People throw the word privacy around in crypto like it’s some kind of magic ingredient.
Every new project claims it.
Every whitepaper promises it.
After watching this cycle for years, the pattern is pretty familiar.
A new “privacy chain” appears.
The technology sounds impressive.
But the moment real-world use cases show up, the model starts breaking down.
That’s why Midnight Network caught my attention.
Not because it’s louder than other projects. Actually the opposite. It has been building relatively quietly, and the deeper you look into it, the more it feels like the team is trying to solve a real design problem inside blockchain rather than repeating the same narrative.
Here’s the issue most privacy projects run into.
They treat privacy like a curtain.
Pull the curtain down.
Hide everything.
Problem solved.
At least that’s the theory.
But once everything disappears behind that curtain, a new question appears:
How do you prove anything actually happened?
That’s where many privacy systems struggle.
If nothing is visible, verification becomes difficult. And without verification, trust becomes fragile.
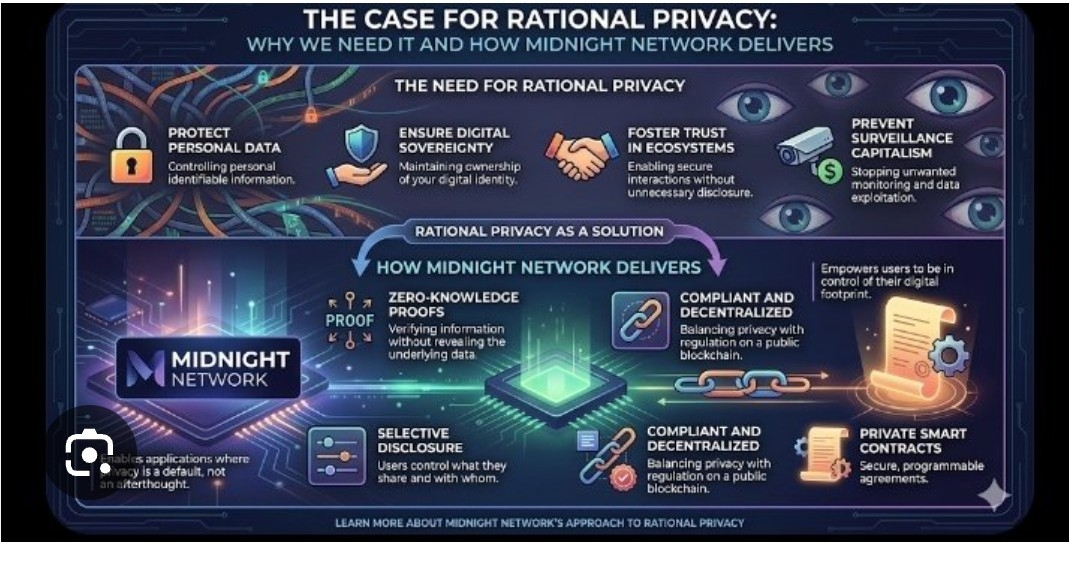
Midnight approaches this differently by relying heavily on Zero-Knowledge Proofs.
If you’ve spent time in crypto, you already know why this matters.
Zero-knowledge technology allows someone to prove something is true without revealing the underlying data.
That changes the equation completely.
Instead of exposing every detail of a transaction or process, the network can confirm that the rules were followed while keeping sensitive information private.
And that balance is important.
Early blockchains like Bitcoin and Ethereum built trust through total transparency. Everything was visible on-chain. Anyone could verify activity.
That model worked well for the early stage of crypto.
But full transparency also means exposing far more information than many people actually want public:
wallet behavior
business logic
financial activity
sensitive data
Not everything belongs on a public ledger forever.
At the same time, systems that hide everything create the opposite problem.
If no one can see anything, people start asking uncomfortable questions.
Midnight is essentially trying to land between those two extremes.
Sensitive information can remain private, while the proof that rules were followed stays verifiable.
In other words:
Proof without exposure.
And that approach opens the door to applications that simply don’t work on fully transparent chains.
Think about things like:
• confidential payments
• private identity systems
• enterprise financial workflows
• smart contracts with protected business logic
Companies are unlikely to move critical operations onto a blockchain if every detail is publicly visible to competitors.
That’s just reality.
Midnight seems designed with that reality in mind.
Another interesting design choice is the network’s dual-asset structure.
Instead of forcing one token to handle everything, the system separates the economic roles.
The token NIGHT acts as the core asset connected to governance and network participation.
Meanwhile, the operational resource used for transaction activity is DUST.
At first this might sound like a small technical detail, but it solves a common problem in blockchain systems.
On many networks, the same token must serve multiple purposes:
governance
gas fees
speculation
incentives
When the price spikes, transaction costs often spike with it.
Midnight’s model separates capital from network activity, which can make the system more predictable for users and developers.
That kind of architecture usually appears when a team spends more time thinking about long-term infrastructure than short-term hype.
And that’s probably the most important point here.
Midnight doesn’t feel like it was built to ride a narrative cycle.
It feels like infrastructure for a version of Web3 where privacy becomes a default feature rather than an afterthought.
Of course, having a strong design is only the first step.
Crypto history is full of projects with good ideas that never turned into real ecosystems.
Execution always decides the outcome.
Developers need to build.
Applications need to launch.
Users need to show up.
That’s the real test for Midnight Network.
But the reason people keep paying attention to it is fairly simple.
It isn’t trying to become just another blockchain with a recycled pitch.
It’s trying to build a system where privacy, verification, and usability can exist together without breaking the network.
And honestly, that foundation already feels stronger than most privacy narratives the crypto market has seen before.