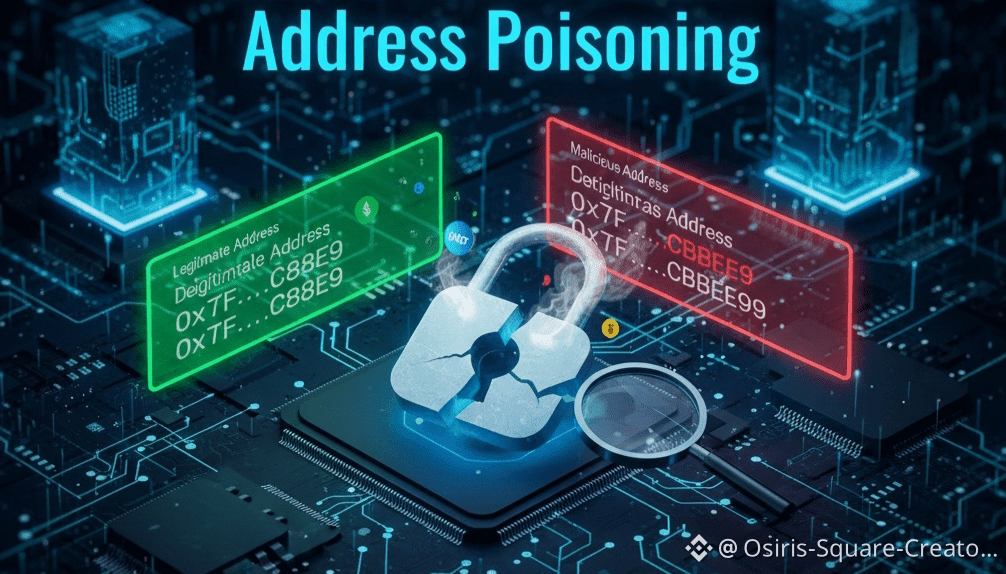
The attack consists of "poisoning" your transaction history. The attacker uses software to generate a vanity address that shares the same first and last characters as an address you frequently interact with (or even your own address).
The process is simple but deadly:
The scammer detects a legitimate transaction on the blockchain.
Create an almost identical address: for example, if your address ends in ...A1b2, the attacker's address will also end in ...A1b2.
It sends you a negligible amount of $USDT or tokens so its address appears in your recent transaction history.
The trap: The next time you send funds, you might accidentally copy the scammer's address from your history instead of the real one.
Specialist Observations and Reasoning
When analyzing these attacks on networks like #Ethereum or #BNB_Chain , I observe that the attacker's success relies on address shortening that many user interfaces employ. If you only see 0x12...A1b2, it's impossible to distinguish the real from the fake.
Moreover, the use of $USDT and other stablecoins is the primary target due to the high volume of daily transfers, making the attacker's "dust" (small amounts) go unnoticed among your regular transactions.
How to defend: Golden Rules
🚫 Never copy from history: Treat your transaction history as a contaminated zone. Never copy an address from there for a new transfer.
📚 Use the Contact List: Platforms like #Binance and wallets like #MetaMask or #TrustWallet allow you to save "Trusted Addresses." Always use them.
🔍 Central character verification: Attackers match the start and end. If you're verifying manually, check the middle characters of the address; that's where the similarity fails.
0️⃣ Ignore zero-value transactions: If you see you received a tiny amount of a token you didn't expect, do not interact with that address. It's the bait.
🛡️ Hardware Wallets: Devices like Ledger or Trezor require you to verify the full address on a separate physical screen. It's a vital layer of security.

The evolution of the attack in 2026
As we advance, attackers use AI to predict sending patterns. However, the most robust technical solution remains using name services like ENS (.eth) or Space ID (.bnb). When sending to tuname.eth, you eliminate the risk of confusing a complex alphanumeric string.
🚀 Protect your assets today!
Address Poisoning only works if you're in a hurry. Security in Web3 is a marathon, not a sprint.
Share this article with your friends so no one else falls into this visual trap.
Education is your best firewall!
#Security #AddressPoisonin #Web3Security #CryptoSafety #BinanceSquare