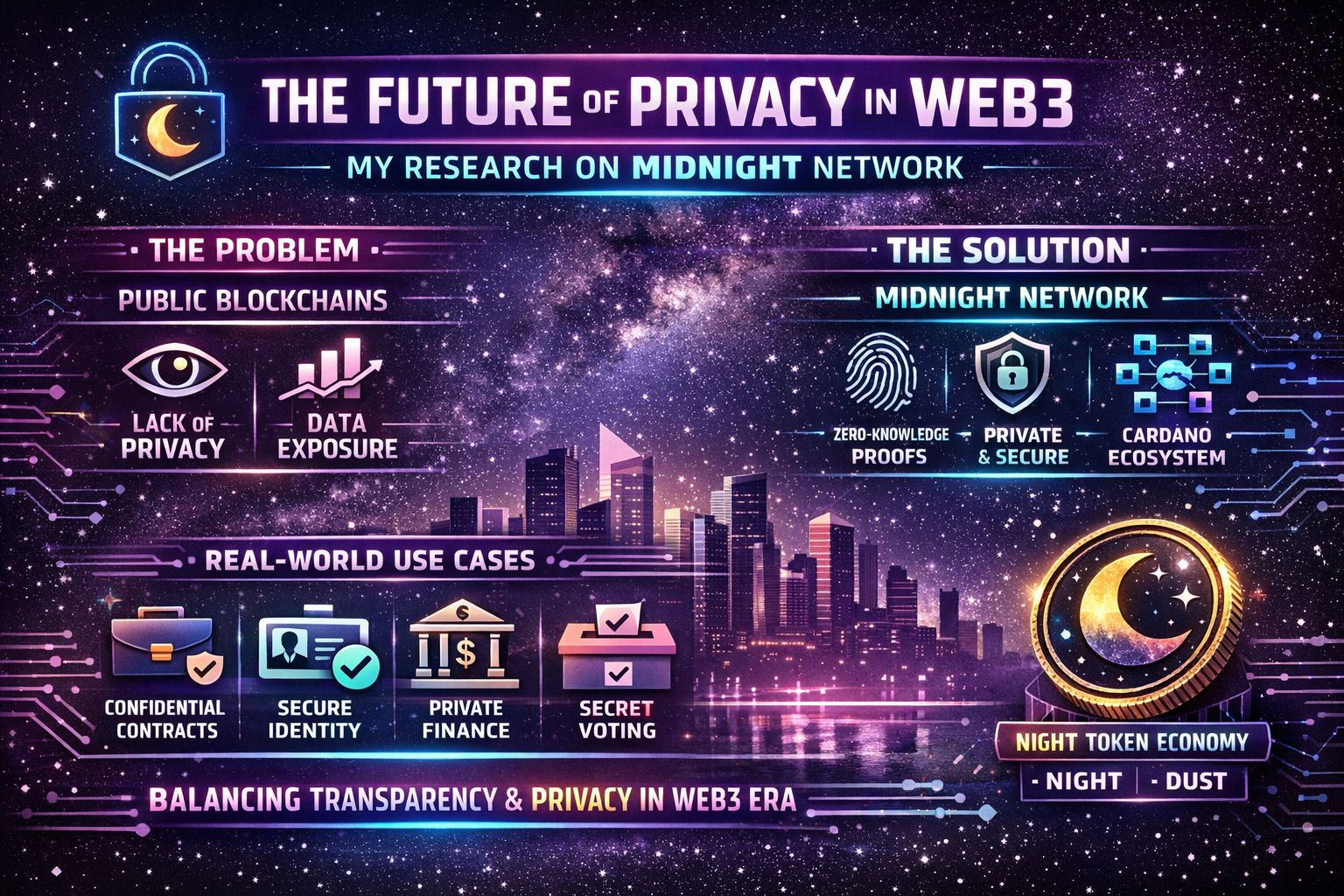
 Crypto has always promised freedom. Freedom from middlemen, freedom from censorship, and freedom to control your own assets. But there’s a strange contradiction at the heart of most blockchains.
Crypto has always promised freedom. Freedom from middlemen, freedom from censorship, and freedom to control your own assets. But there’s a strange contradiction at the heart of most blockchains.
Everything is public.
Every wallet. Every transaction. Every movement of funds. Anyone with a block explorer can follow the trail. Transparency is great for verification, but it comes with a cost: privacy.
That’s where Midnight Network begins to stand out.
Instead of choosing between transparency and privacy, Midnight is exploring a middle path where both can exist together.
Confidential Smart Contracts
One of the most interesting qualities of Midnight Network is its focus on confidential smart contracts. Traditional smart contracts execute publicly, meaning all data used in the contract can potentially be seen.
Midnight introduces a different approach. Smart contracts can process sensitive data while keeping that data hidden from the public. The blockchain still verifies that everything is valid, but the underlying information remains private.
This opens the door to use cases that public chains struggle with, especially in industries where confidentiality matters.
Selective Data Disclosure
Privacy doesn't always mean hiding everything. Sometimes you need to prove something without revealing the full story.
Midnight uses zero-knowledge technology to enable selective disclosure. This means users or applications can prove facts—like compliance with a rule or ownership of an asset—without exposing unnecessary details.
For businesses, institutions, and developers, this could be extremely valuable. It creates a system where verification and privacy coexist.
Enterprise-Friendly Design
Many blockchain systems are built mainly for retail users or DeFi traders. Midnight is thinking more broadly.
Its architecture aims to support enterprise-grade applications where regulatory requirements and data protection are critical. Financial institutions, supply chains, healthcare systems, and digital identity platforms all require strict privacy controls.
By focusing on this area, Midnight is positioning itself for real-world use rather than purely speculative ecosystems.
Regulatory Compatibility
Privacy in crypto often raises concerns about regulation. Midnight’s design tries to balance confidentiality with compliance.
Through selective disclosure and cryptographic verification, organizations can show regulators that rules are being followed without revealing private operational data.
This approach could help bridge the long-standing gap between blockchain innovation and regulatory acceptance.
Scalable Privacy Infrastructure
Privacy technologies are often criticized for being slow or computationally heavy. Midnight aims to integrate advanced cryptography in a way that still supports scalable applications.
If successful, it could become part of the underlying infrastructure that supports privacy-focused blockchain services without sacrificing performance.
Quiet Infrastructure That Could Matter
Not every important technology becomes a headline trend.
Some systems quietly become the infrastructure behind the scenes—the plumbing that makes other applications possible.
Midnight Network might follow that path. Instead of chasing hype cycles, it is exploring a deeper problem: how to keep blockchain verifiable while protecting sensitive information.
The future of crypto may depend not just on transparency, but on controlled transparency.
And that’s exactly the space Midnight Network is trying to build.